Search results for "Windows"
-
 2.8KVulnerabilities
2.8KVulnerabilitiesNew Variant of DLL Search Order Hijacking Bypasses Windows 10 and 11 Protections
Security researchers have detailed a new variant of a dynamic link library (DLL) search order hijacking technique that could be used by...
-

 1.8KMalware
1.8KMalwareNew Go-Based JaskaGO Malware Targeting Windows and macOS Systems
A new Go-based information stealer malware called JaskaGO has emerged as the latest cross-platform threat to infiltrate both Windows and Apple macOS...
-
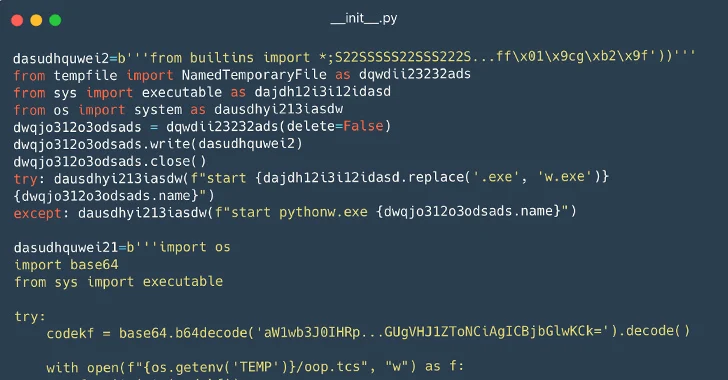
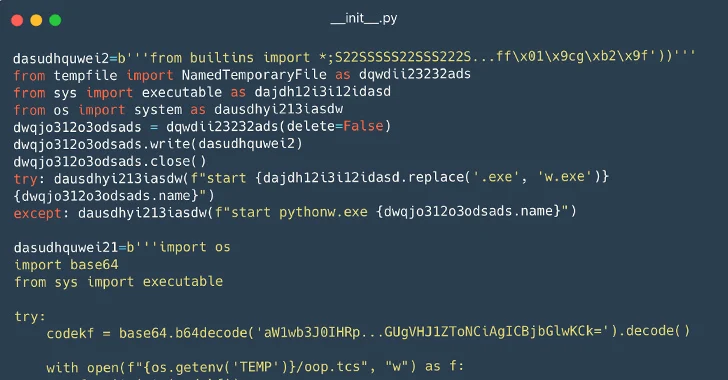 3.9KMalware
3.9KMalware116 Malware Packages Found on PyPI Repository Infecting Windows and Linux Systems
Cybersecurity researchers have identified a set of 116 malicious packages on the Python Package Index (PyPI) repository that are designed to infect...
-

 733Vulnerabilities
733VulnerabilitiesHackers Can Exploit ‘Forced Authentication’ to Steal Windows NTLM Tokens
Cybersecurity researchers have discovered a case of “forced authentication” that could be exploited to leak a Windows user’s NT LAN Manager (NTLM)...
-

 4.3KCyber Attack
4.3KCyber AttackNew BiBi-Windows Wiper Targets Windows Systems in Pro-Hamas Attacks
Cybersecurity researchers have warned about a Windows version of a wiper malware that was previously observed targeting Linux systems in cyber attacks...
-
 4.5KMalware
4.5KMalwareResearchers Find 34 Windows Drivers Vulnerable to Full Device Takeover
As many as 34 unique vulnerable Windows Driver Model (WDM) and Windows Driver Frameworks (WDF) drivers could be exploited by non-privileged threat...
