All posts tagged "authentication"
-

 405News
405News‘EarEcho’ Lets You Unlock Your Smartphone ‘Using Your Ear’
The authentication process on smartphones has evolved over the years. What started as passwords, changed to fingerprint and facial recognition subsequently. Now...
-
 333News
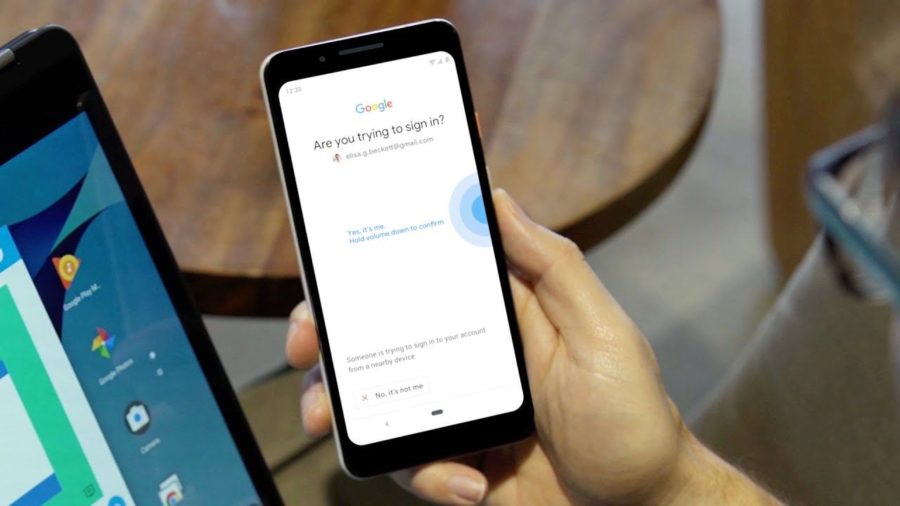
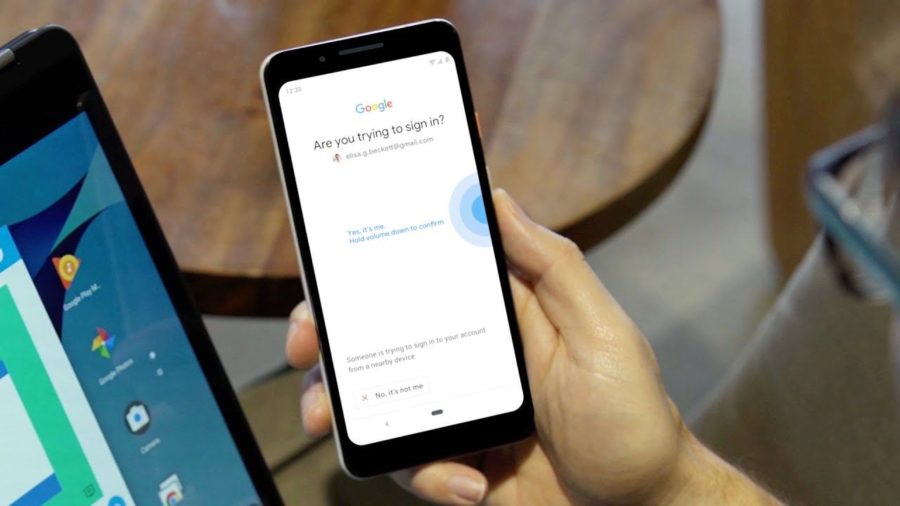
333NewsYour Android Phone Is Now A Physical Security Key — Here’s How To Use It
Two-factor authentication is one of the most reliable authentication methods. However, if anybody has access to the authentication codes received in messages, your...
-

 345Incidents
345IncidentsVulnerability in Fortnite authentication system affects user accounts
Security investigators were able to steal access tokens attacking an Epic Games subdomain According to network security and ethical hacking specialists from...
-
 258Malware
258MalwareUSB-IF Launches USB Type-C Authentication Program To Protect Against From Malicious Devices
USB-IF announced USB Type-C Authentication Program to confirm the authencity of the USB device USB device, USB cable or USB charger. The...
-
 392Shop
392ShopThetis FIDO U2F Security key – Universal Two Factor Authentication USB
FIDO U2F Security key is a personal encryption method which individualizes your online security by providing a secondary layer of encryption via...
-

 235Articles
235ArticlesIntel and Lenovo are trying to build UAF and U2F authentication into their devices
81 percent of data breaks last year involved weak, default or stolen passwords, and phishing attacks have advanced 65 percent year-on-year. Protecting...
-

 238Wireless Attacks
238Wireless AttacksNzyme – Wireless Monitoring, Intrusion Detection & Forensics
Nzyme collects 802.11 management frames directly from the air and sends them to a Graylog (Open Source log management) setup for WiFi IDS, monitoring,...
-

 177Geek
177GeekVulcanJS: Easiest Way To Build Full Stack Web Applications
Short Bytes: VulcanJS is a full stack toolkit based on React, Redux, Apollo GraphQL, and Meteor created by Sacha Greif. It allows a...
-

 296Hacked
296HackedFacebook Just Launched A New Open Source Tool For Recovering Passwords Easily
Short Bytes: If you regularly forget the passwords for your online accounts, then a Facebook tool, known as Delegated Recovery, might be...
-

 207Hacked
207HackedSecurity Is PAINful — The Four Cornerstones Of Security
Short Bytes: Digital security is always a hot topic, but its growth is accelerating. In order to implement security, you need to...






