Search results for "attack"
-

 130Data Security
130Data SecurityNew DDoS attack uses smartphone browsers to flood site with 4.5bn requests
Researchers have found that smartphone browsers can deliver a powerful flooding attack. Researchers suspect a mobile advertising network has been used to...
-

 231Data Security
231Data SecurityNew Attacks Recall Old Problems with Browser Cookies
In case didn’t know or need a reminder, browser cookies aren’t exactly impervious to attack. The DHS-sponsored CERT at the Software Engineering...
-

 236Password
236PasswordiOS 9 security flaw lets attackers access device through Siri
Apple’s iOS 9 contains a security flaw that lets cybercriminals gain limited access to a device through Siri.
-
 174Vulnerabilities
174VulnerabilitiesSecurity wares like Kaspersky AV can make you more vulnerable to attacks
Antivirus applications and other security software are supposed to make users more secure, but a growing body of research shows that in...
-

 334Cyber Events
334Cyber EventsUS Navy Developing Cyber Protection System to Protect Ships from Cyberattacks
The experts over at United States Navy are busy in the development of a cyber-protection system, codenamed RHIMES (the Resilient Hull, Mechanical,...
-

 182Vulnerabilities
182VulnerabilitiesWestern Digital My Cloud Devices Can Be Hacked by Local or Remote Attackers
Security researchers at VerSprite have tested and discovered a few vulnerabilities in Western Digital’s My Cloud NAS (Network Attached Storage) hard drive,...
-

 94Malware
94MalwareApple removes hundreds of malicious apps after major malware attack
Apple has removed more than 300 malicious apps after confirming the first major breach to its iOS app store.
-
 342News
342NewsPhishing Attack Causes Bitcoin Payment Processor BitPay to Lose $1.8M
BitPay the Atlanta-based Bitcoin payment processor had been hit by a massive phishing attack costing the company $1.8 million. Verified by the...
-

 139Malware
139MalwareNew PoS Trojan Can Download Other Malware, Launch DDOS Attacks
The world of computer viruses and antivirus solutions is in a constant change, with cyber-crooks evolving their code and cyber-security firms trying...
-

 302Hacked
302Hacked“seL4” is an Unhackable Kernel for Keeping All Computers Safe From Cyberattack
Short Bytes: The Australian national research agency Data61 has developed an unhackable kernel named seL4 and proved its unhackable property mathematically. The kernel...
-
 128Cyber Crime
128Cyber CrimeHackers Using Amazon As A Bait For Phishing Attacks
A new phishing campaign has been doing the rounds on the Internet in which hackers are using Amazon UK’s fake email message...
-

 121Vulnerabilities
121VulnerabilitiesAndroid’s 5.x Lock Screen may be bypassed by attackers
Android devices may be protected by a lock screen which requires some form of authentication before access to most phone features, its...
-

 331Data Security
331Data SecurityCisco Routers Vulnerable To Malware Attacks Via Backdoor Firmware Installation
It has always been believed that Cisco routers being used in the enterprise environment could be hacked via installation of backdoor firmware,...
-
 275Incidents
275IncidentsDD4BC Hacker Group Blackmails Companies for Bitcoin Using DDOS Attacks
A group of hackers that goes under the name of DD4BC, first spotted in September 2014, has recently intensified its activity, launching...
-

 166Vulnerabilities
166VulnerabilitiesMicrosoft Patches Graphics Component Flaw Under Attack
Microsoft today patched a vulnerability in its graphics component present in Windows, Office and Lync that has been publicly attacked, and is...
-

 137Vulnerabilities
137VulnerabilitiesWhatsApp “MaliciousCard” Vulnerabilities Allowed Attackers to Compromise Hundreds of Millions of WhatsApp Users
WhatsApp Web is a web-based extension of the WhatsApp application on your phone. The web application mirrors all messages sent and received,...
-

 178Vulnerabilities
178VulnerabilitiesAttackers bundle an old version of TeamViewer to exploit vulnerability
We’re used to seeing malware that exploits unpatched vulnerabilities in software. But in a new twist attackers are bundling an old version...
-

 114Vulnerabilities
114VulnerabilitiesAttacker Compromised Mozilla Bug System, Stole Private Vulnerability Data
Security experts constantly tell users not to reuse passwords on multiple accounts, but the message often falls on deaf ears. Now, officials at...
-
 243How To
243How ToSentry – Prevents Brute Force Attacks Against SSH, FTP, SMTP and More
Supporting OS (operating system) FreeBSD Mac OS X Linux (CentOS, Debain, Ubuntu) Download Command: bash || sh export SENTRY_URL=https://raw.githubusercontent.com/msimerson/sentry/master/sentry.pl curl -O $SENTRY_URL...
-
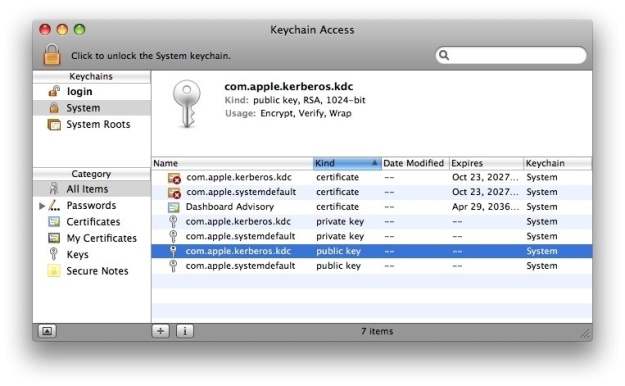
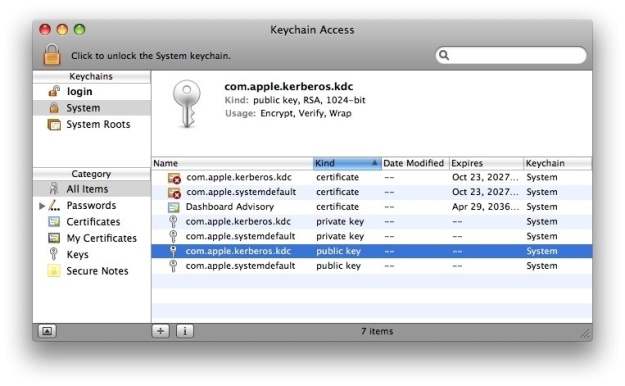 221Vulnerabilities
221VulnerabilitiesAttackers Can Steal Passwords from the Mac Keychain via Email or SMS
It didn’t even take a day for security researchers to find a serious way of exploiting the mechanism through which user clicks...
-

 184Cyber Events
184Cyber EventsAnonymous Offshoot GhostSec Launches Another Phase of Attacks Against ISIS
Another phase of an online battle against the members of the so-called Islamic State (IS, previously ISIS/ISIL) group has been launched throughout the world by...






