All posts tagged "Bumblebee"
-
 2.3KMalware
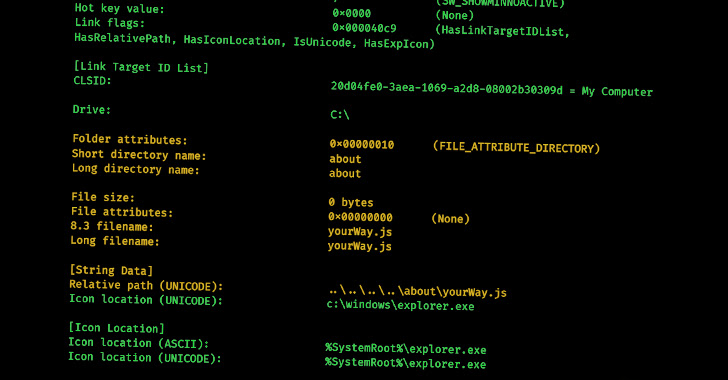
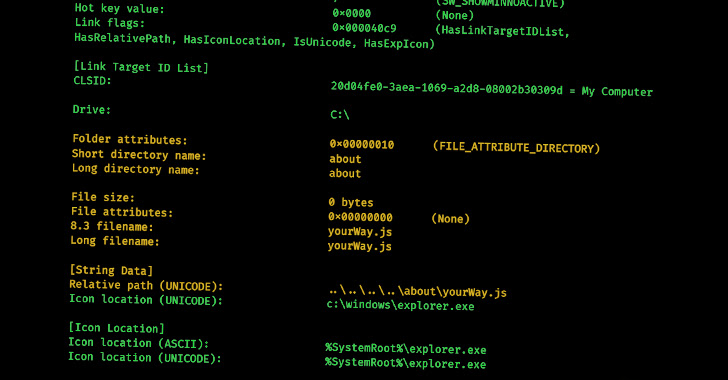
2.3KMalwareNew Research Delves into the World of Malicious LNK Files and Hackers Behind Them
Cybercriminals are increasingly leveraging malicious LNK files as an initial access method to download and execute payloads such as Bumblebee, IcedID, and...
-

 4.6KMalware
4.6KMalwareNew Analysis Reveals Raspberry Robin Can be Repurposed by Other Threat Actors
A new analysis of Raspberry Robin’s attack infrastructure has revealed that it’s possible for other threat actors to repurpose the infections for...
-
 4.8KMalware
4.8KMalwareRaspberry Robin Operators Selling Cybercriminals Access to Thousands of Endpoints
The Raspberry Robin worm is becoming an access-as-a-service malware for deploying other payloads, including IcedID, Bumblebee, TrueBot (aka Silence), and Clop ransomware....






