Search results for "Traffic"
-

 308Cyber Events
308Cyber EventsThe Pirate Bay suffers 40% traffic drop after domain ban in Netherlands
The Pirate Bay is in hot water once again – This time the reason is the Netherlands where authorities have blocked The...
-
 250Malware
250MalwareSimple DNSCrypt, a tool to encrypt DNS traffic on Windows and protect your privacy
DNS requests are one of the elements that most often spy on third-party applications and services. Every time we visit a website,...
-
 234Security Tools
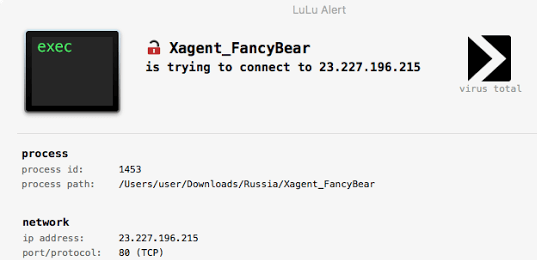
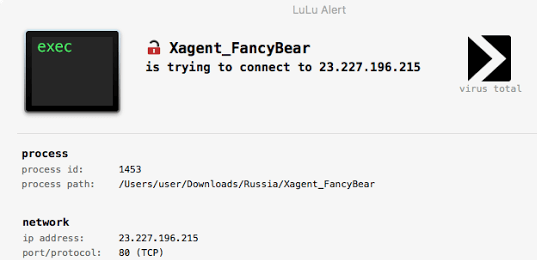
234Security ToolsLuLu – macOS Firewall That Aims To Block Unauthorized (Outgoing) Network Traffic
LuLu is the free open-source macOS firewall that aims to block unauthorized (outgoing) network traffic, unless explicitly approved by the user: Full...
-

 226MITM
226MITMNetRipper – Smart Traffic Sniffing for Penetration Testers
NetRipper is a post exploitation tool targeting Windows systems which uses API hooking in order to intercept network traffic and encryption related...
-
 257Data Security
257Data SecurityCisco’s new tool will detect malware in encrypted traffic
On January 10, Cisco’s officially released its software platform Encrypted Traffic Analytics (ETA) that can keep a check on network packet metadata...
-

