All posts tagged "Attack"
-
 1.0KWeb Application Security
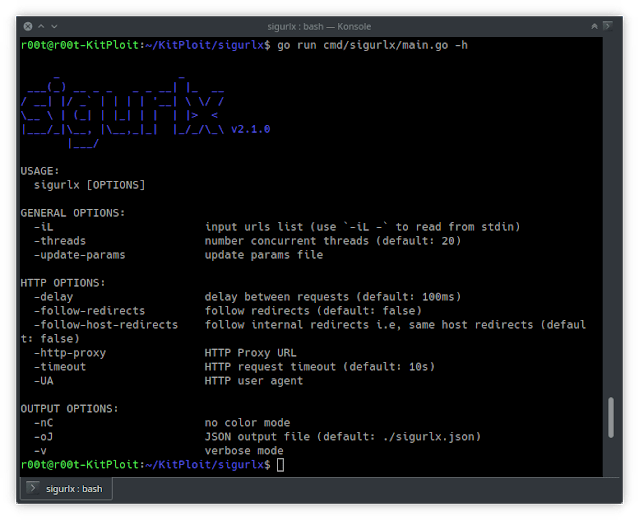
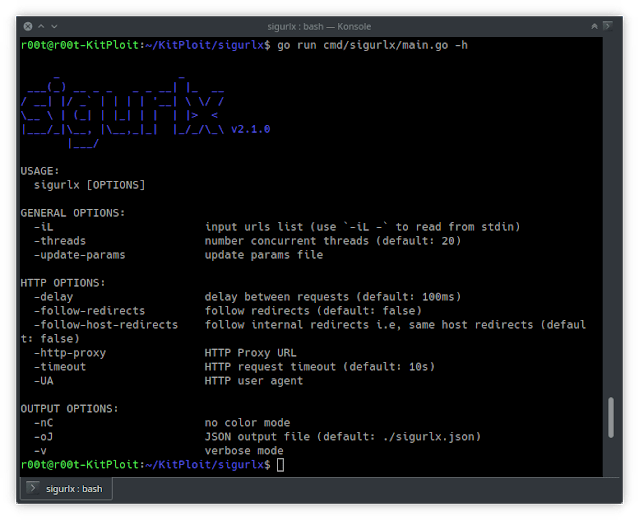
1.0KWeb Application SecuritySigurlx – A Web Application Attack Surface Mapping Tool
sigurlx a web application attack surface mapping tool, it does …: Categorize URLs URLs’ categories: > endpoint > js {js} >...
-
 388System Administration
388System AdministrationKube-Alien – Tool To Launches Attack on K8s Cluster from Within
This tool launches attack on k8s cluster from within. That means you already need to have an access with permission to...
-

 359Wireless Attacks
359Wireless AttacksSKA – Simple Karma Attack (Evil Twin Attack)
SKA allows you to implement a very simple and fast karma attack. You can sniff probe requests to choice the fake...
-

 513Password Attacks
513Password AttacksW3Brute – Automatic Web Application Brute Force Attack Tool
w3brute is an open source penetration testing tool that automates attacks directly to the website’s login page. w3brute is also supported for...
-

 223Data Security
223Data SecurityHow to do reconnaissance attack over your target the correct way
A team of information security experts explains that a domain name represents some kind of label for IP addresses on the Internet....
-

 353Incidents
353IncidentsHow to make a Subdomain Takeover Attack
A team of information security experts tells us that sub-domain acquisition vulnerabilities happen whenever a subdomain points to a service (for example,...
-

