All posts tagged "ransomware"
-
 1.7KMalware
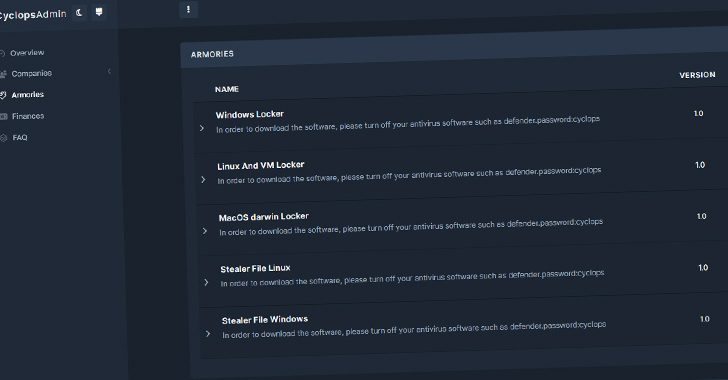
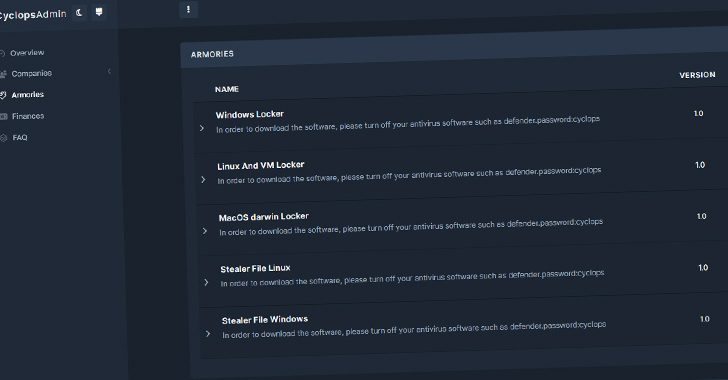
1.7KMalwareCyclops Ransomware Gang Offers Go-Based Info Stealer to Cybercriminals
Threat actors associated with the Cyclops ransomware have been observed offering an information stealer malware that’s designed to capture sensitive data from...
-
 3.0KMalware
3.0KMalwareMicrosoft: Lace Tempest Hackers Behind Active Exploitation of MOVEit Transfer App
Microsoft has officially linked the ongoing active exploitation of a critical flaw in the Progress Software MOVEit Transfer application to a threat...
-
 948Malware
948MalwareAceCryptor: Cybercriminals’ Powerful Weapon, Detected in 240K+ Attacks
A crypter (alternatively spelled cryptor) malware dubbed AceCryptor has been used to pack numerous strains of malware since 2016. Slovak cybersecurity firm...
-

 448Malware
448MalwareIranian Agrius Hackers Targeting Israeli Organizations with Moneybird Ransomware
The Iranian threat actor known as Agrius is leveraging a new ransomware strain called Moneybird in its attacks targeting Israeli organizations. Agrius,...
-

 2.9KMalware
2.9KMalwareMeet ‘Jack’ from Romania! Mastermind Behind Golden Chickens Malware
The identity of the second threat actor behind the Golden Chickens malware has been uncovered courtesy of a fatal operational security blunder,...
-

 728Malware
728MalwareNotorious Cyber Gang FIN7 Returns With Cl0p Ransomware in New Wave of Attacks
The notorious cybercrime group known as FIN7 has been observed deploying Cl0p (aka Clop) ransomware, marking the threat actor’s first ransomware campaign...
-
 900Malware
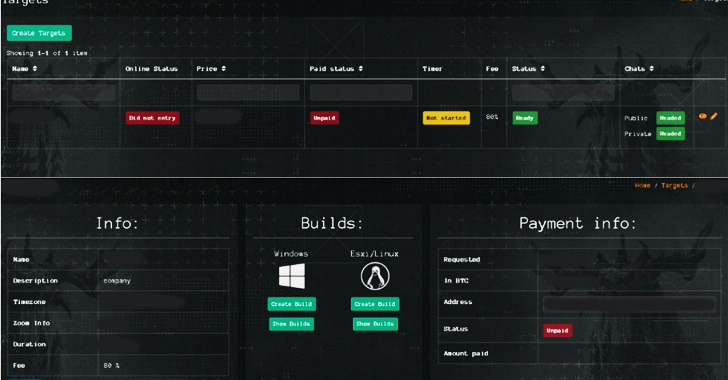
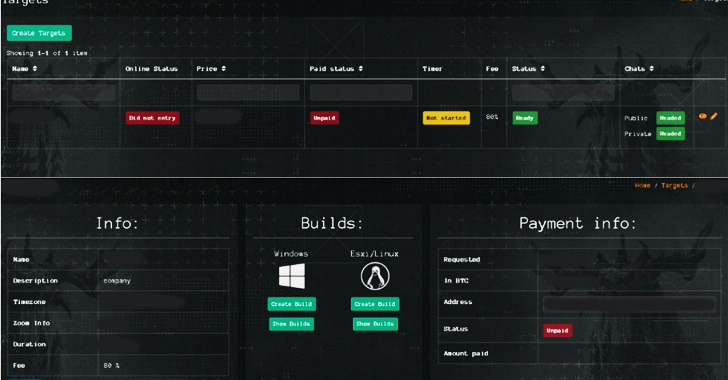
900MalwareInside Qilin Ransomware: Affiliates Take Home 85% of Ransom Payouts
Ransomware affiliates associated with the Qilin ransomware-as-a-service (RaaS) scheme earn anywhere between 80% to 85% of each ransom payment, according to new...
-
 4.1KMalware
4.1KMalwareNew Ransomware Gang RA Group Hits U.S. and South Korean Organizations
A new ransomware group known as RA Group has become the latest threat actor to leverage the leaked Babuk ransomware source code...
-
 240Malware
240MalwareNew ‘MichaelKors’ Ransomware-as-a-Service Targeting Linux and VMware ESXi Systems
A new ransomware-as-service (RaaS) operation called MichaelKors has become the latest file-encrypting malware to target Linux and VMware ESXi systems as of...
-

