Search results for "Takeover"
-
 225Articles
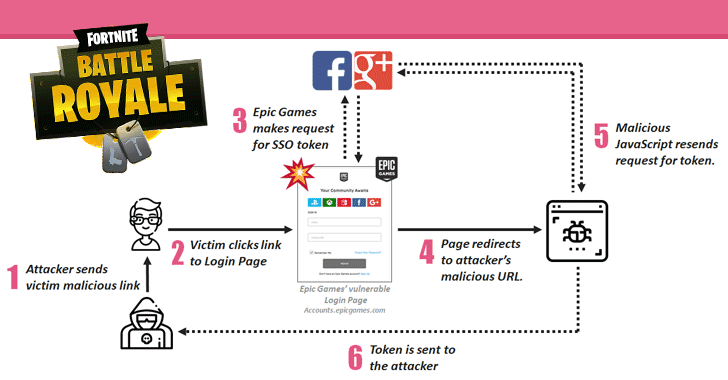
225ArticlesFortnite Flaws Allowed Hackers to Takeover Gamers’ Accounts
Check Point researchers have discovered multiple security vulnerabilities in Fortnite, a massively popular online battle game, one of which could have allowed...
-
 256News
256NewsHacker takeovers Drake’s Fortnite account to yell racial slurs
The official Fortnite account of the Canadian rapper Drake going by the handle of “Duddus647” was hacked in an attack on Thanksgiving weekend. The hacker used...
-
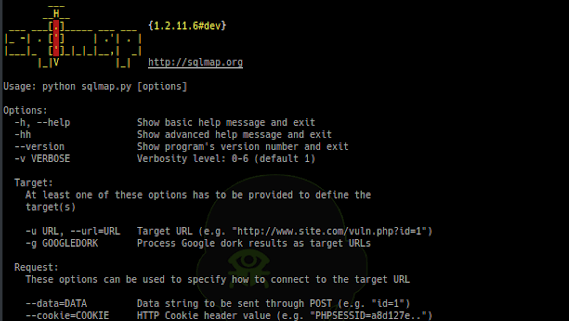
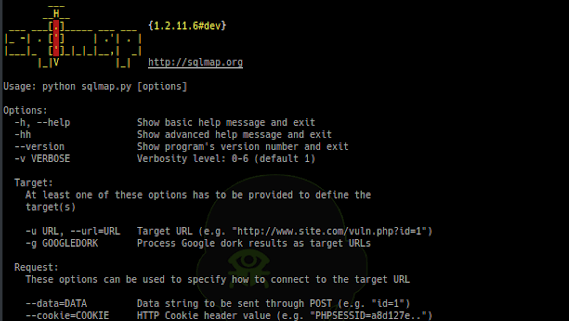 260Exploitation Tools
260Exploitation ToolsSQLMap v1.2.11 – Automatic SQL Injection And Database Takeover Tool
SQLMap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over...
-
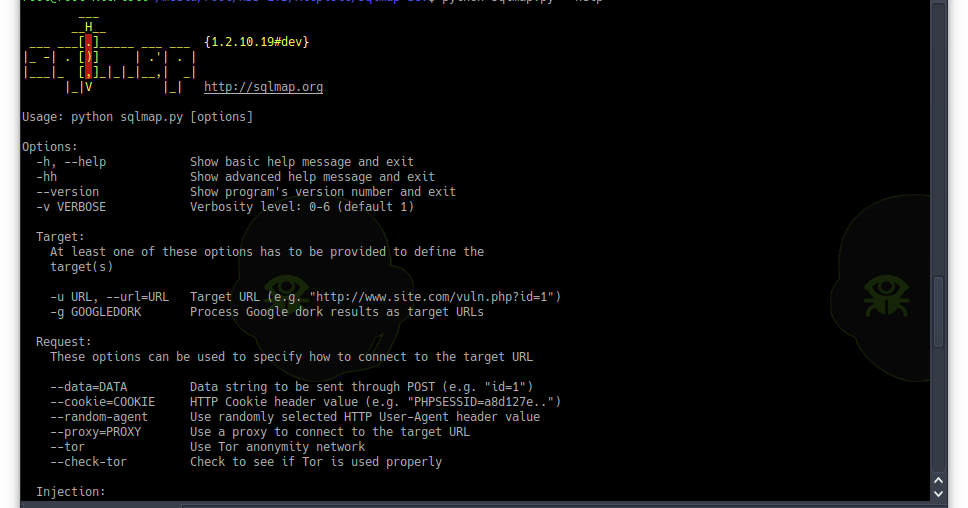
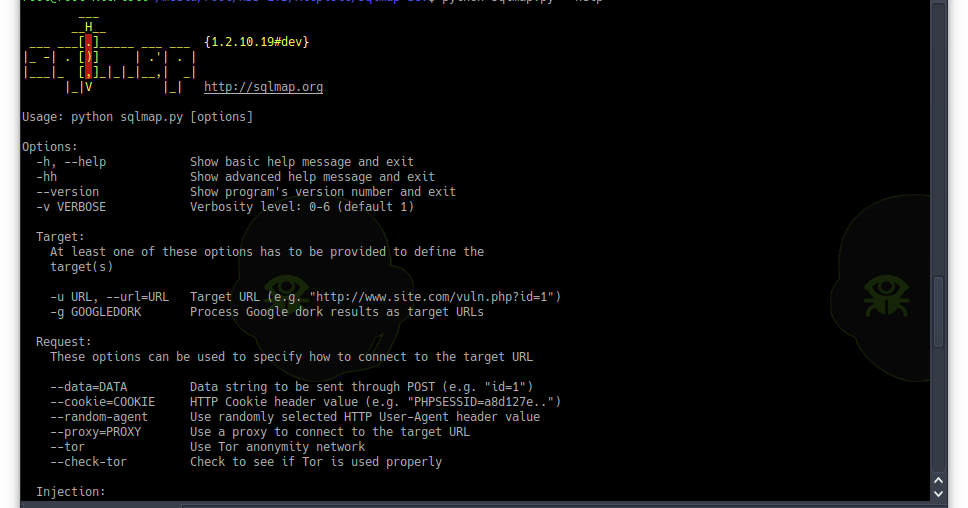 211Exploitation Tools
211Exploitation ToolsSQLMap v1.2.10 – Automatic SQL Injection And Database Takeover Tool
SQLMap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over...
-
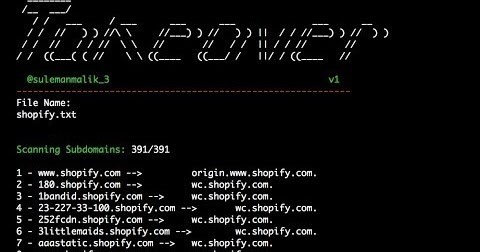
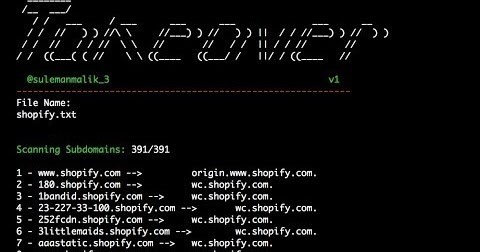 280Information Gathering
280Information GatheringTakeOver v1 – Extracts CNAME Record Of All Subdomains At Once
What is Subdomain Takeover? Subdomain takeover is a class of vulnerability where subdomain points to an external service that has been deleted....
-

