Search results for "Windows 10"
-

 91Password
91PasswordWindows 10 to tighten security with prominent 2FA
Microsoft is taking aim at traditional single password systems with the upcoming version of Windows, by including build in two-factor authentication according...
-

 138News
138NewsWindows 10 Technical Preview: A Spy in Disguise?
Windows 10 Technical Preview (TP), a trial version released last week, collects and transmits lots of user data to Microsoft, according to...
-

 2.3KMalware
2.3KMalwareThis new UEFI bootkit malware of size 80 Kb can hack patched Windows 11, 10 Machine with AV
Threat actors have taken note of the large number of UEFI vulnerabilities that have been found in recent years, as well as...
-
 4.5KData Breach
4.5KData BreachMicrosoft Exchange Bug Exposes ~100,000 Windows Domain Credentials
An unpatched design flaw in the implementation of Microsoft Exchange’s Autodiscover protocol has resulted in the leak of approximately 100,000 login names...
-

 619Geek
619GeekWindows licenses for under 10 HR20
Windows licenses are usually expensive. For example, for an original license of Microsoft’s “Windows 10 Pro” in the official Microsoft store 199.99$...
-

 420Lists
420Lists10 Best System Information Software: Find Full Specs Of Windows PC
The job of a good system information software is to tell you every detail about your PC’s hardware and software. Some of...
-
 374News
374Newsdeepin 15.10 Is A Beautiful Linux Distro That’ll Make Windows Users Jealous
The deepin Linux distro has a long history of different names, including Deepin, Linux Deepin, etc. This China-based distro is also known for...
-

 333Vulnerabilities
333VulnerabilitiesA new Windows vulnerability affects versions 8 and 10
The flaw is being exploited by at least two malicious actors; Users are encouraged to install updates as soon as they are....
-

 356Lists
356Lists10 Best And Free Music Player Apps For Windows [2019 Edition]
People who have spent a lot of money to curate their music collection are always in search of a best and free...
-
 174News
174NewsThis Chrome Bug Can Freeze Your Windows PC With 100% Disk Usage
Google Chrome is already known for slowing down computers, ultimately leading to 100% disk usage. On top of that, we now have...
-

 216Hacked
216Hacked100,000 Windows Users In China Hit By New Ransomware Strain
A ransomware that encrypts personal files and then demands 110 yuan (~$16) in ransom has affected over 100,000 Windows PC in China. The...
-

 267Pentest Linux Distributions
267Pentest Linux DistributionsCAINE 10.0 – GNU/Linux Live Distribution For Digital Forensics Project, Windows Side Forensics And Incident Response
CAINE (Computer Aided INvestigative Environment) is an Italian GNU/Linux live distribution created as a Digital Forensics project. Currently, the project manager is Nanni Bassetti...
-
 199Malware
199MalwareSmokeLoader Malware Abusing MS Office Document and Compromise Windows 8 ,10 Users PC
A dangerous malicious campaign SmokeLoader Malware abusing MS office document that spreading via spam Email and targetting windows 8 and above users....
-
 373Lists
373Lists10 Best Free PDF Reader Software For Windows (2018 Edition)
As our basic PDF reading needs are fulfilled by web browsers, the need for a free PDF reader software is decreasing. Still,...
-
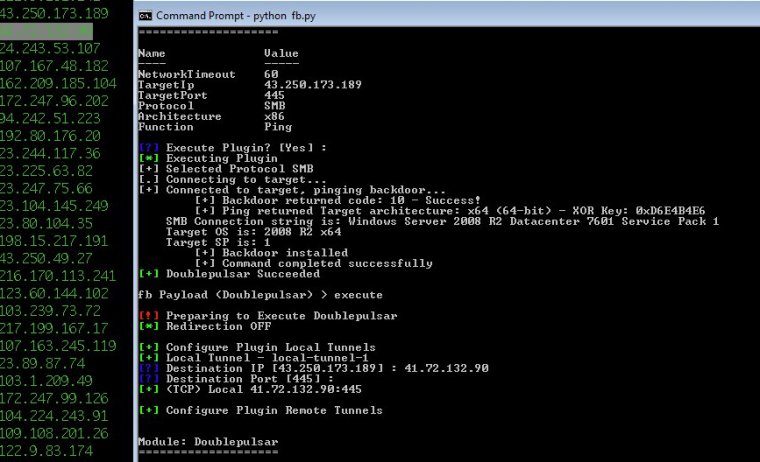
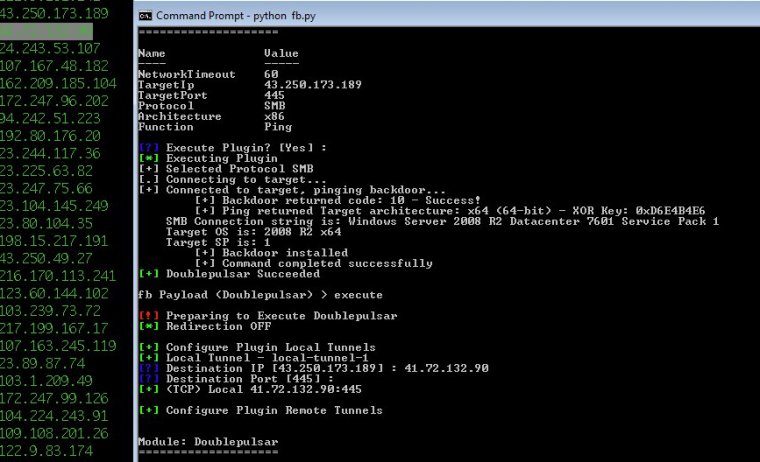 137Vulnerabilities
137Vulnerabilities10,000 Windows computers may be infected by advanced NSA backdoor
Did script kiddies use DoublePulsar code released by NSA-leaking Shadow Brokers? Security experts believe that tens of thousands of Windows computers may...
-

