All posts tagged "cryptography"
-

 277Pentest Linux Distributions
277Pentest Linux DistributionsParrot Security 3.10 – Security Oriented GNU/Linux Distribution
Security GNU/Linux distribution designed with cloud pentesting and IoT security in mind. It includes a full portable laboratory for security and digital...
-
 258Cryptography and Encryption
258Cryptography and EncryptionAletheia – Machine Learning Image Steganalysis
Aletheia is a steganalysis tool for the detection of hidden messages in images. The goal of steganalysis is to identify suspected packages,...
-
 222Vulnerability Analysis
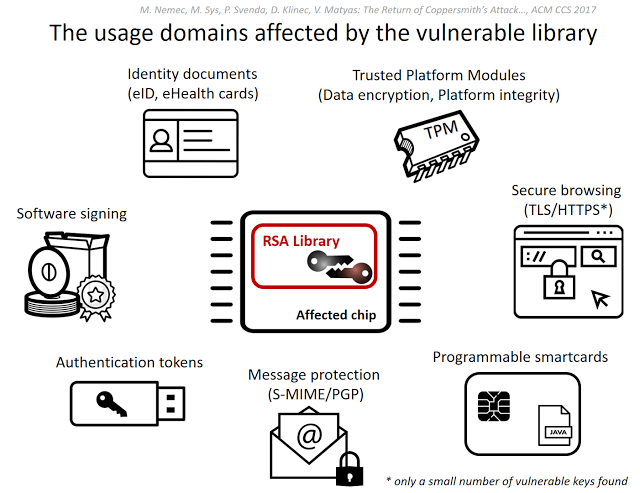
222Vulnerability AnalysisROC – Infineon RSA Vulnerability
This tool is related to ACM CCS 2017 conference paper #124 Return of the Coppersmith’s Attack: Practical Factorization of Widely Used RSA...
-
 240Pentest Linux Distributions
240Pentest Linux DistributionsParrot Security 3.9 – Security GNU/Linux Distribution Designed with Cloud Pentesting and IoT Security in Mind
Security GNU/Linux distribution designed with cloud pentesting and IoT security in mind. It includes a full portable laboratory for security and digital...
-
 403Cryptography and Encryption
403Cryptography and EncryptionBitCracker – Open Source BitLocker Password Cracking Tool
BitCracker is the first open source BitLocker password cracking tool. BitLocker is a full-disk encryption feature available in recent Windows versions (Vista,...
-

