All posts tagged "malware"
-

 250News
250NewsResearchers Encode Physical DNA with Malware To infect Computers
When DNA was synthesized, nobody had thought that it could be used to spread computer viruses, but a group of researchers from...
-

 346Cyber Events
346Cyber EventsNorth Korea Hit By Konni and Inexsmar Malware After Missile Tests
An unknown hacking group has been targeting organizations in North Korea with Konni Malware. It is a RAT/remote access Trojan having all...
-

 192Malware
192MalwareLarge scale Cyber attack Targeting Weak Spot in the Vital Electrical Infrastructure
A new research published last week by Willem Westerhof describing an outsized scale cyber attack targeting the crucial electrical infrastructure based on...
-

 293Cyber Crime
293Cyber CrimeWannaCry hero gets bail; pleading not guilty over Kronos malware
As you might know, 23-year-old Marcus Hutchins (@MalwareTechBlog on Twitter) who once made the news for stopping WannaCry ransomware attack was arrested by the...
-
 135Cyber Attack
135Cyber AttackHacker Sentenced More Than 3 Years Jail For Spreading Linux Malware
A Russian man accused of infecting tens of thousands of servers through Linux malware around the world to generate millions of dollars...
-

 351Geek
351GeekHero Researcher Who Halted WannaCry Ransomware Arrested by FBI
An IT security researcher going by the Twitter handle of @MalwareTechBlog (real name Marcus Hutchins) has been detained by the law enforcement authorities...
-

 382News
382NewsVault 7: CIA’ Dumbo Project Hijacking Webcams and Microphones
The Vault7 saga is far from over, and every passing week we are being introduced to a new set of tricks and...
-

 103Cyber Attack
103Cyber AttackBanking Trojan Inspired By Wannacry To Add Self Spreading Ability
Even though WannaCry and Petya ransomware wave have slowed down, motivated by money laundering criminals, and hackers have taken world class outbreaks...
-

 184News
184NewsDangerous Mobile Banking Trojan Uses Keylogger To Steal Everything
Security researchers have discovered that one of Android’s most dangerous Mobile banking Trojan family has been modified to add a keylogger for...
-

 189Hacked
189HackedShieldFS Stops Ransomware Attacks With 97% Success And Recovers Your Lost Files
Short Bytes: A team of Italian security researchers has created a Windows filesystem add-on named ShieldFS to fight the ransomware attacks. By...
-
 362Malware
362MalwareMachine learning system to create invisible malwares – gym-malware
In the recent DEF CON Meet, technical director of security shop Endgame Hyrum Anderson disclosed a research paper on adapting API frameworks...
-
 340News
340NewsPre-installed Trojan in Cheap Android Devices Steal Data, Intercept Chats
Android devices are one of the most vulnerable mobile OS (operating systems) due to its open source nature. But what would a...
-
 366News
366NewsHealthcare Clinic Suffers Ransomware Attack; 300K Patients Impacted
This without a doubt is the second largest health data breach caused by a ransomware attack. An Oaks, Philadelphia based women’s healthcare...
-

 417News
417NewsHow A Coffee Machine Infected Factory Computers with Ransomware
It’s no surprise that the Internet of Things (IoT) devices are highly vulnerable to cyber attacks but who would know a time...
-
 231Vulnerabilities
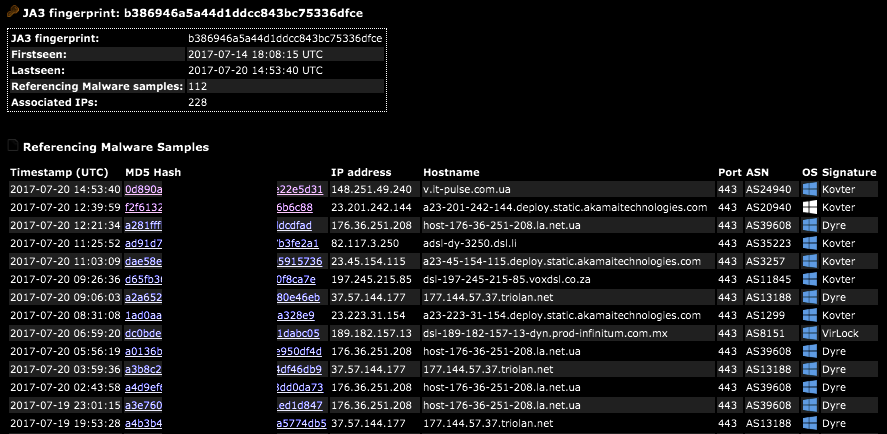
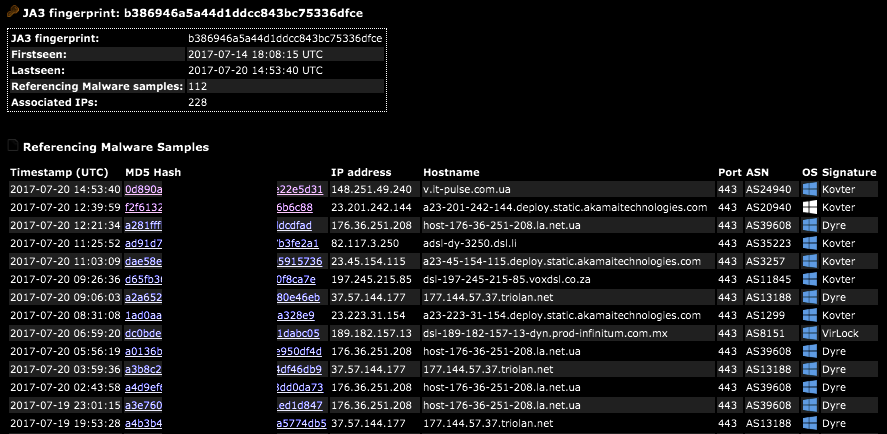
231VulnerabilitiesSSL/TLS Client Fingerprinting for Malware Detection
A JA3 hash represents the fingerprint of an SSL/TLS client application as detected via a network sensor or device, such as Bro...
-

 212Cyber Crime
212Cyber CrimeChina arrests 11 hackers for infecting 250M devices with Fireball malware
Law enforcement authorities in China have arrested eleven hackers suspected of developing Fireball malware which infected 250 million computers worldwide. Among the...
-

 332News
332News6 billion records hacked in 2017 so far; ransomware victims paid $25 million
With every passing day, hackers and cyber criminals are becoming more sophisticated in their attacks. Resultantly, they are getting their hands on...
-

 289Data Security
289Data SecurityCowerSnail Backdoor Targeting Windows Devices
Kaspersky Lab has identified the presence of a backdoor designed primarily for attacking Windows systems. When the backdoor successfully infects the system...
-

 160News
160NewsWatch Security Researcher As She Hacks ATM by Drilling a Hole
ATMs (automated teller machines) have remained a preferred target of hackers around the world. Last year, ATMs in over a dozen locations...
-

 266Hacked
266HackedMystery “FruitFly” Malware Infected Macs For Years, No One Noticed It Until 2017
Short Bytes: Two malware which go by the name FruitFly and FruitFly 2 have been discovered over the course of the last...
-
 72Malware
72Malware“Perverse” malware infecting hundreds of Macs remained undetected for years
Surveillance malware dubbed Firefly was easy to spot but flew under the radar anyway. A mysterious piece of malware that gives attackers...






