All posts tagged "cryptography"
-

 5.0KVulnerabilities
5.0KVulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
The maintainers of the PuTTY Secure Shell (SSH) and Telnet client are alerting users of a critical vulnerability impacting versions from 0.68...
-

 4.4KVulnerabilities
4.4KVulnerabilitiesNew “GoFetch” Vulnerability in Apple M-Series Chips Leaks Secret Encryption Keys
A new security shortcoming discovered in Apple M-series chips could be exploited to extract secret keys used during cryptographic operations. Dubbed GoFetch,...
-

 3.8KMalware
3.8KMalwareLummaC2 Malware Deploys New Trigonometry-Based Anti-Sandbox Technique
The stealer malware known as LummaC2 (aka Lumma Stealer) now features a new anti-sandbox technique that leverages the mathematical principle of trigonometry...
-

 4.7KMalware
4.7KMalwareRoyal Ransomware Threat Takes Aim at U.S. Healthcare System
The U.S. Department of Health and Human Services (HHS) has cautioned of ongoing Royal ransomware attacks targeting healthcare entities in the country....
-

 3.8KMalware
3.8KMalwareOpen Source Ransomware Toolkit Cryptonite Turns Into Accidental Wiper Malware
A version of an open source ransomware toolkit called Cryptonite has been observed in the wild with wiper capabilities due to its...
-
 3.9KMalware
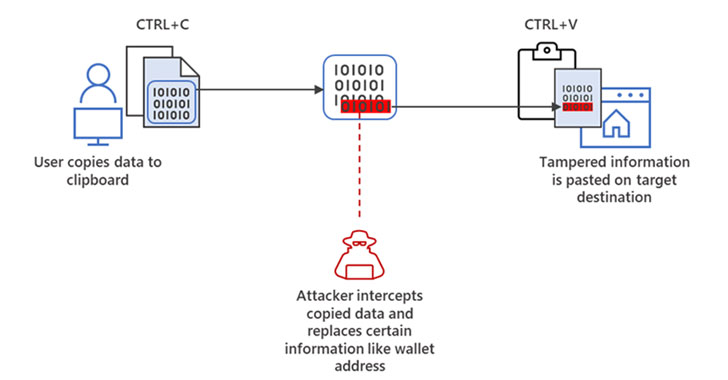
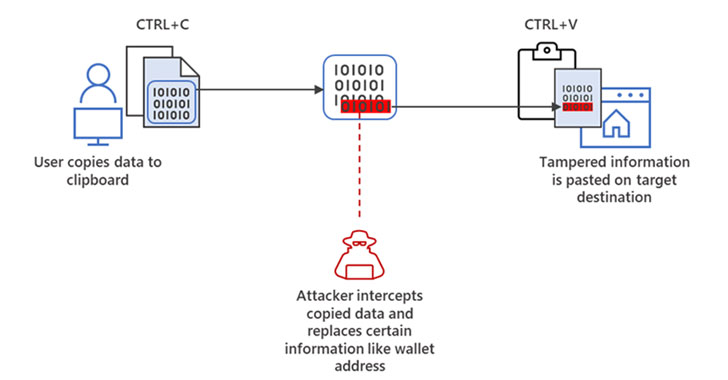
3.9KMalwareMicrosoft Warns of “Cryware” Info-Stealing Malware Targeting Crypto Wallets
Microsoft is warning of an emerging threat targeting internet-connected cryptocurrency wallets, signaling a departure in the use of digital coins in cyberattacks....
-

 4.2KNews
4.2KNewsScientists Crack Largest Encryption Key After 35 Million Hrs Of Computing
French scientists have set a world record by cracking the most complex cryptography algorithm to date. The encryption key, in this case,...
-

 356Exploitation Tools
356Exploitation ToolsCryptonDie – A Ransomware Developed For Study Purposes
CryptonDie is a ransomware developed for study purposes. Options --key key used to encrypt and decrypt files, default is random string(recommended)...
-

