All posts tagged "backdoor"
-

 5.1KCyber Events
5.1KCyber EventsMicrosoft, FireEye report 3 new malware linked to SolarWinds hackers
Microsoft and cybersecurity firm FireEye has identified three new malware used by SolarWinds hackers in their last year’s attack on highly critical...
-

 923Data Security
923Data SecurityKaspersky spots CIA malware with backdoor capabilities
Dubbed Purple Lambert by Kaspersky; the malware passively listens to network traffic and search for a “magic packet.” The Global Research and...
-
 1.5KSystem Administration
1.5KSystem AdministrationCDK – Zero Dependency Container Penetration Toolkit
CDK is an open-sourced container penetration toolkit, designed for offering stable exploitation in different slimmed containers without any OS dependency. It...
-
 3.2KExploitation Tools
3.2KExploitation ToolsDrow – Injects Code Into ELF Executables Post-Build
drow is a command-line utility that is used to inject code and hook the entrypoint of ELF executables (post-build). It takes...
-
 4.2KData Security
4.2KData SecurityMeet ACbackdoor malware targeting Linux and Windows devices
Recently, a malware by the name of ACbackdoor has been discovered which infects both Windows and Linux based systems. With little to...
-
 4.5KMalware
4.5KMalwareMulti-Platform Malware “ACBackdoor” Attack Both Windows & Linux Users PC by Executing Arbitrary Code
Researchers discovered a previously undetected multi-platform malware called ACbackdoor that has both Linux and Windows Variant to infect the respective users and...
-

 1.0KMalware
1.0KMalwareNew Hacking Group Using Metasploit To Install Backdoor Malware On Windows By Exploiting MS Office
Researchers detect a wave of malware campaigns from a new hacking group named TA2101 that targeting various organizations in German and Italy...
-
 2.0KMalware
2.0KMalwareA new and dangerous backdoor available on deep web
According to reports from digital forensics experts, the dangerous hacker group known as Platinum has announced the release of Titanium, a new...
-
 848Malware
848MalwareTitanium APT Hackers Inject New Hidden Backdoor on Windows Using Fileless Technique
A new wave of malware attack strikes again from the Titanium APT group that infects windows with hidden backdoor by mimicking common...
-

 3.7KNews
3.7KNewsBeware! World’s Most Notorious Hacking Group Launches New Trojan
Platinum, the infamous Advanced Persistent Threat (APT) group, has launched a new backdoor trojan named Titanium that has advanced capabilities of taking...
-
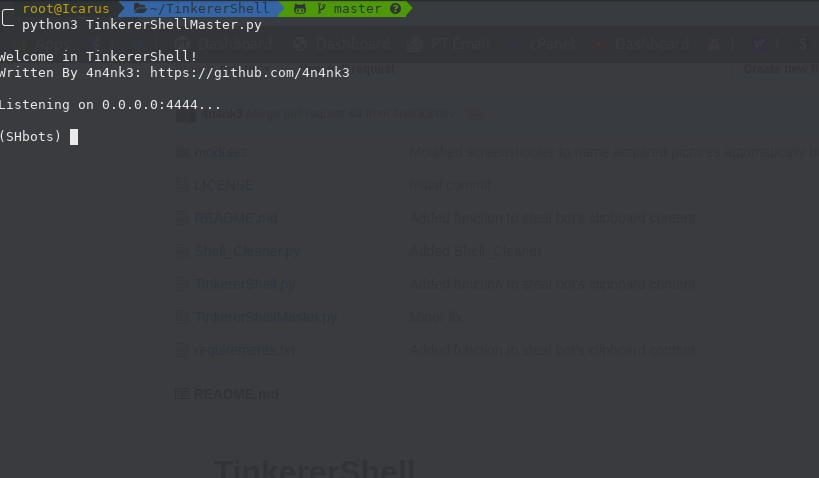
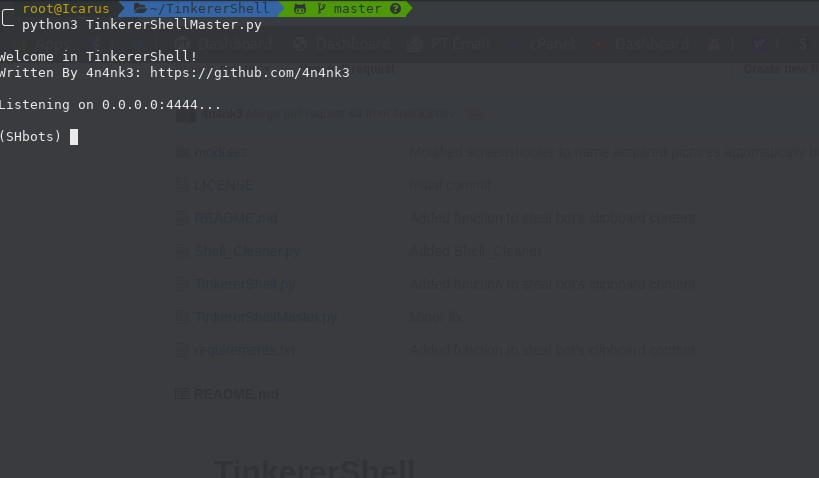 4.0KExploitation Tools
4.0KExploitation ToolsTinkererShell – A Simple Python Reverse Shell Written Just For Fun
A simple reverse shell written in python 3.7 just for fun. Actually it supports Windows and Linux OS and integrates some...
-

