All posts tagged "Code"
-
 4.1KMalware
4.1KMalwareBlackCat: A New Rust-based Ransomware Malware Spotted in the Wild
Details have emerged about what’s the first Rust-language-based ransomware strain spotted in the wild that has already amassed “some victims from different...
-
 3.2KExploitation Tools
3.2KExploitation ToolsDrow – Injects Code Into ELF Executables Post-Build
drow is a command-line utility that is used to inject code and hook the entrypoint of ELF executables (post-build). It takes...
-
 4.5KReverse Engineering
4.5KReverse EngineeringHyperDbg – The Source Code Of HyperDbg Debugger
HyperDbg is designed with a focus on using modern hardware technologies to provide new features to the reverse engineering world. It...
-
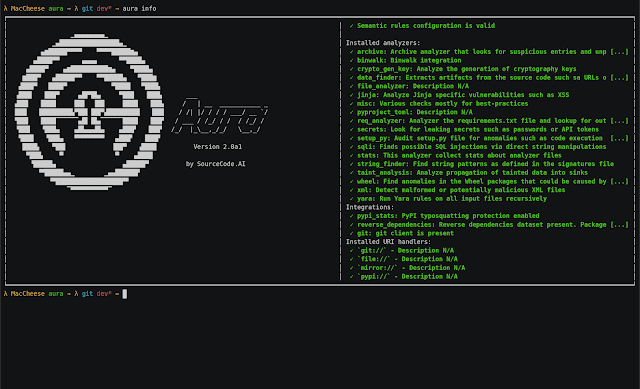
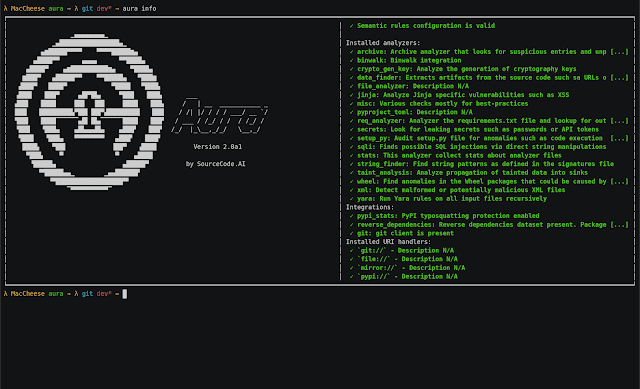 2.8KVulnerability Analysis
2.8KVulnerability AnalysisAura – Python Source Code Auditing And Static Analysis On A Large Scale
Aura is a static analysis framework developed as a response to the ever-increasing threat of malicious packages and vulnerable code published...
-
 382Reverse Engineering
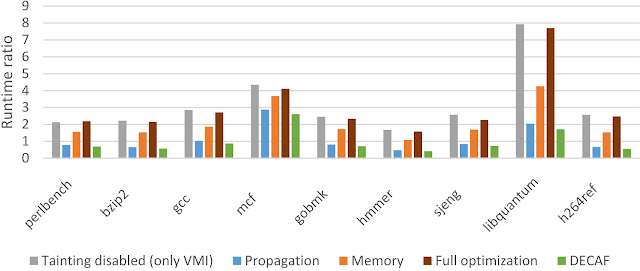
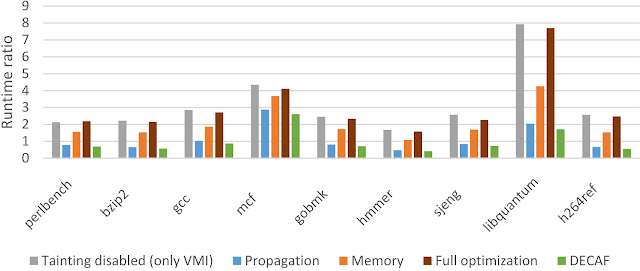
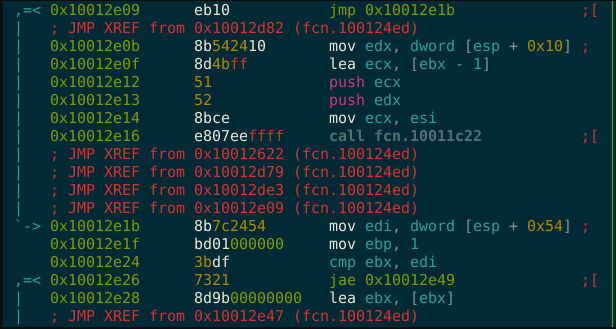
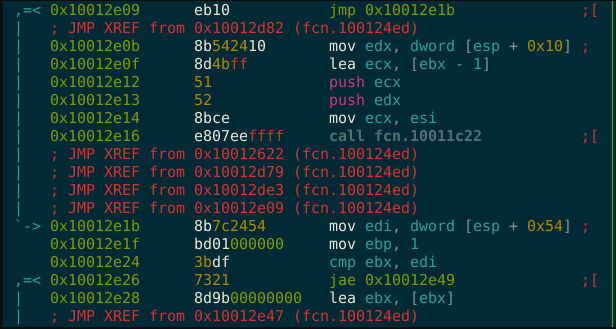
382Reverse EngineeringDECAF – Short for Dynamic Executable Code Analysis Framework
DECAF++, the new version of DECAF, taint analysis is around 2X faster making it the fastest, to the best of our...
-
 429Reverse Engineering
429Reverse EngineeringMetame – Metamorphic Code Engine For Arbitrary Executables
metame is a simple metamorphic code engine for arbitrary executables. From Wikipedia: Metamorphic code is code that when run outputs a...
-

