All posts tagged "backdoor"
-

 106Incidents
106IncidentsCryptsy Bitcoin Trader Robbed, Blames Backdoor in the Code of a Wallet
The stolen Bitcoin & Litecoin were worth over $5.7 million. Cryptsy, a website for trading Bitcoin, Litecoin, and other smaller crypto-currencies, announced a...
-

 340News
340NewsHow Your Webcam Can Become Your Worst Nightmare
A group of security researchers turned a working webcam into a backdoor allowing attackers to remotely connect themselves with the device. The...
-

 231Data Security
231Data SecurityJuniper drops NSA-developed code following new backdoor revelations
Researchers contradict Juniper claim that Dual_EC_DRBG weakness couldn’t be exploited. Juniper Networks, which last month made the startling announcement its NetScreen line...
-

 106Data Security
106Data SecurityFireEye Security Devices Provide Attackers with Backdoor into Corporate Networks
FireEye security equipment can be compromised, Google finds. Two security researchers working for Google have discovered a simple method of compromising FireEye security...
-
 160Data Security
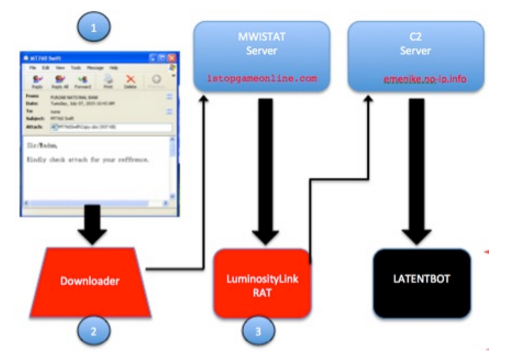
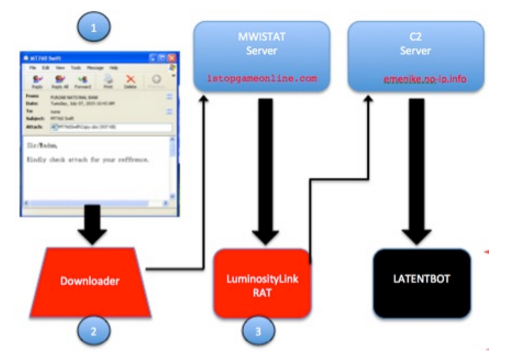
160Data SecurityLATENTBOT, one the highly obfuscated backdoor in the wild
Experts at FireEye have discovered a stealthy botnet relying on a backdoor called LATENTBOT has compromised companies around. Experts at FireEye have discovered...
-
 166Data Security
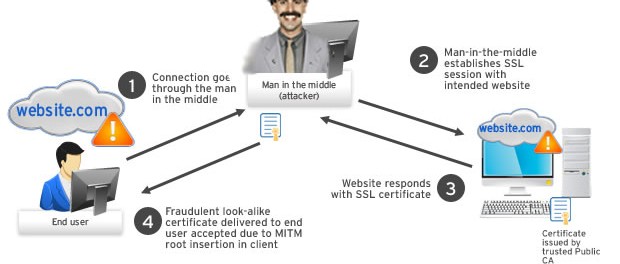
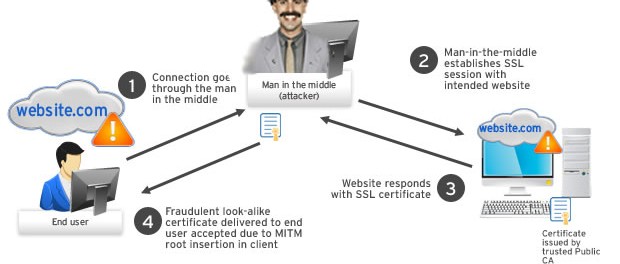
166Data SecurityKazakhstan will force its citizens to install internet backdoors
The poorly thought-out and crude surveillance technique could have a devastating effect on the country’s internet security. In less than a month,...
-

 240Data Security
240Data SecurityHack Remote Windows PC using The Backdoor factory with Metasploit
The goal of BDF is to patch executable binaries with user desired shellcode and continue normal execution of the prepatched state. First...
-
 220Data Security
220Data SecurityNo backdoor, no service: BlackBerry to exit Pakistan
Blackberry is all set to shut down its operations in Pakistan. The statement came from the company after continuing request from the...
-

 143Data Security
143Data Security600,000 cable modems have an easy to pop backdoor in a backdoor
Brazilian whacks Arris for easy-t-o-guess default password, fix promised fast. Security bod Bernardo Rodrigues has found a backdoor-within-a-backdoor affecting some 600,000 Arris...
-