 203Cyber Crime
203Cyber CrimeDigital exchange joins law enforcement in hunt for WannaCry ransom bitcoins
Patrick O’Neill, a journalist at CyberScoopNews, has claimed that since August 3rd, ShapeShift has been helping law enforcement to trace bitcoin transactions...
-
 181Cryptocurrency
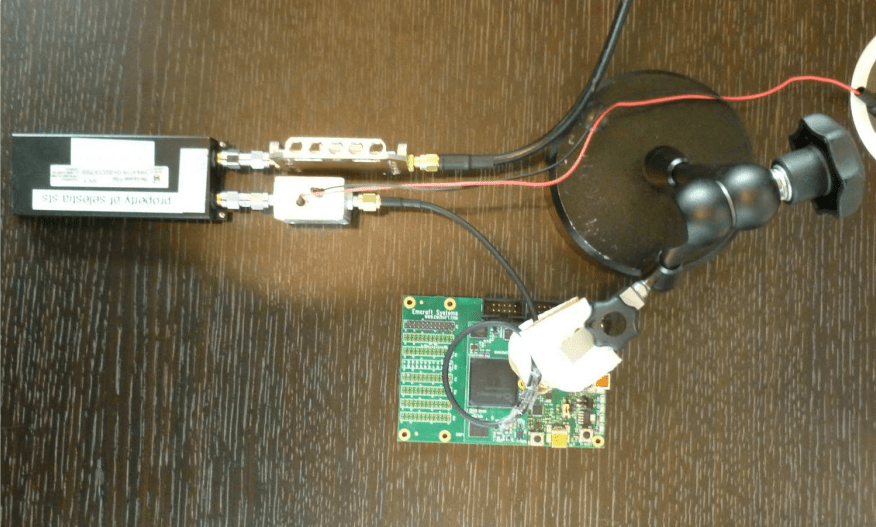
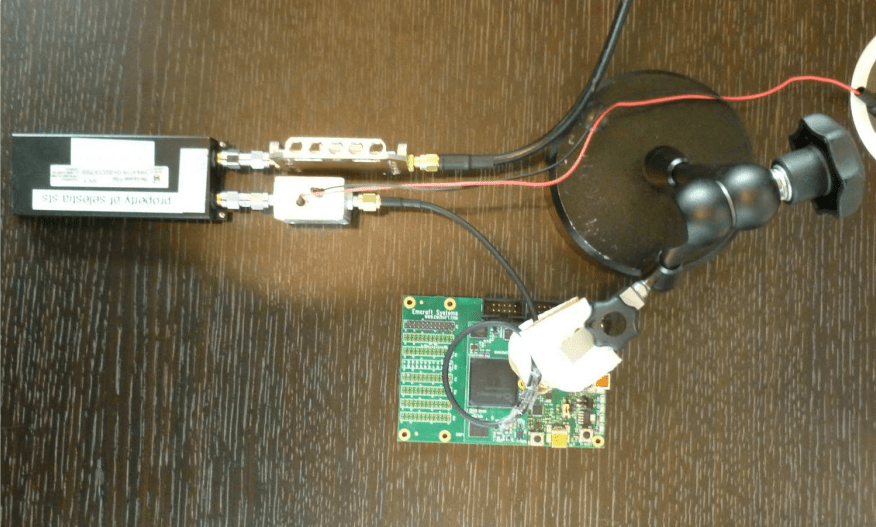
181CryptocurrencyAES-256 keys can be sniffed within Seconds Using €200 Worth Hardware kit
Side-channel attacks over AES is not new, previous attacks required a direct access. Now the security experts from Fox-IT and Riscure show how...
-
 210Hacked
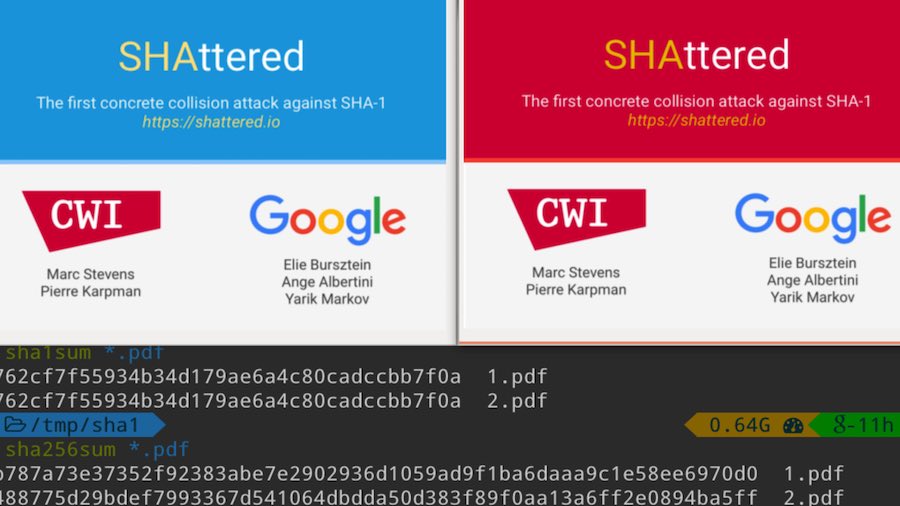
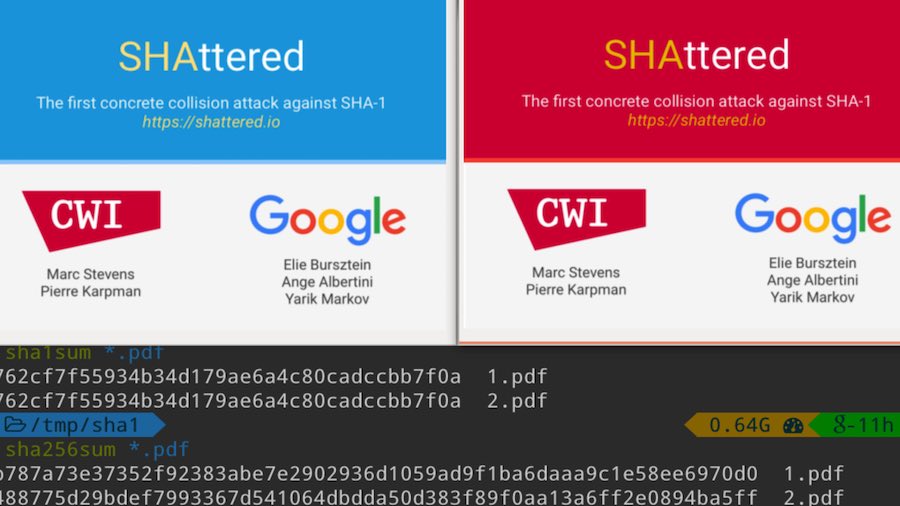
210HackedGoogle Just Broke SHA-1 Encryption — One Of The Most Popular Cryptographic Hash Functions
Short Bytes: Google has achieved the first successful SHA-1 collision attack. By creating a specially crafted PDF prefix, the researchers were able...
-