-
 937Cyber Attack
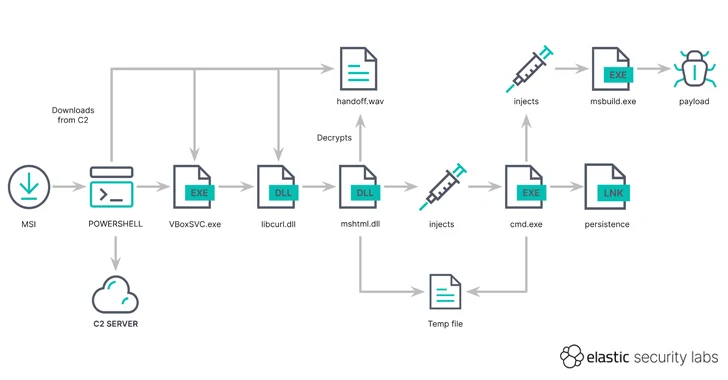
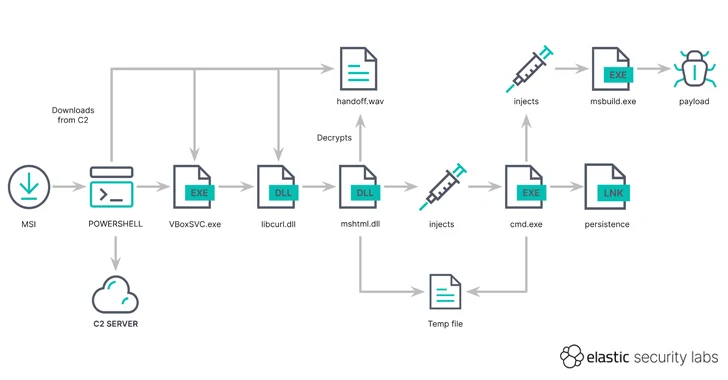
937Cyber AttackHackers Using MSIX App Packages to Infect Windows PCs with GHOSTPULSE Malware
A new cyber attack campaign has been observed using spurious MSIX Windows app package files for popular software such as Google Chrome,...
-
 2.5KVulnerabilities
2.5KVulnerabilitiesCISA Warns of Active Exploitation of JetBrains and Windows Vulnerabilities
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added two security flaws to its Known Exploited Vulnerabilities (KEV) catalog due...
-

 2.3KMalware
2.3KMalwareNew ZenRAT Malware Targeting Windows Users via Fake Password Manager Software
A new malware strain called ZenRAT has emerged in the wild that’s distributed via bogus installation packages of the Bitwarden password manager....
-

 1.6KVulnerabilities
1.6KVulnerabilitiesN-Able’s Take Control Agent Vulnerability Exposes Windows Systems to Privilege Escalation
A high-severity security flaw has been disclosed in N-Able’s Take Control Agent that could be exploited by a local unprivileged attacker to...
-

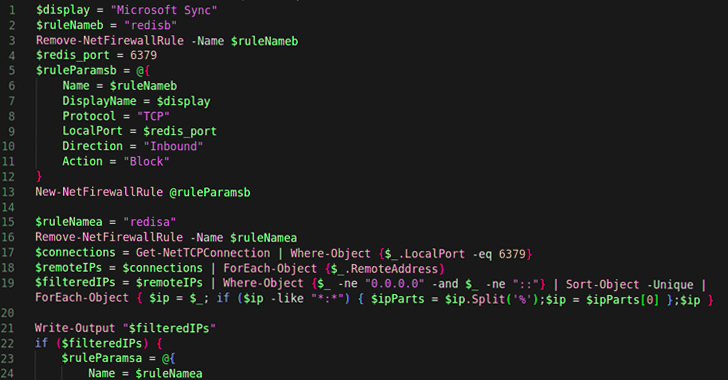
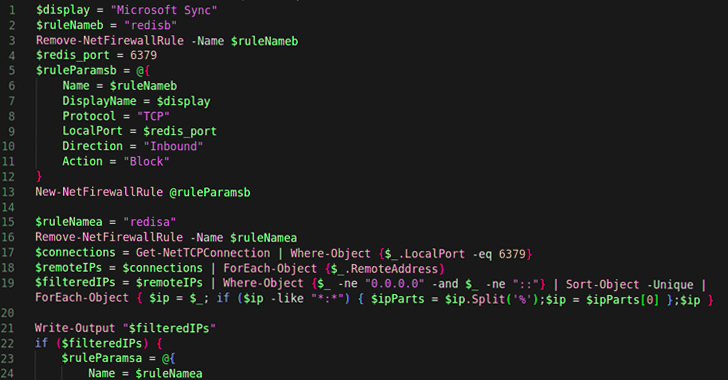
 5.0KMalware
5.0KMalwareCybercriminals Using PowerShell to Steal NTLMv2 Hashes from Compromised Windows
A new cyber attack campaign is leveraging the PowerShell script associated with a legitimate red teaming tool to plunder NTLMv2 hashes from...
