Search results for "malware"
-

 2.0KCyber Attack
2.0KCyber AttackNiceRAT Malware Targets South Korean Users via Cracked Software
Threat actors have been observed deploying a malware called NiceRAT to co-opt infected devices into a botnet. The attacks, which target South...
-

 2.5KMalware
2.5KMalwareArid Viper Launches Mobile Espionage Campaign with AridSpy Malware
The threat actor known as Arid Viper has been attributed to a mobile espionage campaign that leverages trojanized Android apps to deliver...
-

 929Malware
929MalwarePakistan-linked Malware Campaign Evolves to Target Windows, Android, and macOS
Threat actors with ties to Pakistan have been linked to a long-running malware campaign dubbed Operation Celestial Force since at least 2018....
-

 2.1KMalware
2.1KMalwareNew Cross-Platform Malware ‘Noodle RAT’ Targets Windows and Linux Systems
A previously undocumented cross-platform malware codenamed Noodle RAT has been put to use by Chinese-speaking threat actors either for espionage or cybercrime...
-
 3.3KMalware
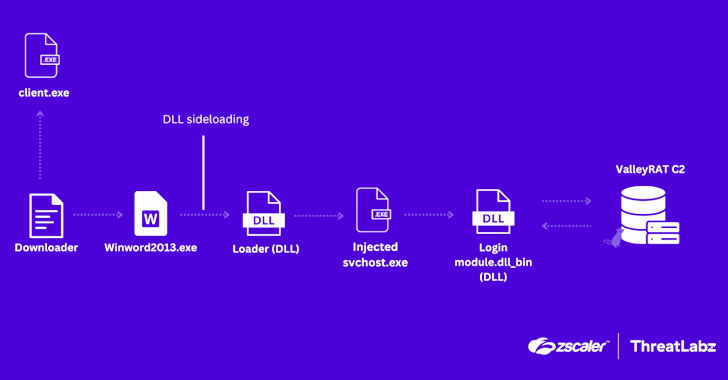
3.3KMalwareChina-Linked ValleyRAT Malware Resurfaces with Advanced Data Theft Tactics
Cybersecurity researchers have uncovered an updated version of malware called ValleyRAT that’s being distributed as part of a new campaign. “In the...
-

 276Malware
276MalwareSPECTR Malware Targets Ukraine Defense Forces in SickSync Campaign
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of cyber attacks targeting defense forces in the country with a malware...
-