 510Vulnerabilities
510VulnerabilitiesBl00dy Ransomware Gang Strikes Education Sector with Critical PaperCut Vulnerability
U.S. cybersecurity and intelligence agencies have warned of attacks carried out by a threat actor known as the Bl00dy Ransomware Gang that...
-
 3.3KMalware
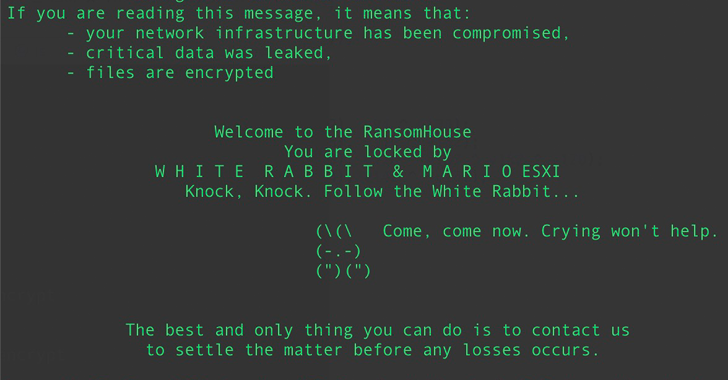
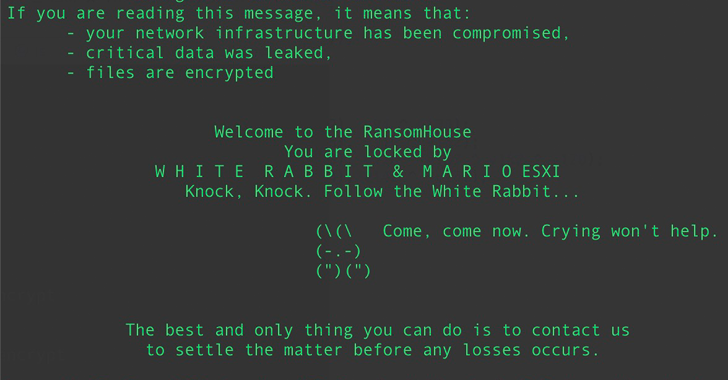
3.3KMalwareBabuk Source Code Sparks 9 Different Ransomware Strains Targeting VMware ESXi Systems
Multiple threat actors have capitalized on the leak of Babuk (aka Babak or Babyk) ransomware code in September 2021 to build as...
-

 2.6KMalware
2.6KMalwareJoin Our Webinar: Learn How to Defeat Ransomware with Identity-Focused Protection
Are you concerned about ransomware attacks? You’re not alone. In recent years, these attacks have become increasingly common and can cause significant...
-

 3.7KData Breach
3.7KData BreachMSI Data Breach: Private Code Signing Keys Leaked on the Dark Web
The threat actors behind the ransomware attack on Taiwanese PC maker MSI last month have leaked the company’s private code signing keys...
-

 4.7KData Breach
4.7KData BreachWestern Digital Confirms Customer Data Stolen by Hackers in March Breach
Digital storage giant Western Digital confirmed that an “unauthorized third party” gained access to its systems and stole personal information belonging to...
-