-

 4.7KMalware
4.7KMalwareHackers Can Exploit Windows Container Isolation Framework to Bypass Endpoint Security
New findings show that malicious actors could leverage a sneaky malware detection evasion technique and bypass endpoint security solutions by manipulating the...
-
 1.1KData Security
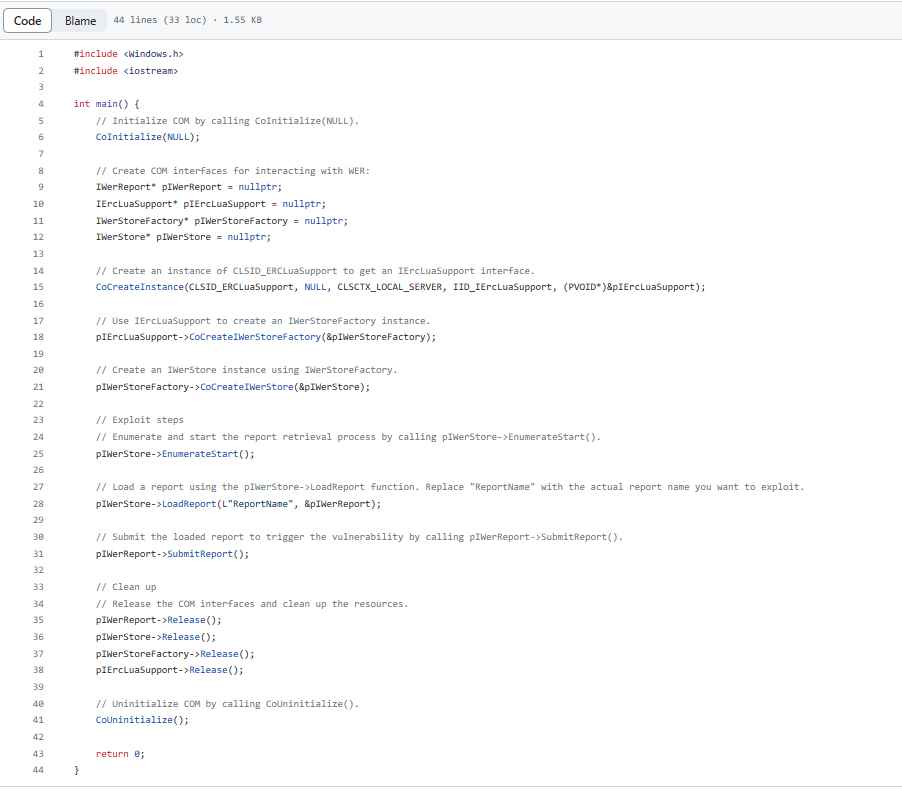
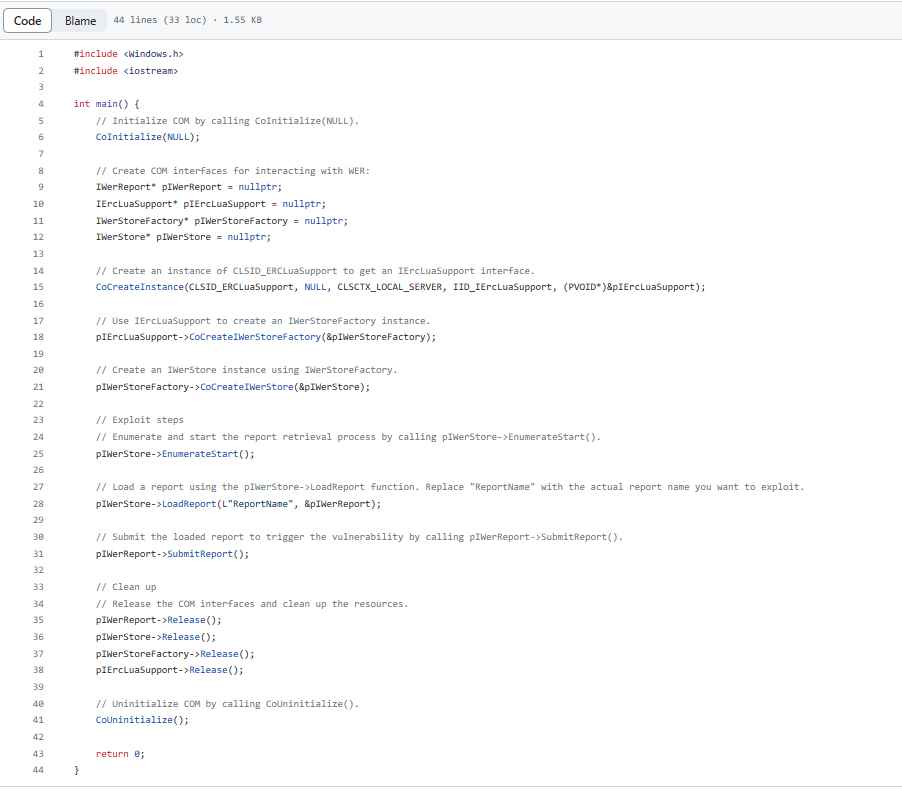
1.1KData SecurityThis C++ code gets you administrator rights on vulnerable Windows 10 machine
