All posts tagged "bypass"
-
 5.0KExploitation Tools
5.0KExploitation ToolsByp4Xx – Bypass 403 Forbidden Messages With Well-Known Methods
byp4xx.sh __ __ __ / /_ __ ______ / // / _ ___ __ / __ / / / / __...
-

 380Mobile Security
380Mobile SecuritySHAREit App Vulnerabilities Allows Hackers to Bypass Android Device Authentication & Download Arbitrary Files Remotely
Researchers recently discovered 2 new critical vulnerabilities in the SHAREit App lets attackers bypass the Android device authentication mechanism and download the...
-

 224News
224NewsWhatsApp iOS Bug Allows Anyone To Bypass Touch ID/Face ID
WhatsApp recently introduced the ability for iOS users to access the app via Touch ID or Face ID for added security. Now,...
-
 251Information Gathering
251Information GatheringCloudBunny – A Tool To Capture The Real IP Of The Server That Uses A WAF As A Proxy Or Protection
CloudBunny is a tool to capture the real IP of the server that uses a WAF as a proxy or protection. How...
-

 245Articles
245ArticlesWhat is the Lightning Network? A Beginner’s Guide
Author: Colin Harper If you’ve ever dealt in Bitcoin, you may have suffered through hour-long (or at worst, day-long) transaction times. It’s...
-

 267Articles
267ArticlesWhat is Litecoin? | A Beginner’s Guide
Author: Alex Moskov What is Litecoin? Litecoin (LTC) is a decentralized peer-to-peer cryptocurrency that was released on October 7th, 2011 and went...
-

 311Information Gathering
311Information GatheringHow to Bypass Cloudflare with HatCloud – Kali Linux 2018.1
HatCloud is built in Ruby. It tries to bypass CloudFlare and discover real IP. This can be useful if you need to...
-
 198Information Gathering
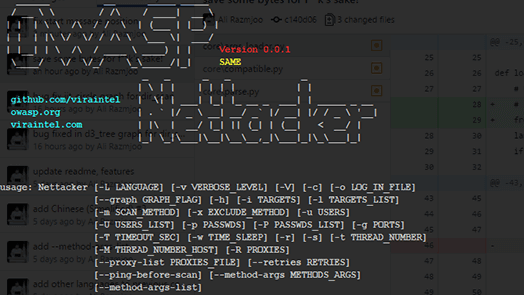
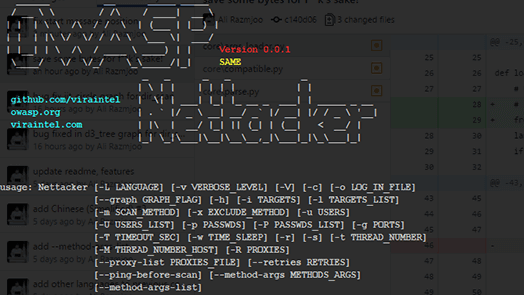
198Information GatheringOWASP-Nettacker – Automated Penetration Testing Framework
OWASP Nettacker project is created to automate information gathering, vulnerability scanning and eventually generating a report for networks, including services, bugs, vulnerabilities,...
-

 367Vulnerability Analysis
367Vulnerability AnalysisWhatWaf – Detect And Bypass Web Application Firewalls And Protection Systems
WhatWaf is an advanced firewall detection tool who’s goal is to give you the idea of “There’s a WAF?”. WhatWaf works by...
-

 313Exploitation Tools
313Exploitation ToolsDr0p1t-Framework 1.3.2.1 – A Framework That Creates An Advanced FUD Dropper With Some Tricks
Have you ever heard about trojan droppers ? In short dropper is type of malware that downloads other malwares and Dr0p1t gives...
-

