All posts tagged "cryptocurrency"
-

 1.4KMalware
1.4KMalwareQubitstrike Targets Jupyter Notebooks with Crypto Mining and Rootkit Campaign
A threat actor, presumably from Tunisia, has been linked to a new campaign targeting exposed Jupyter Notebooks in a two-fold attempt to...
-
 1.1KMalware
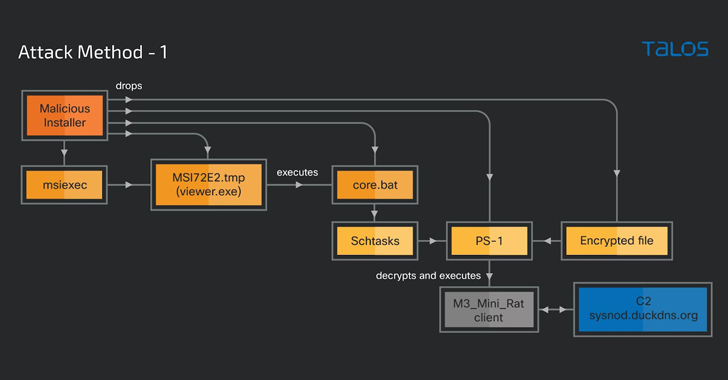
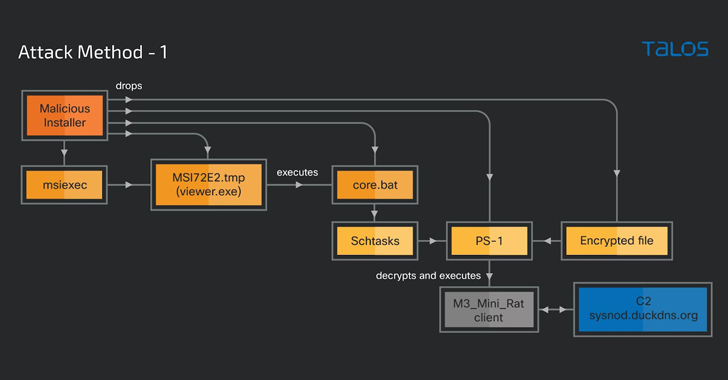
1.1KMalwareCybercriminals Weaponizing Legitimate Advanced Installer Tool in Crypto-Mining Attacks
A legitimate Windows tool used for creating software packages called Advanced Installer is being abused by threat actors to drop cryptocurrency-mining malware...
-