CVE-2023-36874 is not just any vulnerability; rather, it is a zero-day that is being actively exploited. This indicates that the vulnerability was...
-
 3.2KMalware
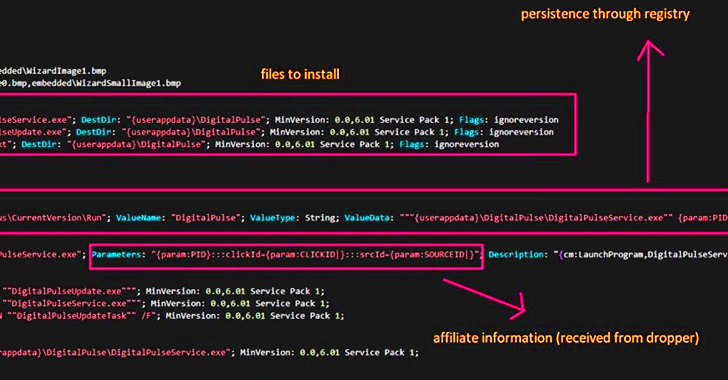
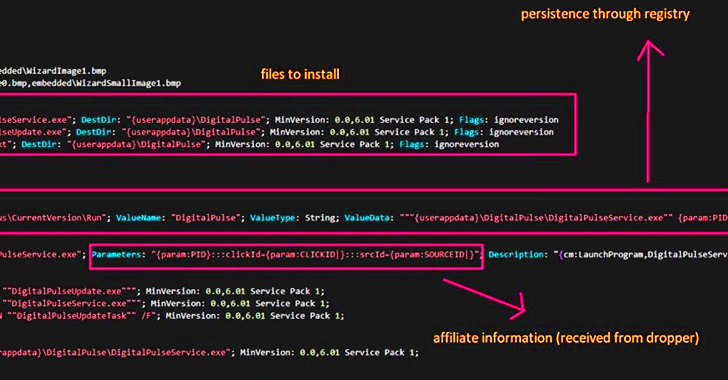
3.2KMalwareThis Malware Turned Thousands of Hacked Windows and macOS PCs into Proxy Servers
Threat actors are leveraging access to malware-infected Windows and macOS machines to deliver a proxy server application and use them as exit...
