All posts tagged "cybersecurity"
-
 4.0KHack Tools
4.0KHack ToolsSharpHide – Tool To Create Hidden Registry Keys
Just a nice persistence trick to confuse DFIR investigation. Uses NtSetValueKey native API to create a hidden (null terminated) registry key. This...
-
 1.0KHack Tools
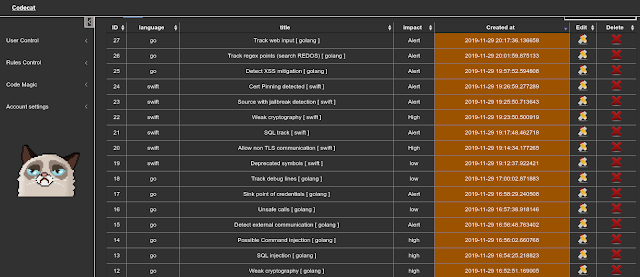
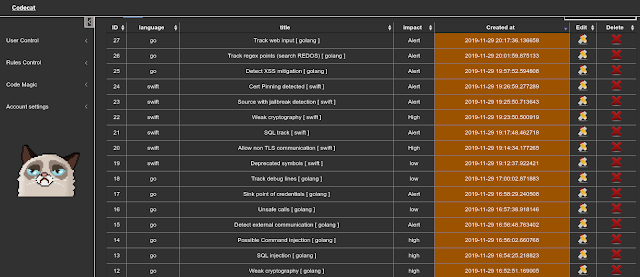
1.0KHack ToolsCodecat – Tool To Help In Manual Analysis In Codereview
CodeCat is a open source tool to help you in codereview, to find/track sinks and this points follow regex rules…How too install,...
-

 4.1KData Security
4.1KData SecurityHackerOne platform got hacked by a researcher who reported a vulnerability but never got paid
HackerOne is one of the most important vulnerability reporting platforms, so it has access to large amounts of information, although sometimes that...
-

 4.6KData Security
4.6KData SecurityThis Outlook bug lets hackers access your emails just like Hillary Clinton
According to web application security specialists, a recently patched vulnerability in Microsoft login system could have been exploited to trick some users...
-
 3.1KIncidents
3.1KIncidentsLucky Strike, Pall Mall and Kent consumers’ information leaked and infected by ransomware
Data protection specialists from security firm vpnMentor reported the detection of a data breach on a Romanian web platform, owned by tobacco...
-