 361Enumeration
361EnumerationTakeOver : Script Extracts CNAME Record Of All Subdomains At Once
Subdomain takeover is a class of vulnerability where subdomain points to an external service that has been deleted. The external services are...
-
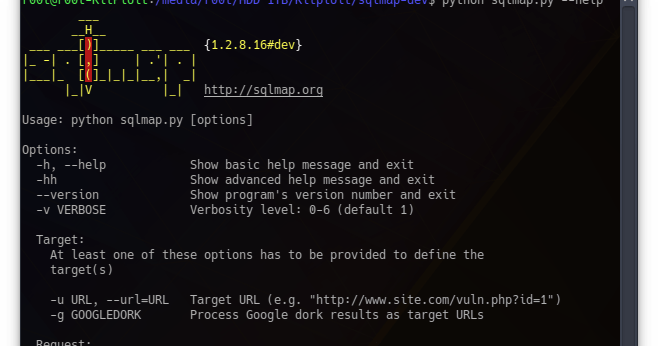
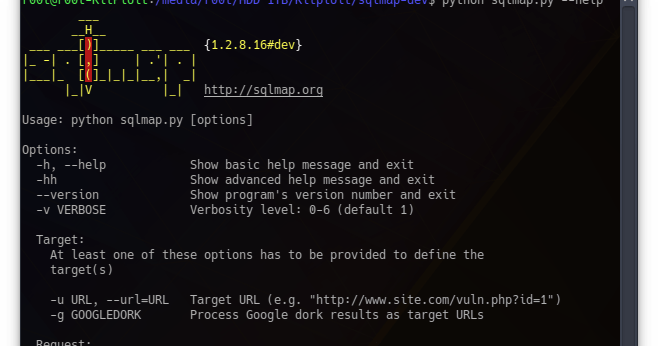 249Exploitation Tools
249Exploitation ToolsSQLMap v1.2.8 – Automatic SQL Injection And Database Takeover Tool
SQLMap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over...
-
 243Exploitation Tools
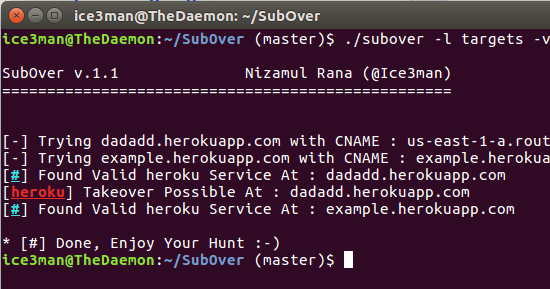
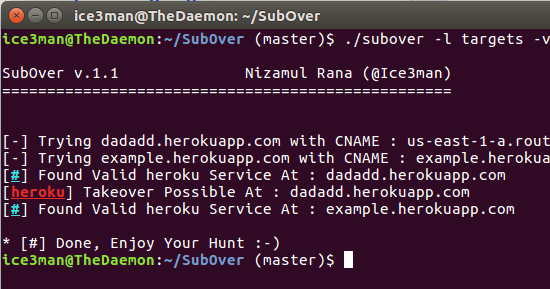
243Exploitation ToolsSubOver v1.1.1 – A Powerful Subdomain Takeover Tool
Subover is a Hostile Subdomain Takeover tool originally written in python but rewritten from scratch in Golang. Since it’s redesign, it has...
-

