Search results for "Tor"
-
 3.8KRansomware
3.8KRansomwareRorschach – Fastest Encryption Ransomware Ever Found in Ransomware History
Researchers from Checkpoint found a new and previously unknown ransomware variant dubbed “Rorschach” with highly sophisticated features that target U.S. companies. Rorschach...
-

 907Vulnerabilities
907VulnerabilitiesHackers Exploiting WordPress Elementor Pro Vulnerability: Millions of Sites at Risk!
Unknown threat actors are actively exploiting a recently patched security vulnerability in the Elementor Pro website builder plugin for WordPress. The flaw,...
-
 3.0KMalware
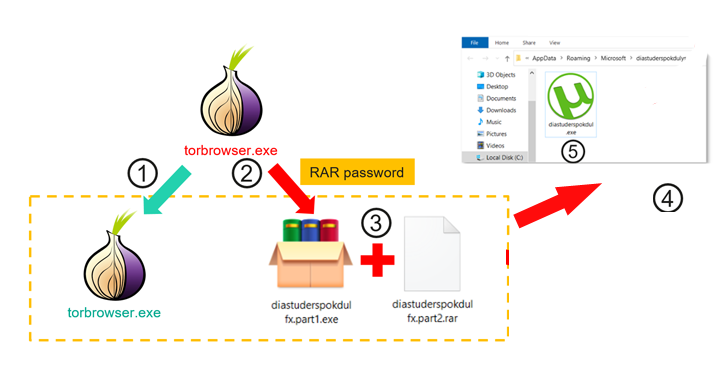
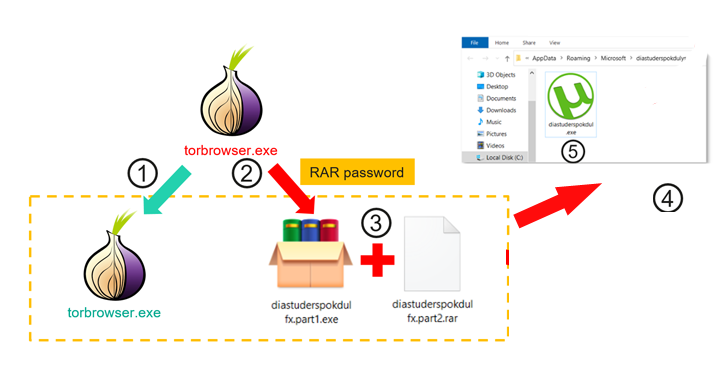
3.0KMalwareTrojanized TOR Browser Installers Spreading Crypto-Stealing Clipper Malware
Trojanized installers for the TOR anonymity browser are being used to target users in Russia and Eastern Europe with clipper malware designed...
-

 1.7KData Security
1.7KData SecurityBest open source tool for cyber incident detection in Microsoft Azure, Azure Active Directory, and Microsoft 365
The Goose Tool is a new free tool that may assist network defenders in identifying possibly malicious activities in Microsoft Azure, Azure...
-
 3.0KMalware
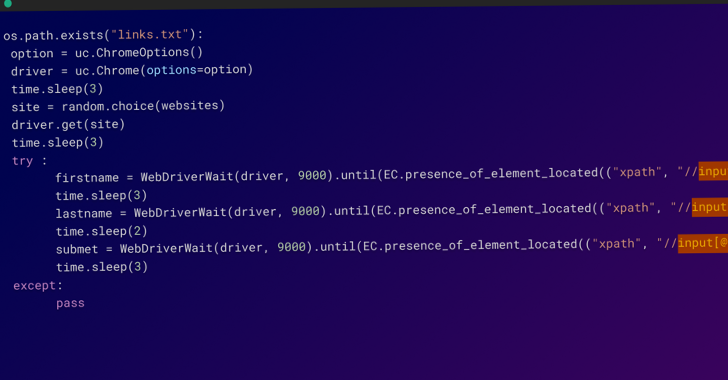
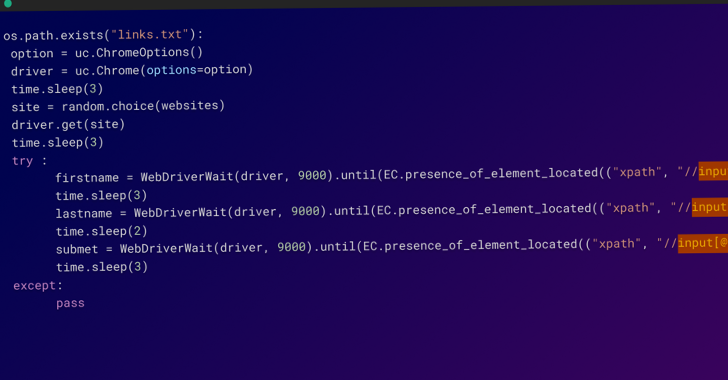
3.0KMalwareWarning: AI-generated YouTube Video Tutorials Spreading Infostealer Malware
Threat actors have been increasingly observed using AI-generated YouTube Videos to spread a variety of stealer malware such as Raccoon, RedLine, and...
-

