All posts tagged "USB"
-
 332Data Security
332Data SecurityNew Intel CPUs Can Be “Hacked” Using The USB Port And A Hardware Feature
Short Bytes: On Modern Intel CPUs, the USB 3.0 port can be used to access the hardware debugging interface JTAG via DCI....
-
 224Data Security
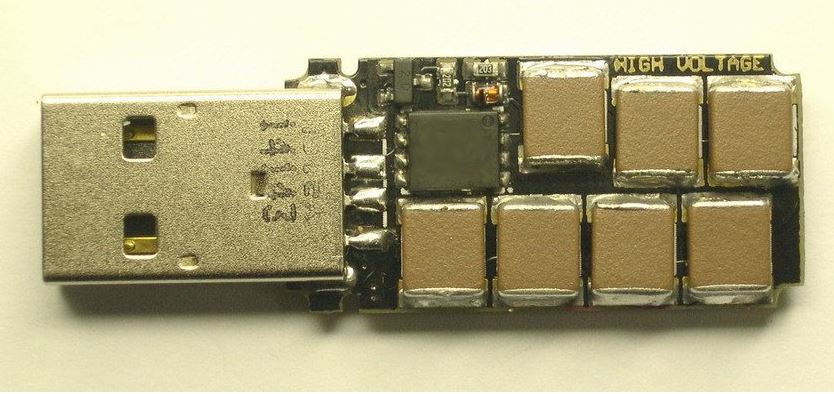
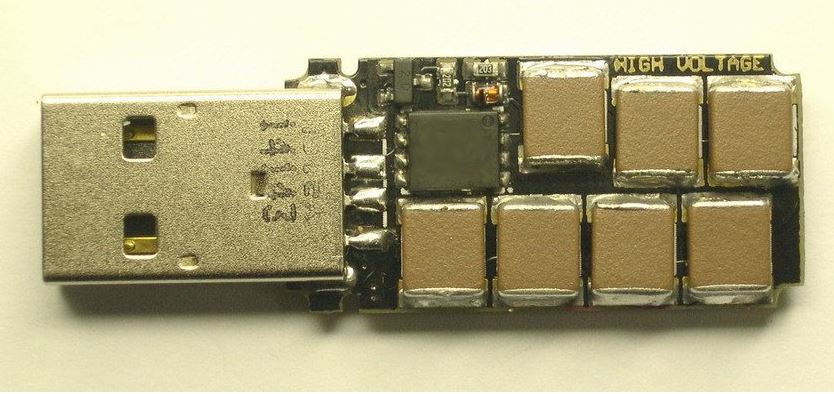
224Data SecurityUSB Killer, yours for $50, lets you easily fry almost every device
Only real defense for billions of devices is physically capping ports. Last year we wrote about the “USB Killer”—a DIY USB stick...
-

 185Hacked
185HackedThis USB Killer, Made From Camera Flash Parts, Is Your Computer’s Worst Enemy
Short Bytes: Infecting people’s computers with the help of malicious USB drives is an old trick being used by hackers even today. Going...
-

 305How To
305How ToHow To Build A “USB Password Generator” To Create And Enter Passwords Automatically
Short Bytes: Willing to own your personal USB key that takes care of your password changing tasks? Using a USB, an ATtiny85,...
-

 122How To
122How ToLock and unlock your computer with a USB drive, Like A Hacker
If you prevent access to your computer with just a password, you are missing out on an alternate (and more secure) way...
-
How To
How to Format a Write Protected USB Flash Drive Using Command Line
32GB of sweet USB flash drive storage space just sits in your office drawer, ironically taking up space. Why? Because you can’t...
-

 183How To
183How ToWAS – Automatic USB Drive Malware Scanning Tool
WAS, is a simple automatic USB drive malware scanning tool that helps for people who often be in a hurry or absent...
-

 183Data Security
183Data SecurityNow you can buy USB Kill that could fry your PC via USB
The manufacturer USBKill.com has commercialized USB Kill 2.0, a USB dongle that is able to fry any computer through the USB ports....
-