 3.3KMalware
3.3KMalwareHackers Exploit Legitimate Packer Software to Spread Malware Undetected
Threat actors are increasingly abusing legitimate and commercially available packer software such as BoxedApp to evade detection and distribute malware such as...
-
 830Cyber Attack
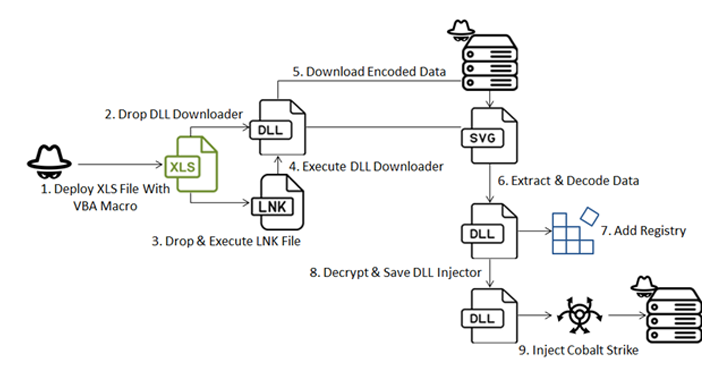
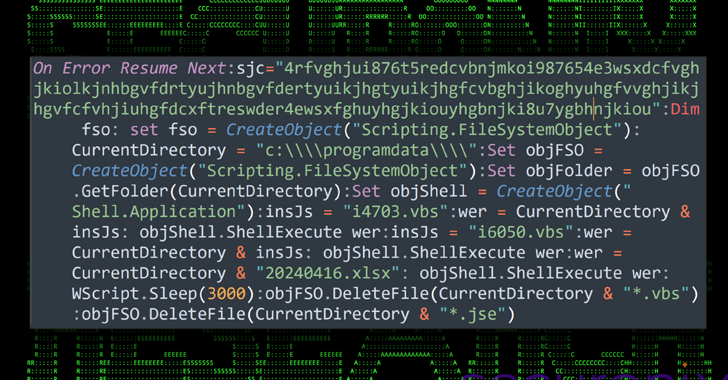
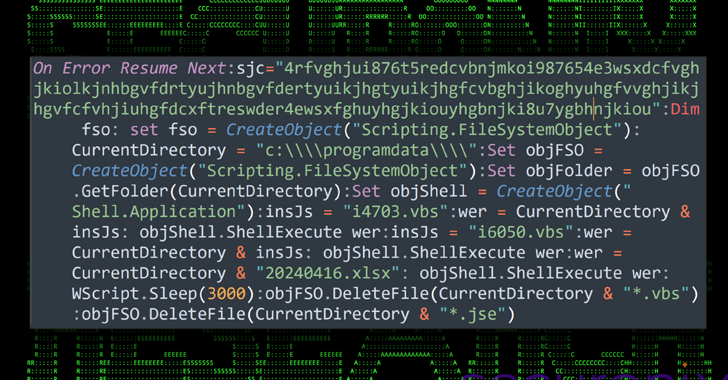
830Cyber AttackHackers Use MS Excel Macro to Launch Multi-Stage Malware Attack in Ukraine
A new sophisticated cyber attack has been observed targeting endpoints geolocated to Ukraine with an aim to deploy Cobalt Strike and seize...
-
 743Data Breach
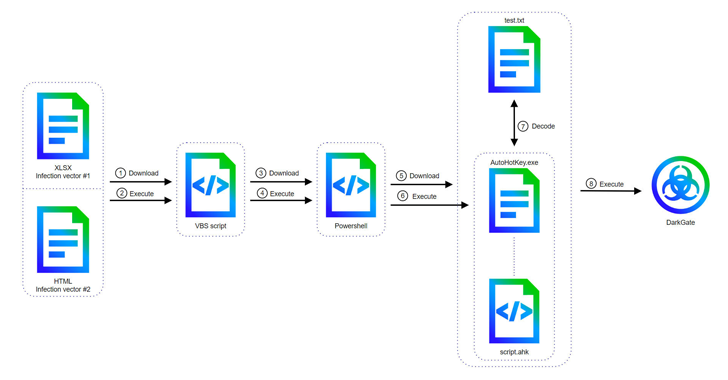
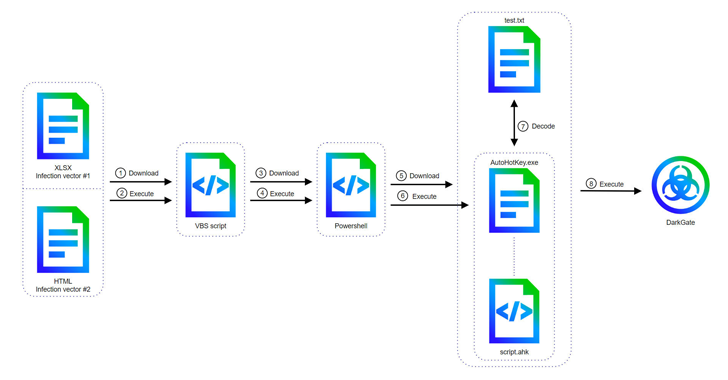
743Data BreachDarkGate Malware Replaces AutoIt with AutoHotkey in Latest Cyber Attacks
Cyber attacks involving the DarkGate malware-as-a-service (MaaS) operation have shifted away from AutoIt scripts to an AutoHotkey mechanism to deliver the last...
-

