All posts tagged "Cyber-Attack"
-

 457Cyber Attack
457Cyber AttackUrgent: Microsoft Issues Patches for 97 Flaws, Including Active Ransomware Exploit
It’s the second Tuesday of the month, and Microsoft has released another set of security updates to fix a total of 97...
-

 3.9KMalware
3.9KMalwareCISA Warns of 5 Actively Exploited Security Flaws: Urgent Action Required
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added five security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing...
-

 350Malware
350MalwareTaiwanese PC Company MSI Falls Victim to Ransomware Attack
Taiwanese PC company MSI (short for Micro-Star International) officially confirmed it was the victim of a cyber attack on its systems. The...
-

 2.1KCyber Attack
2.1KCyber AttackIran-Based Hackers Caught Carrying Out Destructive Attacks Under Ransomware Guise
The Iranian nation-state group known as MuddyWater has been observed carrying out destructive attacks on hybrid environments under the guise of a...
-

 5.1KCyber Attack
5.1KCyber AttackCryptoClippy: New Clipper Malware Targeting Portuguese Cryptocurrency Users
Portuguese users are being targeted by a new malware codenamed CryptoClippy that’s capable of stealing cryptocurrency as part of a malvertising campaign....
-

 3.0KData Breach
3.0KData BreachProtect Your Company: Ransomware Prevention Made Easy
Every year hundreds of millions of malware attacks occur worldwide, and every year businesses deal with the impact of viruses, worms, keyloggers,...
-

 2.1KMalware
2.1KMalwareCryptocurrency Companies Targeted in Sophisticated 3CX Supply Chain Attack
The adversary behind the supply chain attack targeting 3CX deployed a second-stage implant specifically singling out a small number of cryptocurrency companies....
-
 2.2KCyber Attack
2.2KCyber AttackWinter Vivern APT Targets European Government Entities with Zimbra Vulnerability
The advanced persistent threat (APT) actor known as Winter Vivern is now targeting officials in Europe and the U.S. as part of...
-
 945Cyber Attack
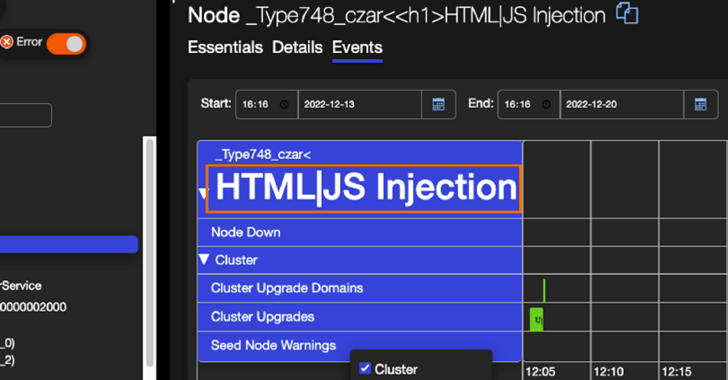
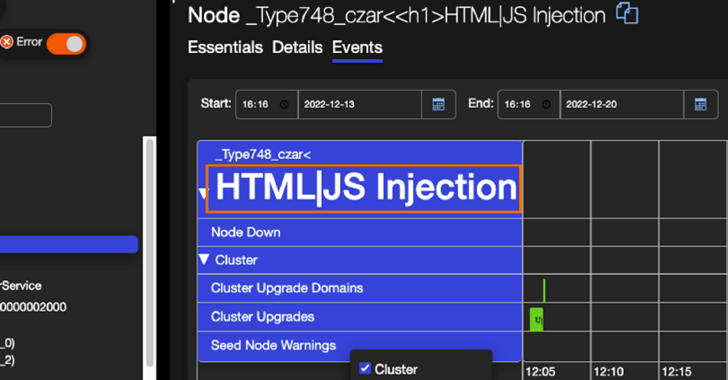
945Cyber AttackResearchers Detail Severe “Super FabriXss” Vulnerability in Microsoft Azure SFX
Details have emerged about a now-patched vulnerability in Azure Service Fabric Explorer (SFX) that could lead to unauthenticated remote code execution. Tracked...
-