 346Information Gathering
346Information GatheringHow to Gather Email Addresses with TheHarvester – Kali Linux 2018.1
theHarvester is a tool for gathering e-mail accounts, subdomain names, virtual hosts, open ports/ banners, and employee names from different public sources...
-
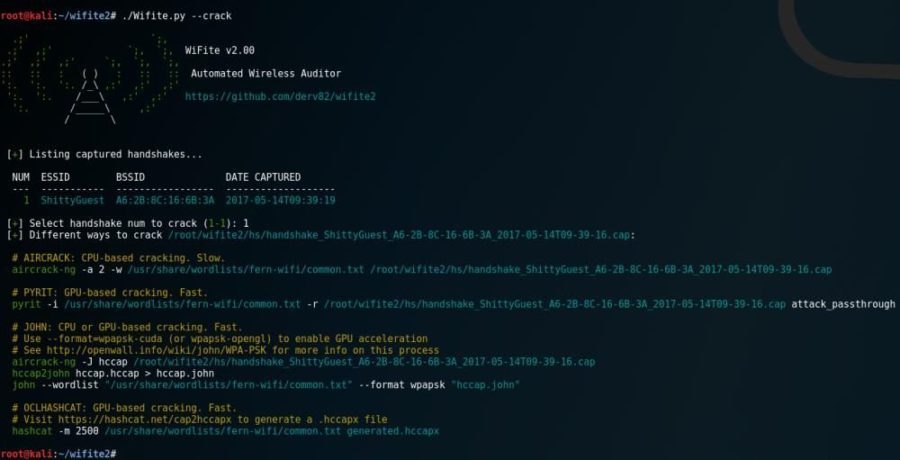
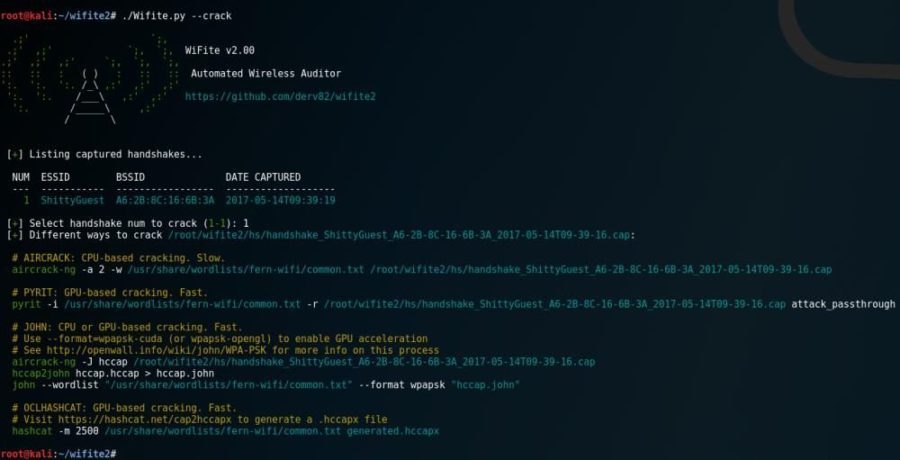 240Wireless Attacks
240Wireless AttacksWiFite 2 – Automated Wireless Attack Tool
Wifite is a Python script for auditing wireless networks which aims to be the “set it and forget it” wireless auditing tool. ...
-

 236Exploitation Tools
236Exploitation Toolsshimit – A tool that implements the Golden SAML attack
shimit is a python tool that implements the Golden SAML attack. python .shimit.py -h usage: shimit.py [-h] -pk KEY [-c CERT] [-sp SP]...
-

 243Cyber Crime
243Cyber CrimeCyber security and strategy
Cybersecurity is a practice that ensures that all the information, confidentiality and availability are intact and not compromised with. It depends on...
-
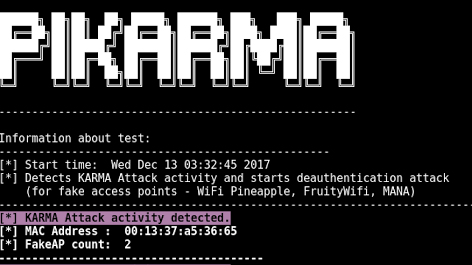
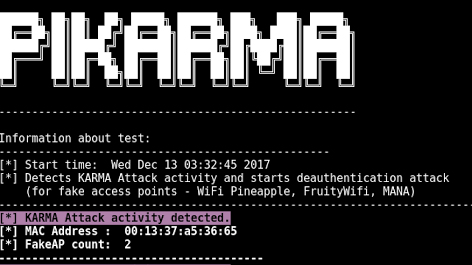 256Wireless Attacks
256Wireless AttacksPiKarma – Detects Wireless Network Attacks
Detects wireless network attacks performed by KARMA module (fake AP). Starts deauthentication attack (for fake access points) Working Principle for PiKarma Collects...
-