 244Network Tools
244Network ToolsDNSCAP – DNS Traffic Capture
dnscap is a network capture utility designed specifically for DNS traffic. It produces binary data in pcap(3) and other format. This utility is similar to tcpdump(1),...
-
 161Incidents
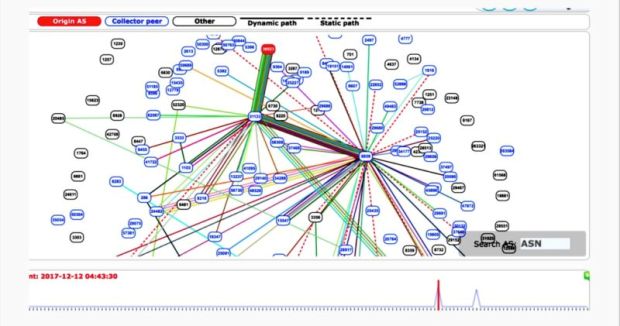
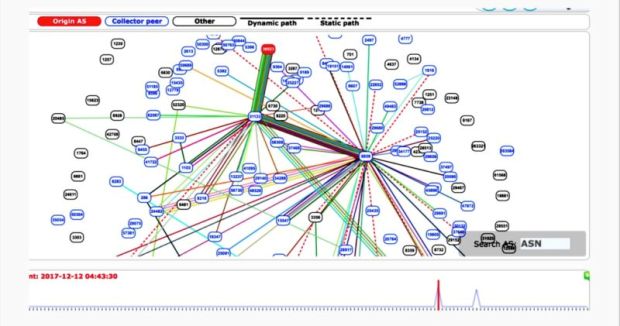
161Incidents“Suspicious” event routes traffic for big-name sites through Russia
Google, Facebook, Apple, and Microsoft all affected by “intentional” BGP mishap. Traffic sent to and from Google, Facebook, Apple, and Microsoft was...
-
 286News
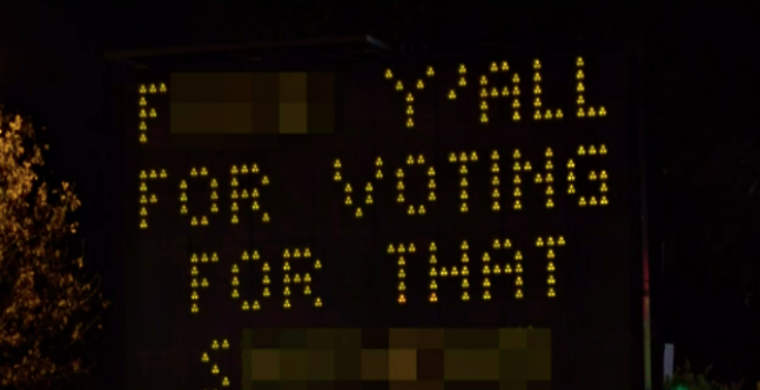
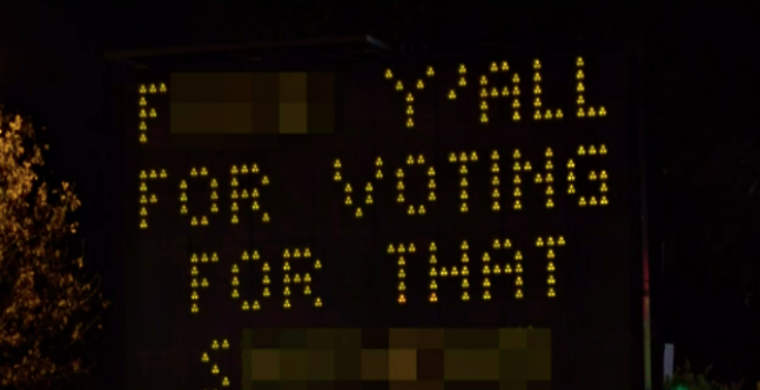
286NewsSomeone hacked this traffic sign with anti-Trump messages
A traffic sign near North Central Expressway in Dallas was hacked by unknown perpetrator on Friday (November 8th) night and defaced with an obscene...
-
 278Firewall
278FirewallBro – An Open-source Network Traffic Analyzer
Bro is a passive, open-source network traffic analyzer. It is primarily a security monitor that inspects all traffic on a link in depth...
-

 209Firewall
209FirewallOpen Source Invalid Traffic Detection: Nameles
Nameles provides an easy to deploy, scalable IVT detection and filtering solution that is proven to detect at a high level of...
-

 399Geek
399GeekVulnerability in WPA2 Protocol Allows Attackers to Intercept and Decrypt Encrypted Data Traffic
According to cyber-security researchers Frank Piessens and Mathy Vanhoef from Belgium’s Katholieke Universiteit Leuven, there is a dangerous flaw in the WPA2...
-

 179Network Tools
179Network ToolsNameles – Open Source Invalid Traffic Detection
Nameles provides an easy to deploy, scalable IVT detection and filtering solution that is proven to detect at a high level of...
-
 206Vulnerabilities
206VulnerabilitiesMetadata From IoT Traffic Exposes In-Home User Activity
Metadata from web traffic generated by smart devices installed in a home can reveal quite a lot of information about the owner’s...
-

 196Geek
196GeekHotspot Shield VPN accused of redirecting user traffic to advertisers
A renowned privacy group Center for Democracy & Technology (CDT) has accused Hotspot Shield VPN developed by AnchorFree, Inc. of violating user privacy by...
-

