All posts tagged "Trojan"
-
 89Malware
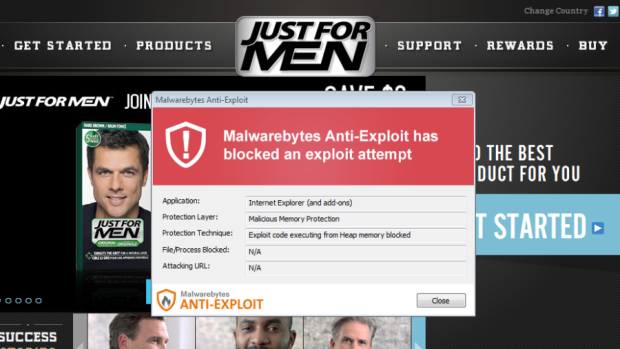
89MalwareJust For Men website serves malware
The website for Just For Men, a company that sells various products for men as its name implies, was serving malware to...
-

 114Malware
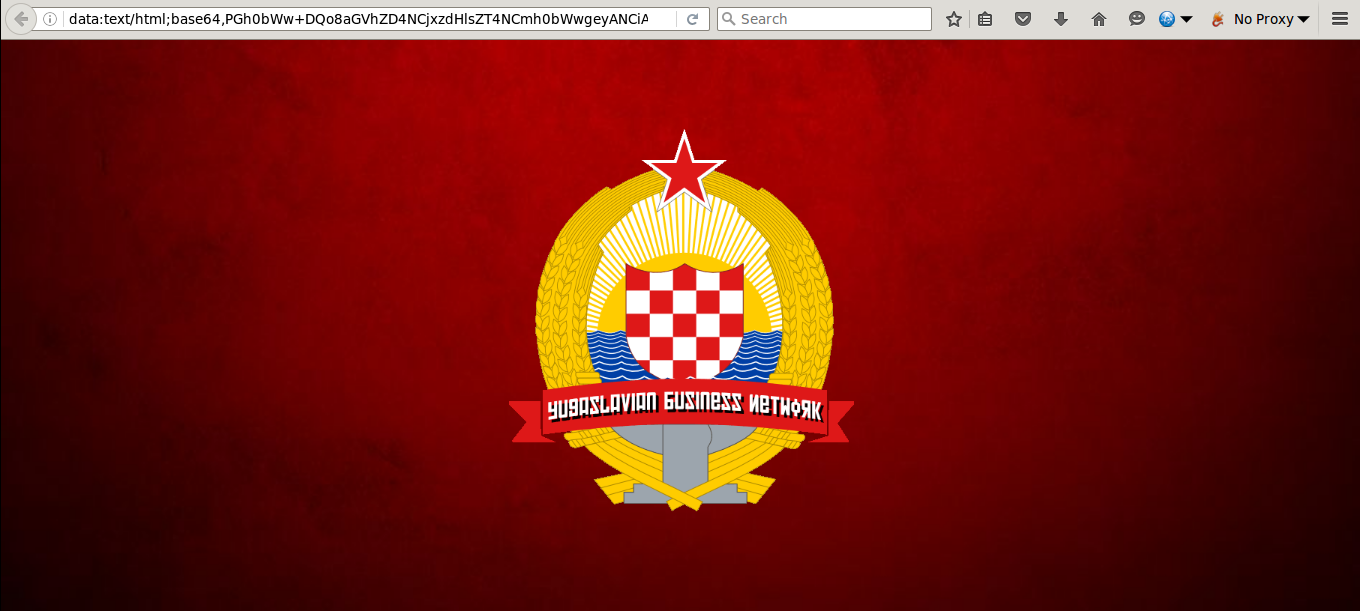
114MalwareInfoArmor Uncovers Malicious Torrent Distribution Network
InfoArmor has identified a special tool used by cybercriminals to distribute malware by packaging it with the most popular torrent files on...
-

