All posts tagged "data security"
-

 2.2KData Breach
2.2KData BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
A new Android trojan called SoumniBot has been detected in the wild targeting users in South Korea by leveraging weaknesses in the...
-

 645Vulnerabilities
645VulnerabilitiesPython’s PyPI Reveals Its Secrets
GitGuardian is famous for its annual State of Secrets Sprawl report. In their 2023 report, they found over 10 million exposed passwords,...
-

 3.3KVulnerabilities
3.3KVulnerabilitiesWebinar: Learn How to Stop Hackers from Exploiting Hidden Identity Weaknesses
We all know passwords and firewalls are important, but what about the invisible threats lurking beneath the surface of your systems? Identity...
-

 2.0KVulnerabilities
2.0KVulnerabilitiesCritical Unpatched Ray AI Platform Vulnerability Exploited for Cryptocurrency Mining
Cybersecurity researchers are warning that threat actors are actively exploiting a “disputed” and unpatched vulnerability in an open-source artificial intelligence (AI) platform...
-

 2.9KData Breach
2.9KData BreachFrom 500 to 5000 Employees – Securing 3rd Party App-Usage in Mid-Market Companies
A company’s lifecycle stage, size, and state have a significant impact on its security needs, policies, and priorities. This is particularly true...
-
 1.2KVulnerabilities
1.2KVulnerabilitiesNew Hugging Face Vulnerability Exposes AI Models to Supply Chain Attacks
Cybersecurity researchers have found that it’s possible to compromise the Hugging Face Safetensors conversion service to ultimately hijack the models submitted by...
-

 791Malware
791MalwareCybercriminals Weaponizing Open-Source SSH-Snake Tool for Network Attacks
A recently open-sourced network mapping tool called SSH-Snake has been repurposed by threat actors to conduct malicious activities. “SSH-Snake is a self-modifying...
-

 2.1KVulnerabilities
2.1KVulnerabilitiesExperts Detail New Flaws in Azure HDInsight Spark, Kafka, and Hadoop Services
Three new security vulnerabilities have been discovered in Azure HDInsight’s Apache Hadoop, Kafka, and Spark services that could be exploited to achieve...
-
 2.8KVulnerabilities
2.8KVulnerabilitiesWhy Public Links Expose Your SaaS Attack Surface
Collaboration is a powerful selling point for SaaS applications. Microsoft, Github, Miro, and others promote the collaborative nature of their software applications...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesNew Terrapin Flaw Could Let Attackers Downgrade SSH Protocol Security
Security researchers from Ruhr University Bochum have discovered a vulnerability in the Secure Shell (SSH) cryptographic network protocol that could allow an...
-
 2.2KData Breach
2.2KData BreachCost of a Data Breach Report 2023: Insights, Mitigators and Best Practices
John Hanley of IBM Security shares 4 key findings from the highly acclaimed annual Cost of a Data Breach Report 2023 What...
-

 4.1KVulnerabilities
4.1KVulnerabilitiesHackers Exploited ColdFusion Vulnerability to Breach Federal Agency Servers
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) warned of active exploitation of a high-severity Adobe ColdFusion vulnerability by unidentified threat actors...
-
 2.8KData Breach
2.8KData BreachGenerative AI Security: Preventing Microsoft Copilot Data Exposure
Microsoft Copilot has been called one of the most powerful productivity tools on the planet. Copilot is an AI assistant that lives...
-

 4.7KMalware
4.7KMalwareQakbot Takedown Aftermath: Mitigations and Protecting Against Future Threats
The U.S. Department of Justice (DOJ) and the FBI recently collaborated in a multinational operation to dismantle the notorious Qakbot malware and...
-
 873Data Breach
873Data BreachThis Free Solution Provides Essential Third-Party Risk Management for SaaS
Wing Security recently announced that basic third-party risk assessment is now available as a free product. But it raises the questions of...
-

 1.2KVulnerabilities
1.2KVulnerabilitiesTransform Your Data Security Posture – Learn from SoFi’s DSPM Success
As cloud technology evolves, so does the challenge of securing sensitive data. In a world where data duplication and sprawl are common,...
-
 4.8KData Breach
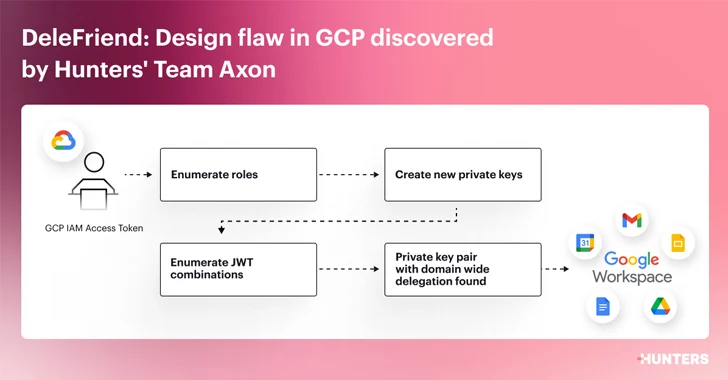
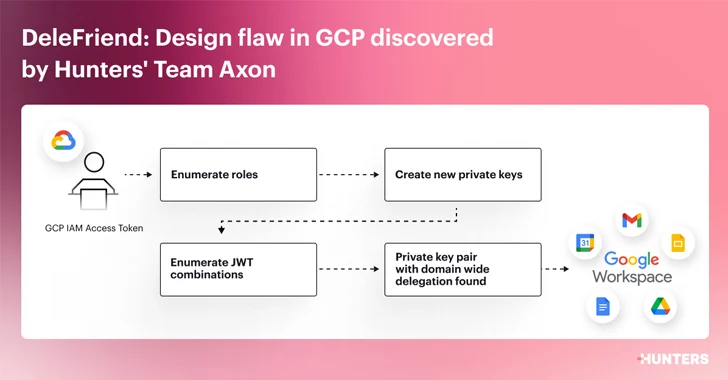
4.8KData BreachDesign Flaw in Google Workspace Could Let Attackers Gain Unauthorized Access
Cybersecurity researchers have detailed a “severe design flaw” in Google Workspace’s domain-wide delegation (DWD) feature that could be exploited by threat actors...
-

 4.4KVulnerabilities
4.4KVulnerabilitiesQNAP Releases Patch for 2 Critical Flaws Threatening Your NAS Devices
QNAP has released security updates to address two critical security flaws impacting its operating system that could result in arbitrary code execution....
-

 2.3KData Breach
2.3KData BreachKinsing Actors Exploiting Recent Linux Flaw to Breach Cloud Environments
The threat actors linked to Kinsing have been observed attempting to exploit the recently disclosed Linux privilege escalation flaw called Looney Tunables...
-
 2.0KMalware
2.0KMalwareViperSoftX InfoStealer Adopts Sophisticated Techniques to Avoid Detection
A significant number of victims in the consumer and enterprise sectors located across Australia, Japan, the U.S., and India have been affected...
-

 3.0KData Breach
3.0KData BreachProtect Your Company: Ransomware Prevention Made Easy
Every year hundreds of millions of malware attacks occur worldwide, and every year businesses deal with the impact of viruses, worms, keyloggers,...