 2.4KCyber Attack
2.4KCyber AttackNorth Korean Affiliates Suspected in $40M Cryptocurrency Heist, FBI Warns
The U.S. Federal Bureau of Investigation (FBI) on Tuesday warned that threat actors affiliated with North Korea may attempt to cash out...
-
 1.4KMalware
1.4KMalwareHackers Target Apache Tomcat Servers for Mirai Botnet and Crypto Mining
Misconfigured and poorly secured Apache Tomcat servers are being targeted as part of a new campaign designed to deliver the Mirai botnet...
-
 808Malware
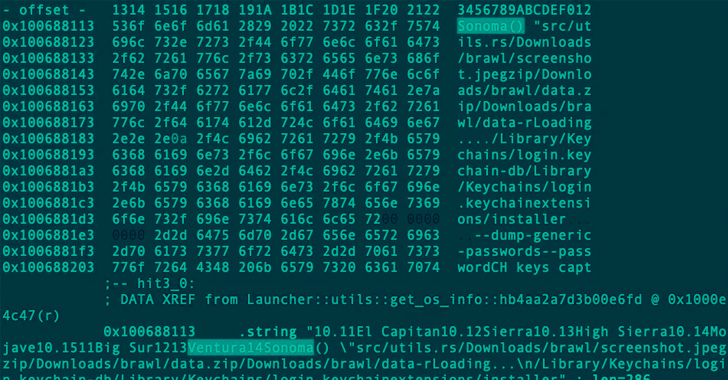
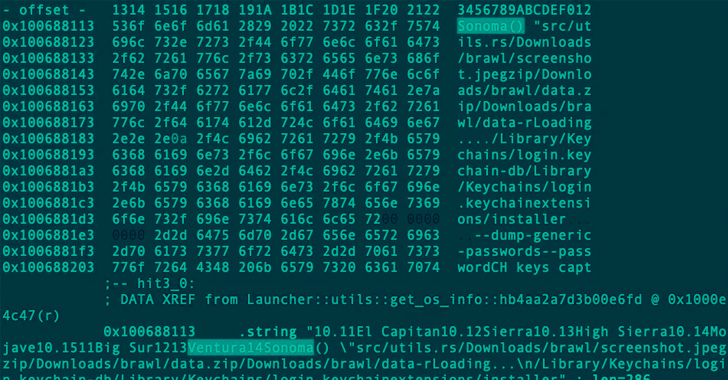
808MalwareRust-based Realst Infostealer Targeting Apple macOS Users’ Cryptocurrency Wallets
A new malware family called Realst has become the latest to target Apple macOS systems, with a third of the samples already...
-
 3.5KMalware
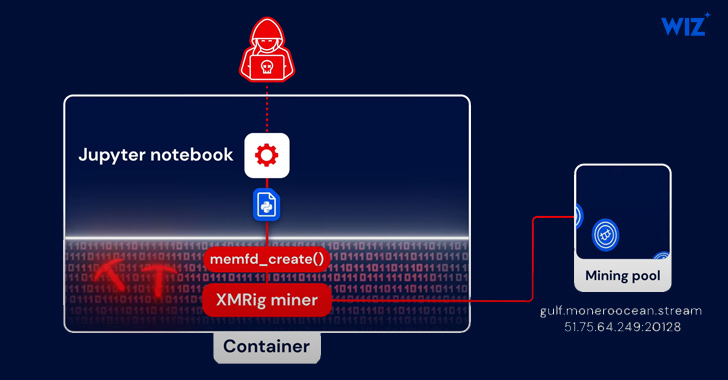
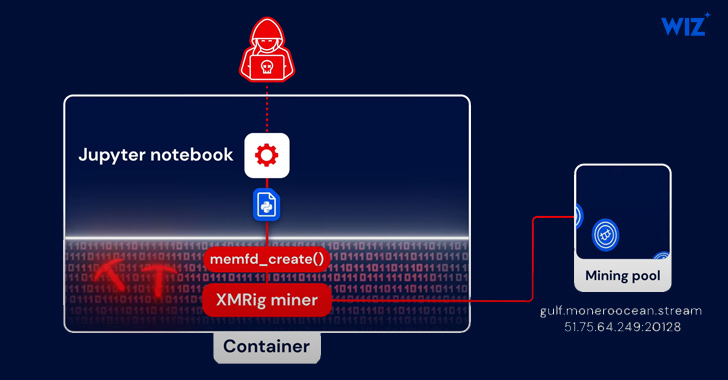
3.5KMalwarePython-Based PyLoose Fileless Attack Targets Cloud Workloads for Cryptocurrency Mining
A new fileless attack dubbed PyLoose has been observed striking cloud workloads with the goal of delivering a cryptocurrency miner, new findings...
-

 1.7KMalware
1.7KMalwareJapanese Cryptocurrency Exchange Falls Victim to JokerSpy macOS Backdoor Attack
An unknown cryptocurrency exchange located in Japan was the target of a new attack earlier this month to deploy an Apple macOS...
-

 4.5KMalware
4.5KMalwareRansomware Hackers and Scammers Utilizing Cloud Mining to Launder Cryptocurrency
Ransomware actors and cryptocurrency scammers have joined nation-state actors in abusing cloud mining services to launder digital assets, new findings reveal. “Cryptocurrency...
-
 2.6KMalware
2.6KMalwareBeware: New DoubleFinger Loader Targets Cryptocurrency Wallets with Stealer
A novel multi-stage loader called DoubleFinger has been observed delivering a cryptocurrency stealer dubbed GreetingGhoul in what’s an advanced attack targeting users...
-

 969Malware
969MalwareNew Malware Campaign Leveraging Satacom Downloader to Steal Cryptocurrency
A recent malware campaign has been found to leverage Satacom downloader as a conduit to deploy stealthy malware capable of siphoning cryptocurrency...
-

 2.4KMalware
2.4KMalware8220 Gang Exploiting Oracle WebLogic Flaw to Hijack Servers and Mine Cryptocurrency
The notorious cryptojacking group tracked as 8220 Gang has been spotted weaponizing a six-year-old security flaw in Oracle WebLogic servers to ensnare...
-

 3.0KMalware
3.0KMalwareNew Atomic macOS Malware Steals Keychain Passwords and Crypto Wallets
Threat actors are advertising a new information stealer for the Apple macOS operating system called Atomic macOS Stealer (or AMOS) on Telegram...
-

 1.8KCyber Attack
1.8KCyber AttackKubernetes RBAC Exploited in Large-Scale Campaign for Cryptocurrency Mining
A large-scale attack campaign discovered in the wild has been exploiting Kubernetes (K8s) Role-Based Access Control (RBAC) to create backdoors and run...
-