 194Vulnerabilities
194VulnerabilitiesAnti Virus Software’s Design Flaw Leads to Bypass Windows Local Privilege
A new Antivirus design flaw has discovered and named as AVGater for the Windows Local Privilege Escalation Vulnerability which is presented in...
-
 171Exploitation Tools
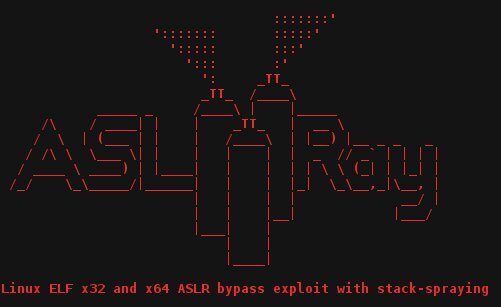
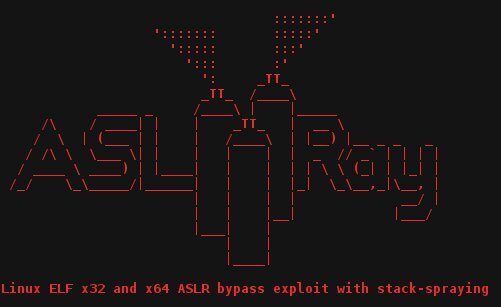
171Exploitation ToolsASLRay – Linux ELF x32 and x64 ASLR bypass exploit with stack-spraying
Linux ELF x32 and x64 ASLR bypass exploit with stack-spraying. Properties: ASLR bypass Cross-platform Minimalistic Simplicity Unpatchable Dependencies: Linux 2.6.12+ – will...
-
 274Exploitation Tools
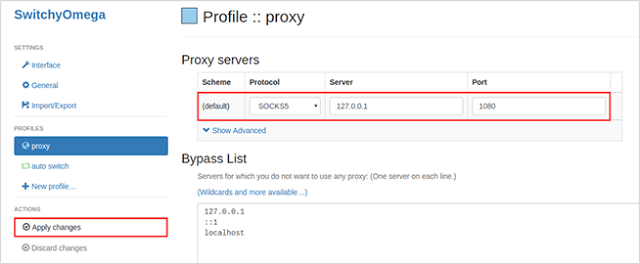
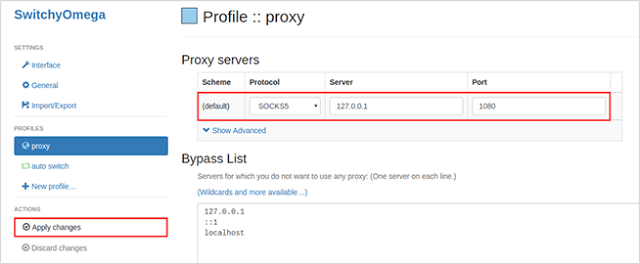
274Exploitation ToolsShadowSocks ConnecTion – A Wrapper Tool For Shadowsocks To Consistently Bypass Firewalls
A wrapper tool for shadowsocks to consistently bypass firewalls. Quick start Automatically connect The easiest way to run this tool is just...
-

 233How To
233How ToWAFNinja – A Tool To Bypass WAF
WAFNinja is a CLI tool written in Python. It is the best tool for penetration testers to bypass a WAF by automating...
-
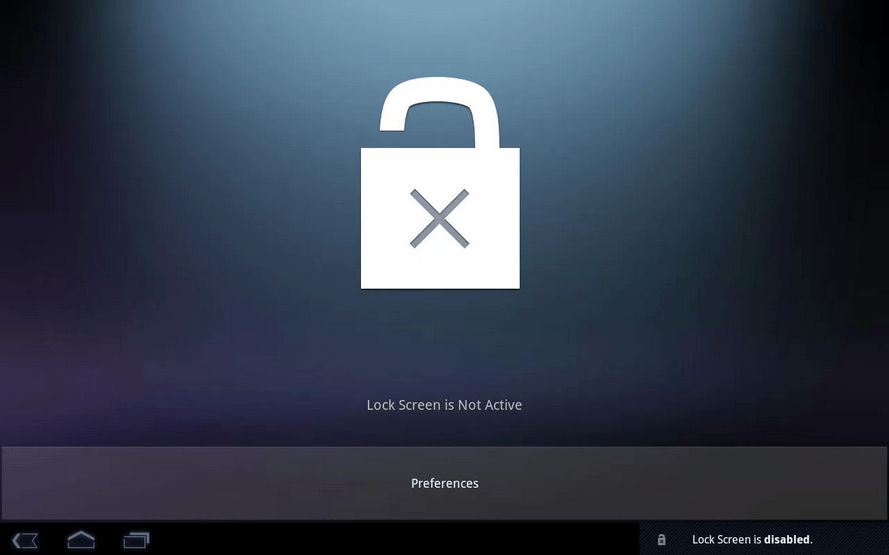
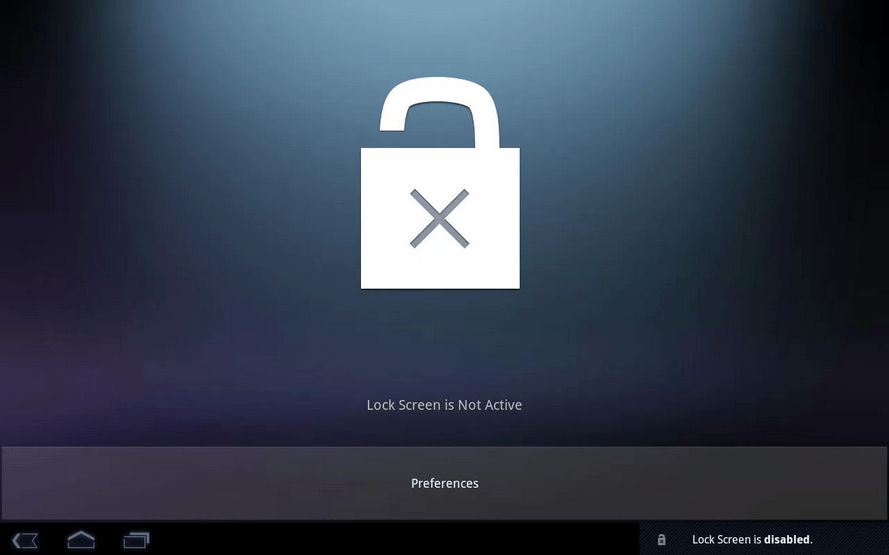 227Android Hacking
227Android HackingHow to bypass Android Lockscreen
Today i’m going to show you guys how to bypass android lockscreen using two methods. Method 1 What you need: Windows or...






