All posts tagged "black hat"
-

 300News
300NewsFree Facial Recognition Tool to Track People on Social Media Sites
A new facial recognition tool is developed by the researchers at Trustwave, an information security company. This is an open-source facial recognition...
-
 358Video Tutorials
358Video TutorialsHow to Generate a PHP Backdoor using Weevely – Kali Linux
Weevely is a web shell designed for post-exploitation purposes that can be extended over the network at runtime. Upload weevely PHP agent...
-
 289Vulnerabilities
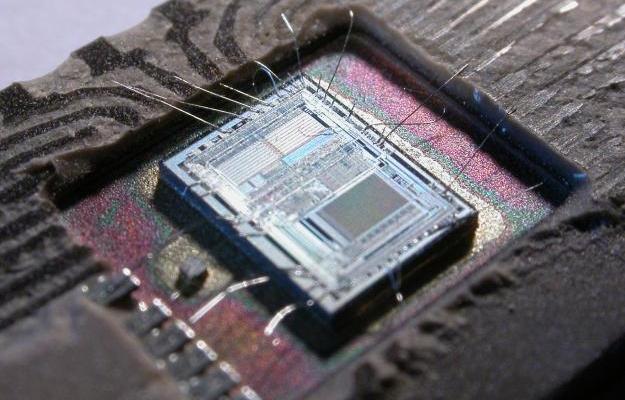
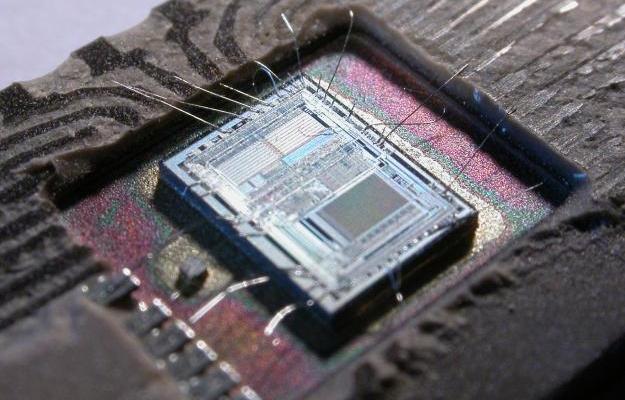
289VulnerabilitiesExperts can hack most CPUs since 2008 over USB by triggering Intel Management Engine flaw
Intel’s management engine – in most Positive Technologies plans to demonstrate at the next Black Hat conference how to hack over USB...
-

 193Hacked
193Hacked5 Best Hacks From The Black Hat 2016
Short Bytes: At the Black Hat 2016 hacker conference in Las Vegas, the world saw a variety of cutting-edge cyber security applications....
-

 180Incidents
180IncidentsHacked Websites Used in Black Hat SEO Campaign Redirecting Users to Adult Sites
Infected websites are hard to detect, only show up for users coming off search engines and for search bots. A new black hat...
-

 177Malware
177MalwareMalware Is Using the Dark Web to Stay Hidden
The dark web is well known as a space where anything can be bought or sold: guns, drugs, stolen data, and extreme...
-

 306Hacked
306HackedExplained: How Criminals Hack Your Chip And Pin Card
Short Bytes: EMV credit cards have till now been assumed to be unhackable. The security professor from the University of California explains how...
-

 268Data Security
268Data SecurityResearchers Show How To Hack Corvette with A Text Message
A video demonstration by the University of California researchers how a simple text message can control your car. The months of July and August have...
-

 308Data Security
308Data Security7 Unexpected Hacks of 2015, Thanks To DefCon and Black Hat
This year, at DefCon 23 and Black Hat USA 2015 security conferences, hackers are going to discuss how vulnerable and severely flawed...
-
 223Data Security
223Data SecurityShield Your PC from Radiofrequency, Hackers Can Steal Data Using Radio/Sound Waves
A recent experiment by a researcher would force you to reconsider the safety of your important data and make you put a...
-

 310Data Security
310Data SecurityHacker Shows How to Locate, Unlock, Start GM Cars with a Hacked Mobile App
As the dates for the Black Hat and Def Con Hacking Conference are approaching closer and closer, we are hearing more and...
-

 306Data Security
306Data SecurityJeep Cherokee On-Board System Hacked, More Than 470,000 Vehicles at Risk
We have heard about hacking websites, computers, planes, and other devices, but hacking a moving car? Well, it happened and it happened live....