 100Malware
100MalwareDualToy Windows Trojan Secretly Sideloads Apps on Android and iOS Devices
Number of DualToy infections is on the rise. A trojan targeting Windows computers is secretly sideloading mobile applications to any Android or iOS...
-
 97Vulnerabilities
97VulnerabilitiesSundown Is Just a Bunch of Exploits Stolen from Other Exploit Kits
Sundown EK fails to improve market share among fellow EKs. The Sundown exploit kit (EK), which has been trying to fill the void...
-
 73Malware
73MalwareThe Hunt for Lurk
When we first encountered Lurk, in 2011, it was a nameless Trojan. It all started when we became aware of a number...
-

 112Data Security
112Data SecurityJBifrost: Yet Another Incarnation of the Adwind RAT
The Adwind Remote Access Trojan (RAT) is a popular Java-based backdoor capable of infecting Windows, Linux, Mac OS and Android operating systems....
-
 210Malware
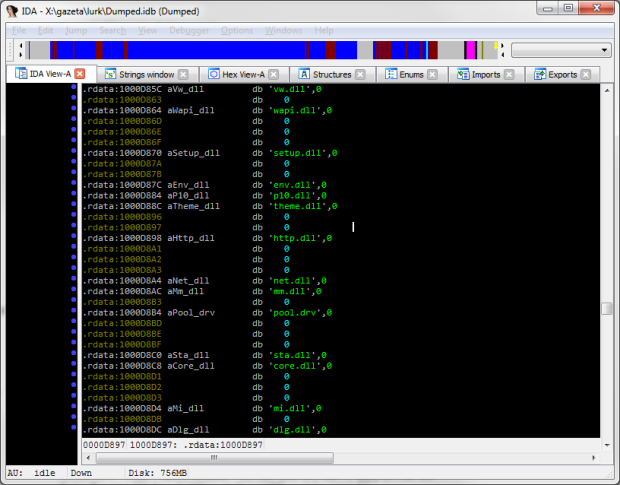
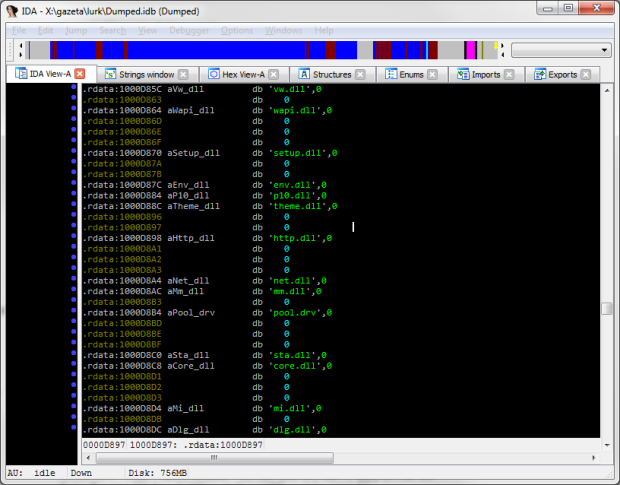
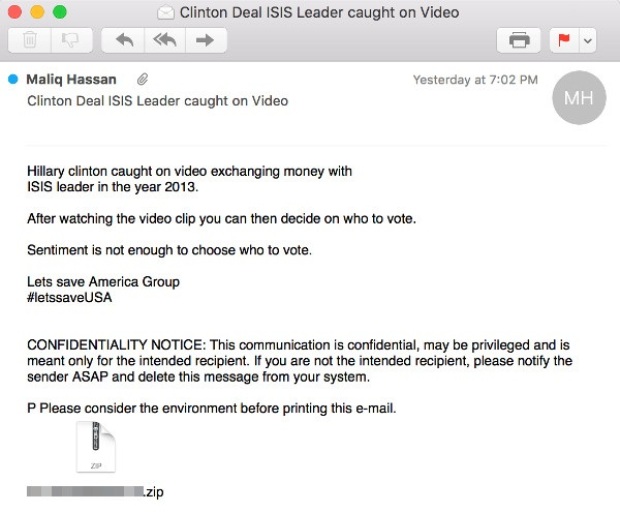
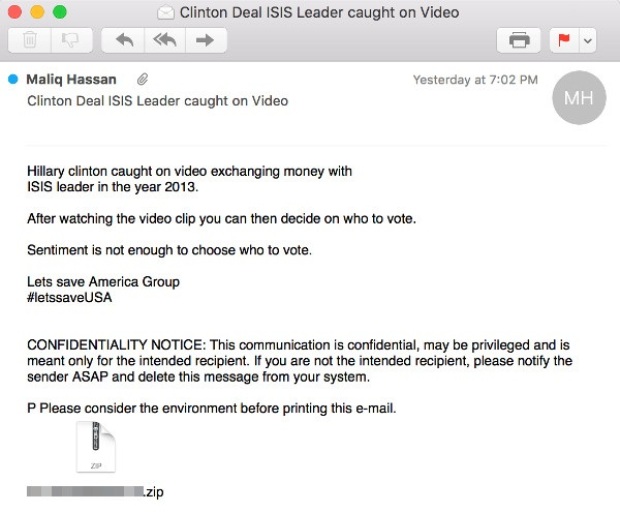
210MalwareNon-existent video involving Hillary Clinton and ISIS leader used as bait in malicious spam
Malicious attachment contains Adwind cross-platform remote access Trojan. Cybercriminals are using clickbait, promising a video showing Democratic Party presidential nominee Hillary Clinton exchanging...
-

