All posts tagged "cybercrime"
-
 230Data Security
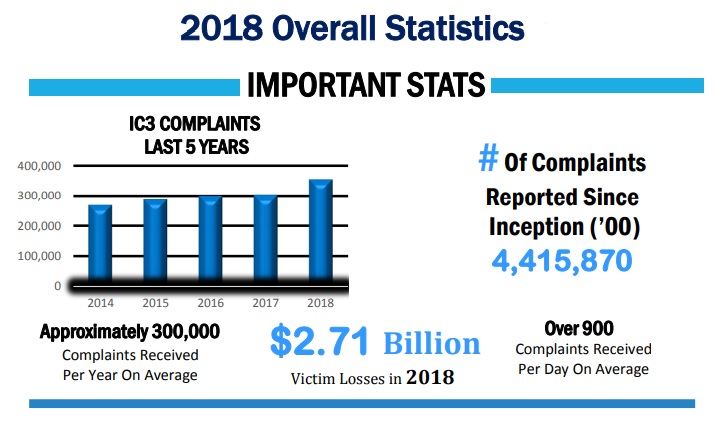
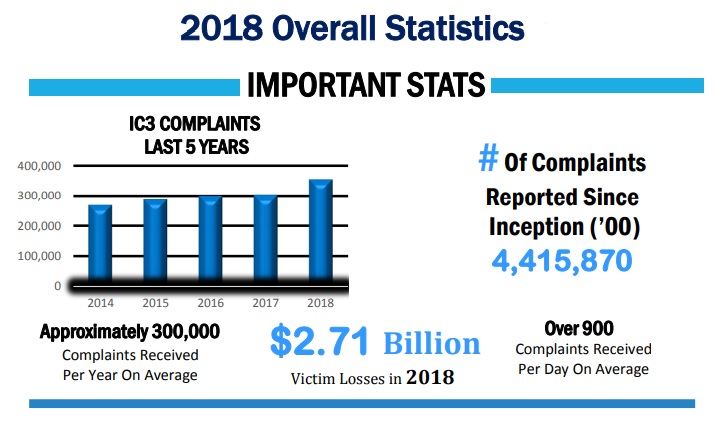
230Data SecurityLosses due to Internet crimes reached nearly $3 billion USD in 2018: FBI
The U.S. government’s online crime report states that, during the year 2018, the FBI Internet Crime Complaints Center (IC3) received about 352k...
-

 337News
337NewsGoogle Helps Identify Crime Suspects Using Location History
Google, by using the location data in devices, helps identify suspects of crimes in many instances of criminal investigation. Google keeps tracking...
-

 243Incidents
243IncidentsAn individual is arrested for blackmailing adult websites visitors
A hacker dedicated to blackmailing visitors of pornographic content websites has been arrested by the British authorities. According to the vulnerability testing...
-
 239News
239NewsCybercrime On Facebook Is Of Least Concern To Its Executives
There is no better time for committing Cybercrime on Facebook than right now. At least that’s the intent the platform is displaying with its...
-

 384Leaks
384LeaksWill AI Solve the Gaming Industry’s Cybersecurity Issues?
Over the last few years, several gaming platform-based cyber attacks have come to light. Given the rise in microtransactions and in-game currency...
-

 3.0KRansomware
3.0KRansomwareCommunity Efforts Against Ransomware
Ransomware attacks are by nature loud, they immediately inform the user of the device that their files are encrypted, and they need...
-

 283Malware
283MalwareOne of the largest aluminum producer suffers severe ransomware infection
Reports of an ethical hacker from the International Institute of Cyber Security mention that Norsk Hydro, one of the world’s leading aluminum-producing...
-

 342News
342NewsWordPress Plugin WooCommerce is Vulnerable to XSS Attacks
As WordPress gained popularity over its CMS competitors like Joomla and Drupal, it grew to a level where plugin developers jumped into...
-

 225Incidents
225IncidentsAttention: New viral challenge that encourages children to hurt themselves; experts consider it might be a scam
Some consider that the real goal behind the operators of this viral challenge is to collect sensitive details According to experts in...
-

 341Incidents
341IncidentsA 25 years old earned $17M USD, a seaside home and luxury cars by selling drugs in dark web
The Australian authorities maintain that Ward operated a sophisticated drug distribution network on dark web Australian authorities have seized a house on...
-

 233Incidents
233IncidentsHackers try to steal a bank in Malta; security operation shutdown is implemented
All the services of the Bank of Valletta have been interrupted The Bank of Valletta, Malta, shut down all of its operations...
-

 240Data Security
240Data SecurityCriminals in darknet seek to recruit business employees: How to Prevent
Organizations face a new inside threat Cybercriminals have rendered the darknet into their workplace. According to security monitoring and ethical hacking experts...
-

 3.0KData Breach
3.0KData BreachEskom’s Denial Of Responsibility With The Data Breach, Invalid According To Security Experts
Power utilities are not safe against cybercriminals, this is the fact that has been proven by Eskom (Elektrisiteitsvoorsieningskommissie), a power utility in...
-

 405Data Security
405Data SecurityPolice acts against website offering for-hire cyberattack services
British police seized over 50 devices probably used to perform cyberattacks during several raids British authorities have carried out multiple raids against...
-

 207News
207NewsBusiness Interruption Again Top Business Risk in Singapore
Business interruption once again becomes the top business risk in Singapore, according to a recent report. It is the eighth annual Allianz...
-

 323News
323NewsThings CISOs Should Keep in Mind, for 2019
CISOs (Chief Information Security Officers) have a critical role to play, as regards the overall security of any enterprise today. And it’s...
-

 181Data Security
181Data SecurityDo you have the required skills to work for cybercriminals?
Criminal gangs seek to recruit people with advanced computer skills According to network security specialists from the International Institute of Cyber Security,...
-

 203Data Security
203Data SecurityPharmaceutical companies, cybercriminals’ favorite targets
Malicious actors have shown particular attention to the drug development industry Information security and digital forensics specialists from the International Institute of...
-

 675Leaks
675LeaksCybercrime Evolution: 2017 is for Ransomware, while 2018 is for Cryptojacking Malware
The growth of Bitcoin and its derivative cryptocurrencies have expanded people’s point-of-view on what it really is, a new representation of real-world...
-

 186Cyber Crime
186Cyber CrimeTA505 Cybercrime Group Experimenting with a New RAT In The Wild
Apparently, the notorious cybercrime community named TA505 is very active again, this time they are heavily testing in the wild the effectiveness...
-

 300Cyber Crime
300Cyber CrimeWindows-based Forensic Tools Available for Everyone
Forensic investigations became the “new normal”, as cybercriminals increased their activities at the expense of users and businesses alike. It is sad...