 381Geek
381GeekQuality Of Code Doesn’t Matter Much In Open Source Contributions: Study
One can imagine that contributions to open source projects would be evaluated on the quality of code above anything else. However, researchers...
-

 270News
270NewsMicrosoft’s New Programming Language ‘Bosque’ Keeps Your Code Simple
Microsoft has launched a new programming language called Bosque. The company says Bosque has been designed to write code that is “simple, obvious,...
-

 374News
374NewsMost Loved And Hated Programming Languages In 2019, According To Hired
A recent survey of software engineers conducted by Hired has brought new insights into the state of programming languages in 2019. 98,000 developers participated...
-
 257Hacked
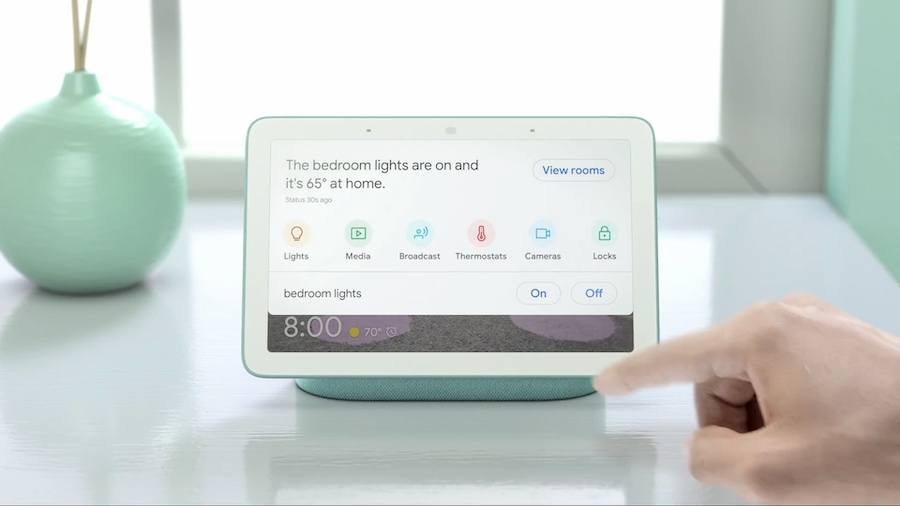
257HackedGoogle Home Hub Can Be Exploited By One Line Of Code
Security researcher Jerry Gamblin revealed how a few lines of codes written in XML for Google Home Hub can be used to gain...
-

 412Video Tutorials
412Video TutorialsWPSploit – WordPress Plugin Code Scanner – Kali Linux 2017.3
WPSploit is intended for Penetration Testers who audit WordPress plugins or developers who wish to audit their own WordPress plugins. It checks...
-
 235Articles
235ArticlesThousands Of IoT Devices Are Vulnerable To Remote Code Execution
Security researchers from security firm Elttam have discovered a critical vulnerability (tracked as CVE-2017-17562) in GoAhead tiny web server that affects many...
-

 247Reverse Engineering
247Reverse EngineeringRetDec – Retargetable Machine-Code Decompiler
RetDec is a retargetable machine-code decompiler based on LLVM. The decompiler is not limited to any particular target architecture, operating system, or executable file...
-

 252Articles
252ArticlesvBulletin Vulnerable To Code Execution & File Deletion Flaws
Last week, security researchers have published the details of two possibly critical flaws affecting version 5 of the vBulletin forum software. vBulletin...
-
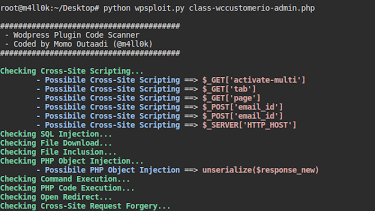
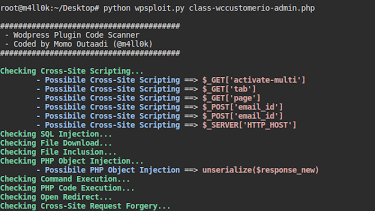 237Security Tools
237Security ToolsWPSploit – WordPress Plugin Code Scanner
This tool is intended for Penetration Testers who audit WordPress plugins or developers who wish to audit their own WordPress plugins. For...
-
 337Articles
337ArticlesWikiLeaks Publishes the Source Code and Development logs to Hive, a major component of the CIA infrastructure to Control its Malware
Today, 9 November 2017, WikiLeaks publishes the source code and development logs to Hive, a major component of the CIA infrastructure to...
-
 232Geek
232GeekTaco: This New Code From MIT Offers 100-Times Speed Increase
When we take sparse data into consideration, the analytic algorithms have to perform lots of additions and multiplications by zero. To imagine such...
-
Articles
Another Vulnerability is found in Intel Management Engine which allows execution of Code with no Digital Fingerprint
Taking advantage of Intel ME technology, within which attackers can execute unsigned code on the target machine. This leads to a full...
-
 243Geek
243Geek10 Signs That Show There’s A Hidden Coder Inside You
Short Bytes: What are the signs that you should look for before joining a coding class? Apart from the love for programming,...
-

 345Geek
345GeekWhat Is “Incremental-Hacking Cycle”? How It Improves Programming And Hacking Skills?
Short Bytes: Very few people understand the basics of hacking and hacker ethics. It’s basically exploring the open source code using various...
-
 184Geek
184GeekPyMotW — Python 3 Module Of The Week
Short Bytes: Programming can be a lot of fun, but sometimes you’re stuck reading through dry documentation which can get boring. PyMotW...






