All posts tagged "Security"
-

 303News
303NewsISIS supporters hack Chile’s Ministry of Defense website
Isis supporter compromised Chile’s Ministry of Defense website on Monday night and left a message “Hacked” on its homepage, www.ssdefensa.cl, along with...
-

 378News
378NewsGoogle Vietnam Domain Hacked by Lizard Squad
Remember Lizard Squad? Yes, the same Lizard Squad who shutdown PSN and Xbox Live last Christmas making the holidays one living hell for games....
-

 201Data Security
201Data SecurityHow pervert security guards stalk women via CCTV
Women Stalked by Security Guards via CCTV – “Sleaze File” contains images of pretty women Five security guards of a high-profile shopping complex...
-

 316News
316NewsSnowden Leak: NSA, GCHQ hacked millions of SIM encryption keys, including yours?
The US surveillance agency, National Security Agency (NSA) along with its British counterpart the Government Communications (GCHQ) has compromised one of the...
-
 244How To
244How ToSpytector Employee Monitoring Made Easy (Review)
It is somewhat a proven fact that Computer & Internet have brought a new era of productivity into the human life in...
-

 189News
189NewsBigFish Games hacked; sensitive data compromised
Hackers have breached the billing and payment pages of BigFish Games and stolen sensitive information, according to the company’s notification letter published...
-
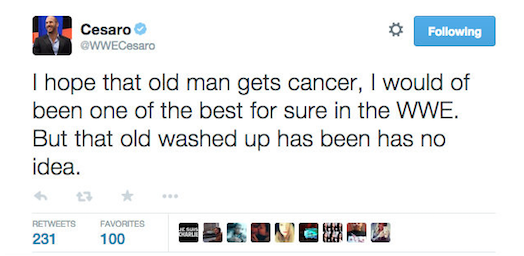
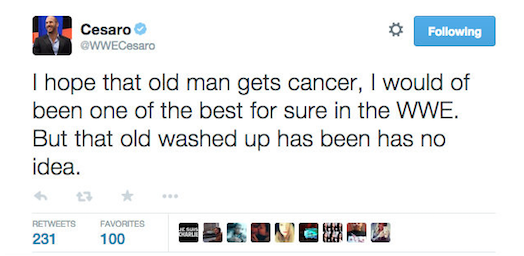 179News
179NewsWWE Superstar Antonio Cesaro’ Twitter account hacked, ‘wish cancer’ on McMahon
The official verified Twitter account of WWE superstar Antonio Cesaro (@WWECesaro) was hacked earlier Tuesday by unknown hacker wishing cancer to the company’s Chairman and...
-

 306Data Security
306Data SecurityVisa to track your smartphone location to “prevent” credit card fraud
Visa, famed payment processing company, will be rolling out its new software with location-tracking capabilities this summer. It will allow banks to...
-

 311News
311NewsWebsite of UAE’ oldest newspaper Al Ittihad hacked by ISIS hackers
On 14th February, 2015, when people were busy celebrating Valentines day; the ISIS hackers were busy targeting UAE’s oldest Arabic language newspaper Al...
-

 385Data Security
385Data SecurityFBI wants to hide how cops are spying on you via “stingray” cellphone tracker
If by any chance, you have been into a local police department for filing a public request in order to know about...
-

 267Data Security
267Data SecurityEmail titled “My New Photo ;)” actually Contains Malware
Email titled “My New Photo ;)” actually Contain Malware – A .Zip file has an attachment Supposedly containing the promised image. Summary: Hackers,...
-

 284Data Security
284Data Security16Mn Devices Compromised by Sophisticated Mobile Malware: Study
According to a study by Alcatel-Lucent’s Motive Security Labs, users around the world are being spied upon by extremely sophisticated mobile malware...
-

 336Data Security
336Data SecurityDARPA Builds ‘Memex’ Deep Web Search Engine to Track Sex Traffickers
A project had been announced by the U.S government’s Defense Advance Research Projects Agency (DARPA) last year which was to create a...
-

 235Data Security
235Data SecurityCritical Vulnerability Allows attacker to have full control over LG Smartphones
Search-Lab Ltd. discovered a serious security vulnerability in the On Screen Phone protocol used by LG Smart Phones. A malicious attacker is...
-
 248Surveillance
248SurveillanceDEA Making Huge Photo Database of Country’s Drivers, vehicles’ number plates
DEA Maintaining Massive database of the country’s drivers and vehicles’ number plates – Database is used by DEA to track car owners. In...
-

 227Data Security
227Data SecurityHackers target Forbes visitors through chained Flash and IE Zero-days vulnerabilities
Hackers pieced together zero-day vulnerabilities in Flash and Internet Explorer 9+ to attack financial services and defense contractor employees visiting Forbes.com, according...
-
 201News
201NewsResearcher publishes 10 million passwords, usernames amid FBI raid
A security researcher has revealed from a research of various data breaches, a collection of 10 million usernames and passwords. The leaked...
-

 418Data Security
418Data SecurityKali Linux 1.1.0 Released! Download Now
The developers at Offensive Security are back with yet another great version of Debian-derived Linux distribution Kali Linux version 1.10. Kali Linux 1.1.0 was...
-

 195Surveillance
195SurveillanceSamsung’s Smart TV may be Spying on YOU!
Samsung decision to process voice commands in its latest Smart TV through cloud server has sparked a new debate on data retention,...
-

 113Cyber Crime
113Cyber CrimeHacker gets 8 Years in Jail for Making Prank Death Threats
Remote Control Virus was used by the Hacker to Penetrate into Computer Systems and issue death threats to users. On Wednesday, the...
-

 297Cyber Events
297Cyber EventsThe Guy who Developed World’s First Email Encryption Software is Broke!
The person who developed the free email encryption software Gnu Privacy Guard in 1997, which was used by famous NSA whistleblower Edward...






