All posts tagged "malware"
-

 155News
155NewsPassword Stealing Malware the latest tool for Cybercriminals
Remember last year, Verizon released data breach investigation report that showed 80 percent of the hacking was related to stolen password. The cybercriminals used...
-

 354Data Security
354Data SecurityThe Pirate Bay is silently mining cryptocurrency without user consent
After being offline for over a week, The Pirate Bay is back online with a cryptocurrency mining code. Last year, it was...
-
 193Malware
193MalwareNew Malicious Macro that Hijacks your Windows Desktop Shortcuts and Points to Download Malware
Cybercriminals using a malicious macro that changes the target of Desktop Shortcuts to download malware and when the user clicks on the...
-
 220Malware
220MalwareNew Double Zero-day Exploit Discovered in same PDF file that Affected Adobe Acrobat & Windows 7
A researcher discovered new double Zero-day exploit that affected Adobe Acrobat, Reader and older Windows 7 platforms, Windows Server 2008. This critical Zero-Day...
-
Malware
MACOS Malware Targeting Cryptocurrency Users On Slack and Discord – 100% Undetected Virustotal
Hackers targeting Cryptocurrency users On Slack and Discord chat platforms with MACOS Malware dubbed OSX.Dummy. The malware targeted users in crypto related...
-

 305News
305NewsHow to Stay Vigilant Against Phishing Scams
Phishing attacks have become a common occurrence in the digital age. While most of us already know what these email scams look...
-

 246Malware
246Malware$50 malware allows users to build their own botnets
A new malware was discovered on sale for the amount of 50 dollars in its beta version, but promising the possibility of...
-
 163Malware
163MalwareHacking Group “RANCOR” Identified Using Malware Families LAINTEE and DDKONG
A new Cyber Espionage Group dubbed RANCOR identified targeting South East Asia using new malware families PLAINTEE and DDKONG. The RANCOR group...
-
 213Malware
213MalwareNecurs Botnet Malware Attack Create a FlawedAMMYY Backdoor on Compromised Windows PC
Necurs botnet malware emerging again with new set of futures to create a backdoor on victims machine to steal sensitive data and...
-

 162News
162NewsOrganizations Should Fear These 4 Cybersecurity Risks
For any organization looking to make a successful digital transformation, cybersecurity must be a top priority—hard stop. Damages and data loss related...
-

 355Data Security
355Data SecurityMeet MyloBot malware turning Windows devices into Botnet
The IT security researchers at deep learning cybersecurity firm Deep Instinct have discovered a sophisticated malware in the wild targeting Microsoft’s Windows-based computers....
-
 282Malware
282Malware60,000 Android Devices are Infected with Malicious Battery Saver App that Steal Various Sensitive Data
Over 60,000 Android devices are infected with malicious Battery Saver app that is capable of stealing sensitive information from victims and generating...
-
 175Malware
175MalwareMyloBot – Highly Sophisticated Botnet Shutdown Windows Defender & Blocking Ports on the Firewall
Newly uncovered complex MyloBot Botnet incorporates different malicious techniques and ability to shut down the Windows Defender and Windows Updates. Basically, botnet do...
-

 234News
234NewsShould Corporate Executives Be Responsible for Security?
Amit Yoran, the current CEO of the cyber exposure company called Tenable Network Security, has recently revealed that corporate executives are regularly...
-

 358News
358NewsRansomhack; a new attack blackmailing business owners using GDPR
Hackers are threatening companies to leak stolen user data online to hurt them through GDPR regulations – In return they are demanding...
-

 255Malware
255MalwareGZipDe – A Sophisticated Malware Attack using Metasploit Backdoor with Encrypted Payload
Sophisticated Malware called GZipDe distributed through the Weaponized malicious document and installed the Metasploit backdoor in targeted victims computer. Metasploit is a powerful...
-

 389Data Security
389Data SecurityIn Russia for World Cup? Beware of fake WiFi hotspots stealing user data
The Football World Cup 2018 has gathered thousands of fans from around the world in Russia to watch their favorite team battling to...
-
 384Exploitation Tools
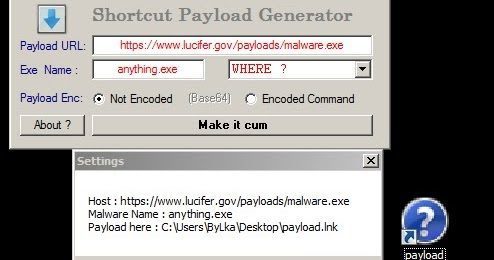
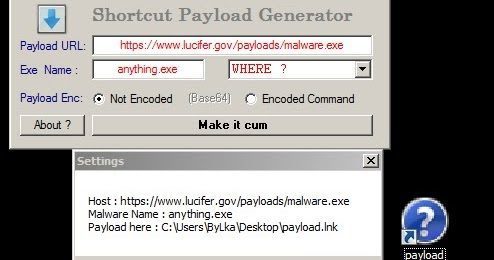
384Exploitation ToolsLNK-Kisser – PowerShell Link Payload Generator
Making FUD Shortcut (.lnk) payloads with LNK-KISSER to remote execute malicious code. Shortcut-Payload-Generator Exploiting Powershell to make ShortCut Payloads [fud]. There...
-

 294Malware
294MalwareFakeSpy – Android Information Stealing Malware Attack to Steal Text Messages, Call Records & Contacts
Cyber criminals spreading new Android Malware called FakeSpy to compromise the infected Android users to stealing text messages, account information, contacts, and...
-

 198News
198NewsFortinet Reflects On The Dangerous New Threatscape
Industry research supports the belief that cybercriminals are currently developing many new ways to boost their attack capabilities, on the network and...
-

 295Malware
295MalwareKardon Loader Enables Anyone to Build their Own Malware Distribution Network
Kardon Loader advertised in underground markets as an open beta product for sale the standalone built cost $50 and with separate charges for...