 4.5KMalware
4.5KMalwareBeware of Malicious 2FA Apps in App Store and Google Play that Deploys Malware
Cybersecurity experts at Sophos recently detected multiple malicious 2FA apps in App Store and Google Play that deploy malware. While Twitter made...
-

 4.2KData Breach
4.2KData BreachDutch Police Arrest 3 Hackers Involved in Massive Data Theft and Extortion Scheme
The Dutch police announced the arrest of three individuals in connection with a “large-scale” criminal operation involving data theft, extortion, and money...
-
 756Cyber Attack
756Cyber AttackAttackers Flood NPM Repository with Over 15,000 Spam Packages Containing Phishing Links
In what’s a continuing assault on the open source ecosystem, over 15,000 spam packages have flooded the npm repository in an attempt...
-

 1.5KCyber Attack
1.5KCyber AttackHydrochasma: New Threat Actor Targets Shipping Companies and Medical Labs in Asia
Shipping companies and medical laboratories in Asia have been the subject of a suspected espionage campaign carried out by a never-before-seen threat...
-

 3.9KVulnerabilities
3.9KVulnerabilities⚡Top Cybersecurity News Stories This Week — Cybersecurity Newsletter
Hey 👋 there, cyber friends! Welcome to this week’s cybersecurity newsletter, where we aim to keep you informed and empowered in the...
-

 5.0KCyber Attack
5.0KCyber AttackNew Threat Actor WIP26 Targeting Telecom Service Providers in the Middle East
Telecommunication service providers in the Middle East are being targeted by a previously undocumented threat actor as part of a suspected intelligence...
-

 3.7KMalware
3.7KMalwareFinancially Motivated Threat Actor Strikes with New Ransomware and Clipper Malware
A new financially motivated campaign that commenced in December 2022 has seen the unidentified threat actor behind it deploying a novel ransomware...
-
 2.8KMalware
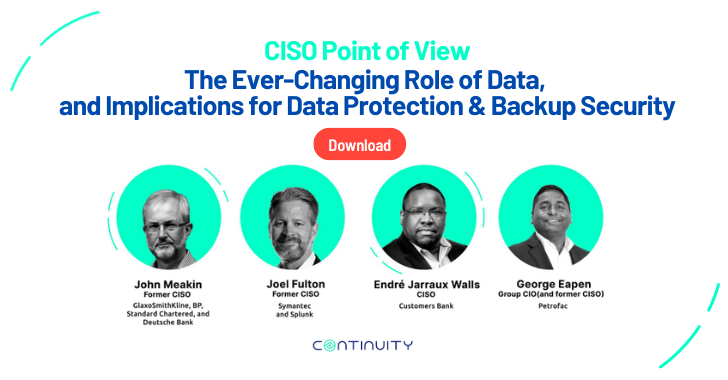
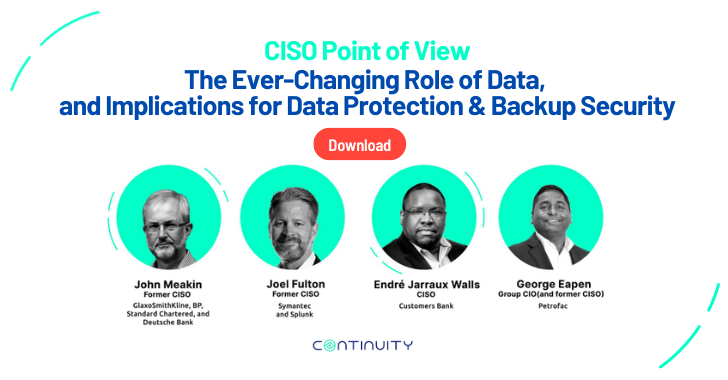
2.8KMalwareA CISOs Practical Guide to Storage and Backup Ransomware Resiliency
One thing is clear. The “business value” of data continues to grow, making it an organization’s primary piece of intellectual property. From...
-

 3.4KMalware
3.4KMalwareHackers Targeting U.S. and German Firms Monitor Victims’ Desktops with Screenshotter
A previously unknown threat actor has been targeting companies in the U.S. and Germany with bespoke malware designed to steal confidential information....
-

 3.5KMalware
3.5KMalwareNew ESXiArgs Ransomware Variant Emerges After CISA Releases Decryptor Tool
After the U.S. Cybersecurity and Infrastructure Security Agency (CISA) released a decryptor for affected victims to recover from ESXiArgs ransomware attacks, the...
-

 1.3KKids Online
1.3KKids OnlineOnline safety laws: What’s in store for children’s digital playgrounds?
As children’s safety and privacy online becomes a matter of increasing urgency, lawmakers around the world push ahead on new regulations in...
-

