All posts tagged "database"
-
 326Information Gathering
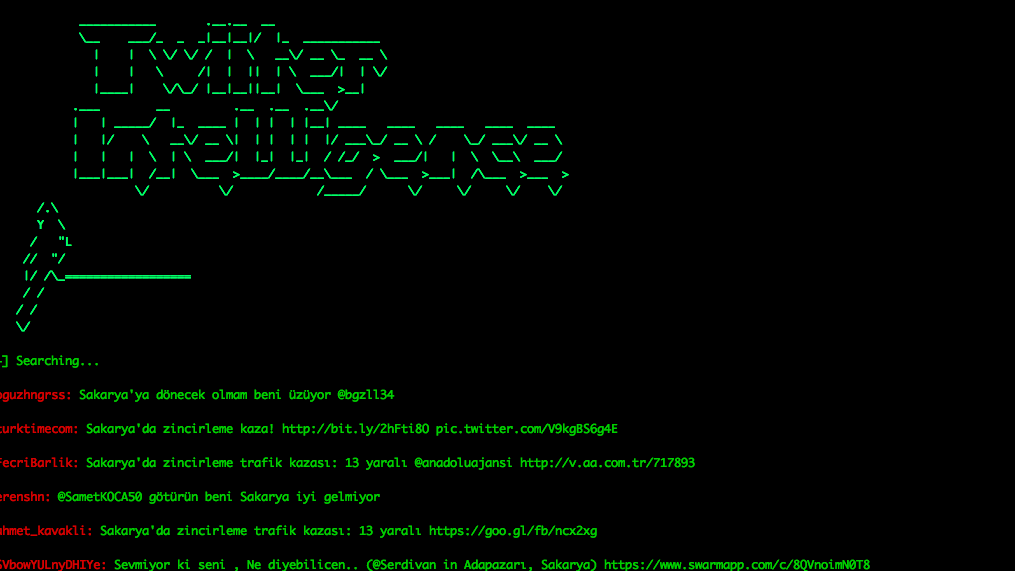
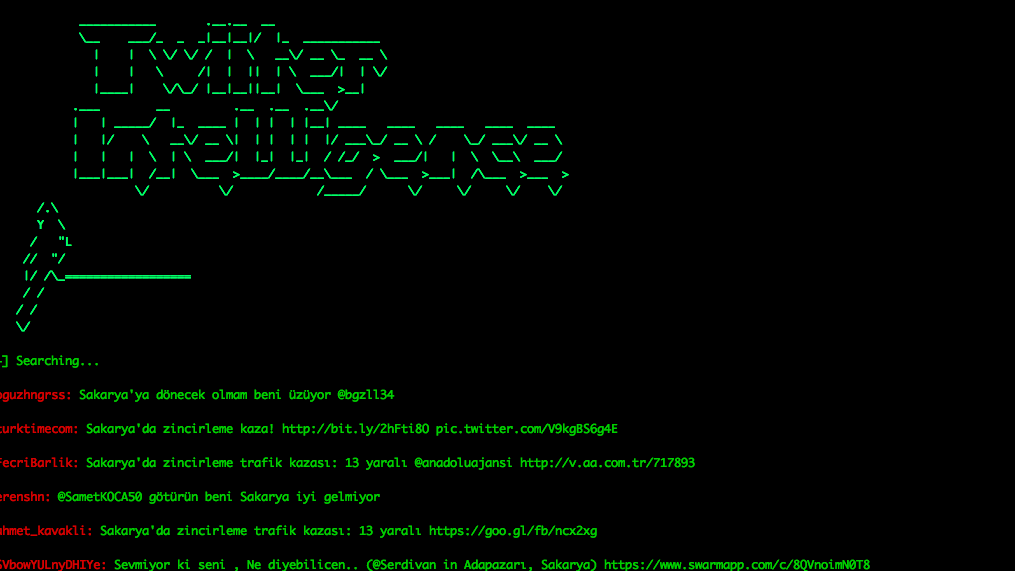
326Information GatheringTwitter-Intelligence – Twitter Intelligence OSINT Project Performs Tracking And Analysis Of The Twitter
A project written in Python to twitter tracking and analysis without using Twitter API. Prerequisites This project is a Python 3.x application....
