All posts tagged "Attack Surface"
-

 563Data Breach
563Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
To minimize the risk of privilege misuse, a trend in the privileged access management (PAM) solution market involves implementing just-in-time (JIT) privileged...
-

 4.1KData Breach
4.1KData BreachHow to Prioritize Cybersecurity Spending: A Risk-Based Strategy for the Highest ROI
As an IT leader, staying on top of the latest cybersecurity developments is essential to keeping your organization safe. But with threats...
-
 300Vulnerabilities
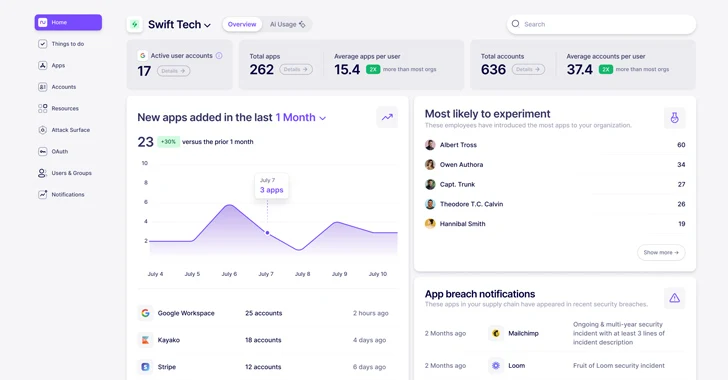
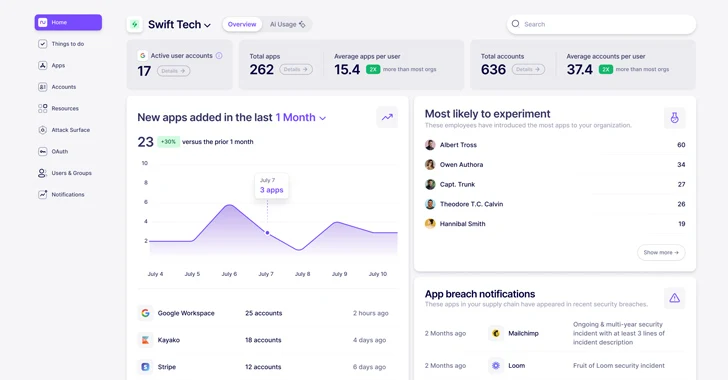
300VulnerabilitiesWhat is Nudge Security and How Does it Work?
In today’s highly distributed workplace, every employee has the ability to act as their own CIO, adopting new cloud and SaaS technologies...
-

 1.3KData Breach
1.3KData BreachGetting off the Attack Surface Hamster Wheel: Identity Can Help
IT professionals have developed a sophisticated understanding of the enterprise attack surface – what it is, how to quantify it and how...
-
 1.2KData Breach
1.2KData BreachMitigate the LastPass Attack Surface in Your Environment with this Free Tool
The latest breach announced by LastPass is a major cause for concern to security stakeholders. As often occurs, we are at a...
-

 2.7KData Breach
2.7KData BreachHow Attack Surface Management Preempts Cyberattacks
The wide-ranging adoption of cloud facilities and the subsequent mushrooming of organizations’ networks, combined with the recent migration to remote work, had...
-

 4.2KCyber Attack
4.2KCyber AttackHow Extended Security Posture Management Optimizes Your Security Stack
As a CISO, one of the most challenging questions to answer is “How well are we protected right now?” Between the acceleration...
-
 1.0KWeb Application Security
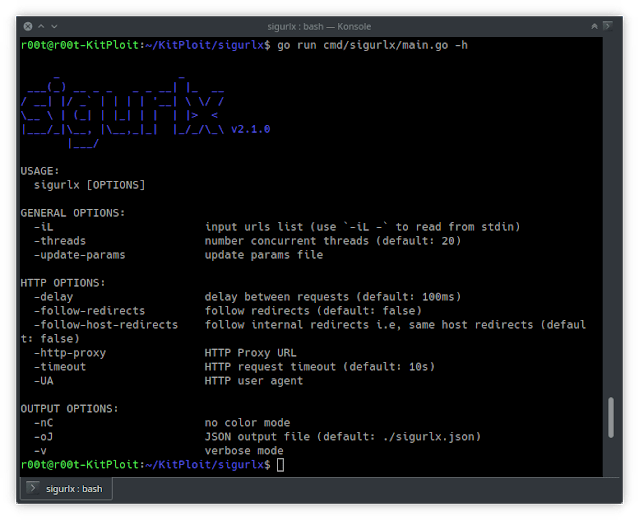
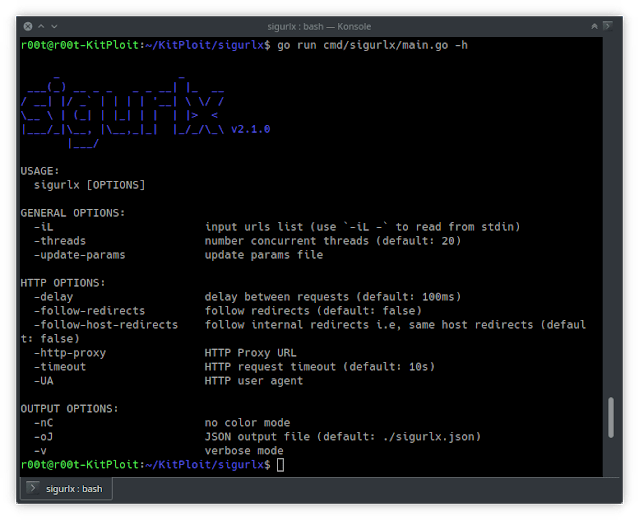
1.0KWeb Application SecuritySigurlx – A Web Application Attack Surface Mapping Tool
sigurlx a web application attack surface mapping tool, it does …: Categorize URLs URLs’ categories: > endpoint > js {js} >...