 352Hacked
352HackedThis Technique Claims To Make Passwords 14 Million% Tougher To Crack
Tide, an Australia-based non-profit organization has come up with a technique called ‘Splintering’ that claims to make usernames and passwords 14 million...
-
 348News
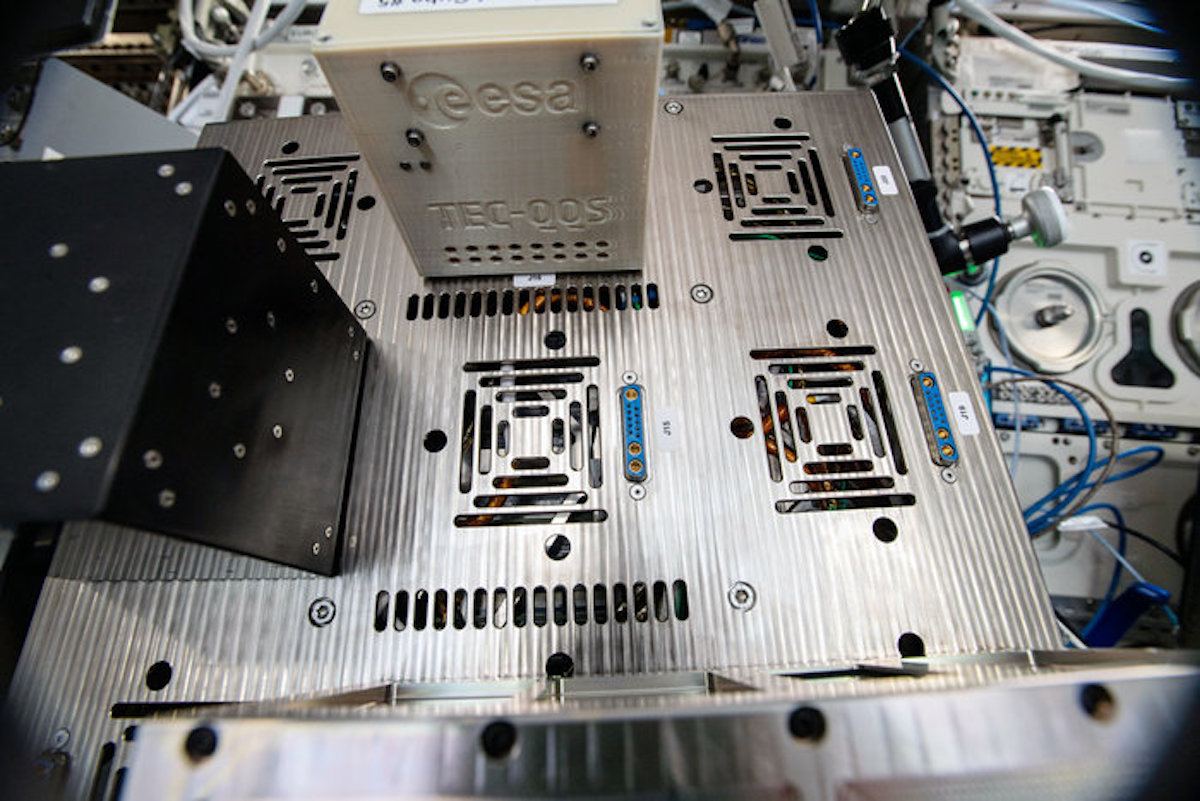
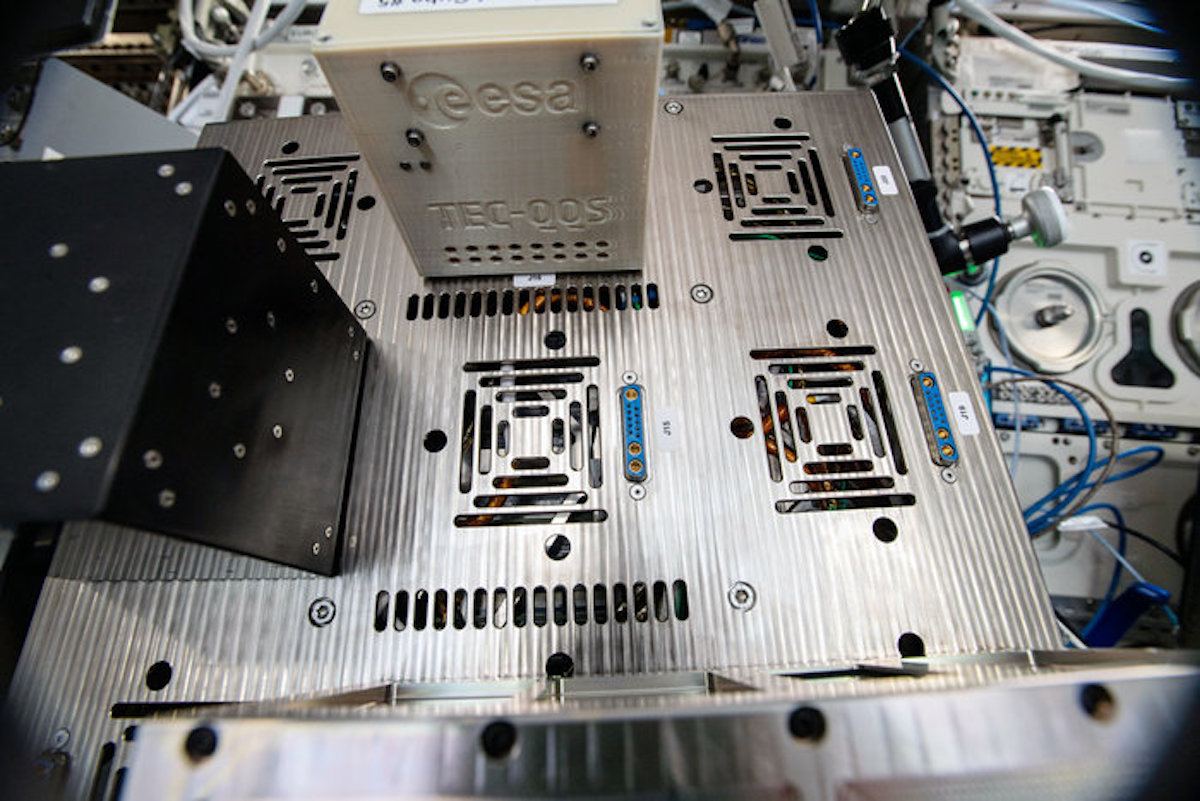
348NewsResearchers Are Using $10 Raspberry Pi Zero For ‘Cheap Encryption’ In Space
There are several techniques of encryption that are deployed to secure communication protocols and devices but these techniques aren’t effective if you...
-