 2.7KHack Tools
2.7KHack ToolsLinuxCheck – Linux Information Collection Script
A small linux information collection script is mainly used for emergency response. It can be used under Debian or Centos.Features CPU TOP10,...
-
 2.1KHack Tools
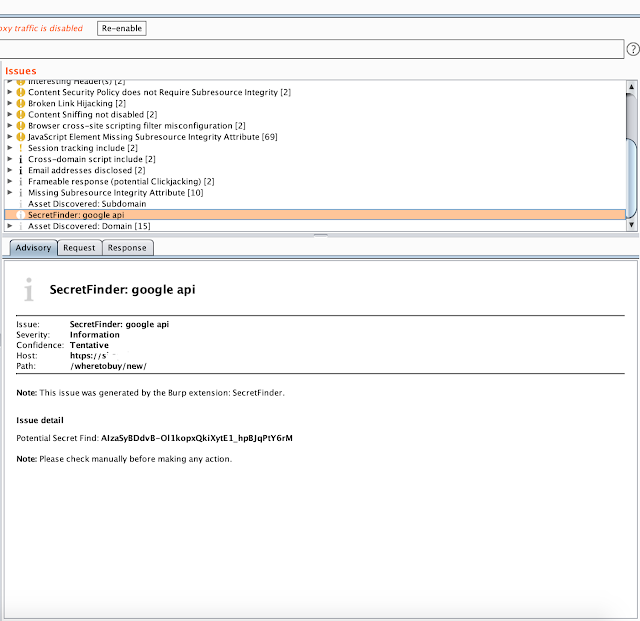
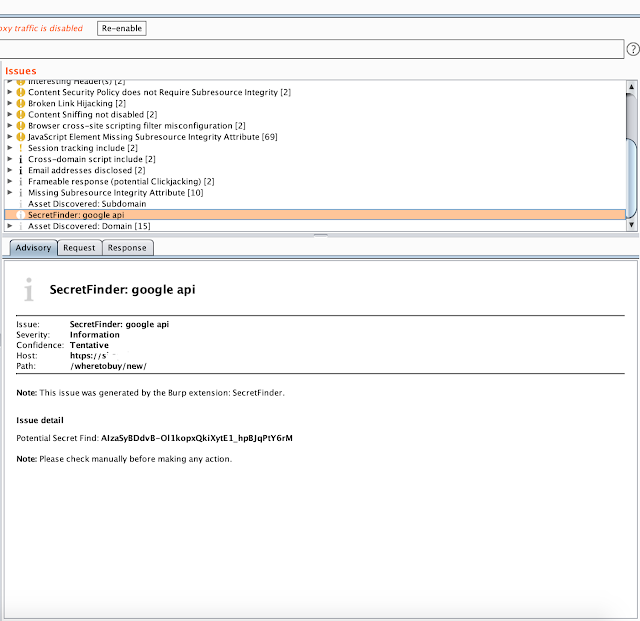
2.1KHack ToolsBurp Suite Secret Finder – Burp Suite Extension To Discover Apikeys/Tokens From HTTP Response
Burp Suite extension to discover a apikey/tokens from HTTP response. Install download SecretFinder wget https://raw.githubusercontent.com/m4ll0k/BurpSuite-Secret_Finder/master/SecretFinder.pyorgit clone https://github.com/m4ll0k/BurpSuite-Secret_Finder.git now open Burp > Extender...
-

 2.7KHack Tools
2.7KHack ToolsaSYNcrone – A SYN Flood DDoS Tool
aSYNcrone is a SYN Flood DDoS Attack Tool!Usage: git clone https://github.com/fatih4842/aSYNcrone.gitcd aSYNcronegcc aSYNcrone.c -o aSYNcrone./aSYNcrone <source IP> <source port> <destination IP> <destination...
-
 908Hack Tools
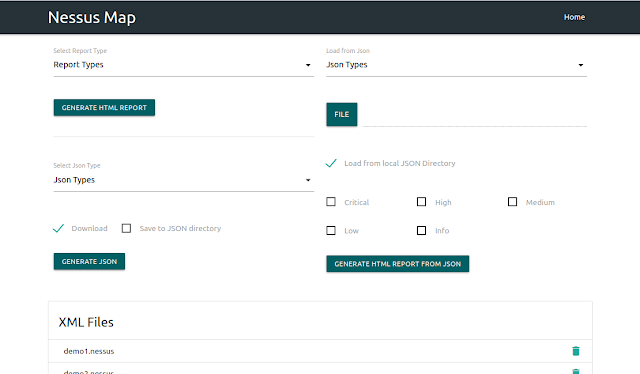
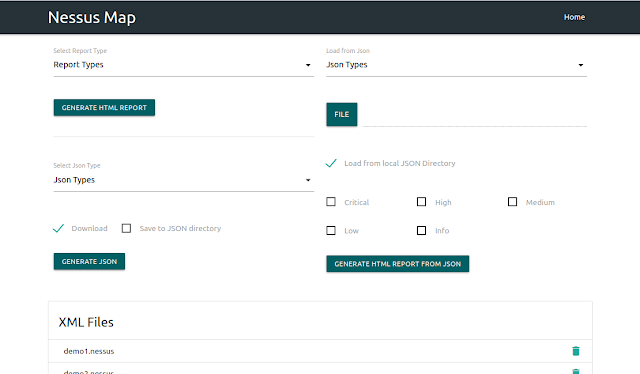
908Hack ToolsNessus Map – Parse .Nessus File(S) And Shows Output In Interactive UI
Nessus XML Praser Requirements Python3 Django Tested on Ubuntu 18.04 What it does Vulnerability based parsing Service based parsing Host bases parsing...
-

