All posts tagged "Cyber Security"
-
 1.1KVulnerabilities
1.1KVulnerabilitiesF5 BIG-IP Flaw Let Hackers Execute Arbitrary System Commands
F5 Networks have addressed critical vulnerabilities in its BIG-IP networking device. The vulnerability tracked as CVE-2021-23031 is a privilege escalation issue on...
-
 4.4KMalware
4.4KMalwareNew Malware “MosaicLoader” Targeting Users Searching for Pirated Software
The new ‘MosaicLoader’ malware, a password-stealing Windows malware is distributed through adverts for cracked software. The cybersecurity company Bitdefender warns as the...
-

 720Cyber Crime
720Cyber Crime4 Ways For Employees To Distinguish Phishing Attacks
Many movies and other media may have a bit of a warped idea of what hackers do, exactly. But one show that...
-

 3.6KData Security
3.6KData Security5 Top Cybersecurity Threats to Businesses
Cybersecurity threats are unpredictable but taking a closer look at them and implementing proper security measures seems like a wise decision. The...
-
 4.3KNews
4.3KNewsTop Certifications for Network Security Administrators in 2021
From cybersecurity to IT security; the demand for security professionals is at its peak like never before. Here are some certifications that...
-

 3.7KData Security
3.7KData SecurityGlobal cybersecurity market is poised to reach nearly $420 billion by 2028
Enterprises of all sizes and industries face a dilemma. How do they justify an increased need for cybersecurity spending in the face...
-

 3.7KCyber Events
3.7KCyber Events5 Biggest Ransomware Attacks of All Time
Cybersecurity threats, and in particular ransomware attacks, are facts of life and daily occurrences in an increasingly digital economy. The more commercial...
-

 1.1KCyber Events
1.1KCyber Events“Hacker Games” launched to challenge and improve cybersecurity skills
Launched by Veracode; Hacker Games will last for 2 weeks (March 15-26, 2021). With the hackers becoming more persistent in finding vulnerabilities...
-

 2.4KData Breach
2.4KData BreachRussian Who Hacked LinkedIn, Dropbox Sentenced to 7 Years in Prison
A Russian hacker who was found guilty of hacking LinkedIn, Dropbox, and Formspring over eight years ago has finally been sentenced to...
-

 2.3KMobile Security
2.3KMobile SecurityCybersecurity and Your Phone Today
Recently, Samsung has rolled out security updates for its mobile devices to fix some critical security vulnerabilities. Samsung has published the official...
-

 3.1KData Breach
3.1KData BreachHackers Using Google Analytics to Bypass Web Security and Steal Credit Cards
Researchers reported on Monday that hackers are now exploiting Google’s Analytics service to stealthily pilfer credit card information from infected e-commerce sites....
-

 2.0KData Breach
2.0KData BreachHackers Leaked 269 GB of U.S. Police and Fusion Centers Data Online
A group of hacktivists and transparency advocates has published a massive 269 GB of data allegedly stolen from more than 200 police...
-

 2.4KData Breach
2.4KData BreachAny Indian DigiLocker Account Could’ve Been Accessed Without Password
The Indian Government said it has addressed a critical vulnerability in its secure document wallet service Digilocker that could have potentially let...
-

 2.3KData Breach
2.3KData BreachJoomla Resources Directory (JRD) Portal Suffers Data Breach
Joomla, one of the most popular Open-source content management systems (CMS), last week announced a new data breach impacting 2,700 users who...
-
 3.7KPhishing
3.7KPhishingBeware of Zoom Phishing Campaign that Threatens Employees Contracts will be Suspended or Terminated
A new zoom phishing campaign observed asking recipients to join a zoom meeting that threatens employees that their contracts will be either...
-
 1.1KVulnerabilities
1.1KVulnerabilitiesNew PlunderVolt Attack Targets Intel SGX Enclaves by Tweaking CPU Voltage
A team of cybersecurity researchers demonstrated a novel yet another technique to hijack Intel SGX, a hardware-isolated trusted space on modern Intel...
-

 952Malware
952MalwareFacebook Sued Hong Kong Firm for Hacking Users and Ad Fraud Scheme
Following its efforts to take legal action against those misusing its social media platform, Facebook has now filed a new lawsuit against...
-
 4.8KVulnerabilities
4.8KVulnerabilitiesSevere Auth Bypass and Priv-Esc Vulnerabilities Disclosed in OpenBSD
OpenBSD, an open-source operating system built with security in mind, has been found vulnerable to four new high-severity security vulnerabilities, one of...
-
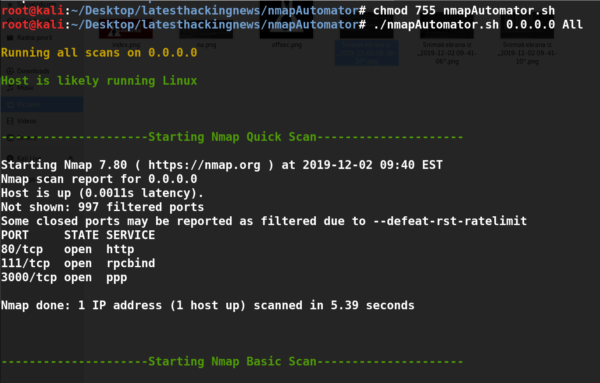
 3.3KHacking Tools
3.3KHacking ToolsNmap Automator – a tool I used during OSCP for simple recon
Nmap Automator is a great tool for initial port scans of a given ip address. It automates the scan techniques which I...
-

 1.2KMalware
1.2KMalwareZeroCleare: New Iranian Data Wiper Malware Targeting Energy Sector
Cybersecurity researchers have uncovered a new, previously undiscovered destructive data-wiping malware that is being used by state-sponsored hackers in the wild to...
-
 2.2KVulnerabilities
2.2KVulnerabilitiesCritical Flaw in GoAhead Web Server Could Affect Wide Range of IoT Devices
Cybersecurity researchers today uncovered details of two new vulnerabilities in the GoAhead web server software, a tiny application widely embedded in hundreds...