 2.1KMalware
2.1KMalwareCryptocurrency Companies Targeted in Sophisticated 3CX Supply Chain Attack
The adversary behind the supply chain attack targeting 3CX deployed a second-stage implant specifically singling out a small number of cryptocurrency companies....
-
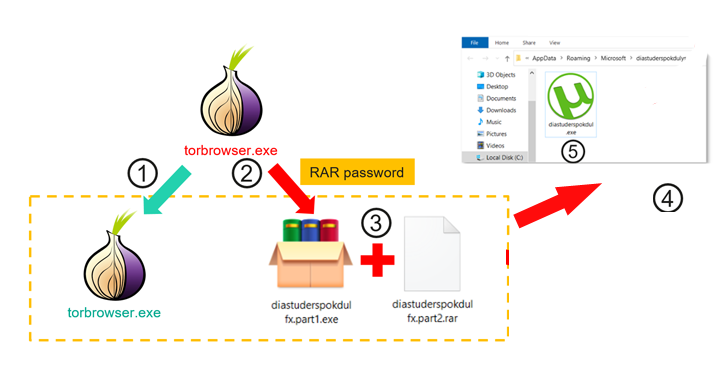
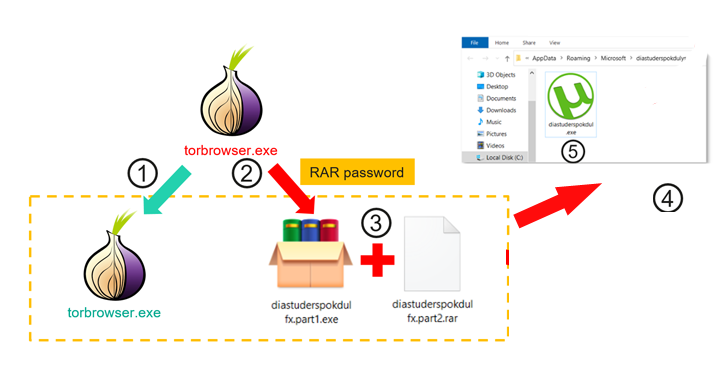 2.9KMalware
2.9KMalwareTrojanized TOR Browser Installers Spreading Crypto-Stealing Clipper Malware
Trojanized installers for the TOR anonymity browser are being used to target users in Russia and Eastern Europe with clipper malware designed...
-