-
 3.8KVulnerabilities
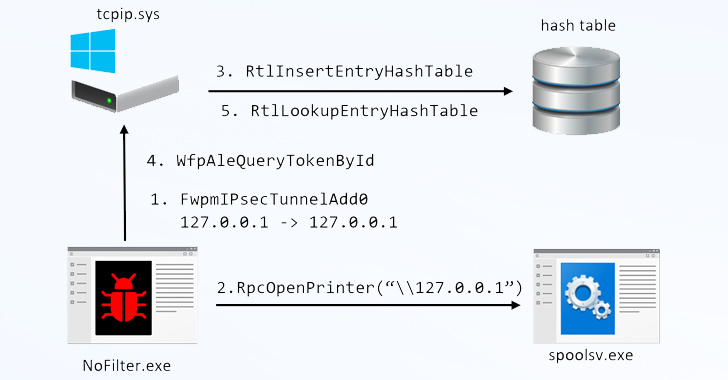
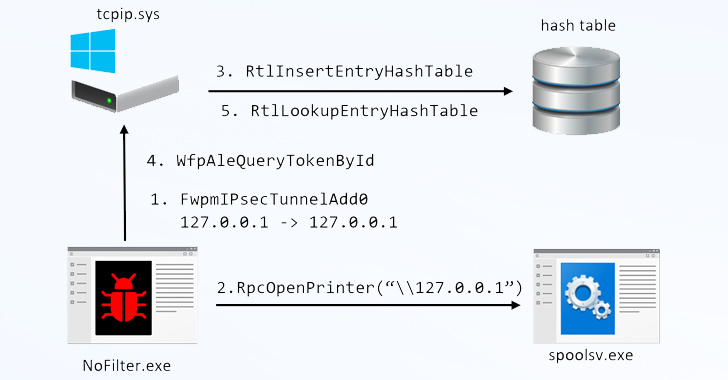
3.8KVulnerabilitiesNoFilter Attack: Sneaky Privilege Escalation Method Bypasses Windows Security
A previously undetected attack method called NoFilter has been found to abuse the Windows Filtering Platform (WFP) to achieve privilege escalation in...
-
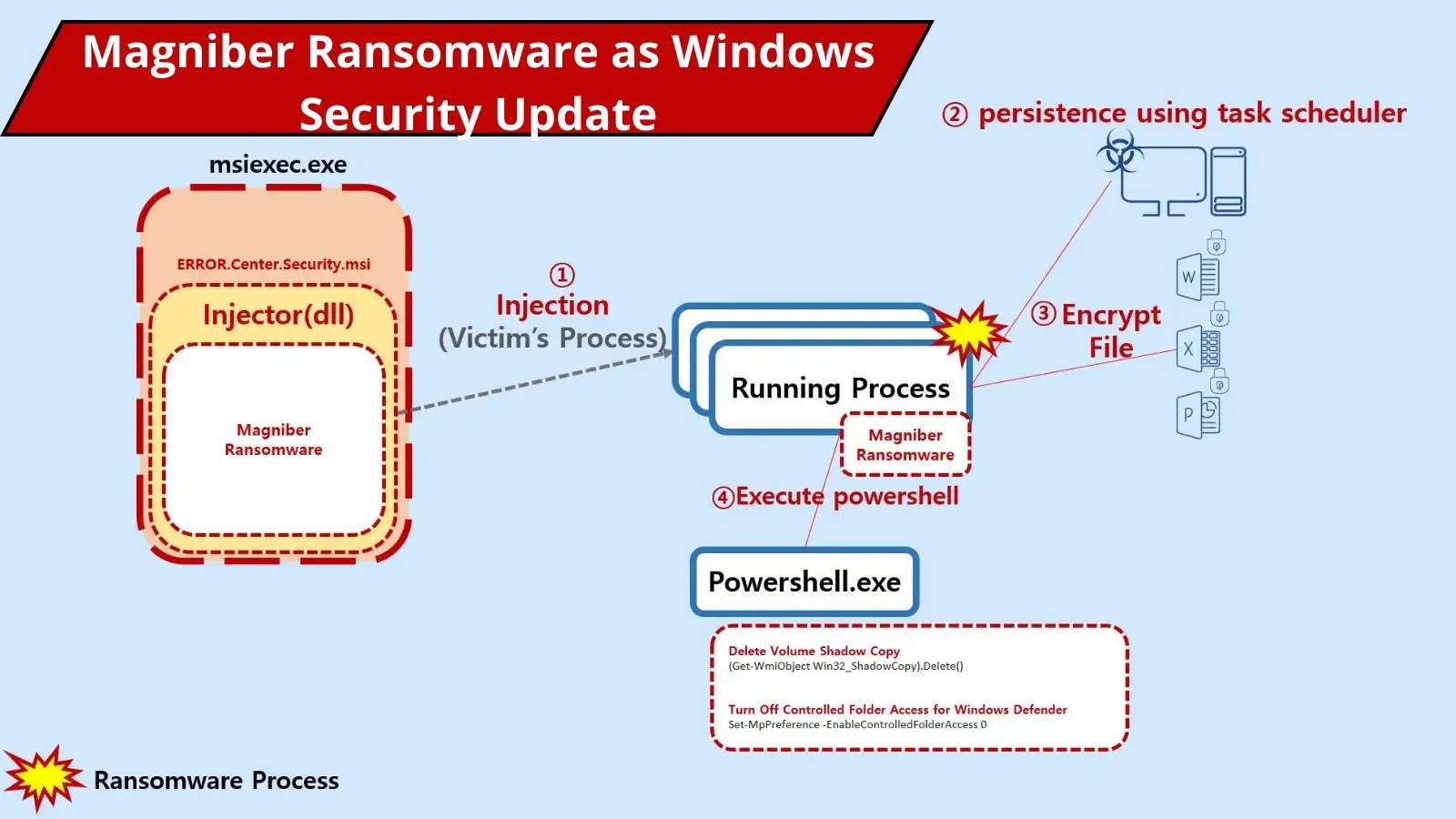
 3.8KRansomware
3.8KRansomwareHackers Deliver Magniber Ransomware Disguised as Windows Security Update
Magniber Ransomware was first detected in late 2017; it targeted South Korean users through malvertising attacks using the Magnitude Exploit Kit. It had...