 289Cryptocurrency
289CryptocurrencyProject Wycheproof – Test crypto libraries against known attacks
Google announced Project Wycheproof – Test crypto libraries against known attacks, it is created and kept up by individuals from Google Security Team,...
-

 274Infosec
274InfosecEvolution of TLS1.3 – Enhanced security and speed
Evolution of TLS1.3 – Enhanced security and speed: As 2016 comes to close and we are preparing for a new year, it’s time...
-
 253Hacked
253HackedAdultFriendFinder Leak: Hackers Now Know Sexual Secrets Of 412 Million People
Short Bytes: One of the biggest data breaches on the Friend Finder Network has compromised the details of 412 million users across...
-
 205Hacked
205HackedUse This Tool To Find Your Personal Data On The Dark Web
Short Bytes: An information security company Terbium Labs claims to find your personal data, if it exists, on the dark web. Their...
-
 126Hacked
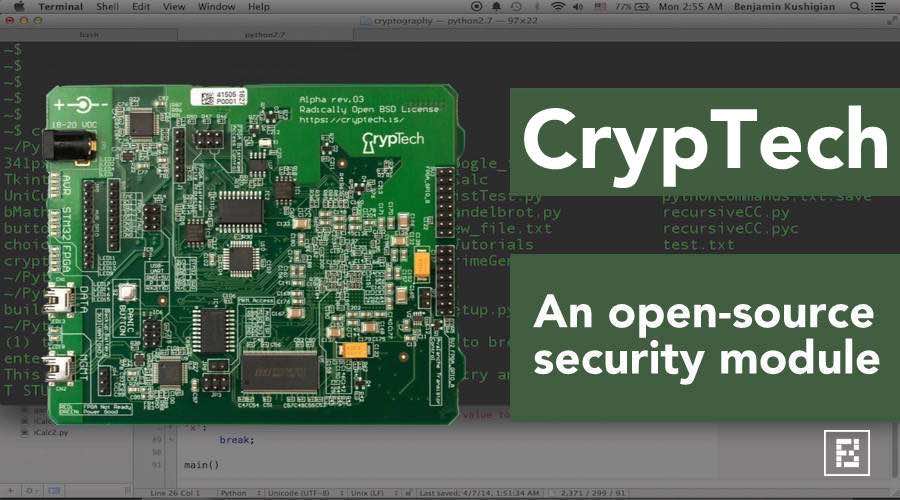
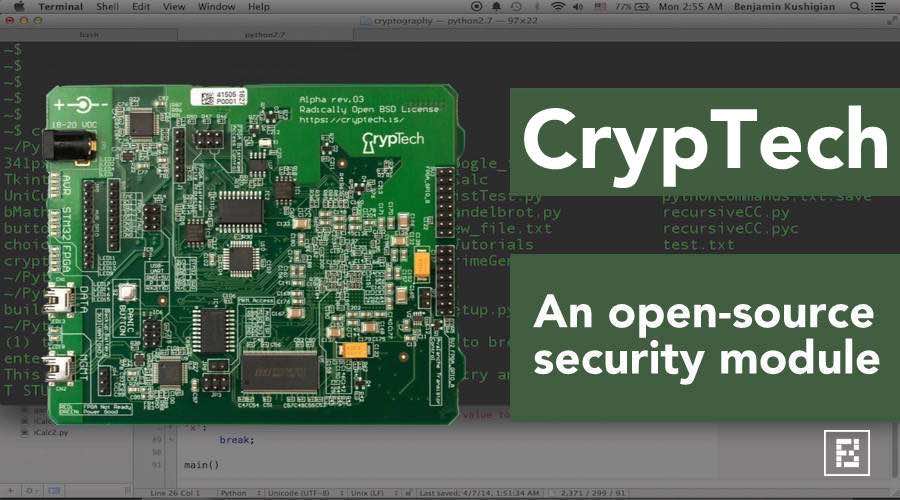
126HackedCrypTech — Internet Engineers’ New Open Source Weapon Against ‘Creepy’ Governments
Short Bytes: The CrypTech project is an independent security hardware development effort that consists of an international team. CrypTech Alpha is an...
-

