All posts tagged "Windows"
-

 2.1KMalware
2.1KMalwareRaaS – Hackers Selling Buran Ransomware in Russian Forum That Encrypt All Version of Windows OS & Windows Server
Researchers uncovered a new ransomware family named “Buran” ransomware that works as a Ransomware-as-a-Service(RaaS) model and actively selling in a well-known Russian...
-

 2.6KHacked
2.6KHackedFirst Windows ‘BlueKeep’ Attacks Spotted Installing Cryptocurrency Miners
Back in May 2019, Microsoft revealed details about a severe hackable flaw that exists in the Remote Desktop Protocol (RDP) in Windows...
-
 5.6KMalware
5.6KMalwareHackers Launching Obfuscated RAT & Spyware To Log Keystroke and Steal Passwords from Windows Apps
Researchers discovered a new malicious campaign that delivered Different payloads such as Agent Tesla spyware and Ave Maria RAT To steal username...
-

 4.9KData Security
4.9KData SecurityNew malware targets Discord users to steal personal data
One of the most frequently used messenger services out there is Discord among others. Lately, they have been in trouble due to...
-
 407Malware
407MalwareWinnti Hacker Group Uses New Malware to Hack Microsoft SQL Servers
Winnti hacker group uses a new malware dubbed skip-2.0 to attack Microsoft SQL Servers and to gain persistence access. Winnti group believed...
-

 652Malware
652MalwareWinnti Hackers Group Launching New Malware via Supply-chain Attacks to Inject Backdoor in Windows
Researchers discovered a new malware campaign from the Winnti threat group that utilizes the supply-chain attacks with a new set of artifacts to...
-

 618Geek
618GeekWindows licenses for under 10 HR20
Windows licenses are usually expensive. For example, for an original license of Microsoft’s “Windows 10 Pro” in the official Microsoft store 199.99$...
-
 588Ransomware
588RansomwareApple iTunes for Windows Zero-day Exploited by BitPaymer Ransomware
Researchers found a new footprint about the recent BitPaymer ransomware campaign that was exploited the Apple iTunes for Windows Zero-day vulnerability to...
-

 383Vulnerabilities
383VulnerabilitiesCritical iTunes vulnerability exploited by ransomware. Update now
A couple of months ago, a team of digtial forensics specialists from security firm Morphisec discovered a malicious campaign that used a...
-
 361Malware
361MalwareBeware!! New “Nodersok” Fileless Malware Hack Windows PC and Change into Zombie Proxies
Microsoft issued a serious warning about the new form of stealthy fileless Malware campaign “Nodersok” that attacks windows computers using living-off-the-land techniques....
-

