All posts tagged "backdoor"
-

 266Cyber Crime
266Cyber CrimeDisguised as Citrix Utility, Kedi RAT Exploits Gmail to Transfer Data
A Remote Access Trojan (RAT) is one of the most used malicious software used by cybercriminals to target unsuspecting users. Based on its...
-

 177Malware
177MalwareBackdoor Found in WordPress Plugin With More Than 200,000 Installations
For the past two and a half months, a WordPress plugin named Display Widgets has been used to install a backdoor on...
-
 277News
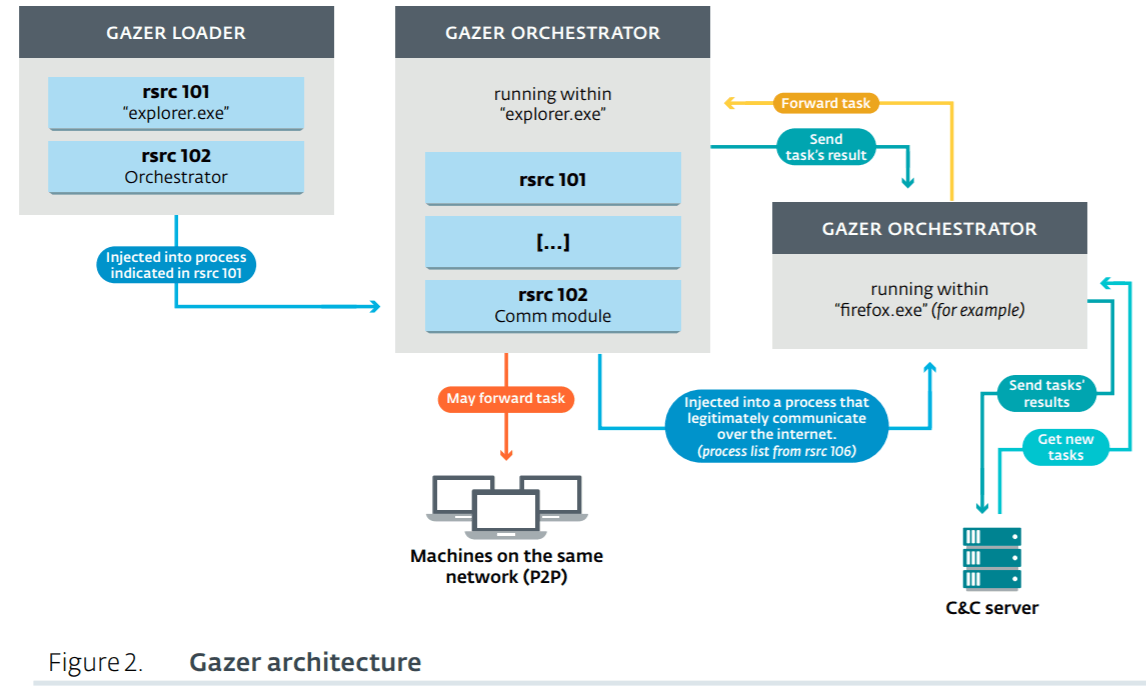
277NewsA New Gazer Backdoor Is Targeting Ministries and Embassies Around The World
ESET security researchers have discovered a new gazer backdoor campaign targeted at consulates, ministries, and embassies around the world to spy on...
-

 166Malware
166MalwareThree Hardcoded Backdoor Accounts Discovered in Arris Modems
Security researchers have found five gaping holes in the firmware running on Arris modems, three of which are hardcoded backdoor accounts. An...
-
 169Malware
169MalwareNew ESET research uncovers Gazer, the stealthy backdoor that spies on embassies
Security researchers at ESET have released new research today into the activities of the notorious Turla cyberespionage group, and specifically a previously undocumented backdoor...
-
 326Geek
326GeekHidden Kill Switch Identified in Controversial Intel ME controller chip
Europe’s leading cyber-security firm Positive Technologies’ security researchers have a bad news for Intel users. They have detected a secret configuration setting...
-

