All posts tagged "backdoors"
-

 339Malware
339MalwareFive Eyes Group demands access to crime suspects data through encryption backdoors
The group threatens to take legal action Five Eyes alliance member countries have threatened to implement legislation if technology providers do not cooperate...
-
Articles
Government Source Code Reviews will not be permitted by McAfee Anymore
News reported in June that McAfee was amongst several Western technology organizations that had acceded in recent years to larger demands by...
-
 363Video Tutorials
363Video TutorialsZeroDoor – A Script Written Lazily For Generating Cross-Platform Backdoors – Kali Linux 2017.2
Hey Guys, In this video i show you a cool script called ZeroDoor which used for Generating Cross-Platform Backdoors. ZeroDoor:https://github.com/Souhardya/Zerodoor A script...
-
Exploitation Tools
ZeroDoor – A Script Written Lazily For Generating Cross-Platform Backdoors
A script written lazily for generating reverse shell backdoors on the go whenever you need without any hassle for your daily penetration...
-
Exploitation Tools
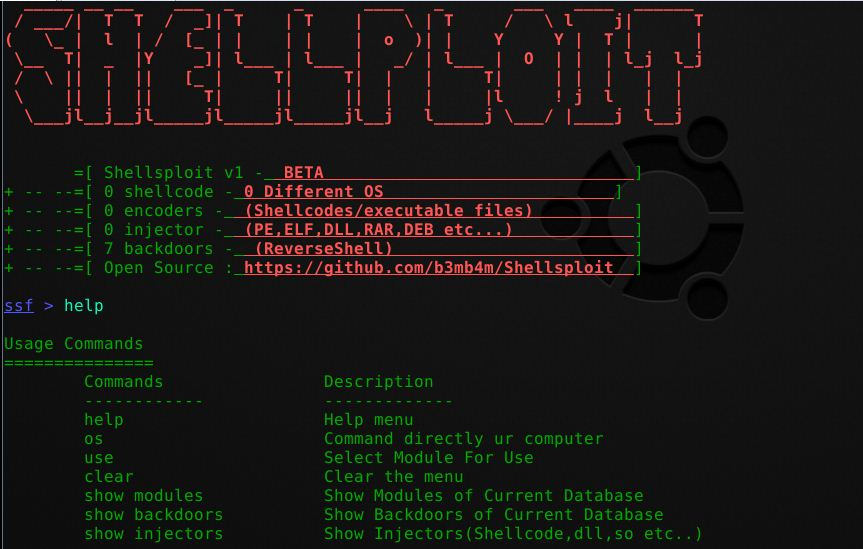
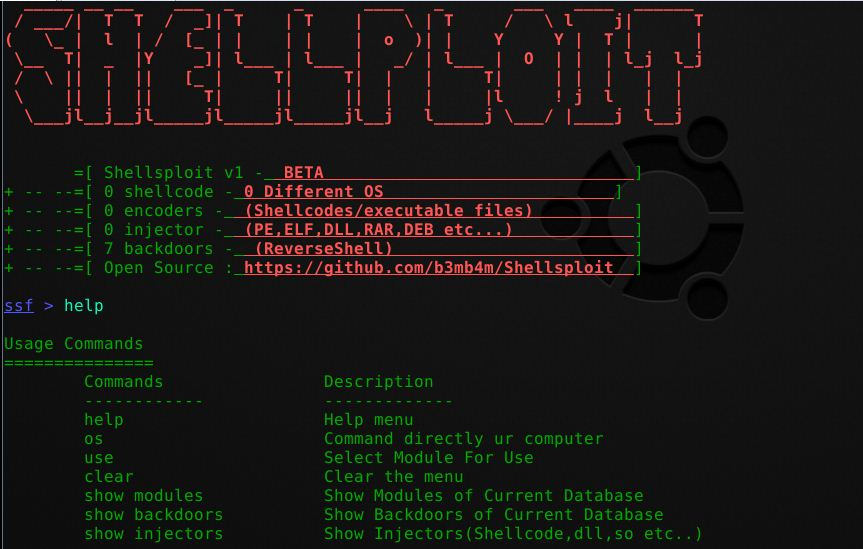
Generate Shellcodes & Backdoors using ShellSploit Framework and Kali Linux 2017.2
Hey Guys, In this video i show you how to generate shellcodes and Backdoors using ShellSploit Framework and Kali Linux 2017.2. ShellSploit:...
-

 224Vulnerabilities
224VulnerabilitiesSambaCry Vulnerability Used to Deploy Backdoors on NAS Devices
Someone is using the SambaCry vulnerability to install a backdoor trojan on Linux devices running older versions of the Samba file-sharing server....
-

 190Malware
190MalwareOpen Ports Create Backdoors in Millions of Smartphones
Mobile applications that open ports on Android smartphones are opening those phones to remote hacking, claims a team of researchers from the...
-