 434Hacked
434HackedThousands Of Windows PCs Affected By Rare Node.js-Based Malware
Microsoft has confirmed that a Node.js-based malware dubbed Nodersok has affected thousands of Windows PCs over several weeks. This new strain of...
-
 388Data Security
388Data SecurityMalware called InnfiRAT is creeping into cryptocurrency wallets
Cryptocurrencies have been known to be the cause of fortune for quite a few people. It all started from 2009 and even...
-
 437Geek
437GeekUpdate Windows 10: 800 million devices at risk of critical vulnerability
According to Microsoft, unprotected servers can spread viruses and malware over the network without the user’s interaction. Microsoft is warning users to...
-
 384Vulnerabilities
384VulnerabilitiesNew SWAPGS vulnerability on Windows affects Intel and AMD CPUs
Vulnerability testing specialists have revealed a security vulnerability that affects all Windows operating system computers running on Intel and AMD 64-bit processors....
-
 366How To
366How ToCommon installation errors with Microsoft Office & how to avoid them
If you have recently purchased Microsoft Office from a genuine Microsoft reseller, the process of installation is as easy and simple as...
-
 300News
300NewsLatest Versions of Windows 10 Are More Secure Against Zero-Day Attacks
According to Matt Miller, a security engineer with the Microsoft Security Response Center, many zero-day vulnerabilities are ineffective against the newest versions...
-
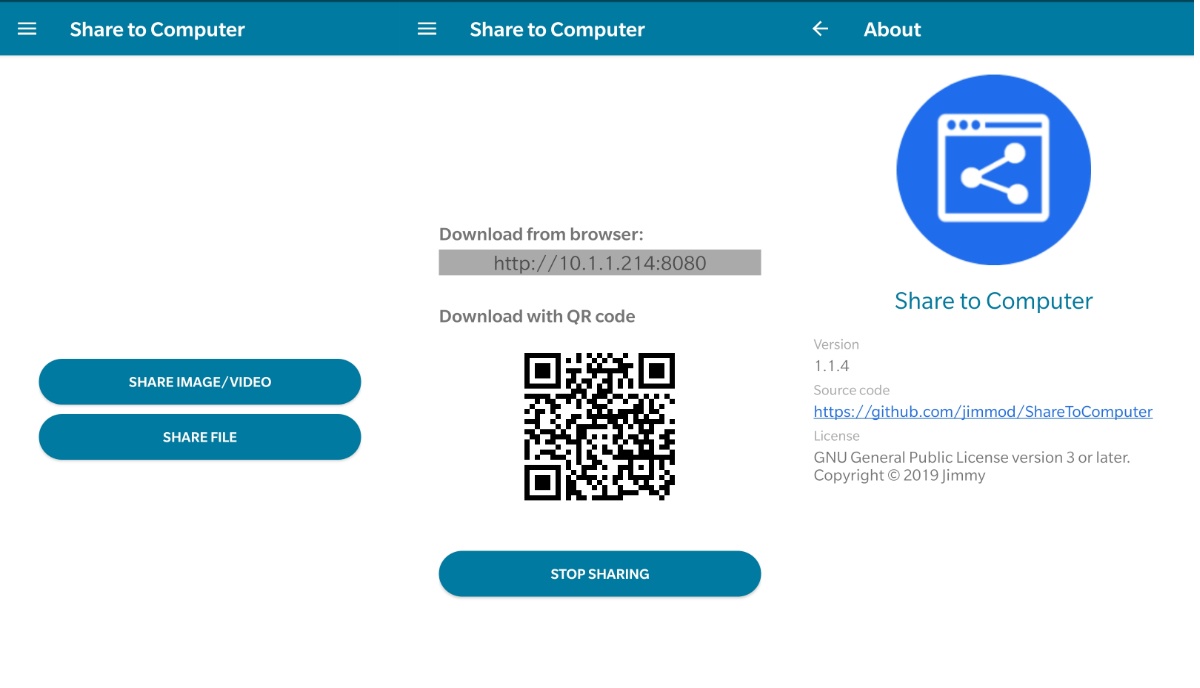
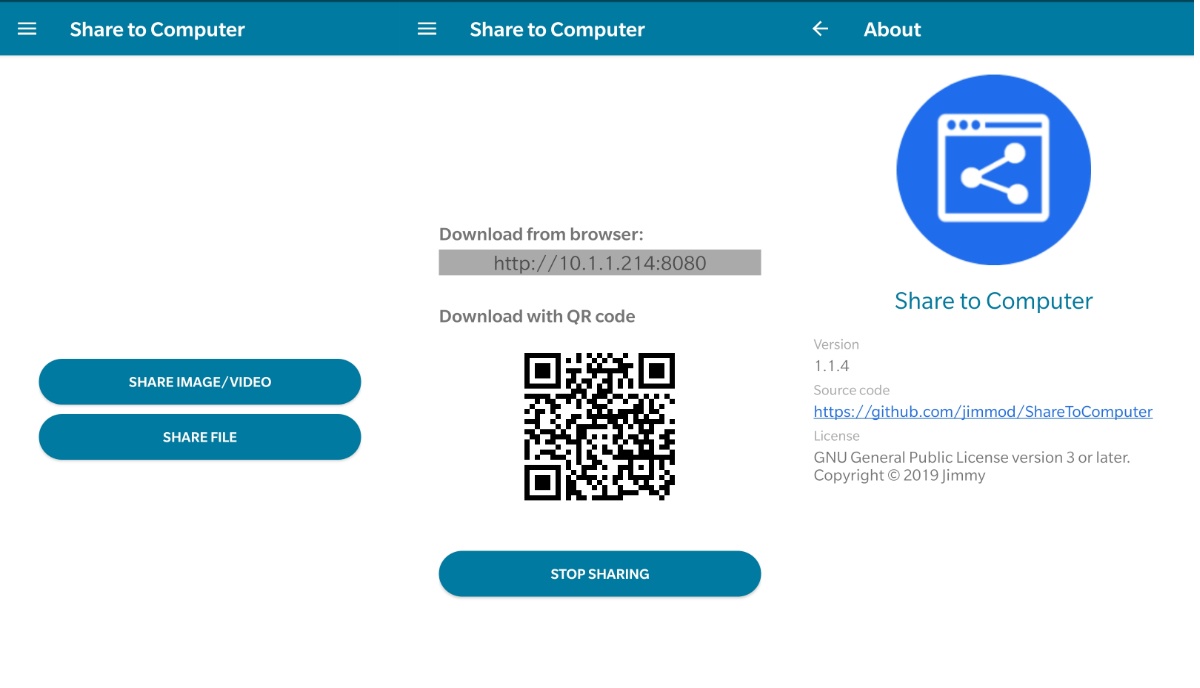 260News
260NewsThis Open Source App Lets You Share Files Between PC & Smartphones Easily
There are a ton of software to share files between phone and PC; however, I have never encountered file-sharing software that is...
-