 1.2KMalware
1.2KMalwareThese free WordPress themes and plugins might contain malware. Avoid their installation
WordPress is probably the most popular content management system (CMS) today, so it’s no wonder it’s also the subject of multiple cybersecurity...
-
 680Malware
680MalwareRussian Turla APT Group Hacked Iranian APT C2 Server For Backdoor Access To Expand The Cyber Attack
Hackers-Hack-Hackers: Russian APT group Turla known as Waterbug compromised the Iranian hacker’s command and control server infrastructure, and the Exfiltrated of data...
-

 537Malware
537MalwareChinese hackers could install backdoors on Microsoft SQL 11 and 12 servers using a “magic word”
The activities of government-sponsored hacker groups can have disastrous consequences. A group of digital forensics experts from ESET has revealed the existence...
-

 466Incidents
466IncidentsAvast internal networks were hacked. Did attackers install backdoors in CCleaner? Is it secure to use this tool?
Even security companies are exposed to cyberattacks. IT system audit specialists report that security software developer Avast has become victim of an...
-
 575Malware
575MalwareFree music files on the Internet could contain malware and backdoors
Digital forensics specialists report a new attack method consisting of the use of WAV audio files to hide and deliver backdoors and...
-
 357Data Security
357Data SecurityMasterMana botnet hits users by evading detection with URL shorteners
MasterMana botnet is part of an ongoing malware campaign. The IT security researchers at Prevailion have discovered an active botnet that has...
-

 361News
361NewsUS And UK Ask Facebook To Create A “Backdoor” To Access Encrypted Texts
The US, UK, and Australia are putting pressure on Facebook to create a backdoor in its encrypted messaging apps that would allow...
-

 431Vulnerabilities
431VulnerabilitiesHackers are exploiting a backdoor on Fortinet SSL VPN; update now
Ethical hacking experts report that, in recent days, threat actors have been scanning the Internet looking for non updated SSL VPNs developed...
-
 257Malware
257MalwareStop programming in Ruby, applications using Ruby libraries have a backdoor
The RubyGems package repository maintenance team recently announced the removal of at least 18 malicious versions of 11 Ruby libraries due to...
-
 439Malware
439MalwareNewly Discovered Hacking Tools Remotely control the Hacked Computers via a GUI & Command-Line Interface
Researchers discovered two new malicious hacking tools (BalkanRAT, BalkanDoor) from the ongoing campaign Balkans that act as a remote access trojan and...