 4.1KCyber Attack
4.1KCyber AttackNorth Korean APT43 Group Uses Cybercrime to Fund Espionage Operations
A new North Korean nation-state cyber operator has been attributed to a series of campaigns orchestrated to gather strategic intelligence that aligns...
-

 3.1KCyber Attack
3.1KCyber AttackOperation Soft Cell: Chinese Hackers Breach Middle East Telecom Providers
Telecommunication providers in the Middle East are the subject of new cyber attacks that commenced in the first quarter of 2023. The...
-
 2.3KCyber Attack
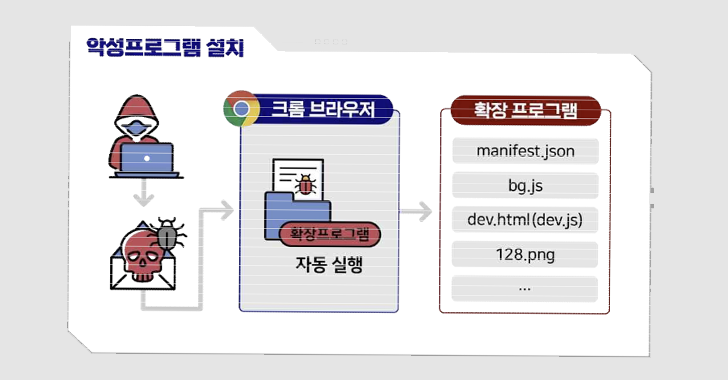
2.3KCyber AttackGerman and South Korean Agencies Warn of Kimsuky’s Expanding Cyber Attack Tactics
German and South Korean government agencies have warned about cyber attacks mounted by a threat actor tracked as Kimsuky using rogue browser...
-
 3.1KCyber Attack
3.1KCyber AttackWinter Vivern APT Group Targeting Indian, Lithuanian, Slovakian, and Vatican Officials
The advanced persistent threat known as Winter Vivern has been linked to campaigns targeting government officials in India, Lithuania, Slovakia, and the...
-

 1.6KData Breach
1.6KData BreachMultiple Hacker Groups Exploit 3-Year-Old Vulnerability to Breach U.S. Federal Agency
Multiple threat actors, including a nation-state group, exploited a critical three-year-old security flaw in Progress Telerik to break into an unnamed federal...
-

 828Data Breach
828Data BreachDoes Your Help Desk Know Who’s Calling?
Phishing, the theft of users’ credentials or sensitive data using social engineering, has been a significant threat since the early days of...
-

 3.5KMalware
3.5KMalwareSharp Panda Using New Soul Framework Version to Target Southeast Asian Governments
High-profile government entities in Southeast Asia are the target of a cyber espionage campaign undertaken by a Chinese threat actor known as...
-
 4.2KMalware
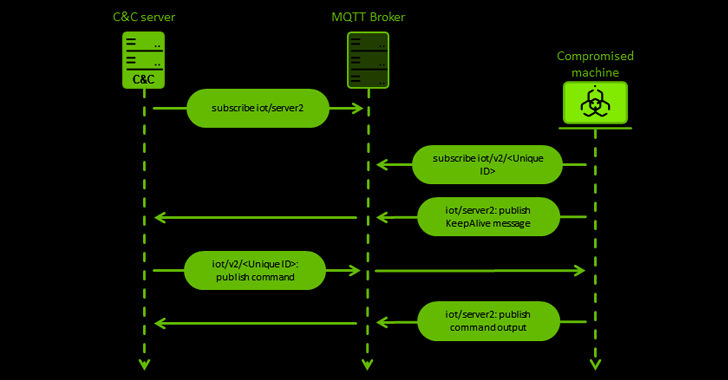
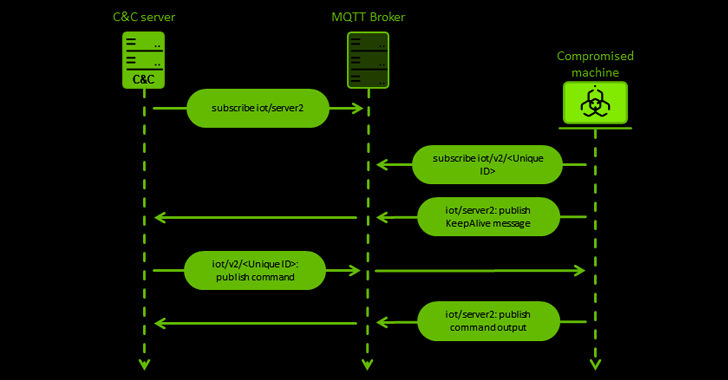
4.2KMalwareChinese Hackers Targeting European Entities with New MQsTTang Backdoor
The China-aligned Mustang Panda actor has been observed using a hitherto unseen custom backdoor called MQsTTang as part of an ongoing social...
-