-
 246Exploitation Tools
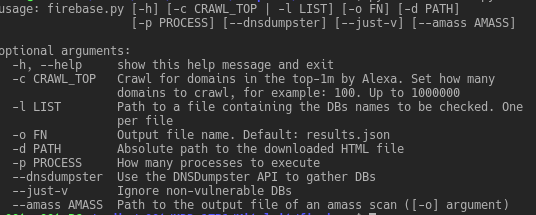
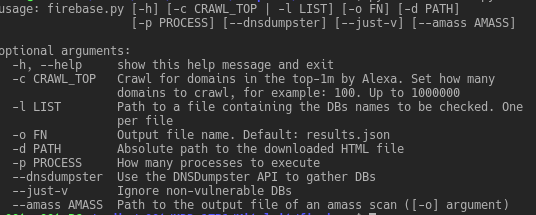
246Exploitation ToolsFirebase Exploiting Tool – Exploiting Misconfigured Firebase Databases
Exploiting vulnerable/misconfigured Firebase databases Prerequisites Non-standard python modules: dnsdumpster bs4 requests Installation If the following commands run successfully, you are ready to...
-
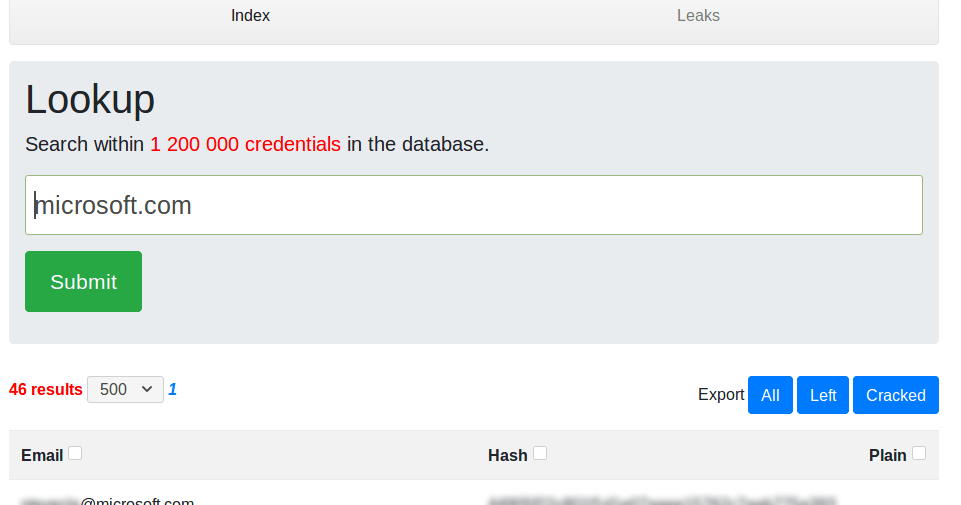
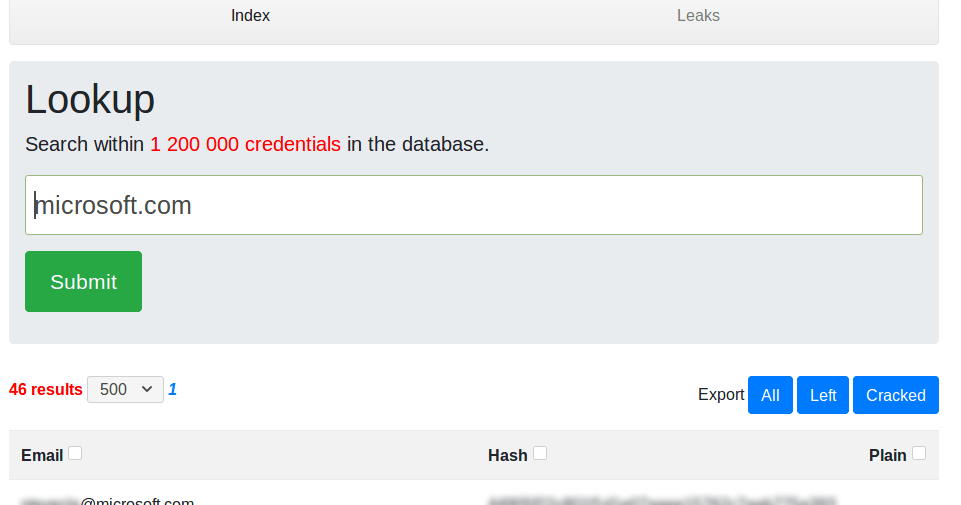 272Password Attacks
272Password AttacksLeakScraper – An Efficient Set Of Tools To Process And Visualize Huge Text Files Containing Credentials
LeakScraper is an efficient set of tools to process and visualize huge text files containing credentials. These tools are designed to help...