 316Cyber Crime
316Cyber Crime2018 cybersecurity trends and predictions
The year 2017 was quite exciting as we came across several new things from Ransomware to IoT malware and more. Several industries...
-
 272Man-In-The-Middle
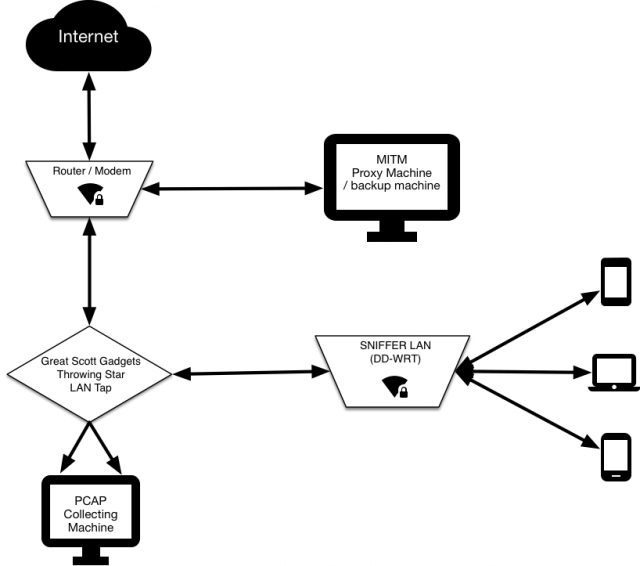
272Man-In-The-MiddleSNIFFlab – Create Your Own MITM Test Environment
Essentially it’s a WiFi hotspot that is continually collecting all the packets transmitted across it. All connected clients’ HTTPS communications are subjected...
-
 246Vulnerability Analysis
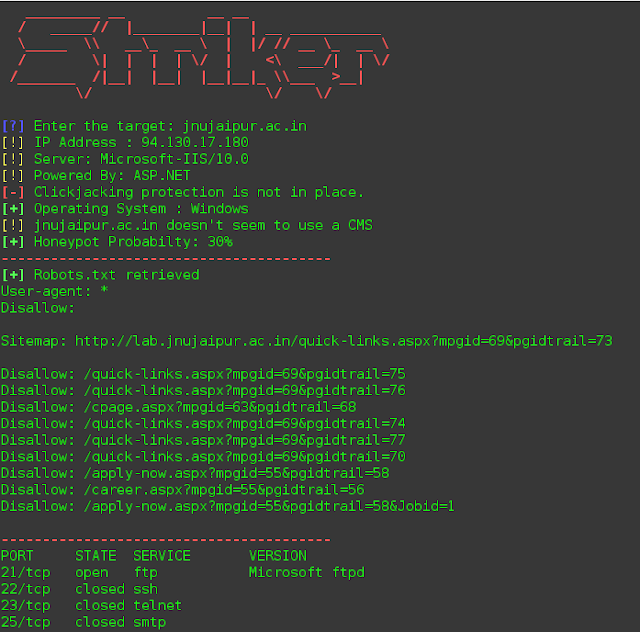
246Vulnerability AnalysisStriker – Offensive Information And Vulnerability Scanner
Striker is an offensive information and vulnerability scanner. Features Just supply a domain name to Striker and it will automatically do the...
-

 583Leaks
583LeaksThe New iOS 11.1 Wi-Fi hacked again
Just when the Apple released 11.1 as a patch to address the crack in WiFi and other exploits, here comes the news...
-

 194Articles
194ArticlesEthereum phishing attack that earns $15K in two hours
Wesley Neelen (security researcher) has received a phishing email that seems to be from the legal online Ethereum wallet site Myetherwallet.com. Cybercriminals...
-
 245Articles
245ArticlesDUHK (Don’t Use Hard-coded Keys) Attack Recovers Encryption Keys & Reveals VPN Connections
DUHK (Don’t Use Hard-coded Keys) is a new crypto implementation attack that could enable attackers to obtain secret keys that secure VPN...
-

 212Articles
212ArticlesCyber Attack Kept Secret from Public by Microsoft for Years
Not the first news of this nature but it was very recently discovered that Microsoft suffered a cyber attack from a group...
-
 229Security Tools
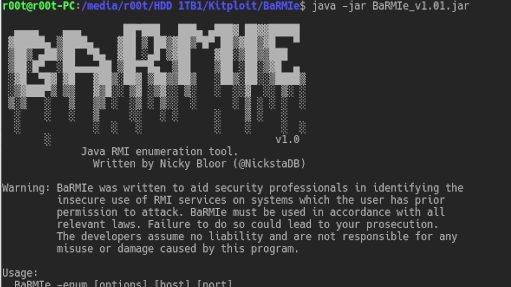
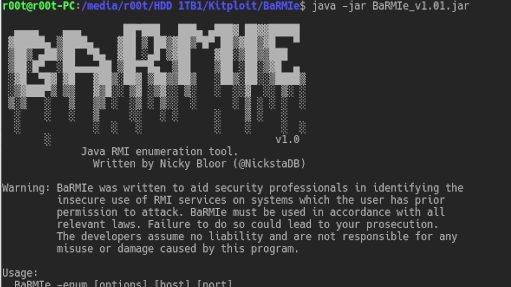
229Security ToolsBaRMIe – Java RMI Enumeration And Attack Tool
BaRMIe is a tool for enumerating and attacking Java RMI (Remote Method Invocation) services. RMI services often expose dangerous functionality without adequate...
-
 273Data Breach
273Data BreachNew Serious Flaw Called KRACK Attack Allow to Break WPA2 WiFi Protocol in Any WiFi Modem
Highly Secured WiFi Protocol “WPA2” Critical Weakness allows to Break any WiFi Network using Key Reinstallation Attack (KRACK Attack) and this flow is given...
-
 231System Administration
231System AdministrationBaRMIe – Java RMI Enumeration & Attack Tool
BaRMIe is a tool for enumerating and attacking Java RMI (Remote Method Invocation) services. RMI services often expose dangerous functionality without adequate...