 282Hacked
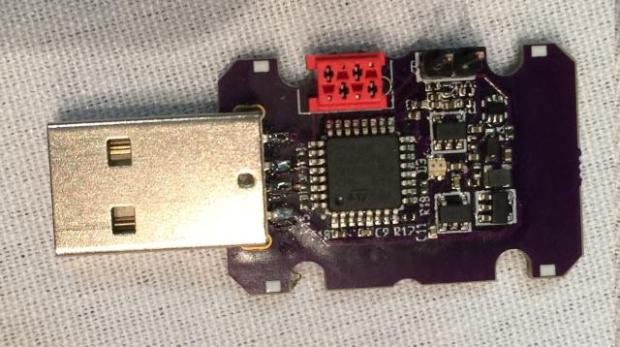
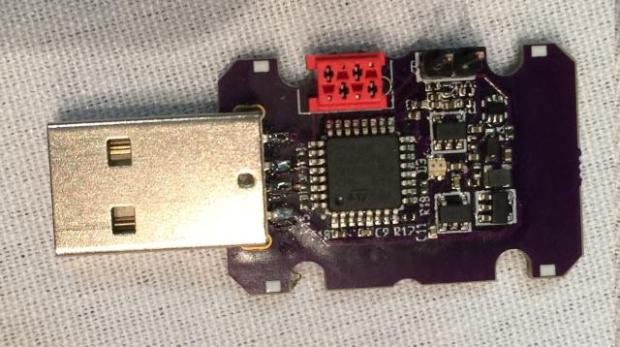
282HackedThis Ruthless USB Killer Can Give Your PC A Painful Death, Now Up For Sale
USB Tester Short Bytes: The USB Killer stick that made headlines last year for being a brutal death to your innocent hardware...
-

 198Data Security
198Data SecurityHow to sniff credentials from locked laptops via Ethernet adapter on USB
First off, this is dead simple and shouldn’t work, but it does. Also, there is no possible way that I’m the first...
-

 312Hacked
312HackedUSBee — Malware That Uses Any USB Drive To Hack Isolated Computers
An ordinary USB drive (A) is sending information to a receiver (B) Short Bytes: A team of Israel’s Ben-Gurion University has developed a...
-
 107Data Security
107Data SecurityChaosKey: This is a hardware True Random Number Generator that attaches via USB.
This is a hardware True Random Number Generator that attaches via USB. Version 0.3 This one uses the better noise source coupled...
-
 174Vulnerabilities
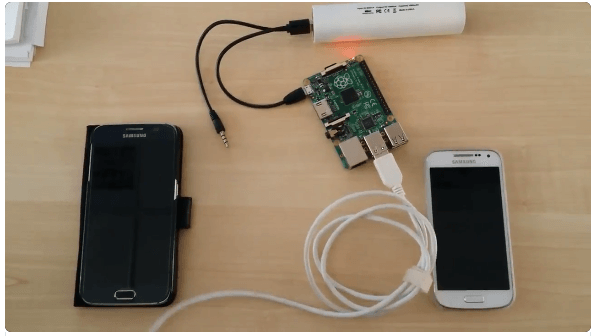
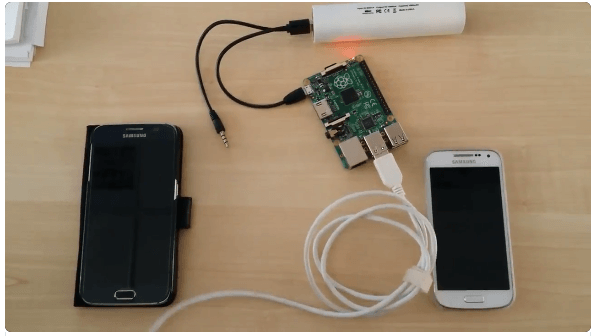
174VulnerabilitiesHacking Samsung Galaxy via Modem interface exposed via USB
Modems in a number of Samsung Galaxy devices are open to receiving AT commands over the USB cable even when they are...
-

 197Hacked
197HackedUSB Thief — This Self-projecting USB Trojan Can Give You Nightmares
Short Bytes: Security researchers have identified a new malware named USB Thief that has the ability to steal data from air-gapped computers without leaving...
-

 170Geek
170GeekKingston’s DataTraveler 2000 Provides Undisputed Security and Encryption
A new USB device series has been launched by Kingston aiming to provide secure and tamper-proof thumb drive to IT professionals while...
-

 184Hacked
184HackedUSB Killer Version 2.0 Burns and Destroys Your Computer
Short Bytes: The maker of USB Killer is here with the USB Killer version 2.0 – a more advanced version of the...
-