 259How To
259How ToTop 10 Pentesting Tools You Can Use in Windows
NMAP : Nmap is a free tool for network discovery and security auditing. It can be used for host discover, open ports,...
-
 326How To
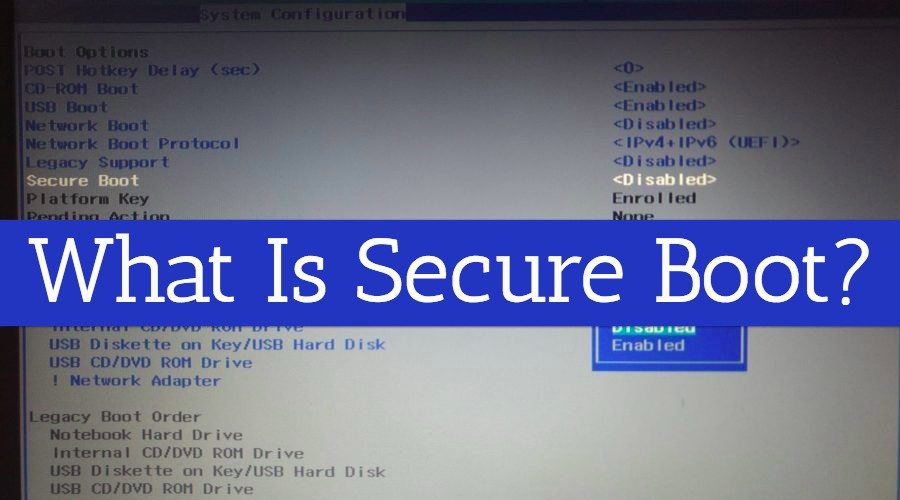
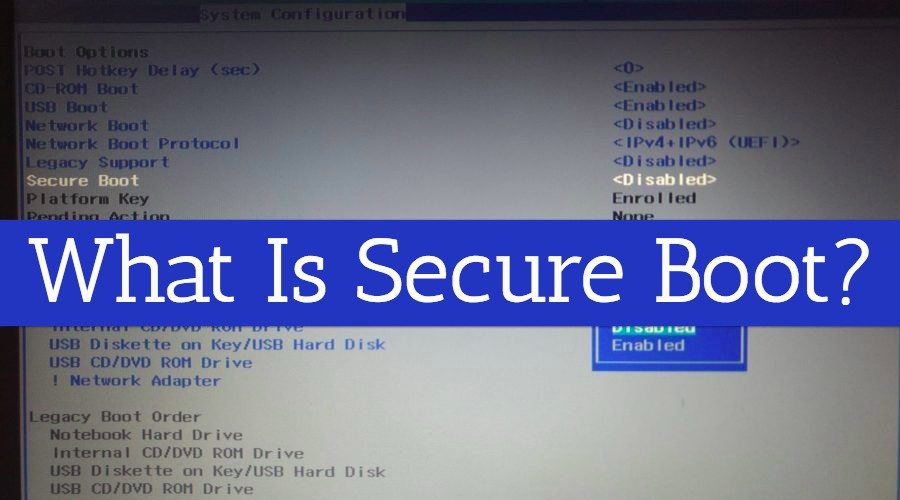
326How ToHow To Enable/Disable Secure Boot In Windows 8, 8.1, And 10?
Short Bytes: Windows 8 and later versions of Windows come with UEFI Firmware settings which allow a user to disable any external...
-

 233Lists
233ListsTop 10 Free Registry Cleaners For Microsoft Windows PC
Short Bytes: Registry Cleaners are the software which does the job of removing outdated registry entries from Windows registry. These registry entries...
-

 205Geek
205GeekWindows10 Anniversary Update Causing Devices to Crash – Yet Again!
After messing around with users’ webcams the Microsoft’s Windows10 Anniversary Update is now causing crash whenever an Amazon Kindle is connected through USB. Microsoft...
-

 303Data Security
303Data Security10 Best Password Cracking Tools Of 2016 | Windows, Linux, OS X
Short Bytes: Password cracking is an integral part of digital forensics and pentesting. Keeping that in mind, we have prepared a list...
-

 329Hacked
329Hacked9 Out Of 10 Windows Security Flaws Could Be Avoided By Just Removing Admin Rights
Short Bytes: The security firm Avecto has just released its security report on Windows operating system. The report outlines an important result...