 163Data Security
163Data SecurityBrazilian Army Gets Hacked Following Cyber-Games Cheating Accusations
Hackers leak data of over 7,000 officers. Hackers who declined to name themselves hacked the servers of the Brazilian Army, and later leaked...
-
 85Data Security
85Data SecurityTop FBI lawyer: You win, we’ve given up on encryption backdoors
We’re your servants, says general counsel unconvincingly After spending months pressuring tech companies to add backdoors into their encryption software, the FBI...
-

 332Data Security
332Data SecuritySDK Security Flaw Puts 100 Million Android Users Vulnerable to Backdoor Attack
A software development kit that has been provided by Baidu (A Chinese search engine) can easily be exploited for installing backdoors on...
-
 231Data Security
231Data SecurityReturn of the EXIF PHP Joomla Backdoor
Our Remediation and Research teams are in constant communication and collaboration. It’s how we stay ahead of the latest threats, but it...
-

 272Data Security
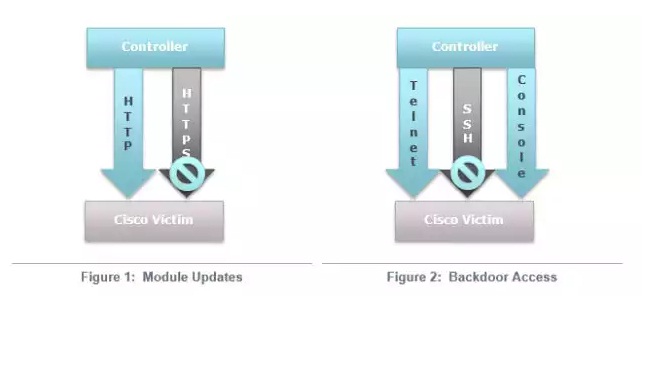
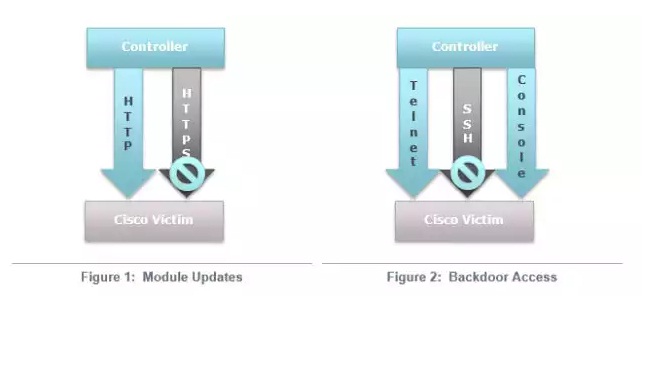
272Data SecurityHackers Can Steal Corporate Passwords Through Cisco’s WebVPN Service Backdoor
Researchers identified a flaw in Cisco’s WebVPN — Hackers managed to install backdoors via two methods on the service — This weakness...
-
 193Malware
193MalwareAbusing Windows Management Instrumentation (WMI) to Build a persistent, Asynchronous and Fileless Backdoor
Matt Graeber showed the method on performing WMI attacks and its effects, but he didn’t talk much about the details. Therefore, this...
-
 113Incidents
113IncidentsBackdoor infecting Cisco VPNs steals customers’ network passwords
Dozens of successful attacks detected that install malicious code on company portals. Attackers are infecting a widely used virtual private network product...
-

 124Malware
124MalwareNew PoS Trojan Can Download Other Malware, Launch DDOS Attacks
The world of computer viruses and antivirus solutions is in a constant change, with cyber-crooks evolving their code and cyber-security firms trying...
-
 116Vulnerabilities
116VulnerabilitiesCisco routers in at least 4 countries infected by highly stealthy backdoor
More than a dozen routers in four countries infected with fully featured implants. Researchers have uncovered active and highly clandestine attacks that...
-

 292Geek
292GeekNATO Will Check for Backdoors in Microsoft’s Products
Microsoft has taken NATO onboard in its program which presents information about vulnerabilities and provides access to source code. A Security Agreement...
-

 304Data Security
304Data SecurityCisco Routers Vulnerable To Malware Attacks Via Backdoor Firmware Installation
It has always been believed that Cisco routers being used in the enterprise environment could be hacked via installation of backdoor firmware,...
-
 120Data Security
120Data SecuritySurvey Shows Most Americans are Fine with Backdoor in Their Devices
A recent survey from Vormetric revealed that people in the United States are OK with the addition of backdoors in their devices/software....






