Search results for "attack"
-

 329Data Security
329Data SecurityHeartbleed now reforms into “Cupid” attack targeting Wi-Fi networks and Android
If you thought that Heartbleed is out of date now, and the whole cyber world is secure, then you have to change...
-

 181How To
181How ToRouter attacks: Five simple tips to lock criminals out
Cybercriminals always look for the weakest link when planning their attacks – and failings in home routers can allow another "way in"....
-

 129Cyber Crime
129Cyber CrimeActivision Blizzard attacks hidden market in game “cheats”
Activision Blizzard - makers of game hits such as Call of Duty and World of Warcraft - have taken “aggressive” legal moves...
-
 437Opinion
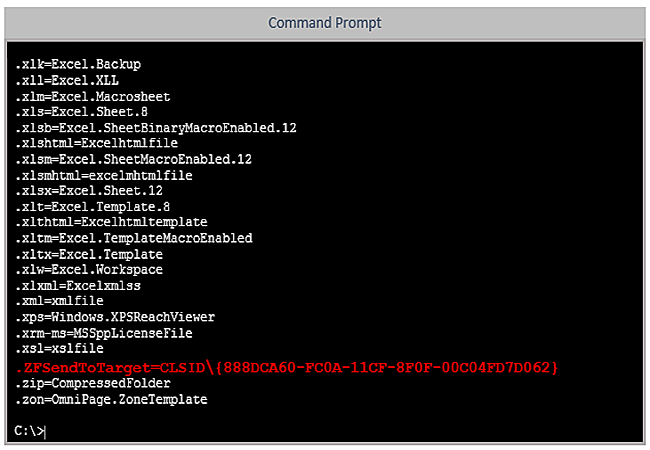
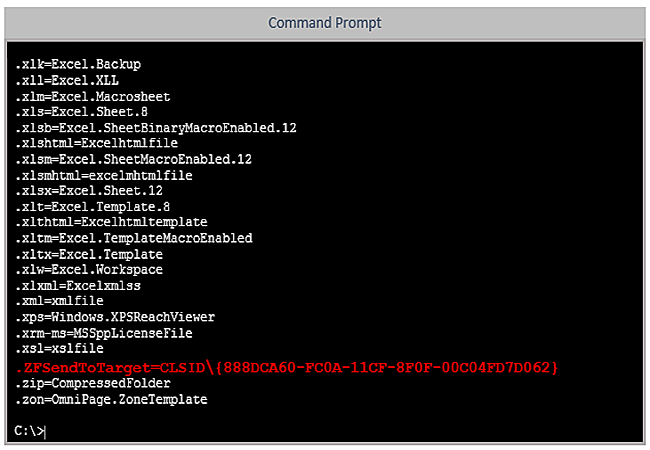
437OpinionSupport Scam Using (MS‑)DOS* Attack
The never-ending Windows support scam often misrepresents obsolete MS-DOS utilities. But three simple rules will bypass most of that social engineering.
-
 86Cyber Crime
86Cyber CrimeDogecoin vault vanishes after attack – and “mysterious withdrawals”
The popular online wallet site Dogevault is offline after attackers destroyed data on the site. The impact on user funds is unknown...
-

 109Cyber Crime
109Cyber CrimeNetwork structure must change to resist cyber attacks, warns Dr. Eric Cole
Infosecurity expert Dr Eric Cole is to urge companies to take a close look at their network structure, and change it to...
-
 119Malware
119MalwareFake Facebook app attack can lead to your Android being spied upon, and your bank account being hacked
Hackers are using a notorious banking Trojan horse to display a bogus message from Facebook, in an aggressive attempt to infect Android...
-

 203Cyber Crime
203Cyber CrimeCanadian teenager is first to be arrrested for Heartbleed bug attack
A 19-year-old teenager in London, Ontario, Canada has become the first criminal to be arrested for exploiting the ‘Heartbleed’ bug to steal...
-

 186Malware
186MalwareInterview: Windigo victim speaks out on the ‘stealth’ malware that attacked his global company
Francois Gagnon is a Canadian business owner who was targeted because his company had lots of servers, and many customers - victims...
-

 93Cyber Crime
93Cyber CrimeSwooping robot attack which felled triathlete “may be work of hackers”
A competitor in an Australian triathlon was hospitalized with injuries and “pieces of propeller in her head” after a drone plunged from...
-

 103Cyber Crime
103Cyber CrimeAttack on Samsung’s Boxee TV service leaks 158,000 passwords and emails
An attack on the forums for the Boxee internet-TV service has yielded 158,000 customer passwords - and what appears to be email...
-

 203Cyber Events
203Cyber EventsAnonymous threatens cyberattack on Albuquerque Police Department for shooting and killing homeless man
Anonymous threatens cyberattack on Albuquerque Police Department for shooting and killing mentally ill homeless man James M. Boyd. File photo of mentally ill...
-
 81Cyber Crime
81Cyber CrimeOver 500,000 PCs attacked every day after 25,000 UNIX servers hijacked by Operation Windigo
Malware researchers at ESET have uncovered a widespread cybercriminal operation that has seized control of tens of thousands of Unix servers. Learn...
-
 128Malware
128Malware“You have cancer” phishing attack shows how low cybercriminals will go
A “particularly unpleasant” phishing email purporting to be the results of a blood count report showing that the recipient may have cancer...
-

 244News
244NewsPowerful DDoS attack by Ukrainian hackers takes down NATO and its Cyber Defence Centre Server
A group of Ukrainian hackers going with the handle of CyberBerkut has taken down the official website of North Atlantic Treaty Organization (NATO) along with...
-

 135Malware
135MalwareMicrosoft Word users urged to apply urgent fix after targeted attacks
Microsoft Word users have been urged to update their software after attacks against users of MS Word 2010, where opening a “specially...
-

 98Cyber Crime
98Cyber CrimeFridge attacks “raise big questions” says Microsoft security chief
The emerging ‘internet of things’ raises big security questions, and vulnerabilities in connected devices such as ‘smart’ fridges may force companies to...
-

 164Scams
164ScamsHow cybercriminals ‘market’ email attacks – and why LinkedIn lures are today’s prize phish
Cybercriminals ‘manage’ phishing emails using techniques similar to those used by marketing agencies, including the use of ‘test audiences’ to see how...
-
 343News
343NewsCyberwar Heating Up: Ukraine hit by massive cyber attack from Russia, mobile networks blocked
The telecommunication system of Ukraine has got hit by cyber-attacks through the equipment which have been installed in the Russian-influenced Crimea. These...
-

 80Cyber Crime
80Cyber CrimeBitcoin bank Flexcoin shuts down after attackers loot $570,000 from “hot wallet”
The attackers were able to steal all the bitcoins stored in the bank’s “hot wallet” - the portion of its funds on...
-

 107Cyber Crime
107Cyber CrimeMore than 300,000 wireless routers hijacked by criminals in global attack
More than 300,000 wireless routers worldwide are under the control of an unknown group of cybercriminals, who have made malicious changes to...