 107Data Security
107Data SecurityBeware; dangerous new malware ‘Joao’ hits gamers worldwide
Gaming is an addiction but for cyber criminals, it is a lucrative business. IT security researchers at ESET have discovered a new malware...
-

 123Malware
123MalwareMACOS FRUITFLY BACKDOOR ANALYSIS RENDERS NEW SPYING CAPABILITIES
LAS VEGAS—The FruitFly backdoor became a known entity in January, but it’s a good bet that for years it had been in...
-
 276Incidents
276IncidentsStantinko Modular Backdoor Infected Over 500,000 Computers
Over 500,000 users have had their computers infected with a stealthy malware named Stantinko, according to a 99-page report released yesterday by Slovak...
-
 107Vulnerabilities
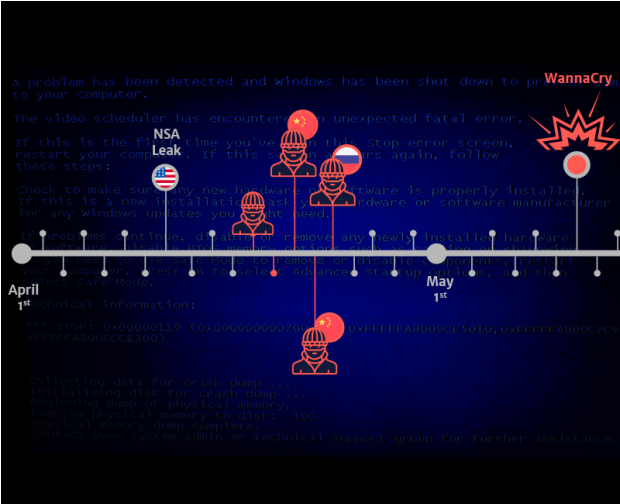
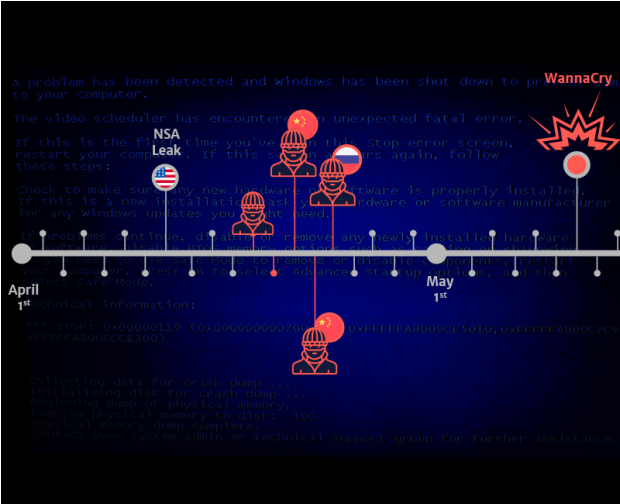
107VulnerabilitiesMultiple Groups Have Been Exploiting ETERNALBLUE Weeks Before WannaCry
We have found evidence of much more sophisticated actors leveraging the NSA ETERNALBLUE exploit to infect, install backdoors and exfiltrate user credentials...
-

 168Vulnerabilities
168VulnerabilitiesHIKVISION PATCHES BACKDOOR IN IP CAMERAS
Hikvision, a Chinese manufacturer of video surveillance equipment, recently patched a backdoor in a slew of its cameras that could have made...
-

 131Malware
131MalwareLeaked: The UK’s secret blueprint with telcos for mass spying on internet, phones – and backdoors
Real-time full-blown snooping with breakable encryption. The UK government has secretly drawn up more details of its new bulk surveillance powers –...
-