 889Malware
889MalwareCybercriminals Targeting Law Firms with GootLoader and FakeUpdates Malware
Six different law firms were targeted in January and February 2023 as part of two disparate threat campaigns distributing GootLoader and FakeUpdates...
-
 2.6KMalware
2.6KMalwareNew EX-22 Tool Empowers Hackers with Stealthy Ransomware Attacks on Enterprises
A new post-exploitation framework called EXFILTRATOR-22 (aka EX-22) has emerged in the wild with the goal of deploying ransomware within enterprise networks...
-

 1.2KCyber Attack
1.2KCyber AttackCISA Issues Warning on Active Exploitation of ZK Java Web Framework Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a high-severity flaw affecting the ZK Framework to its Known Exploited Vulnerabilities...
-
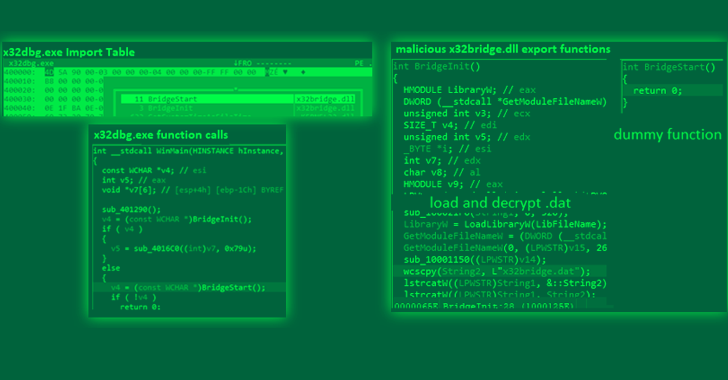
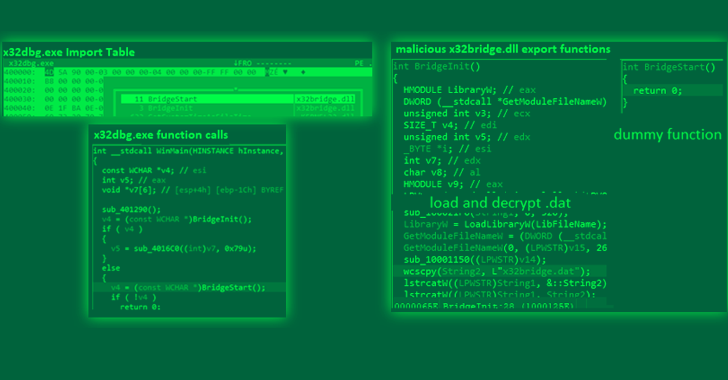 3.6KCyber Attack
3.6KCyber AttackPlugX Trojan Disguised as Legitimate Windows Debugger Tool in Latest Attacks
The PlugX remote access trojan has been observed masquerading as an open source Windows debugger tool called x64dbg in an attempt to...