 3.4KCyber Attack
3.4KCyber AttackAndariel Hackers Target South Korean Institutes with New Dora RAT Malware
The North Korea-linked threat actor known as Andariel has been observed using a new Golang-based backdoor called Dora RAT in its attacks...
-
 3.2KMalware
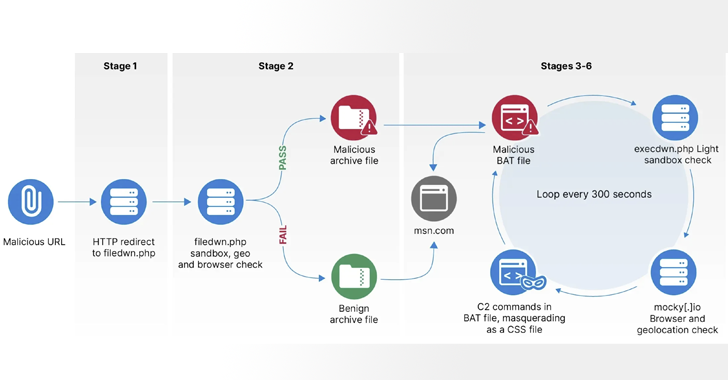
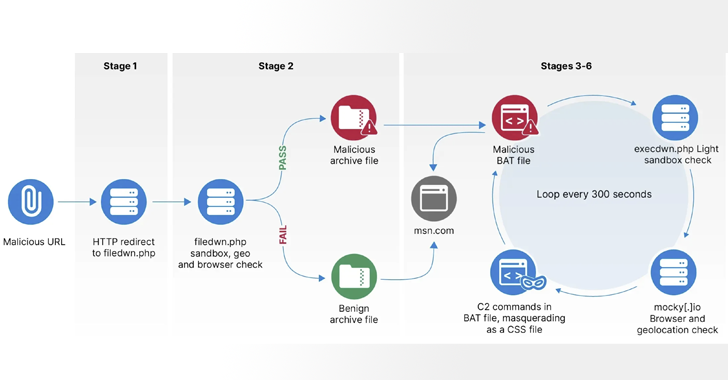
3.2KMalwareRussian Hackers Target Europe with HeadLace Malware and Credential Harvesting
The Russian GRU-backed threat actor APT28 has been attributed as behind a series of campaigns targeting networks across Europe with the HeadLace...
-

 2.6KVulnerabilities
2.6KVulnerabilitiesRedTail Crypto-Mining Malware Exploiting Palo Alto Networks Firewall Vulnerability
The threat actors behind the RedTail cryptocurrency mining malware have added a recently disclosed security flaw impacting Palo Alto Networks firewalls to...
-

 2.3KMalware
2.3KMalwareEuropol Shuts Down 100+ Servers Linked to IcedID, TrickBot, and Other Malware
Europol on Thursday said it shut down the infrastructure associated with several malware loader operations such as IcedID, SystemBC, PikaBot, SmokeLoader, Bumblebee,...
-

 547Malware
547MalwareBeware: These Fake Antivirus Sites Spreading Android and Windows Malware
Threat actors have been observed making use of fake websites masquerading as legitimate antivirus solutions from Avast, Bitdefender, and Malwarebytes to propagate...
-