 362Incidents
362IncidentsHow to make a Subdomain Takeover Attack
A team of information security experts tells us that sub-domain acquisition vulnerabilities happen whenever a subdomain points to a service (for example,...
-

 281Data Security
281Data SecurityHackers can takeover & control emergency alarm system with a $35 radio
Researcher Identifies Emergency Alert Systems Vulnerable to Exploitation Due to SirenJack Flaw – Critical Military and State Infrastructure at Risk of Attacks by Malicious Hackers. ...
-
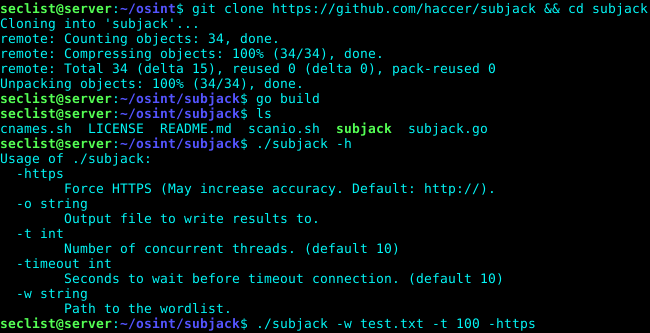
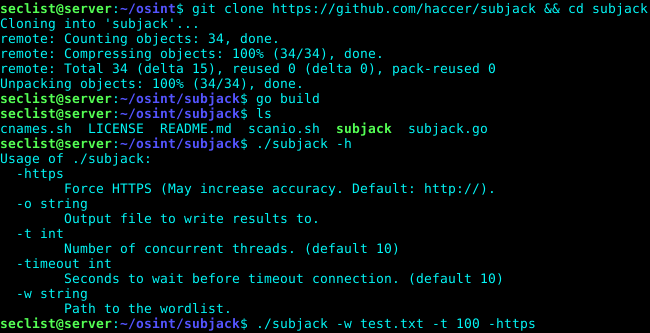 239Exploitation Tools
239Exploitation ToolsSubjack – Hostile Subdomain Takeover Tool Written in Go
subjack is a Hostile Subdomain Takeover tool written in Go designed to scan a list of subdomains concurrently and identify ones that...
-