 368Malware
368MalwareNew ransomware infects Windows machines even without clicking or opening an email
Specialists in ethical hacking from the cybersecurity firm Kaspersky reported the discovery of a new ransomware variant much more dangerous than encryption...
-
 448News
448NewsMicrosoft Teases ‘Windows 1.0’ In 2019 And The Internet Is More Confused Than Ever
All of a sudden, a couple of days ago, Microsoft reached out to its Twitter handle and started teasing the good old...
-
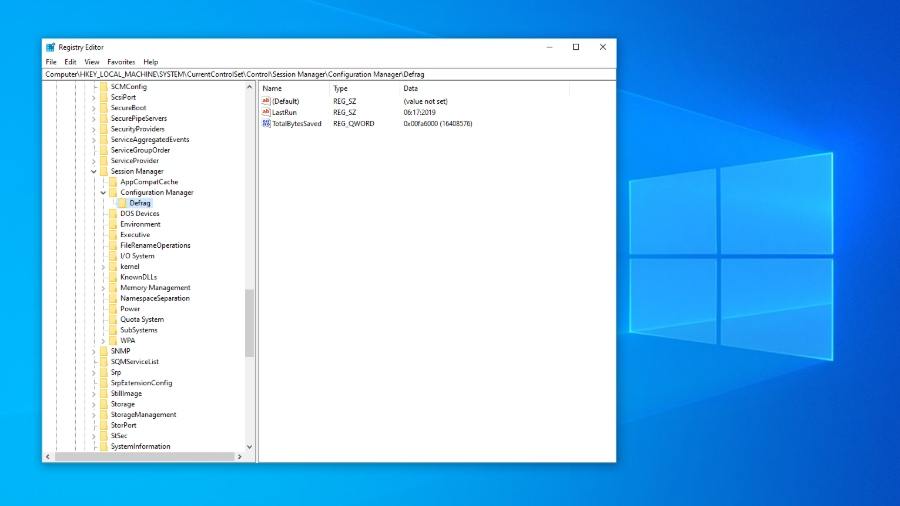
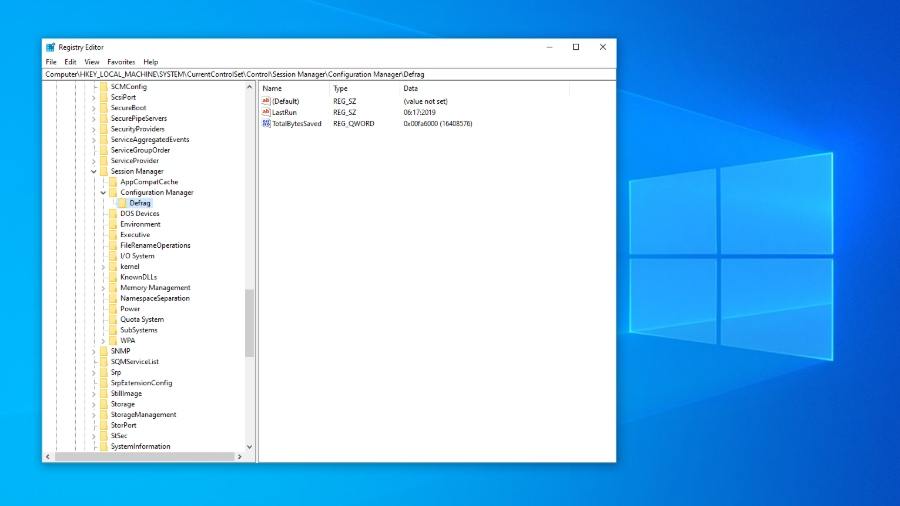 381News
381NewsMicrosoft Explains Why 800 Million Windows 10 Users Can’t Auto Backup Registry
If you’re a Windows user, chances are quite less you haven’t opened Windows Registry after tweaking some values just the way a...
-

 355Geek
355GeekNew Windows 10 bug causes PCs to take longer to shut down
Windows 10 bug: If you have a device connected via cable to the USB Type-C input, you may have to wait another...






