All posts tagged "vulnerability"
-

 273Data Security
273Data SecurityWordPress Websites Exposed to Severe Content Injection Vulnerability
WordPress is one of the most used content management system (CMS) in the world. So when there is a security flaw in...
-

 350Vulnerabilities
350VulnerabilitiesWordPress Publishes Critical Security Update XSS, SQL Injection vulnerabilities
WordPress 4.7.1 and earlier forms are influenced by various vulnerabilities. A remote attacker could exploit some of these vulnerabilities to take control...
-

 282How To
282How ToSee How Android Pattern Lock Can Be Cracked In Just 5 Attempts
Pattern lock on Android smartphones might be the quickest and simplest way to gain get entry to to the device. a collection of...
-
 342News
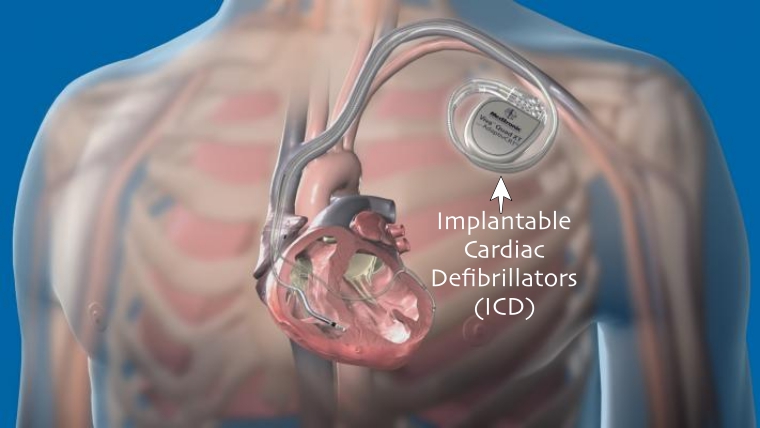
342NewsAfter IoTs, it is the IMDs that are Most Vulnerable to Hacking
Researchers from UK and Belgium have jointly conducted a research and concluded that hacking into implantable medical devices or IMDs is as...
-
How To
How to Scan for SMB vulnerabilities using Nmap
Hi there my fellow hackers, we are back with another tutorial. Today we will see how we can use a Nmap script...
-

 108News
108NewsFirefox vulnerable to Malicious Add On Attacks
Firefox is vulnerable to a Malicious Add On Attacks. A critical vulnerability which is in the fully patched version of the Mozilla’s...
-
 245Vulnerabilities
245VulnerabilitiesQuadRooter: New Android Vulnerabilities in Over 900 Million Devices
Check Point today disclosed details about a set of four vulnerabilities affecting 900 million Android smartphones and tablets that use Qualcomm® chipsets....
-
 228News
228NewsAutomated Web Application Scanner Acunetix Website Hacked
The developers of Acunetix vulnerability scanner tool had their website defaced by a hacker who claims he did it for Lulz! An...
-

 172Hacked
172HackedNo Time For QuickTime: Uninstall It ASAP
Short Bytes: A security firm Trend Micro has announced a call to action on the situation that Apple is deprecating QuickTime for...
-

 374Cyber Events
374Cyber EventsProgram Languages That Generate Most Software Security Bugs
You maybe a top notch developer or programmer but do you know which program languages generate most software security bugs? Recently, a lot...
-

 264Data Security
264Data SecurityHacker Earns 50k Miles by Exposing Vulnerability in United Airlines Website
Earlier this year we reported about security measures taken by United Airlines that they’ll give you up to a million miles to...
-

 310Geek
310GeekMicrosoft Windows Devices Responsible For 80% of Malware Infections
Microsoft Windows, in spite of having an insignificant share in the mobile market, is the leading operating system that is responsible for...
-

 377Data Security
377Data SecuritySecurity Flaw in Millions of Websites Leave Users Vulnerable to Ransomware
Potential Security Flaw In Obsolete CMS and Plugins Left Millions of Users Vulnerable To Ransomware. More than 142 million websites have been...
-

 280Data Security
280Data SecurityHackers Can Replace Apps on Your Android Device with New Vulnerability
The Zero-day vulnerability presented by IBM’s researchers Or Peles and Roee Hay will affect all Android devices. The two researchers from IBM’s...
-

 169Surveillance
169SurveillanceExposing Facebook privacy flaw is a crime? Sure Seems Like It
Aran Khanna, a Harvard student, was deprived of a chance to intern at Facebook after he exposed a critical privacy related flaw...
-

 226Data Security
226Data SecurityFacebook API Security Flaw Left 1.44 Billion Users’ Identities at Risk
A security flaw in the Facebook API allows hackers to decrypt and scan IDs, which left 1.44 billion Facebook users identities at...
-
 297Geek
297GeekAndroid Stagefright Bug Is Critical, Let Hackers Snoop into Your Phone Silently
Are you an Android phone user? Please pay attention as now it only takes one text message to hack an Android phone....
-
 279News
279NewsHacker uses Toy to Hack and Open Garage Doors in Seconds
An electronic Mattel toy was transformed into a tool by Samy Kamkar to unlock all kinds of fixed-code garage doors within seconds....
-

 223Data Security
223Data SecurityNotion of Cloud’s Unmatched Security Shattered by ‘Venom’ vulnerability
The CrowStrike researchers discovered that any attacker can burst out of specific virtual machines and exploit whatever is running nearby — The...
-

 342Data Security
342Data SecurityXSS Vulnerability Found in Famous WordPress Plugins
Researchers have identified a relatively “common” cross-site scripting flaw (XSS) in some famous WordPress plugins — A coordinated plugin update has been released to...
-

 279Data Security
279Data SecurityFlash Player Bug Records Audio and Video without User Permission
Researchers have identified a vulnerability in some Adobe Flash Player versions that can be exploited by attackers for spying on users having...