 238Geek
238GeekIP Security Cameras Vulnerable to Hostile Takeovers
According to a report submitted by the security company called F-Secure, the security cameras made by a Foscam company from China have some...
-

 321Vulnerabilities
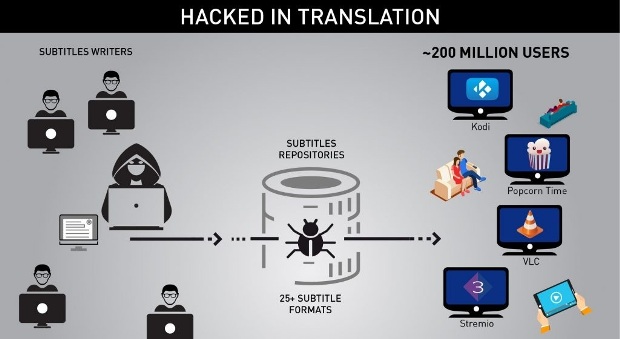
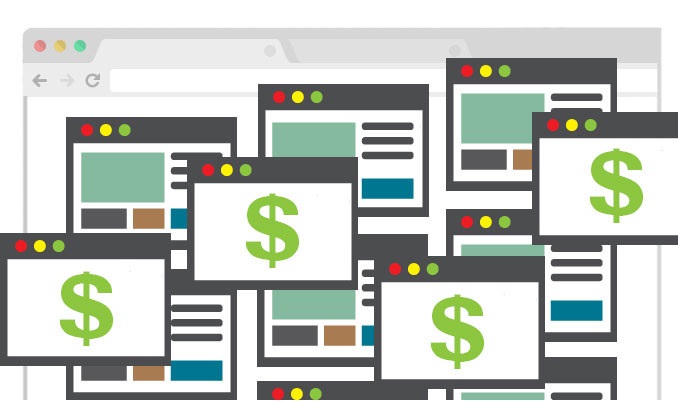
321Vulnerabilities200 Million Downloaded video players including VLC Player are vulnerable to Malicious subtitles Attack -A Complete Takeover Attack
A new Cyber Attack Spreading through Vulnerable Subtitles which Downloaded by Victims Media Player and threatens more than 200 Millions of vulnerable...
-
 187Incidents
187IncidentsHacked in Translation – from Subtitles to Complete Takeover
Check Point researchers revealed a new attack vector which threatens millions of users worldwide – attack by subtitles. By crafting malicious subtitle...
-

 306Data Security
306Data SecurityFlickr’ Account Takeover Vulnerability Patched, Researcher Gets $7k Bounty
A security researcher named “Michael Reizelman” privately disclosed a serious vulnerability in Flickr and earned a bounty of $7,000 in the process. A...
-

 181Data Security
181Data SecurityFACEBOOK FIXES VULNERABILITY THAT LED TO ACCOUNT TAKEOVER, PAYS RESEARCHER $16K
Facebook quickly resolved a vulnerability in its Business Manager tool late last month that could have let an attacker take over any Facebook page....
-

 260Vulnerabilities
260VulnerabilitiesLenovo Bloatware Patched to Fix System Takeover Bug
Lenovo Solution Center allowed attackers to get admin access. Lenovo has hid a crucial security update in an old security advisory from last...
-

 287Geek
287GeekNew Bug Lets Attacker Takeover PC via Outlook Email
ShortRead: A suspicious email sent to Outlook users can control user’s system, though, Microsoft has introduced a patch for the issue but...
-
 180Vulnerabilities
180VulnerabilitiesKemoge Android Adware Campaign Can Lead to Device Takeover
Google has been busy removing a number of apps from Google Play that are disguised as popular selections that are actually pushing...
-

 286Data Security
286Data SecurityVulnerable In-flight WiFi lets hackers to remotely takeover modern aircraft
The on-plane Wireless systems can easily be hacked by compromising the websites visited by travelers — This happens if same routers/wiring is...
-

 335News
335NewsFacebook Login Bug Lets Hackers Takeover User Accounts with Reconnect Tool
Even after almost a year, Facebook apparently has failed to fix a bug that lets attackers hijack accounts on sites that leverage...






