All posts tagged "android"
-

 189Geek
189GeekHundreds of Android Apps on Google Play Store Infected with Windows Malware
Android apps have always remained an easy target of exploitation primarily because of the high number of Android users across the globe. In the latest research...
-

 349News
349NewsAndroid Password Manager You Trust Could be Exposing Login Data
According to the latest findings from TeamSIK, a group of security researchers associated with Darmstadt, Germany-based Fraunhofer Institute for Secure Information Technology,...
-
 272Ransomware
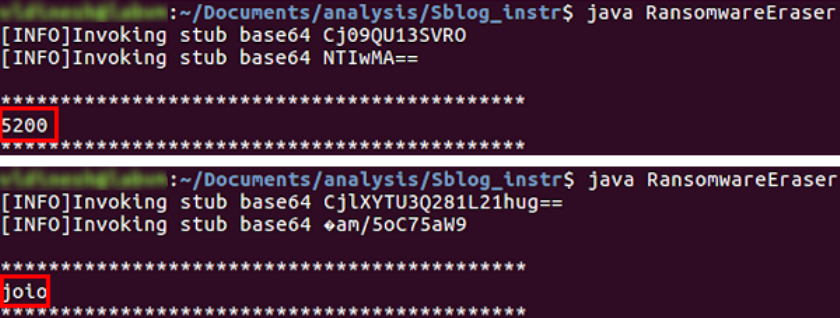
272RansomwareHumorous Android ransomware force victim to speak unlock code
Android Malware which has admirable listening quality, force victim to speak unlock code. The latest variant of the Android ransomware named Android.Lockdroid.E...
-
 97Malware
97MalwareAndroid ransomware requires victim to speak unlock code
Latest Android.Lockdroid.E variant uses speech recognition instead of typing for unlock code input. Being a good listener is normally considered an admirable...
-

 233Data Security
233Data SecurityBitTorrent distribution sites dropping crypto-ransomware on macOS
Cybercriminals prefer crypto-ransomware as it not only successfully targets Windows desktop but also those devices that run on MacOS or Linux. Now,...
-
 263Malware
263MalwareReleased Android malware source code used to run a banking botnet
The new Android banking malware ESET recently discovered on Google Play was spotted in the wild again, targeting more banks. Further investigation...
-

 409Geek
409GeekHow to Install TOR on Android and iOS Devices
You can safeguard your online privacy when you are using an Android or iOS device to browse the internet by using TOR....
-

 229Vulnerabilities
229Vulnerabilities‘Android for Work’ Security Containers Bypassed with Relative Ease
Mobile security experts from Skycure have found two methods for bypassing the security containers put around “Android for Work,” allowing attackers to...
-
 266Cyber Crime
266Cyber CrimeIDF targeted by sophisticated cyber espionage through Android devices
Israeli members of the armed forces have remained under the radar of cyber spies and espionage actors for a very long time....
-

 185Hacked
185HackedGoogle’s Verify Apps Service Now Kills Harmful Apps From Your Device Automatically
Short Bytes: Verify Apps is a cloud-based security feature in the Android operating system. It regularly scans the device for potentially malicious...
-

 75Vulnerabilities
75VulnerabilitiesPhwning the boardroom: hacking an Android conference phone
At Context we’re always on the lookout for interesting devices to play with. Sat in a meeting room one day, we noticed...
-

 197Data Security
197Data SecurityISIS Supporters Targeted with Android OmniRAT Malware
Islamic State supporters are being targeted with a modified version of the Telegram Android app that contains a version of the OmniRAT...
-

 157Malware
157MalwareNew Mac malware pinned on same Russian group blamed for election hacks
Xagent for Macs steals passwords, grabs screenshots, and exfiltrates iPhone backups. APT28, the Russian hacking group tied to last year’s interference in...
-

 104Geek
104GeekAndroid Banking Trojan Marcher Infects Devices to Steal Payment Cards
Cyber-security researchers at Securify, a Dutch security firm, have been evaluating the Marcher Android banking Trojan for the past six months. They...
-
 134Data Security
134Data SecurityAndroid Ad Malware on Google Play Combines Three Deception Techniques
Three apps on Google Play use delayed attacks, self-naming tricks, and an attack list dictated by a command and control server to...
-

 187How To
187How ToHow To Download And Install Android Nougat 7.1.2 Beta
The Android Nougat 7.1.2 Beta is for developers, but as before anyone will be able to install it on a compatible device. Read...
-

 303Geek
303GeekFake Netflix, WhatsApp, Facebook Android Apps Contain SpyNote RAT
Cyber criminals prefer targeting Android devices due to its open-source model which means the source code is freely available for anyone to...
-