 4.1KCyber Attack
4.1KCyber AttackNorth Korean APT43 Group Uses Cybercrime to Fund Espionage Operations
A new North Korean nation-state cyber operator has been attributed to a series of campaigns orchestrated to gather strategic intelligence that aligns...
-
 2.4KMalware
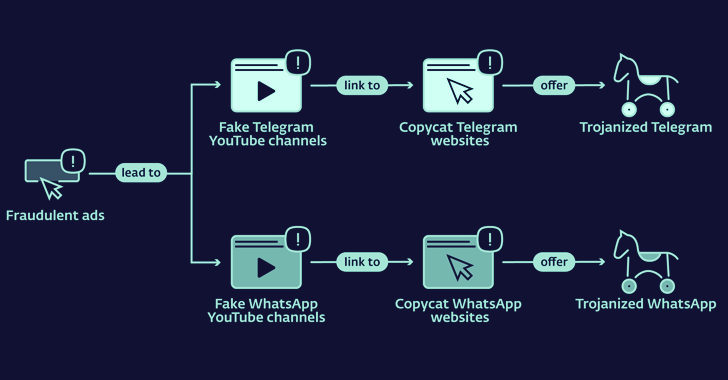
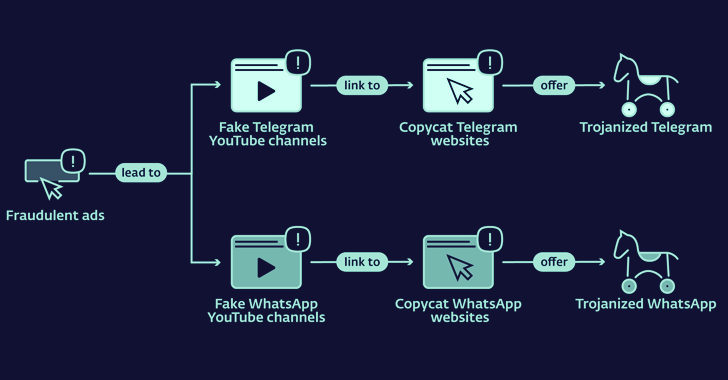
2.4KMalwareLookalike Telegram and WhatsApp Websites Distributing Cryptocurrency Stealing Malware
Copycat websites for instant messaging apps like Telegram and WhatApp are being used to distribute trojanized versions and infect Android and Windows...
-
 5.0KMalware
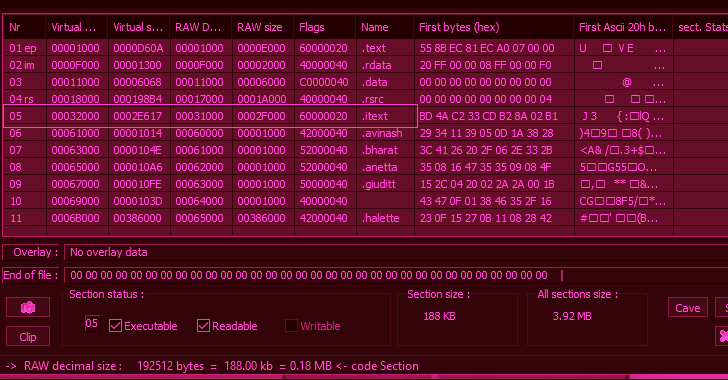
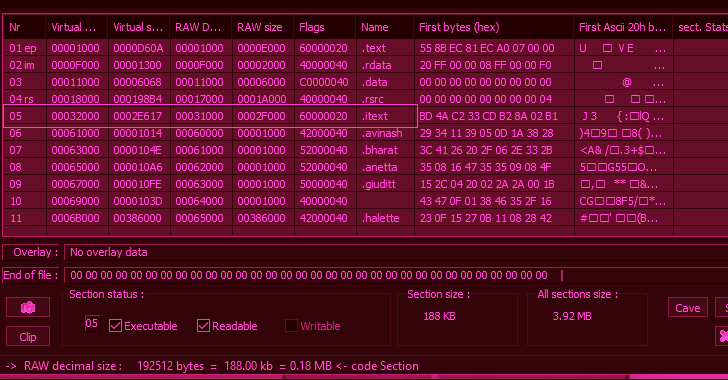
5.0KMalwareParallax RAT Targeting Cryptocurrency Firms with Sophisticated Injection Techniques
Cryptocurrency companies are being targeted as part of a new campaign that delivers a remote access trojan called Parallax RAT. The malware...
-
 4.5KMalware
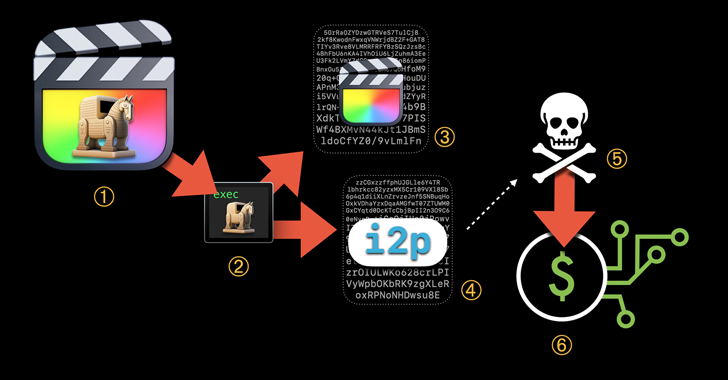
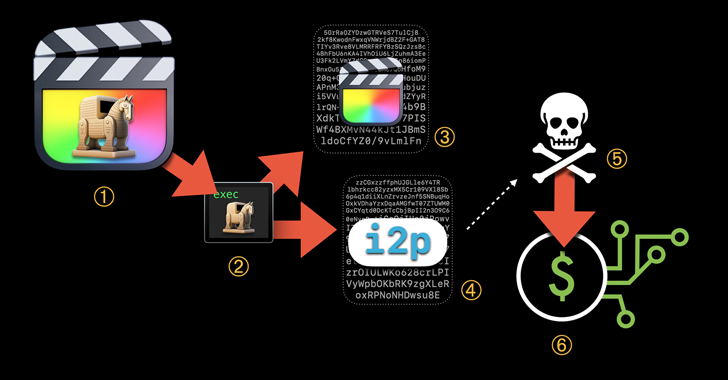
4.5KMalwareHackers Using Trojanized macOS Apps to Deploy Evasive Cryptocurrency Mining Malware
Trojanized versions of legitimate applications are being used to deploy evasive cryptocurrency mining malware on macOS systems. Jamf Threat Labs, which made...
-

 3.6KMalware
3.6KMalwareFinancially Motivated Threat Actor Strikes with New Ransomware and Clipper Malware
A new financially motivated campaign that commenced in December 2022 has seen the unidentified threat actor behind it deploying a novel ransomware...
-

 4.4KCyber Attack
4.4KCyber AttackRussian Hacker Pleads Guilty to Money Laundering Linked to Ryuk Ransomware
A Russian national on February 7, 2023, pleaded guilty in the U.S. to money laundering charges and for attempting to conceal the...