 797Malware
797MalwareJAVS Courtroom Recording Software Backdoored – Deploys RustDoor Malware
Malicious actors have backdoored the installer associated with courtroom video recording software developed by Justice AV Solutions (JAVS) to deliver malware that’s...
-
 2.3KMalware
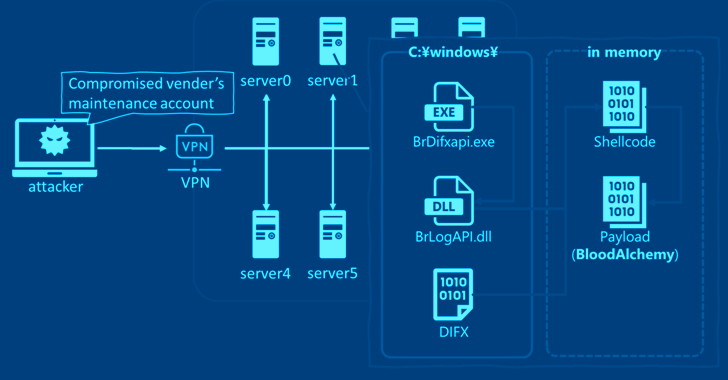
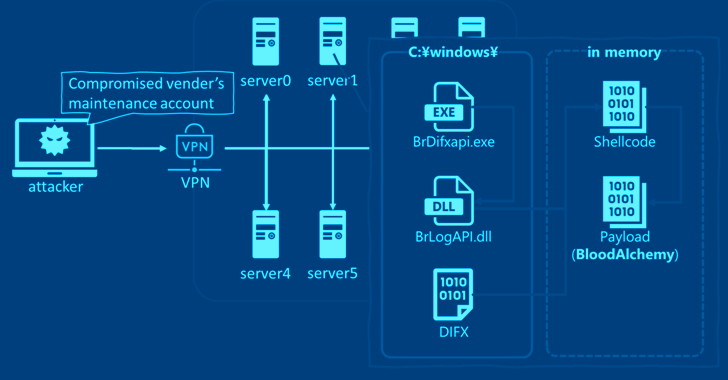
2.3KMalwareStealthy BLOODALCHEMY Malware Targeting ASEAN Government Networks
Cybersecurity researchers have discovered that the malware known as BLOODALCHEMY used in attacks targeting government organizations in Southern and Southeastern Asia is...
-
 1.8KMalware
1.8KMalwareMalware Delivery via Cloud Services Exploits Unicode Trick to Deceive Users
A new attack campaign dubbed CLOUD#REVERSER has been observed leveraging legitimate cloud storage services like Google Drive and Dropbox to stage malicious...
-
 3.0KData Breach
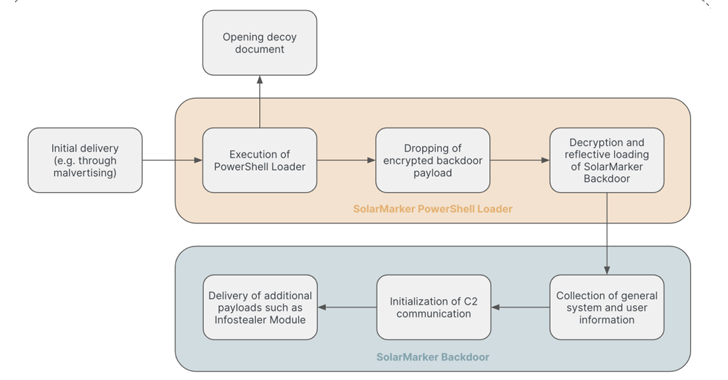
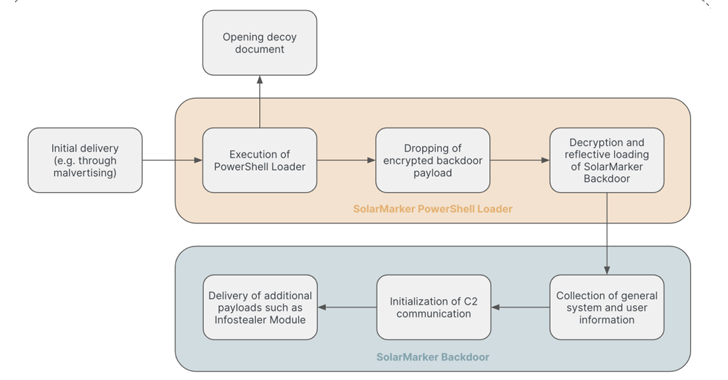
3.0KData BreachSolarMarker Malware Evolves to Resist Takedown Attempts with Multi-Tiered Infrastructure
The persistent threat actors behind the SolarMarker information-stealing malware have established a multi-tiered infrastructure to complicate law enforcement takedown efforts, new findings...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
Multiple threat actors are weaponizing a design flaw in Foxit PDF Reader to deliver a variety of malware such as Agent Tesla,...
-

 3.7KMalware
3.7KMalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
A “multi-faceted campaign” has been observed abusing legitimate services like GitHub and FileZilla to deliver an array of stealer malware and banking...
-

 1.6KMalware
1.6KMalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
Cybersecurity researchers have observed a spike in email phishing campaigns starting early March 2024 that delivers Latrodectus, a nascent malware loader believed...