 256Geek
256GeekMilkydoor: A malware which can turn an Android phone into hacking device
Hackers have developed a highly sophisticated malware named “Milkydoor” which can turn any infected Android phone into a hacking tool. Trend Micro, a security...
-
 325Malware
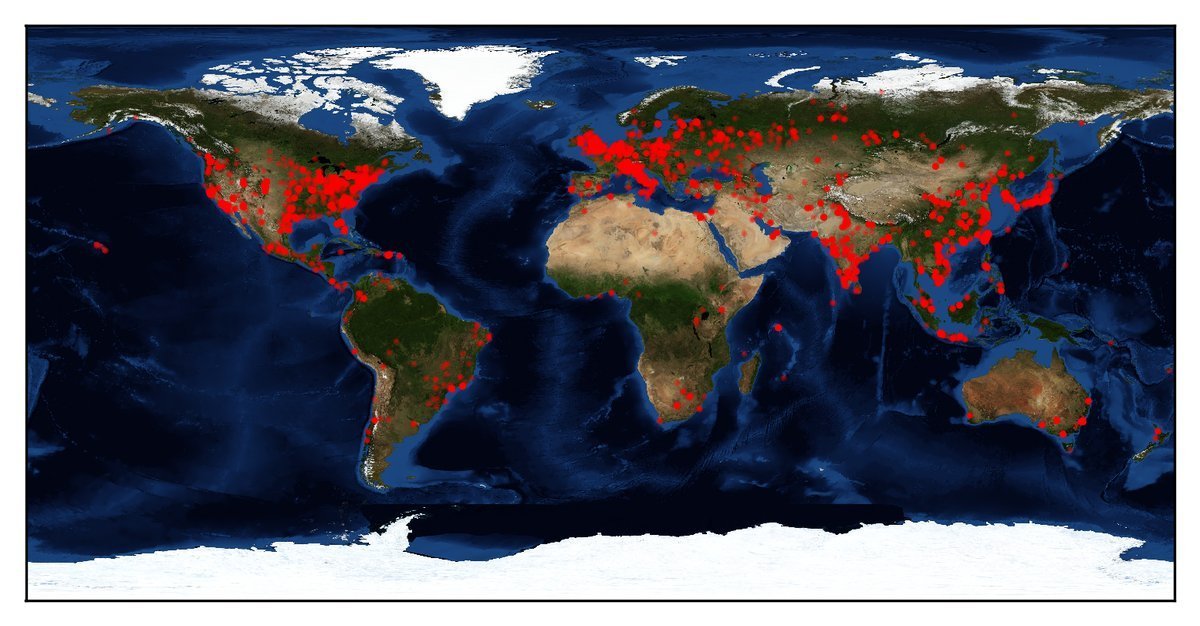
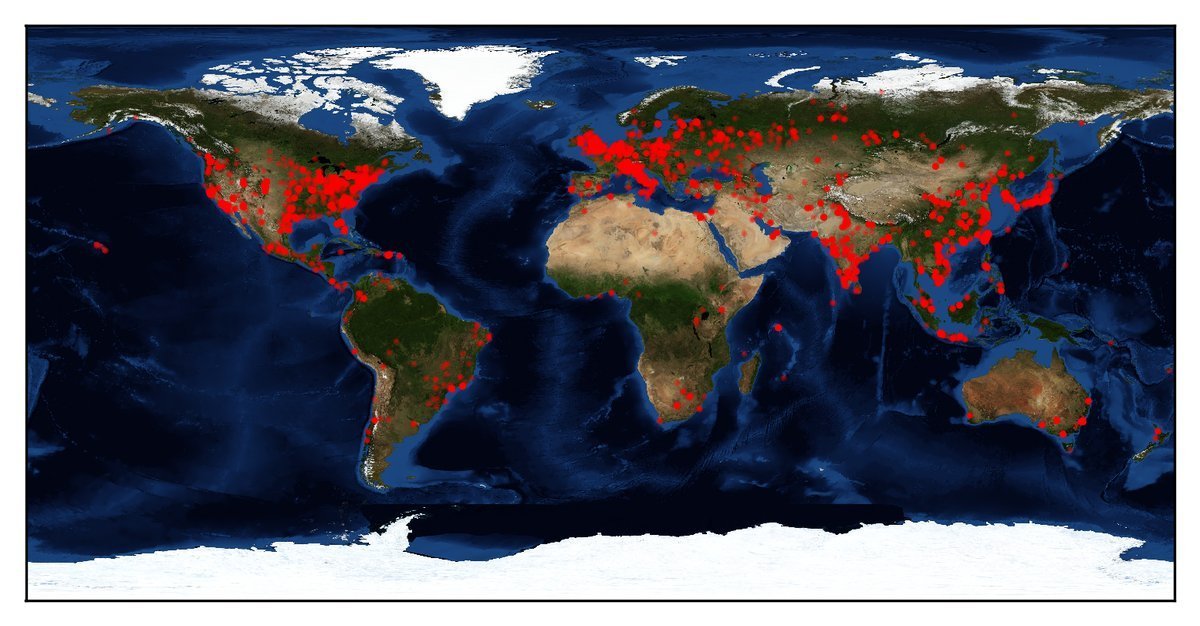
325MalwareMass Scan Revealed More Than 30000 Windows Computers Infected by NSA backdoor DoublePulsar
[jpshare] A Recent Mass Scan Revealed That More than 30000 Windows Machine Infected by National Security Agency Backdoor DOUBLEPULSAR .DOUBLEPULSAR one of the NSA...
-