-
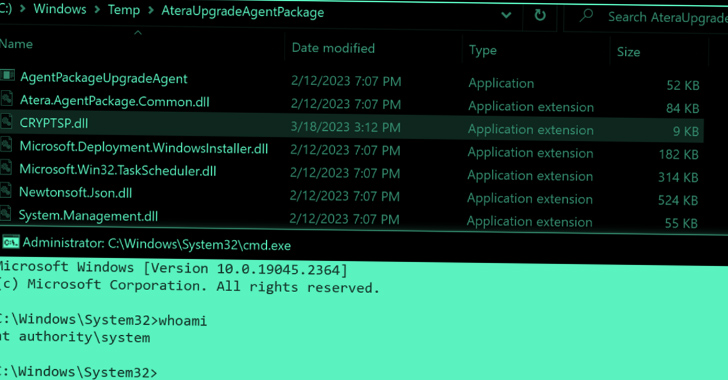
 730Vulnerabilities
730VulnerabilitiesCritical Zero-Days in Atera Windows Installers Expose Users to Privilege Escalation Attacks
Zero-day vulnerabilities in Windows Installers for the Atera remote monitoring and management software could act as a springboard to launch privilege escalation...
-
 2.3KVulnerabilities
2.3KVulnerabilitiesNew P2PInfect Worm Targeting Redis Servers on Linux and Windows Systems
Cybersecurity researchers have uncovered a new cloud targeting, peer-to-peer (P2P) worm called P2PInfect that targets vulnerable Redis instances for follow-on exploitation. “P2PInfect...