 3.7KHack Tools
3.7KHack ToolsSooty – The SOC Analysts All-In-One CLI Tool To Automate And Speed Up Workflow
Sooty is a tool developed with the task of aiding SOC analysts with automating part of their workflow. One of the goals...
-

 1.5KHack Tools
1.5KHack ToolsCAPE – Malware Configuration And Payload Extraction
CAPE is a malware sandbox. It is derived from Cuckoo and is designed to automate the process of malware analysis with the...
-

 2.2KHack Tools
2.2KHack ToolsANDRAX v4 DragonFly – Penetration Testing on Android
ANDRAX is a Penetration Testing platform developed specifically for Android smartphones, ANDRAX has the ability to run natively on Android so it behaves like a common...
-

 2.9KHack Tools
2.9KHack ToolsGoblin – An Impish, Cross-Platform Binary Parsing Crate, Written In Rust
Documentationhttps://docs.rs/goblin/changelog UsageGoblin requires rustc 1.31.1.Add to your Cargo.toml [dependencies]goblin = "0.1" Features awesome crate name zero-copy, cross-platform, endian-aware, ELF64/32 implementation – wow!...
-

 2.3KHack Tools
2.3KHack ToolsCCAT – Cloud Container Attack Tool For Testing Security Of Container Environments
Cloud Container Attack Tool (CCAT) is a tool for testing security of container environments. Quick reference Where to get help: the Pacu/CloudGoat/CCAT...
-
 1.3KHack Tools
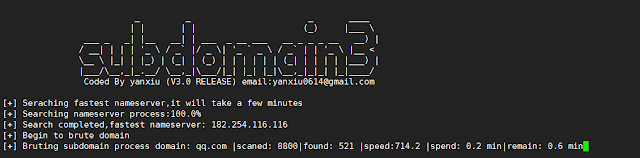
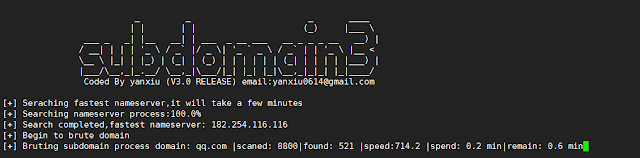
1.3KHack ToolsSubdomain3 – A New Generation Of Tool For Discovering Subdomains
Subdomain3 is a new generation of tool , It helps penetration testers to discover more information in a shorter time than other...
-

 4.1KHack Tools
4.1KHack ToolsMordor – Re-play Adversarial Techniques
The Mordor project provides pre-recorded security events generated by simulated adversarial techniques in the form of JavaScript Object Notation (JSON) files for...
-
 5.4KHack Tools
5.4KHack ToolsAttack Monitor – Endpoint Detection And Malware Analysis Software
Attack Monitor is Python application written to enhance security monitoring capabilites of Windows 7/2008 (and all later versions) workstations/servers and to automate...
-

 4.1KIncidents
4.1KIncidents4 million credit cards used in restaurants for sale in hacking forums
A hacker group has released a new database of stolen payment cards on Joker’s Stash, a popular hacking forum. According to web...
-

 1.5KMalware
1.5KMalwareNew malware transfers money from your mobile banking app to a hackers’ account
There are currently multiple variants of malware for mobile devices used for different purposes. Digital forensics experts mention that, during the most...
-

 4.3KHack Tools
4.3KHack ToolsBaseQuery – A Way To Organize Public Combo-Lists And Leaks In A Way That You Can Easily Search Through Everything
Your private data is being traded and sold all over the internet as we speak. Tons of leaks come out on a...
-

 4.6KIncidents
4.6KIncidentsMagento Marketplace was hacked; the most insecure platform
Data protection experts reported an intrusion that has impacted Adobe Magento Marketplace users, employed to purchase, sell, and download themes and plugins...