 205Malware
205MalwareExpect renewed push for encryption backdoors from Trump administration
Top law enforcement officers, FBI director James Comey and Trump’s nominee for attorney general, Sen. Jeff Sessions, are supportive of giving law...
-
 292Malware
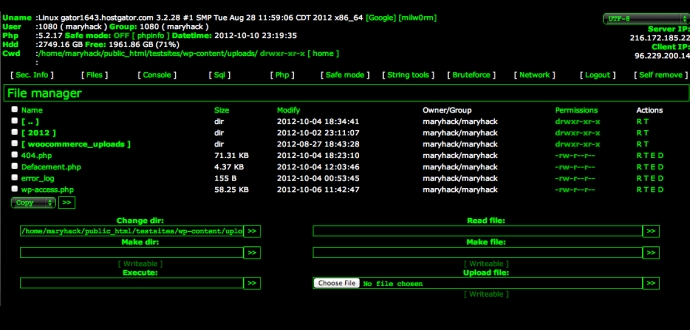
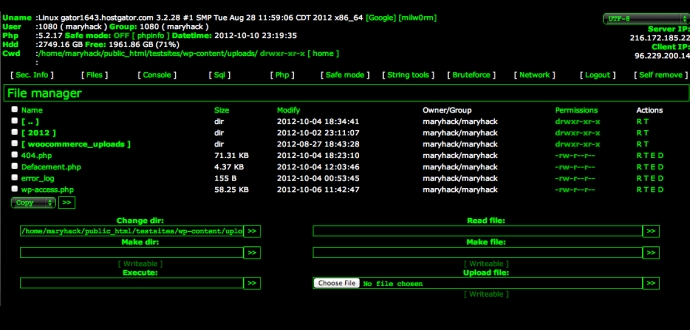
292MalwareDutch coder built backdoors into thousands of websites
Dutch developer used built-in backdoors in websites to steal personal information of customers. A 35-year-old unnamed web developer from Leeuwarden, Netherlands has...
-
 212Data Security
212Data SecurityFakeFile Trojan Opens Backdoors on Linux Computers, Except openSUSE
Trojan targets desktops, not servers or IoT devices. Malware authors are taking aim at Linux computers, more precisely desktops and not servers, with...
-

 210Malware
210MalwareA Malicious ‘Pokémon GO’ App Is Installing Backdoors on Android Devices
Nintendo’s new location-based augmented reality game ‘Pokémon GO’ is hot right now. Like really, really popular—so much so that players are spoofing...
-
 284Vulnerabilities
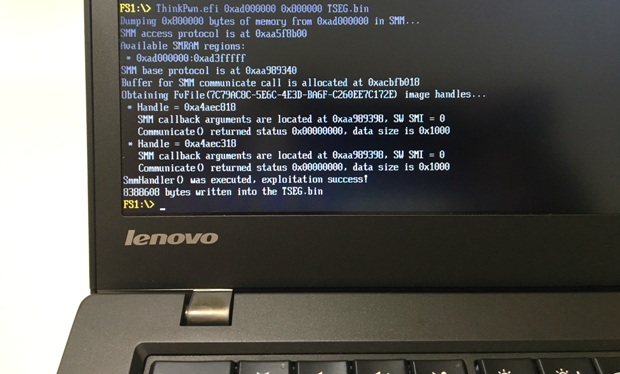
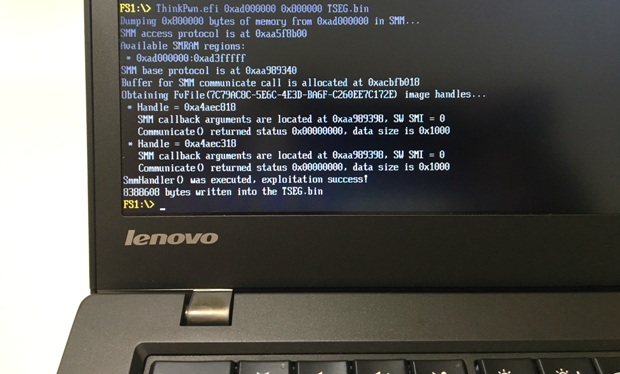
284VulnerabilitiesExploring and exploiting Lenovo firmware secrets
Hi, everyone! In this article I will continue to publish my research of Lenovo ThinkPad’s firmware. Previously I shownhow to discover and...
-
 207Hack Tools
207Hack ToolsShellsploit – New Generation Exploit Development Kit
Shellsploit let’s you generate customized shellcodes, backdoors, injectors for various operating system and let’s you obfuscate every byte via encoders. Install/Uninstall If...
-
 211Data Security
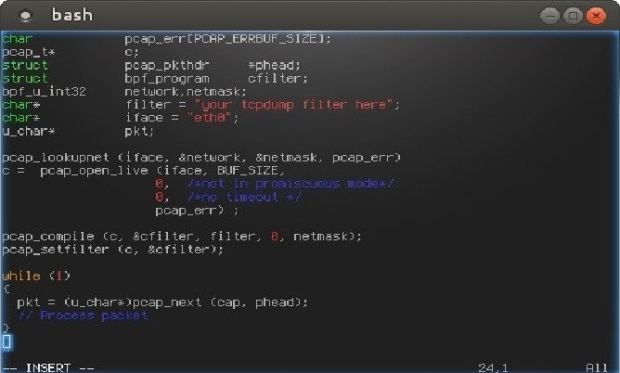
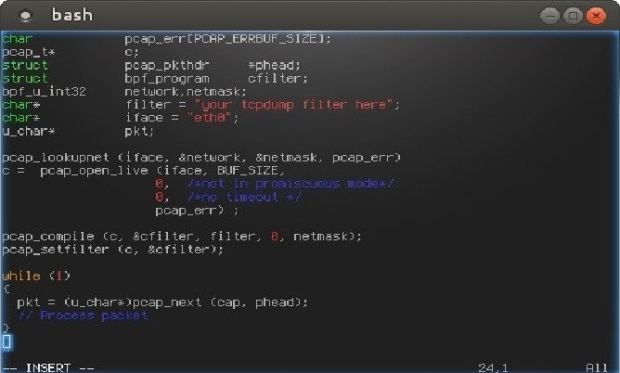
211Data SecurityHow to Build Stealth Backdoors
Today I’m going to tell you about a couple of techniques used to build stealth backdoors. Then, I will also show you...
-