 160Data Security
160Data SecurityChrysler Catches Flak for Patching Hack Via Mailed USB
Six weeks after hackers revealed vulnerabilities in a 2014 Jeep Cherokee that they could use to take over its transmission and brakes,...
-
 201Geek
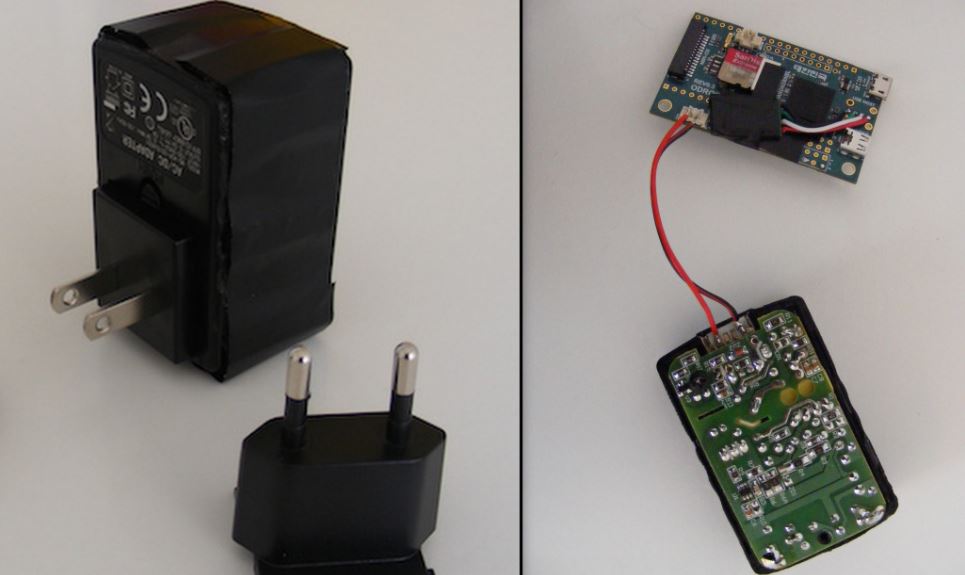
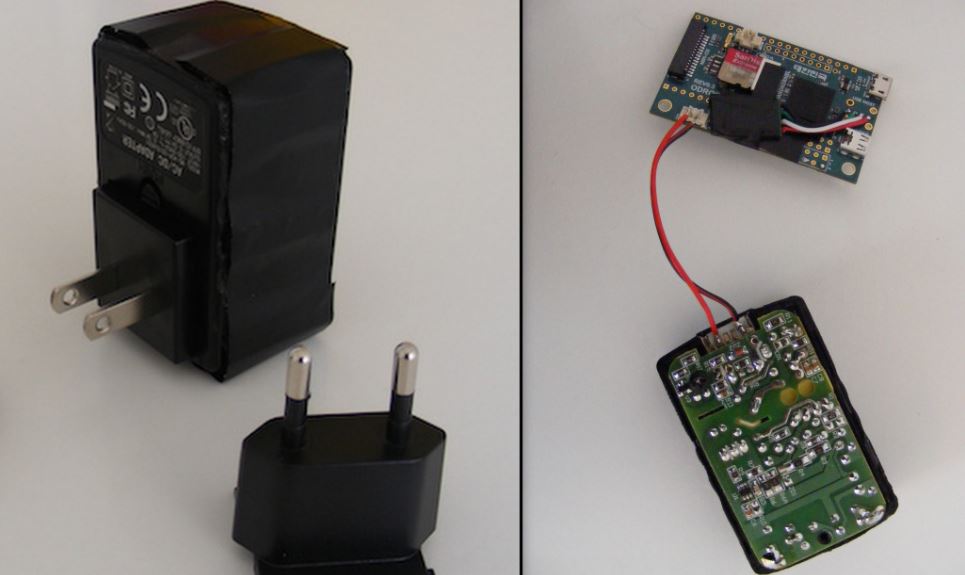
201GeekHow to Convert a USB Charger Into a Linux Computer
Short Bytes: This DIY from Chris Robinson of NODE will show you how to make your own Linux computer from a USB...
-
 339Hacked
339HackedUSBkill – Code That Turns USB Drives Into PC Killing Weapon
Here’s a news that will cheer up all the activists, criminals, activists and whistle blowers. Now they have got a new tool...
-

 333Data Security
333Data SecurityBeware– This Killer USB Drive Can Fry Your Laptop
The killer USB Drive has been designed especially to burn laptops – So be careful while inserting someone’s USB on your laptop. Have you heard...
-
 259Hacked
259HackedThis “Killer USB” Flash Drive Will Explode Your Computer
The Killer USB USB drives are known be humble creatures that help you out by transferring your data. But, what if a...






