All posts tagged "cybersecurity"
-
 147Articles
147ArticlesUnpatched MS Word Flaw Could Allow Hackers to Infect Your Computer
Cybersecurity researchers have revealed an unpatched logical flaw in Microsoft Office 2016 and older versions that could allow an attacker to embed...
-
 198Articles
198ArticlesIBM Buys “Red Hat” Open-Source Software Company for $34 Billion
It’s been quite a year for the open source platforms. Earlier this year, Microsoft acquired popular code repository hosting service GitHub for...
-
 211Articles
211ArticlesWindows Built-in Antivirus Gets Secure Sandbox Mode – Turn It ON
Microsoft Windows built-in anti-malware tool, Windows Defender, has become the very first antivirus software to have the ability to run inside a...
-

 4.6KData Security
4.6KData SecurityCanada is Imitating EU’s GDPR, New Policy Takes Effect On Nov 2018
Canada has apparently imitated European Union’s GDPR, that is the latest news from the country’s Office of Privacy Commissioner of Canada (OPC)....
-
 189Articles
189ArticlesNew Privilege Escalation Flaw Affects Most Linux Distributions
An Indian security researcher has discovered a highly critical flaw in X.Org Server package that impacts OpenBSD and most Linux distributions,...
-

 535Cryptocurrency
535CryptocurrencyNorth Korea Backed Two Cryptocurrency Scams This Year, Says Report
The North Korean government, as per a new report, has sponsored at least two cryptocurrency scams this year. Recorded Future, the cybersecurity...
-

 631Articles
631ArticlesFacebook Fined £500,000 for Cambridge Analytica Data Scandal
Facebook has finally been slapped with its first fine of £500,000 for allowing political consultancy firm Cambridge Analytica to improperly gather...
-

 291Articles
291ArticlesGoogle Makes 2 Years of Android Security Updates Mandatory for Device Makers
When it comes to security updates, Android is a real mess. Even after Google timely rolls out security patches for its Android...
-

 234Articles
234ArticlesRussian Research Lab Aided the Development of TRITON Industrial Malware
Cybersecurity firm FireEye claims to have discovered evidence that proves the involvement of a Russian-owned research institute in the development of the...
-
 162Articles
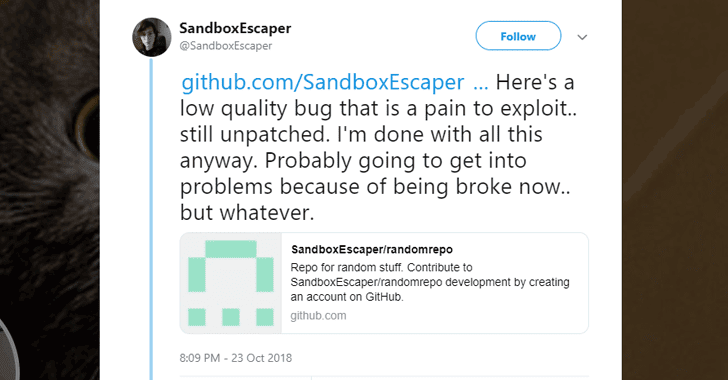
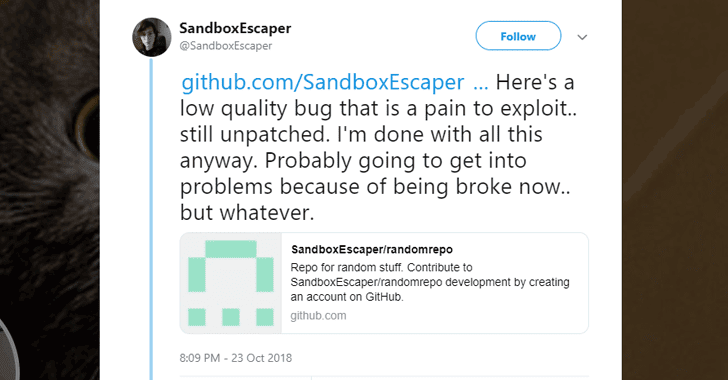
162ArticlesHacker Discloses New Windows Zero-Day Exploit On Twitter
A security researcher with Twitter alias SandboxEscaper—who two months ago publicly dropped a zero-day exploit for Microsoft Windows Task Scheduler—has yesterday released...
-

 223Articles
223ArticlesCritical Code Execution Flaw Found in LIVE555 Streaming Library
Security researchers have discovered a serious code execution vulnerability in the LIVE555 streaming media library—which is being used by popular media players,...
-

 318Infosec
318InfosecCybersecurity in Trading and Forex: What You Need to Know
While cyber attacks occur almost daily in the world, sometimes with catastrophic results, we do not hear about successful attempts of disrupting...
-

 5.1KData Security
5.1KData SecurityPentagon Employee Data Breach, An Eye-Opener
Pentagon, the center of defense of the world’s only superpower: The United States of America embarrassingly admitted that the organization is one...
-

 147News
147NewsSafe Computing Practices for Today’s 24/7 Internet Connected World
Cybersecurity is the responsibility of everyone, as the weakest chain in the link is human-computer operators. Cybercriminals have an easy time to...
-

 242Cyber Crime
242Cyber CrimeStartup Firms at the Age of Growing Cybercrimes
At the turn of the new century, 2000 AD, the dependence of people and companies with technology has been integrated than ever...
-

 174News
174NewsFormjacking in the Nutshell
Due to the diligence of the cybercriminals with their research and development of malware, from time-to-time, new words are introduced in the...
-

 302News
302NewsAspire Health, Another Healthcare Firm as a Phishing Victim
Aspire Health, through its federal court record, has revealed that it was a victim of a nasty phishing attack through email that...
-

 299News
299NewsThe Importance of the IT Team in an Organization
The business of IT comes with its own strength and weaknesses. The job of system administrators is usually only seen with a...
-

 189Cyber Crime
189Cyber CrimeHackers in the Age of Bounty Programs
The popular culture has depicted hackers as evildoers in movies, in TV series and even in the primetime news. However, the commodification...
-

 331Infosec
331InfosecMost Important Cybersecurity Consideration to Secure Your Company’s Integrity
When it comes to cybersecurity then no any business would be able to ignore it! In fact, if we consider the reports...
-

 529Data Security
529Data SecuritySilence, a new group of hackers with alleged links to the cybersecurity industry
Russian-speaking hackers are linked to the theft of 800k USD from European banks At least one of the members of a newly...