 138Hacked
138HackedGoogle Is Working To Save Your Chrome Browser From Evil Quantum Computers
Short Bytes: Google has launched a new encryption algorithm in its Chrome web browser to fend off attacks launched by powerful quantum...
-
 166Hacked
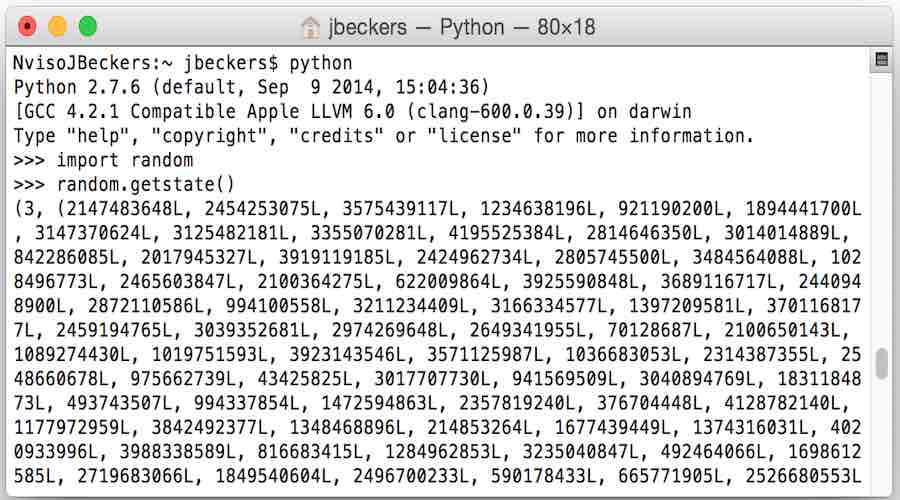
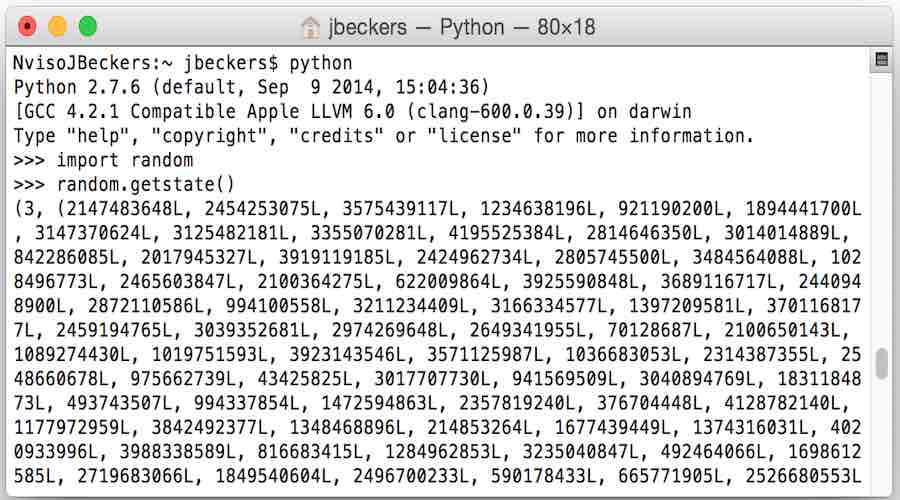
166HackedCybersecurity Breakthrough — A New Way To Generate Pure Random Numbers
Short Bytes: Using “masterpiece”, a new method to generate random numbers by the scientists at the university of Austin, random numbers could...
-

 184News
184NewsHackers To Demonstrate How To Hack An Offline Laptop
White Hat Hackers show us how to Steal Crypto Keys from a Laptop in Another Room Sans Internet Connection Last year, it...
-

 282Cyber Crime
282Cyber CrimeRansomware attack forces animal porn collector to plead guilty to police
A UK man has been charged this week with a non-custodial sentence, after a ransomware infection on his computer made him confess...