-
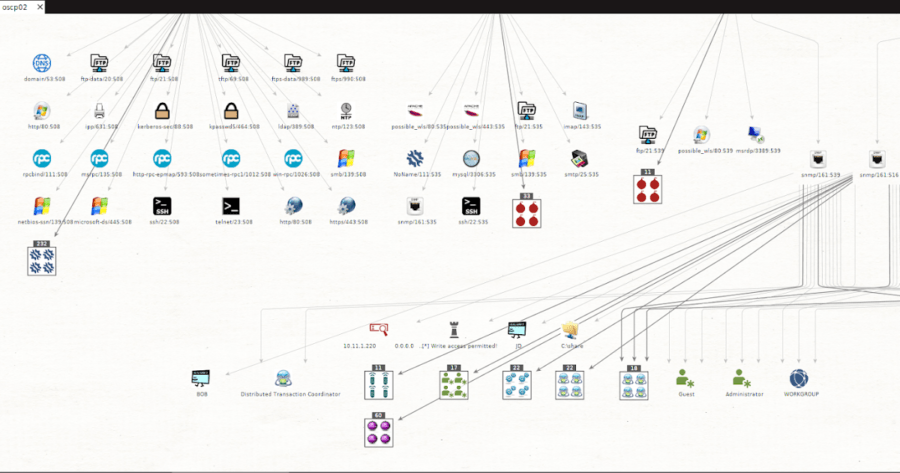
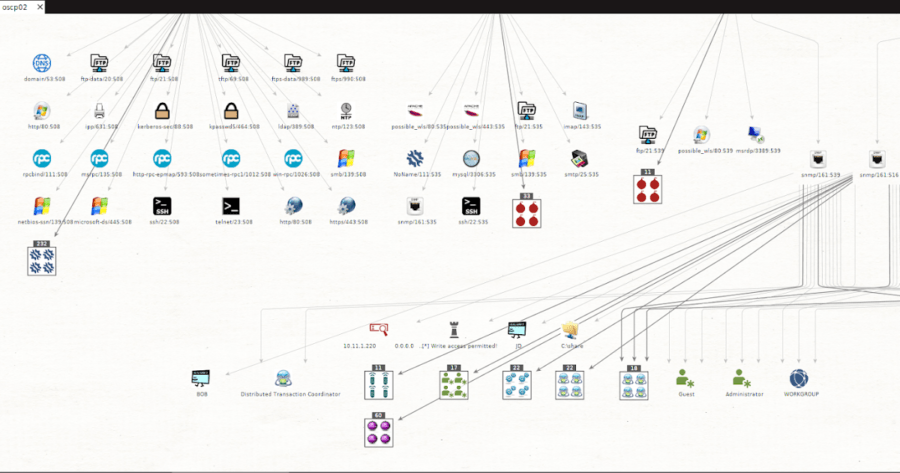 270Information Gathering
270Information GatheringMsploitego – Pentesting Suite For Maltego Based On Data In A Metasploit Database
msploitego leverages the data gathered in a Metasploit database by enumerating and creating specific entities for services. Services like samba, smtp, snmp,...