 273Data Security
273Data SecurityFlaws in ISP gateways let attackers remotely tap internet traffic
Defcon is the most important event for the DIY hacking community and this year too, the conference was held in the same...
-
 167Vulnerabilities
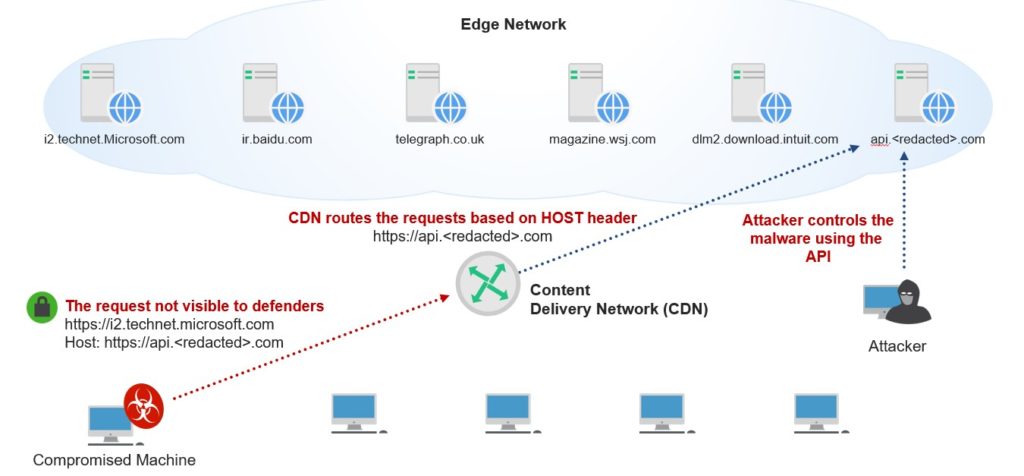
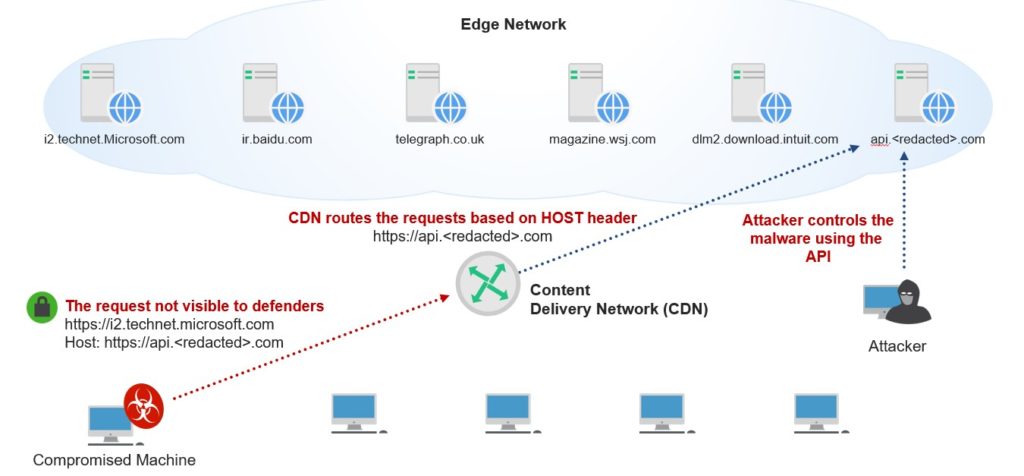
167VulnerabilitiesImplementing Malware Command and Control Using Major CDNs and High-Traffic Domains
In this blog post, we will present a new technique for domain fronting, which enables attackers to abuse Content Delivery Networks (CDNs) to...
-

 178Incidents
178Incidents751 Domains Hijacked to Redirect Traffic to Exploit Kits
On July 7, French domain registrar Gandi lost control over 751 customer domains, which had their DNS records altered to point incoming...
-

 245Hacking Tutorials
245Hacking TutorialsHow to Decrypt SSL traffic using Wireshark
SSL is one the best ways to encrypt network traffic and avoiding man in the middle attacks and other session hijacking attacks....
-

 117Incidents
117IncidentsCIA Malware Can Steal SSH Credentials, Session Traffic
WikiLeaks dumped today the documentation of two CIA hacking tools codenamed BothanSpy and Gyrfalcon, both designed to steal SSH credentials from Windows...
-

 309News
309NewsTraffic Shaping, Technique that NSA uses to spy Americans
According to the latest analysis, the NSA has media secrets “detour parts of Internet traffic that move in the global communication cables,” which...
-
 325Malware
325MalwareVault 7 Leaks : CIA Malware “OutlawCountry” Controls Linux Machine and Redirect the Victims Traffic into CIA Controlled Machine – WikiLeaks
WikiLeaks Revealed another Secret Document of CIA Malware called “OutlawCountry” that targets Linux Running Machines which Control and Redirect all outbound network...