 377Cryptocurrency
377CryptocurrencyWhat is Encryption?
Encryption is the process of converting clear information into the code to prevent unauthorized access to it. Governments, companies, and individuals use...
-

 305Cryptocurrency
305CryptocurrencyWhat is Cryptocurrency?
Digital currency, which is protected by cryptography and is usually used as a medium of exchange in a digital peer-to-peer (P2P) economic...
-
 301Geek
301GeekThe Advantages of a More Secure and Safer Blockchain
Blockchain technology has many uses and advantages over other types of ledger-based technology. One aspect of blockchain technology that is especially valuable...
-

 236Data Security
236Data SecurityCertification authorities, a weak point for web cryptography
According to an investigation, five out of 17 certification authorities are vulnerable to IP fragmentation attacks During a recent cybersecurity event in...
-

 339Cryptography and Encryption
339Cryptography and EncryptionimR0T – Send A Message To Your Whatsapp Contact And Protect Your Text By Encrypting And Decrypting (ROT13)
imR0T: Send a quick message with simple text encryption to your whatsapp contact and protect your text by encrypting and decrypting, basically...
-

 277Articles
277ArticlesCrypto Movie Starring Alexis Bledel Coming Soon
Cryptocurrencies such as Bitcoin have been gaining more and more public attention over recent years. Now, the digital currency industry has hit...
-

 320Data Security
320Data SecurityUpdate your devices: New Bluetooth flaw lets attackers monitor traffic
The Bluetooth flaw also opens door to a man-in-the-middle attack. The IT security researchers at Israel Institute of Technology have discovered a critical security vulnerability in...
-
 282Pentest Linux Distributions
282Pentest Linux DistributionsParrot Security 4.0 – Security GNU/Linux Distribution Designed with Cloud Pentesting and IoT Security in Mind
Parrot 4.0 is now available for download. The development process of this version required a lot of time, and many important updates...
-

 288Geek
288GeekIBM Developing World’s Tiniest Computer Smaller than a Grain of Salt
At Think 2018, IBM has announced developing world’s tiniest computer that will cost less than ten cents to manufacture and can monitor,...
-

 312Infosec
312InfosecSSL/TLS Certificate Revocation is Broken Time for More Reliable Revocation Checking Mechanism
We are moving fast to the encrypted world and the usage of TLS certificates increased dramatically.Security researcher Scott Helme discovered a way...
-
 244Cryptography and Encryption
244Cryptography and Encryptiondnscrypt-autoinstall – Automatic installation and configuration of DNSCrypt
A script for installing and automatically configuring DNSCrypt on Linux-based systems. Description DNSCrypt is a protocol for securing communications between a client...