 3.6KData Breach
3.6KData BreachGitHub Breach – Hackers Stole Code Signing Certificates From Repositories
GitHub announced that it suffered a security breach in which unauthorized individuals obtained access to specific development and release planning repositories and...
-
 4.5KCyber Attack
4.5KCyber AttackNew Report Reveals NikoWiper Malware That Targeted Ukraine Energy Sector
The Russia-affiliated Sandworm used yet another wiper malware strain dubbed NikoWiper as part of an attack that took place in October 2022...
-
 1.3KIncidents
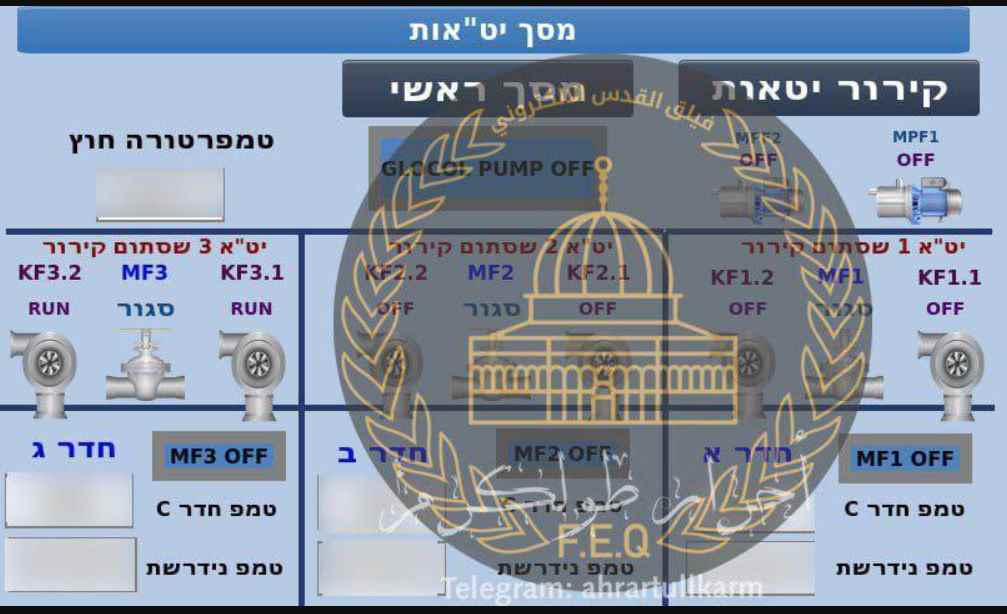
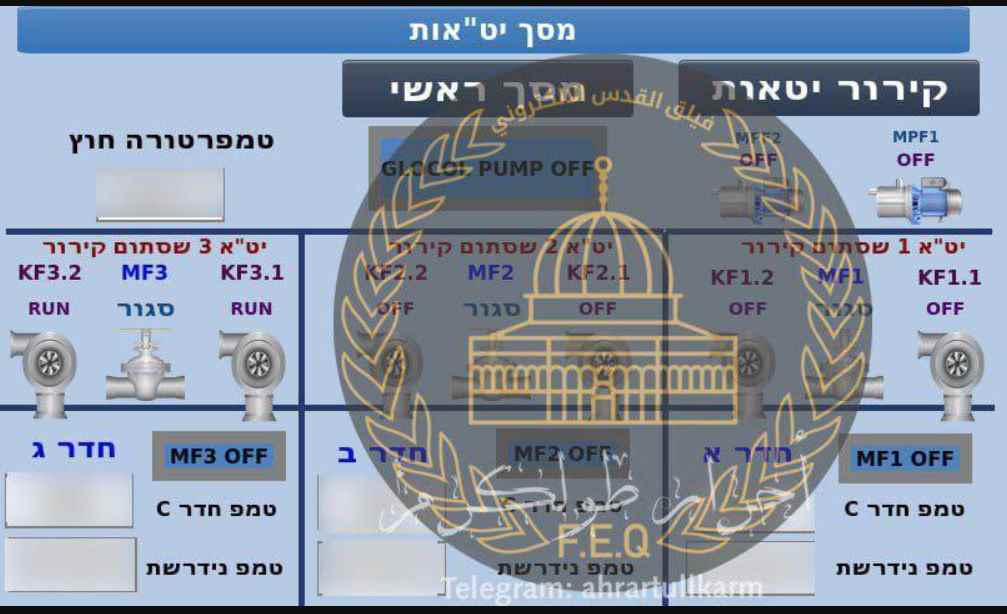
1.3KIncidentsHacker group hacks in Israeli Chemical factories
According to reports, a group of hackers has launched a massive cyberattack on Israeli chemical companies operating in the occupied territories. The...
-
 3.2KIncidents
3.2KIncidentsGitHub hacked again, GitHub Desktop and Atom repositories certificates stolen
GitHub discovered illegal access to a collection of repositories on December 7, 2022. These repositories were used in the design and development...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesSecurity Navigator Research: Some Vulnerabilities Date Back to the Last Millennium
Vulnerability analysis results in Orange Cyberdefenses’ Security Navigator show that some vulnerabilities first discovered in 1999 are still found in networks today....