 228Data Security
228Data SecurityFrom Linux to Windows – New Family of Cross-Platform Desktop Backdoors Discovered
Recently we came across a new family of cross-platform backdoors for desktop environments. First we got the Linux variant, and with information...
-

 187Data Security
187Data SecurityBritish Government Has Already Created a Data Encryption Protocol Complete With a Backdoor
GCHQ insists on shooting itself in the foot with backdoored VoIP encryption protocol, developed in-house by CESG. Britain’s intelligence agency, GCHQ (Government...
-

 200Data Security
200Data SecurityNew York tries to force phone makers to put in crypto backdoors
The sport of holding Apple, Google and other tech companies over a barrel to demand backdoors now has a new player: New...
-

 185Data Security
185Data SecurityWhat the government should’ve learned about backdoors from the Clipper Chip
The Obama administration’s calls for backdoors echo the Clinton-era key escrow fiasco. In the face of a Federal Bureau of Investigation proposal...
-

 204Data Security
204Data SecurityAPT Group Upgrades Malware from the Black Market into Dangerous Backdoor
Cyber-espionage group targeted companies in Asia. Details about the operations of a new cyber-espionage group are emerging, and this gang has been buying...
-

 202Malware
202MalwareRelentless Sofacy APT Attacks Armed With Zero Days, New Backdoors
A new analysis of the Sofacy APT gang, a Russian-speaking group carrying out targeted attacks against military and government offices for close...
-
 197Data Security
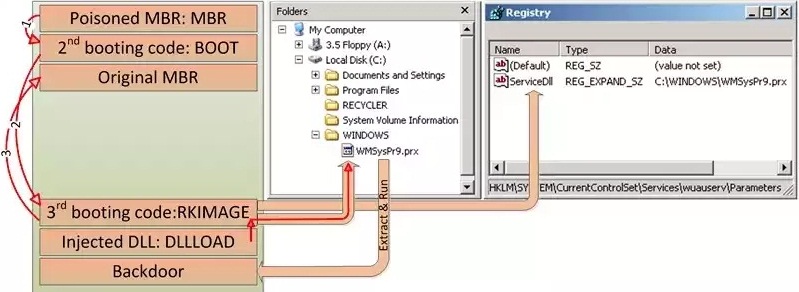
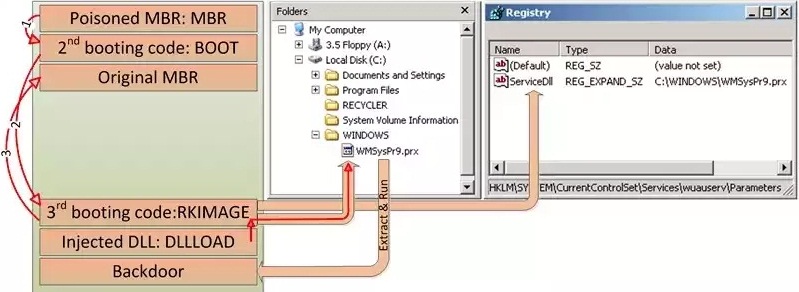
197Data SecurityHDRoot Bootkit Impersonates Microsoft’s Net Command
HDRoot is the work of the Winnti APT group. Hackers activating mainly in South-East Asia have developed a new bootkit trojan, which disguises...