 156Vulnerabilities
156VulnerabilitiesNew Information Stealing Trojan Steals and Uploads Corporate Files
Corporate cybercrime and information theft has become a very lucrative business for malware developers. Not only does it allow them to steal corporate...
-

 187Incidents
187IncidentsHow hackers used this Trojan malware to spy on a territorial dispute
F-Secure researchers say parties involved in the South China Sea arbitration case were infected with the data-stealing NanHaiShu Trojan. Hackers have used...
-
 191Malware
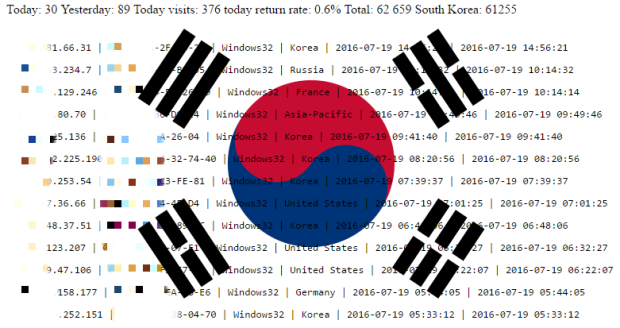
191MalwareBlackMoon Banking Trojan Infected over 160,000 South Koreans
The crooks behind the recent campaign may be from China. Over 100,000 South Koreans had their banking credentials stolen by crooks who...
-

 87Malware
87MalwareDelilah, the first Trojan to recruit Insiders
Delilah is the first extortion trojan that spies on victims and collects information to force them in doing malicious activities from inside....
-

 102Malware
102MalwareAGGRESSIVE TRIADA, HORDE VARIANTS UP MOBILE MALWARE THREAT
Two mobile variants of Triada and Horde malware have been spotted in the wild by Check Point Software Technologies researchers who warn the...
-

 123Malware
123MalwareLurk Banker Trojan: Exclusively for Russia
One piece of advice that often appears in closed message boards used by Russian cybercriminals is “Don’t work with RU”. This is...
-