 319Mobile Security
319Mobile SecurityMobile spyware that steal Twitter credentials uses sandbox to Evade antivirus detections
[jpshare]Security Experts from Avast came through a Malware that uses a sandbox(DroidPlugin) to dynamically load and run an app, without actually installing...
-
 89Malware
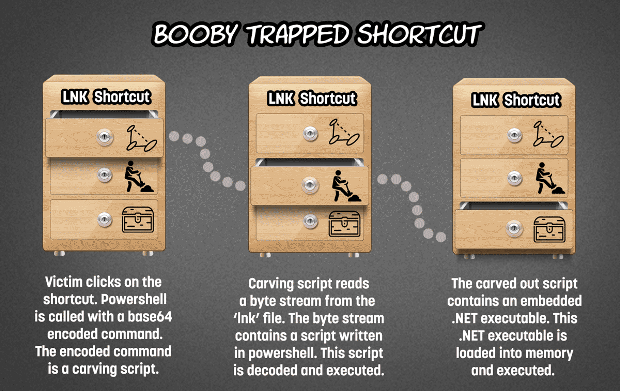
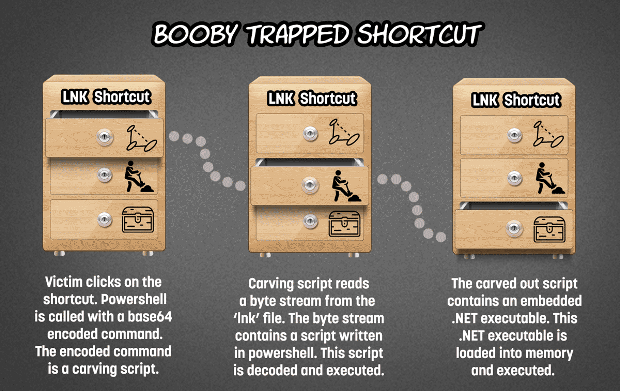
89MalwareBooby trap a shortcut with a backdoor
Embedding a shortcut (.lnk file) which points to powershell (accompanied by an encoded command) in a word document or zip file is...
-

 115Vulnerabilities
115VulnerabilitiesRaging Sysadmin Shuts Down Company Servers, Deletes System Files
A former sysadmin is facing up to ten years in prison and a fine of up to $250,000 after he used a ...
-

 151Vulnerabilities
151VulnerabilitiesBritish Authorities Slam WhatsApp for Encryption Used by London Terrorist
The Brits join US intelligence agencies who’d want a backdoor into the encryption feature on all services. End-to-end encryption services like WhatsApp...
-
 200Malware
200MalwareChinese PUPs distributing Backdoored Drivers which affect Windows operating system
PUP(potentially unwanted program) packages that install’s along with Chinese software’s consist of backdoors targeting English speakers. The backdoor was uncovered by Malware...
-

 119Incidents
119IncidentsBitErrant attack
The BitErrant attack is a fun little exploit that shows what can go wrong in the BitTorrent protocol when SHA1 collisions become...
-
 98Malware
98MalwareHidden backdoor discovered in Chinese IoT devices
Researchers at Trustwave have uncovered a backdoor in IoT devices from a Chinese manufacturer that could leave them open to exploitation. The...






