All posts tagged "Cryptocurrency Miner"
-

 3.7KVulnerabilities
3.7KVulnerabilitiesHackers Exploiting Ivanti VPN Flaws to Deploy KrustyLoader Malware
A pair of recently disclosed zero-day flaws in Ivanti Connect Secure (ICS) virtual private network (VPN) devices have been exploited to deliver...
-

 2.2KMalware
2.2KMalwareNew Docker Malware Steals CPU for Crypto & Drives Fake Website Traffic
Vulnerable Docker services are being targeted by a novel campaign in which the threat actors are deploying XMRig cryptocurrency miner as well...
-

 1.3KMalware
1.3KMalwareBeware: 3 Malicious PyPI Packages Found Targeting Linux with Crypto Miners
Three new malicious packages have been discovered in the Python Package Index (PyPI) open-source repository with capabilities to deploy a cryptocurrency miner...
-
 3.3KMalware
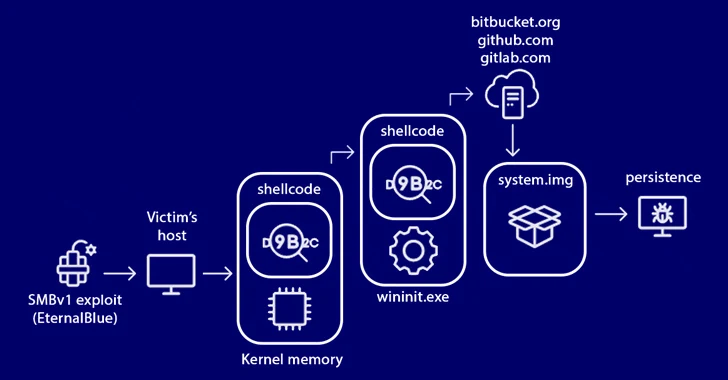
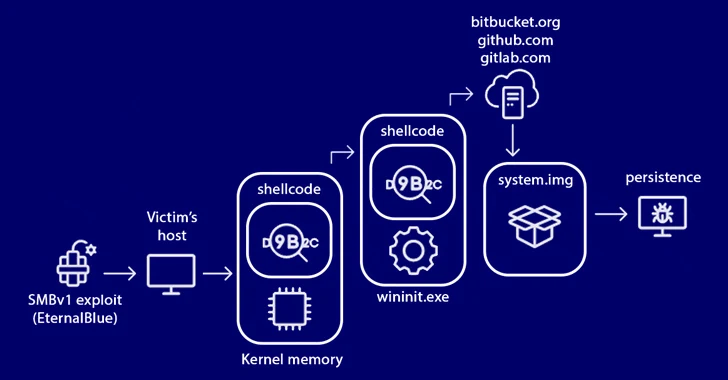
3.3KMalwareStripedFly Malware Operated Unnoticed for 5 Years, Infecting 1 Million Devices
An advanced strain of malware masquerading as a cryptocurrency miner has managed to fly the radar for over five years, infecting no...
-

 275Malware
275MalwareNew shc-based Linux Malware Targeting Systems with Cryptocurrency Miner
A new Linux malware developed using the shell script compiler (shc) has been observed deploying a cryptocurrency miner on compromised systems. “It...
-
 2.4KMalware
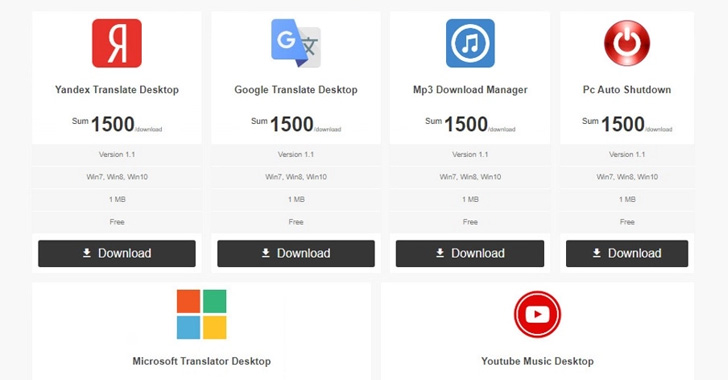
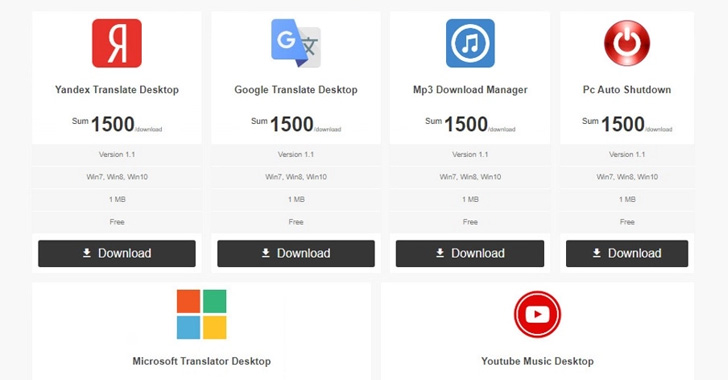
2.4KMalwareNitrokod Crypto Miner Infected Over 111,000 Users with Copies of Popular Software
A Turkish-speaking entity called Nitrokod has been attributed to an active cryptocurrency mining campaign that involves impersonating a desktop application for Google...
-

 2.8KMalware
2.8KMalwareCrypto Miners Using Tox P2P Messenger as Command and Control Server
Threat actors have begun to use the Tox peer-to-peer instant messaging service as a command-and-control method, marking a shift from its earlier...
-

 3.1KCyber Attack
3.1KCyber AttackAtlassian Confluence Flaw Being Used to Deploy Ransomware and Crypto Miners
A recently patched critical security flaw in Atlassian Confluence Server and Data Center products is being actively weaponized in real-world attacks to...
-

 4.3KMalware
4.3KMalwareNew Malware Loader ‘Verblecon’ Infects Hacked PCs with Cryptocurrency Miners
An unidentified threat actor has been observed employing a “complex and powerful” malware loader with the ultimate objective of deploying cryptocurrency miners...
-

 197Data Security
197Data SecurityKodak cryptocurrency miner melts in the air
The company behind the cryptocurrency miner apparently backed by Kodak confirmed that its plans have collapsed Last January, a computer made specifically...
-

 390How To
390How To7 Easy Ways To Block Cryptocurrency Mining In Your Web Browser
Cryptocurrencies are digital or virtual currencies that make use of encryption for security. As they are anonymous and decentralized in nature, one...
-

 315Malware
315MalwareAndroid Gamers Beware of Fake Fortnite Game that Contains Spyware and Cryptocurrency Miner
Android malware posing as Fake Fortnite Game includes spyware, cryptocurrency miner and install unwanted apps that show ads to generate revenue for...
-
 224Cryptocurrency
224CryptocurrencyUbuntu Snap Store Apps Contains Hidden Cryptocurrency Miner Malware
An Ubuntu user identified a malicious code that mines Bytecoin (BCN) hidden in the source code of the Ubuntu snap package (2048buntu...
-

 218Vulnerabilities
218VulnerabilitiesCryptocurrency Miner Distributed via PHP Weathermap Vulnerability, Targets Linux Servers
Legitimate and large-scale cryptocurrency mining operations often invest in dedicated hardware and electric consumption to make a profit. This doesn’t escape the...