 175Incidents
175IncidentsAndroid Trojan Hijacks Browsers to Redirect Users to Custom URLs
Crooks use brand new potent feature to just show adware. A previously discovered and highly dangerous Android trojan has received an update in...
-
 96Malware
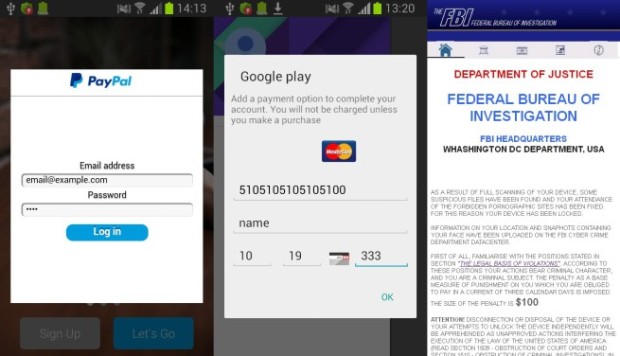
96MalwareAndroid.SmsSpy.88.origin
A Trojan for Android designed to steal user login credentials needed to access online banking programs and to steal money from victims’...
-

 162Incidents
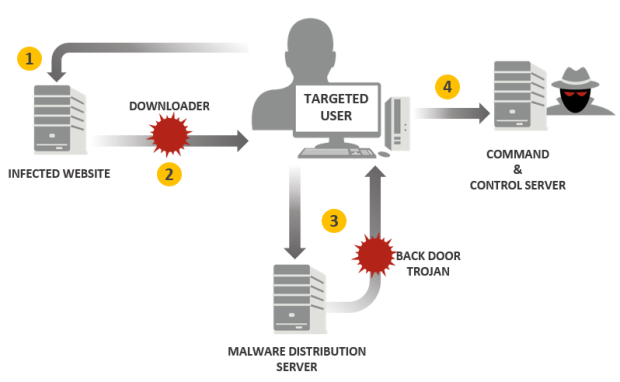
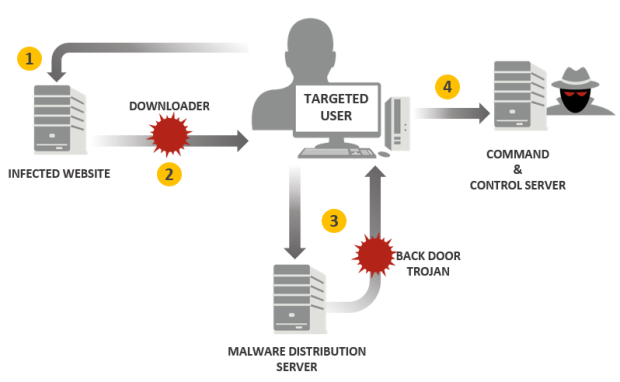
162IncidentsNew backdoor attacks Windows users
Backdoors are typically designed to execute cybercriminals’ commands on the infected machine. As a rule, they are used to gain a remote...
-

 159Malware
159MalwareNew Skype spam leads to Trojan download
Today, we’ve been alerted about an ongoing spam campaign against Skype users. The majority of those affected are in India, Japan, and...
-

 178Data Security
178Data SecurityPetya: the two-in-one trojan
Today, we have encountered a new threat that’s a blast from the past. The Petya Trojan (detected by Kaspersky Lab products as...
-
 183Data Security
183Data SecurityTick cyberespionage group zeros in on Japan
Compromised websites and spear-phishing emails used to infect targets with Daserf Trojan. A longstanding cyberespionage campaign has been targeting mainly Japanese organizations with...
-

 190Hacked
190HackedUSB Thief — This Self-projecting USB Trojan Can Give You Nightmares
Short Bytes: Security researchers have identified a new malware named USB Thief that has the ability to steal data from air-gapped computers without leaving...
-

 179Malware
179MalwareDridex: Financial Trojan aggressively spread in millions of spam emails each day
Built to harvest the banking credentials of victims, the virulent Dridex is now one of the most dangerous pieces of financial malware...






