All posts tagged "Data"
-

 2.1KData Security
2.1KData SecurityHacker leaks 150 million user records from Iranian Raychat app
The hacker behind the data leak claims they downloaded the Raychat app data when the company exposed its entire database online between...
-

 713Cyber Crime
713Cyber CrimeLeaky database exposes fake Amazon product reviews scam
The database contained 7GB worth of data including fake Amazon product reviews and PayPal email addresses of scammers among other sensitive data. Whoever...
-

 4.2KNews
4.2KNewsShinyHunters leak database of Indian wedding portal WedMeGood
The leaked WedMeGood database contains 41.5 GB worth of data which is another massive data leak from ShinyHunters. ShinyHunters, the notorious hacker...
-

 1.6KHow To
1.6KHow ToA Comprehensive Data Recovery Solution
Are you looking for your important file which accidentally got deleted while cleaning out the garbage from your device? Did you lose...
-
 5.3KHow To
5.3KHow ToHow to repair suspect database in SQL Server
Programs work with databases, and if the database crashes essential information can be lost and this will be disastrous to the user....
-
 4.8KHow To
4.8KHow ToHow to Use Excel to Scrape a Website
If you need to extract data from a page or website there are two ways to go about it: you can do...
-
 3.2KGeek
3.2KGeekFacebook data of 500M+ users from 106 countries leaked online
The data was leaked earlier today on an infamous hacker forum without users’ Facebook accounts passwords. For the last couple of years,...
-

 1.5KInformation Gathering
1.5KInformation GatheringToken-Hunter – Collect OSINT For GitLab Groups And Members
Collect OSINT for GitLab groups and members and search the group and group members’ snippets, issues, and issue discussions for sensitive...
-
 4.7KSurveillance
4.7KSurveillanceStudy: Android sends more data to Google than iOS to Apple
Research reveals startling new findings on Android data collection and how it sends 2-times more data to Google than iOS to Apple...
-
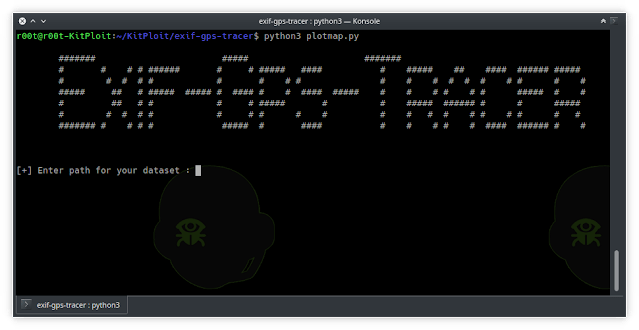
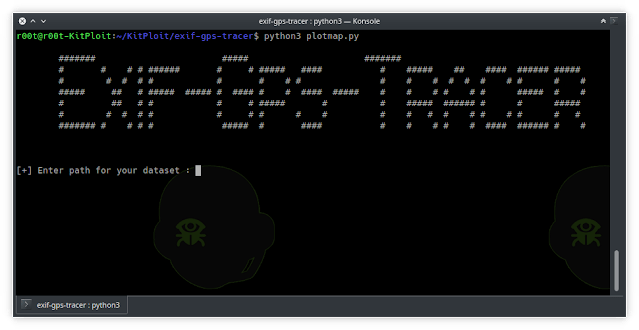 4.1KInformation Gathering
4.1KInformation GatheringExif-Gps-Tracer – Parse GeoLocation Data From Images To A dataset
A python script which allows you to parse GeoLocation data from your Image files stored in a dataset.It also produces output...
-

 4.6KInformation Gathering
4.6KInformation GatheringSarenka – OSINT Tool – Data From Services Like Shodan, Censys Etc
SARENKA is an Open Source Intelligence (OSINT) tool which helps you obtaining and understanding Attack Surface. The main goal is to...
-

 905Information Gathering
905Information GatheringOblivion – Data Leak Checker And OSINT Tool
Oblivion is a tool focused in real time monitoring of new data leaks, notifying if the credentials of the user has...
-

 3.9KNews
3.9KNewsRussian Cops Are Selling Surveillance System Data To Hackers: Report
Moscow, the capital of Russia, has 175,000 CCTV cameras for surveillance purposes. Out of these, over 4,000 cameras are installed in crowded...
-

 5.1KSurveillance
5.1KSurveillanceSMS and personal data of millions of Americans leaked online
The IT security researchers at vpnMentor have discovered a trove of insecure data hosting on a company based in the United...
-

 4.1KIncidents
4.1KIncidents4 million credit cards used in restaurants for sale in hacking forums
A hacker group has released a new database of stolen payment cards on Joker’s Stash, a popular hacking forum. According to web...
-

 4.6KIncidents
4.6KIncidentsMagento Marketplace was hacked; the most insecure platform
Data protection experts reported an intrusion that has impacted Adobe Magento Marketplace users, employed to purchase, sell, and download themes and plugins...
-

 4.4KNews
4.4KNewsDatabase with 1.2 billion people’s data leaked online without password
The database was available for anyone to access without a password. Recently on October 16, 2019, a team of two dark web...
-
 2.6KData Security
2.6KData SecuritySomeone leaked location data of users from a neo-nazi website
Over the past few months, we’ve come across data breaches that are bad for anyone but the bad guys themselves. But just...
-
Security Tools
Tylium – Data for Intrusion Detection, Security Analytics and Threat Hunting
These files contain configuration for producing EDR (endpoint detection and response) data in addition to standard system logs. These configurations enable...
-
 431Information Gathering
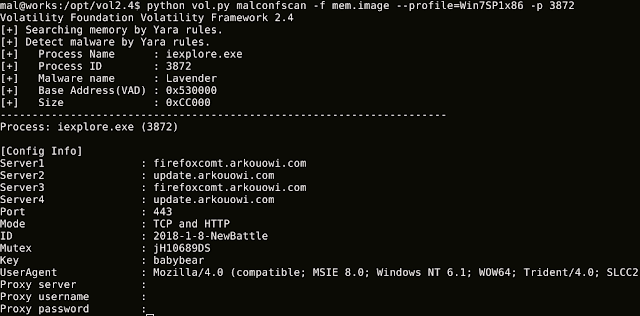
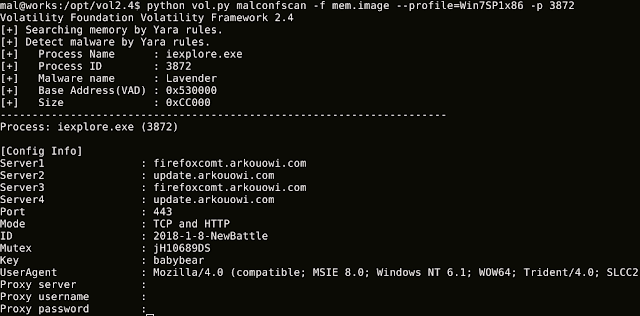
431Information GatheringMalConfScan – Volatility Plugin that Extracts Data Of Malware
MalConfScan is a Volatility plugin extracts configuration data of known malware. Volatility is an open-source memory forensics framework for incident response...
-
 419How To
419How ToAll You Need To Know For External Hard Drive Recovery
External hard drives are one of the convenient forms of data storage. You could store GBs or even terabytes of data and...