-
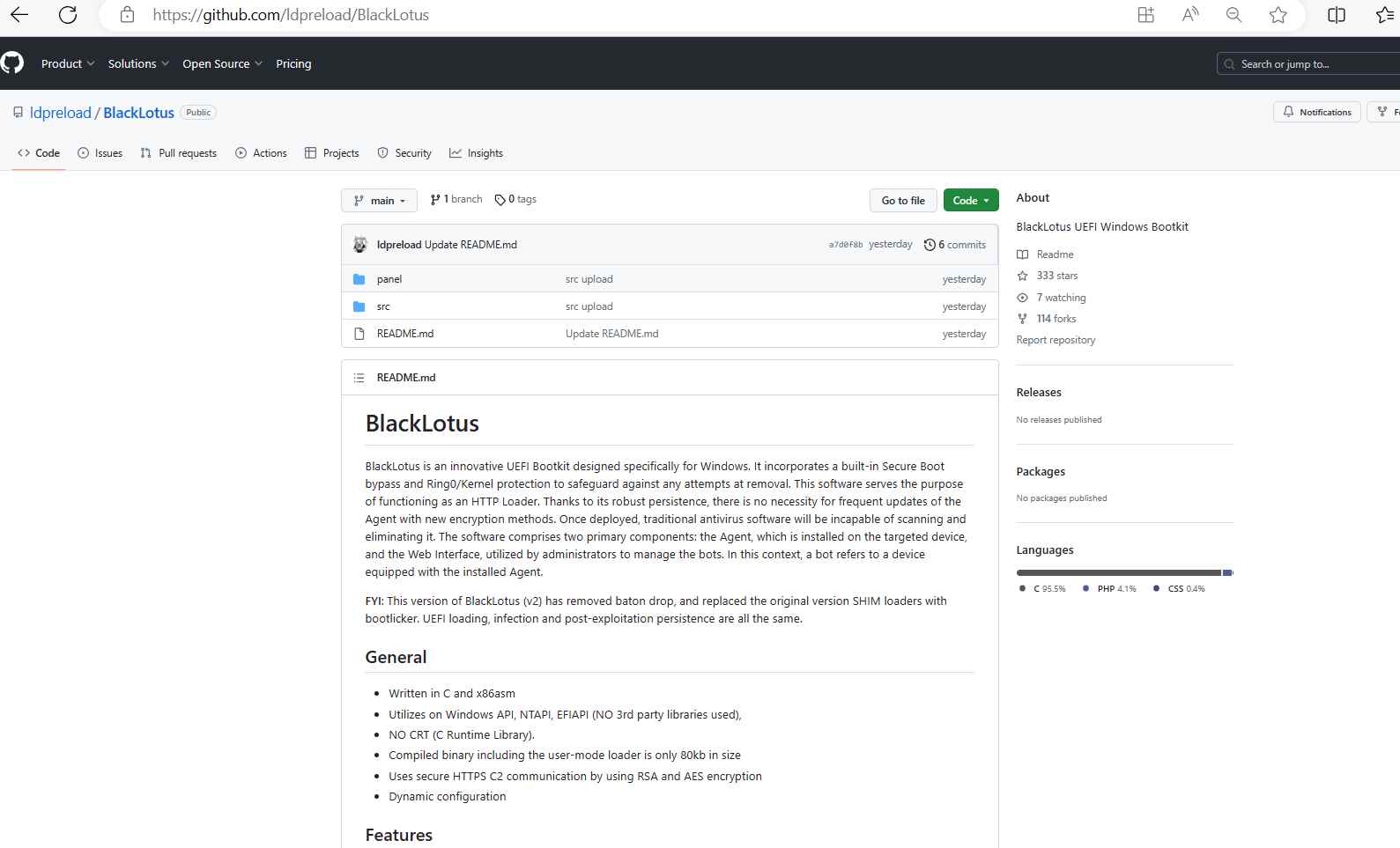
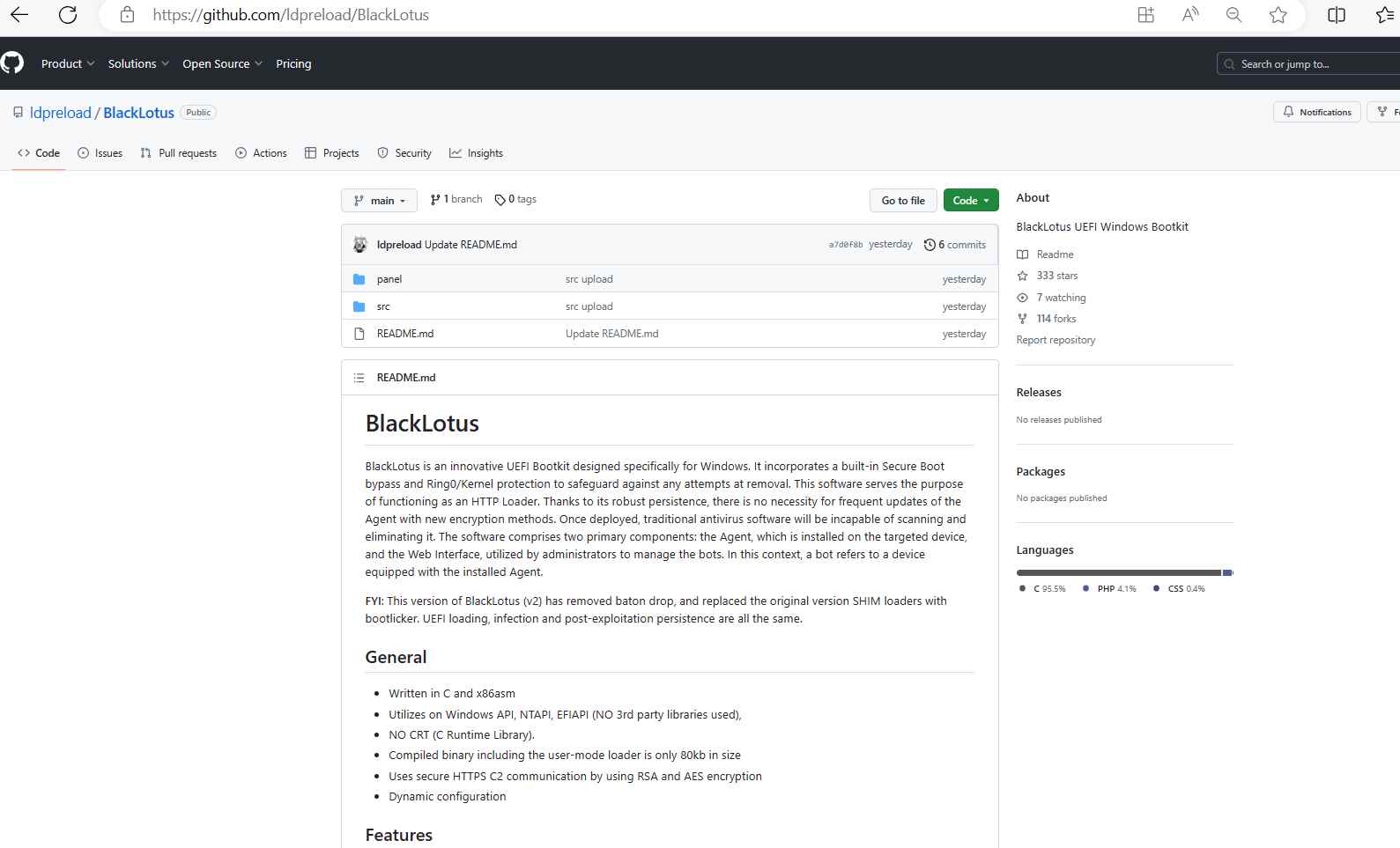 2.8KMalware
2.8KMalwareThis free UEFI malware code can hack Windows machine forever, even if hard disk is removed
The Blacklotus bootkit was developed expressly for Windows, and it first appeared on hacker forums in October of the previous year. It...
-

 2.1KMalware
2.1KMalwareHackers Exploit Windows Policy Loophole to Forge Kernel-Mode Driver Signatures
A Microsoft Windows policy loophole has been observed being exploited primarily by native Chinese-speaking threat actors to forge signatures on kernel-mode drivers....
-
 795Cyber Attack
795Cyber AttackBeware of Big Head Ransomware: Spreading Through Fake Windows Updates
A developing piece of ransomware called Big Head is being distributed as part of a malvertising campaign that takes the form of...