-

 187Geek
187GeekApple Open Sources FoundationDB, Releases Code On GitHub
Back in 2015, Apple bought FoundationDB, a NoSQL database company. It created a distributed database of the same name designed to deal...
-

 261Hacked
261HackedHow “Hacker Search Engine” Shodan Caught Leakage of 750MB Worth Of Server Passwords
Remember Memcached servers? Now, we have another case of servers exposed online and fulfilling evil intentions of the hackers. This time, thousands...
-
 292Information Gathering
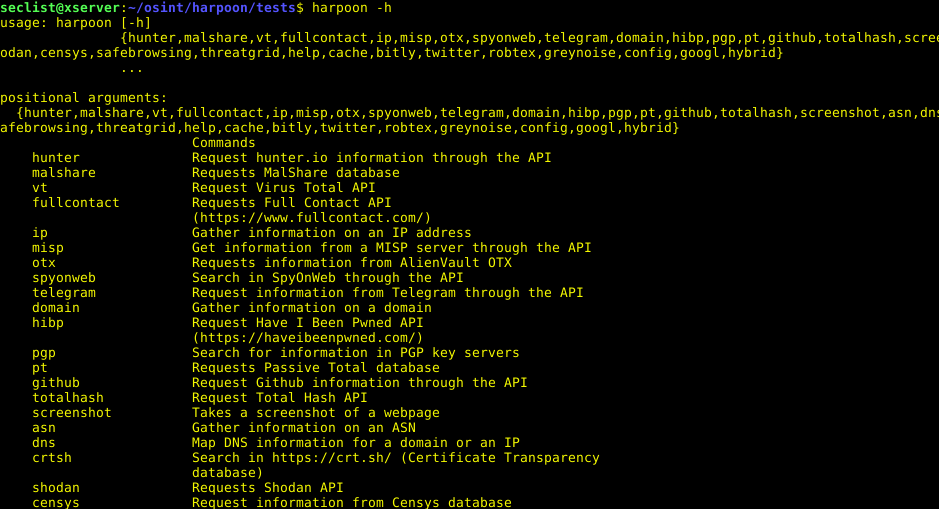
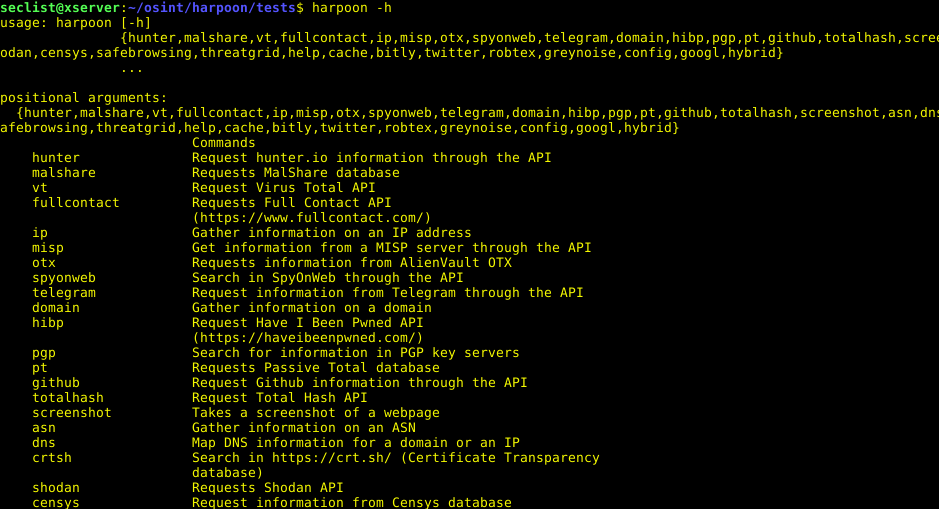
292Information GatheringHarpoon – CLI Tool For Open Source And Threat Intelligence
OSINT tool, CLI Tool For Open Source And Threat Intelligence Install You can simply pip install the tool: pip3 install git+http://[email protected]/Te-k/harpoon --process-dependency-links Optionally...