 2.8KMalware
2.8KMalwareWanted Dead or Alive: Real-Time Protection Against Lateral Movement
Just a few short years ago, lateral movement was a tactic confined to top APT cybercrime organizations and nation-state operators. Today, however,...
-
 646Malware
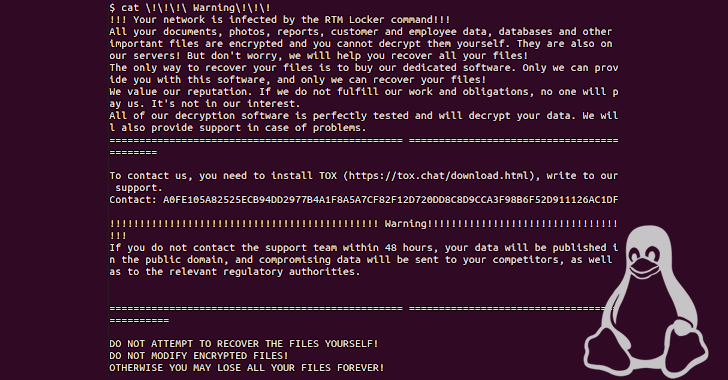
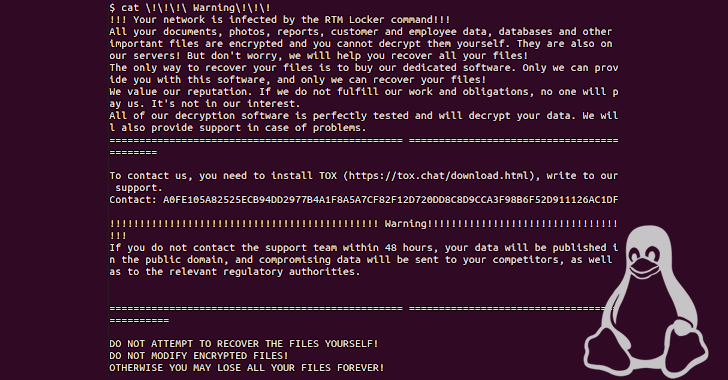
646MalwareRTM Locker’s First Linux Ransomware Strain Targeting NAS and ESXi Hosts
The threat actors behind RTM Locker have developed a ransomware strain that’s capable of targeting Linux machines, marking the group’s first foray...
-

 354Vulnerabilities
354VulnerabilitiesFortra Sheds Light on GoAnywhere MFT Zero-Day Exploit Used in Ransomware Attacks
Fortra, the company behind Cobalt Strike, shed light on a zero-day remote code execution (RCE) vulnerability in its GoAnywhere MFT tool that...
-
 2.6KMalware
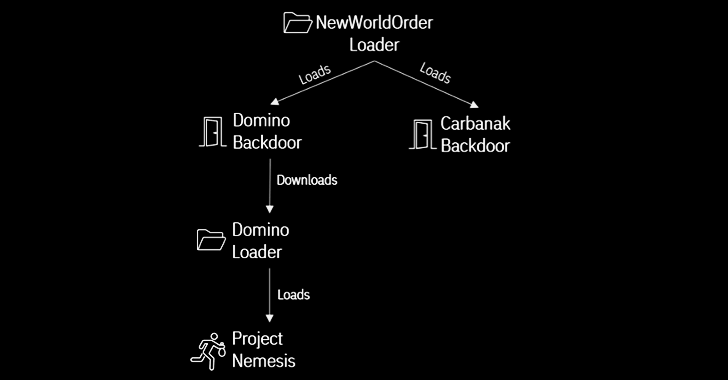
2.6KMalwareFIN7 and Ex-Conti Cybercrime Gangs Join Forces in Domino Malware Attacks
A new strain of malware developed by threat actors likely affiliated with the FIN7 cybercrime group has been put to use by...
-
 3.1KMalware
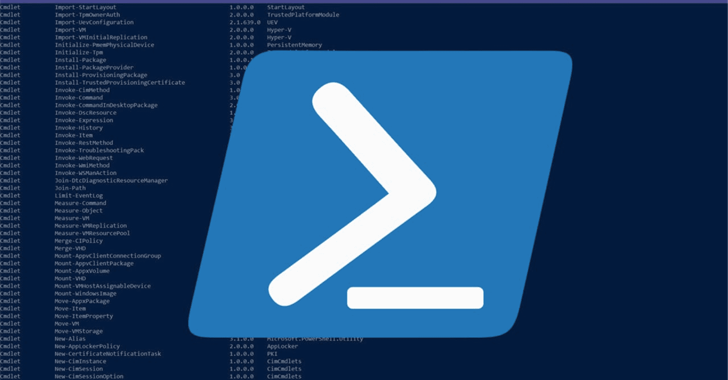
3.1KMalwareVice Society Ransomware Using Stealthy PowerShell Tool for Data Exfiltration
Threat actors associated with the Vice Society ransomware gang have been observed using a bespoke PowerShell-based tool to fly under the radar...
-

 2.3KCyber Attack
2.3KCyber AttackRTM Locker: Emerging Cybercrime Group Targeting Businesses with Ransomware
Cybersecurity researchers have detailed the tactics of a “rising” cybercriminal gang called “Read The Manual” (RTM) Locker that functions as a private...
-

 3.9KMalware
3.9KMalwareCISA Warns of 5 Actively Exploited Security Flaws: Urgent Action Required
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added five security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing...






