Search results for "Wireless"
-

 459How To
459How ToHack Someone’s Bluetooth And Other Wireless Tools Using Kali Linux
Blooover is performing the Bluebug attack(Bluetooth sniffer Linux). Whilst you intend to install the software, you have to be using a phone...
-
Hackers Repository
Cracking WPA/WPA2 WPA Key Wireless Access Point Passphrase
In this article we will learn how to brute force a WPS key using Airodump-ng, Reaver with Pixie Dust addon if your running...
-

 287How To
287How ToHijacker – Graphical User Interface For Wireless Auditing Tools In Android
Hijacker is a Graphical User Interface for the wireless auditing tools airodump-ng, aireplay-ng and mdk3. It offers a simple and easy UI...
-

 281News
281NewsMcDonald’s Drive-Thru Intercom Wireless Frequency System Hacked
The McDonald’s is quite popular among young and adults alike. Every day the franchise receives a huge number of Big Mac lovers...
-

 256News
256NewsHackers to show how to hack wireless keyboard from 250 feet away
Wireless keyboards of 8 high-profile manufacturers are vulnerable to attacks leading to undetectable spying! A Wireless keyboard offers portability allowing users not to...
-

 100Data Security
100Data SecurityRadio Hack Steals Keystrokes from Millions of Wireless Keyboards
YOU SHOULD BE able to trust your wireless keyboard. And yet security researchers have been warning people to be suspicious of wireless...
-

 259Vulnerabilities
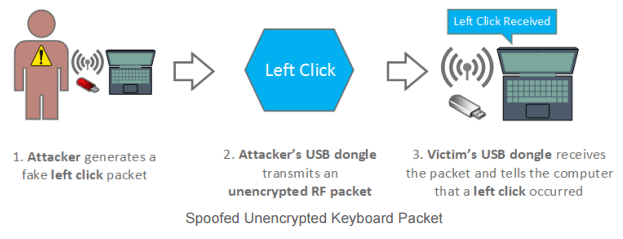
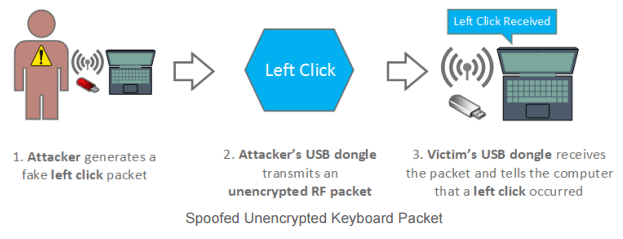
259VulnerabilitiesKeySniffer Flaw Lets Attackers Log and Inject Keystrokes on Wireless Keyboards
The security flaw is technically unpatchable. Attackers can intercept keystrokes from wireless keyboards as they are transmitted to nearby computers, can log sensitive...
-

 81Data Security
81Data SecurityFoul-mouthed worm takes control of wireless ISPs around the globe
Active attack targets Internet-connected radios from Ubiquiti Networks. ISPs around the world are being attacked by self-replicating malware that can take complete control...
-

 102Data Security
102Data SecurityBillions at risk of computer hack due to wireless mouse
Researchers say that wireless mouse could expose billions of computers to hacking Bastille Networks, a startup cyber security company that looks to better...
-
 135Data Security
135Data SecurityMousejack attack – Hijack Wireless Mouse/Keyboard Dongles from 100 meters to control PCs
Mousejack attack – Researchers at Bastille firm demonstrated how to hack computers by exploiting a flaw in many wireless mouse and keyboard...
-

 259News
259NewsHacker Shows How To Hack Wireless Burglar Alarm System Like A Pro
SimpliSafe Alarm Systems’ Inherent Vulnerability Exposes Hazards of Wireless Security Devices Digital age has brought along countless blessings and conveniences for the...
-

 190Data Security
190Data SecurityRemotely Disabling a Wireless Burglar Alarm
Countless movies feature hackers remotely turning off security systems in order to infiltrate buildings without being noticed. But how realistic are these...
-

 215Geek
215GeekApple to Introduce Wireless Charging Technology with a Different Approach
Apple is working on wireless charging technology with aim to revolutionise the way of charging electronic devices Last year, Nikola Labs launched an...
-
 102Data Security
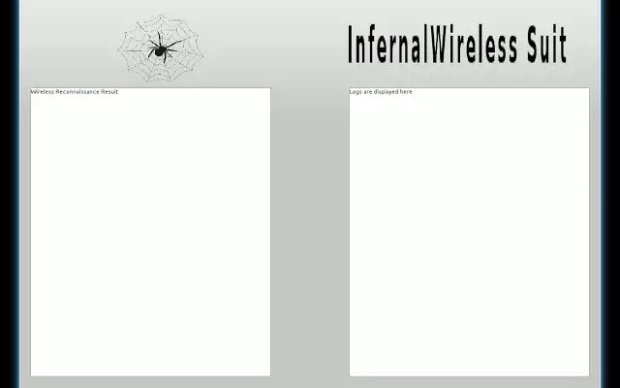
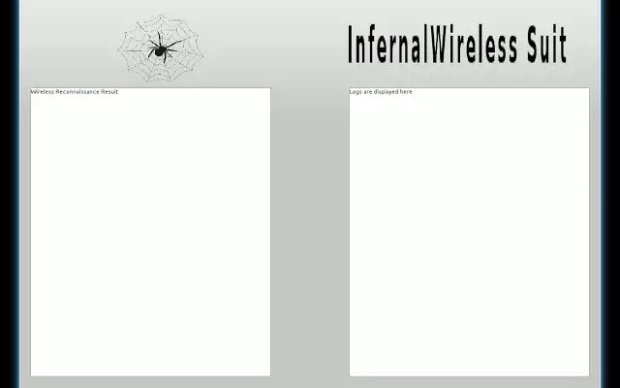
102Data SecurityThe Infernal-Twin tool, easy hacking wireless networks
The Infernal-Twin is an automated tool designed for penetration testing activities, it has been developed to automate the Evil Twin Attack. The Infernal-Twin...
-

 318Data Security
318Data SecurityHacker Steals, Drives Away Jaguar XFR Exploiting Flaw in Wireless System
A silver Jaguar XFR parked in a parking lot in Auckland, New Zealand was stolen with the help of a hacking device that sends...
-

 179Data Security
179Data SecurityHacking Wireless Printers With Phones on Drones
YOU MIGHT THINK that working on a secured floor in a 30-story office tower puts you out of reach of Wi-Fi hackers...
-
 151Hacking Tutorials
151Hacking Tutorials6 Ways to Secure a Wireless Wi-Fi Network
Wireless Networking (Wi-Fi) has made it so easy for anyone to use Internet on your computer, mobile phones, tablets and other wireless...
-

 325Geek
325GeekMan 3D prints a wirelessly power-driven desk lamp inspired by Tesla
It was more like a mission for engineer, David Choi, to 3D print something inspired by Nikola Tesla’s wireless power transmission something...
-

 199Geek
199GeekGoogle wants to be your wireless carrier with encrypted connection
For all of you who want to know what currently Google is planning to work on, the answer is “Project Fi”— Now...
-

 110Malware
110MalwareWireless attacks against ‘air gapped’ targets are possible, Israeli team claims
A team of Israeli researchers has demonstrated a way to hack into an ultra-secure air-gapped network, install malware, and retreive information -...
-

 370Cyber Crime
370Cyber CrimeWi‑Fi light bulbs in security alert over wireless blackout hack
A high-profile ‘connected’ lighting system had a critical vulnerability which allowed attackers to take control of the entire system, switching off light...