 152Geek
152Geek38% of Android VPN Apps on Google Play Store Plagued with Malware
Downloading an application means that you are allowing the software open access to your mobile phone and all the data that is...
-

 278Geek
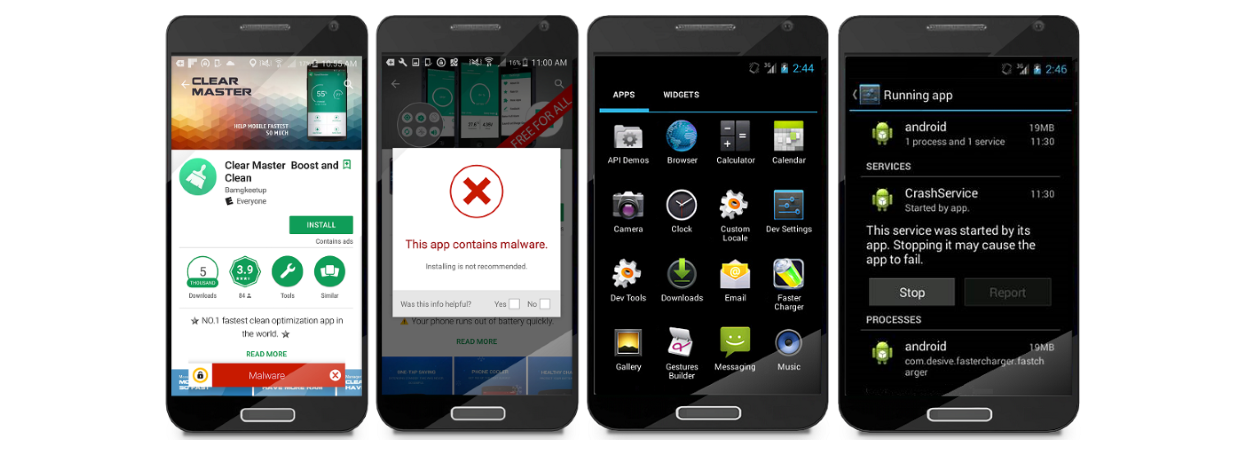
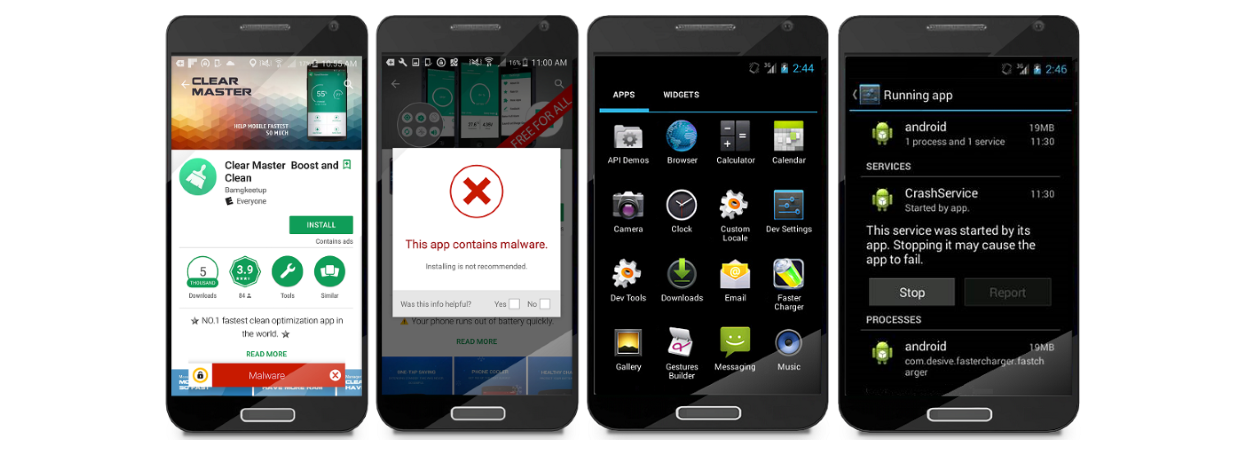
278GeekMalicious “Charger Ransomware” App Discovered on Google Play Store
CheckPoint, a renowned security firm, has discovered that at least one app on Google Play Store is infected with Charger Malware. Charger...
-

 281How To
281How ToSee How Android Pattern Lock Can Be Cracked In Just 5 Attempts
Pattern lock on Android smartphones might be the quickest and simplest way to gain get entry to to the device. a collection of...
-

 299Geek
299GeekHummingWhale Malware infected Android Apps Downloaded Millions of Times
CheckPoint security firm has detected a presence of the notorious HummingWhale malware in 20 Android apps, which are quite commonly used by Android...