-
 252Exploitation Tools
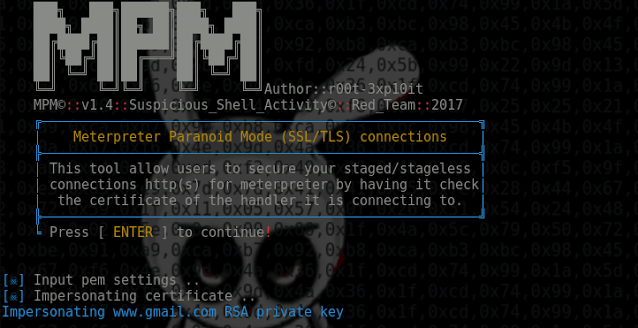
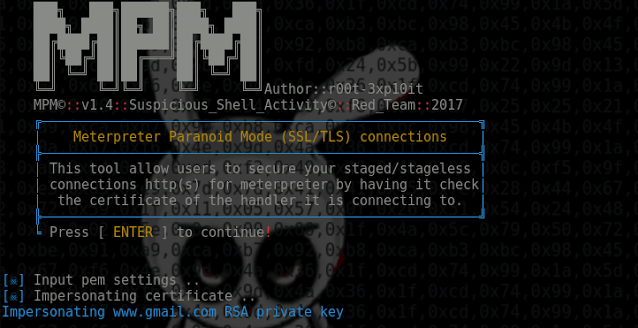
252Exploitation ToolsMeterpreter Paranoid Mode – Meterpreter over SSL/TLS connections
Meterpreter_Paranoid_Mode.sh allows users to secure your staged/stageless connection for Meterpreter by having it check the certificate of the handler it is connecting...
-
 238Exploitation Tools
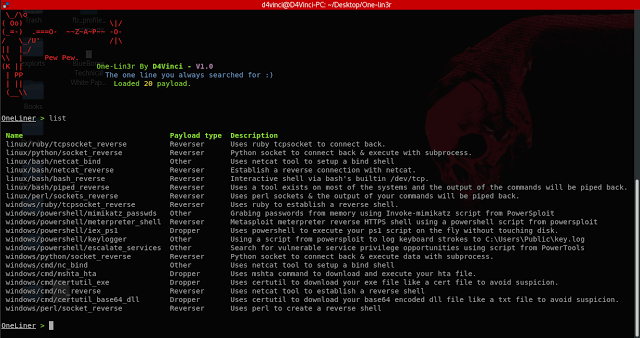
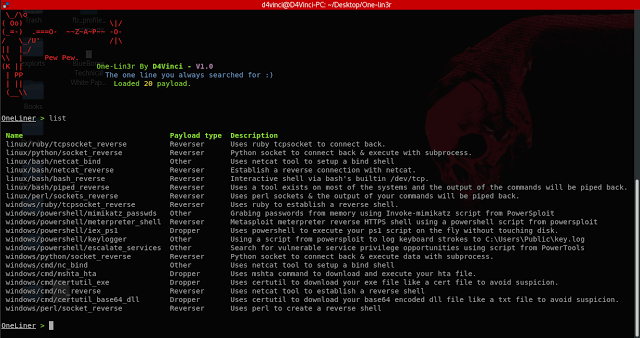
238Exploitation ToolsOne-Lin3r – Gives you One-Liners that Aids in Penetration Testing Operations
One-Lin3r is simple and light-weight framework inspired by the web-delivery module in Metasploit. It consists of various one-liners that aids in penetration...
-

 231System Administration
231System AdministrationACE – The Automated Collection and Enrichment Platform
The Automated Collection and Enrichment (ACE) platform is a suite of tools for threat hunters to collect data from many endpoints in...
-
 194Articles
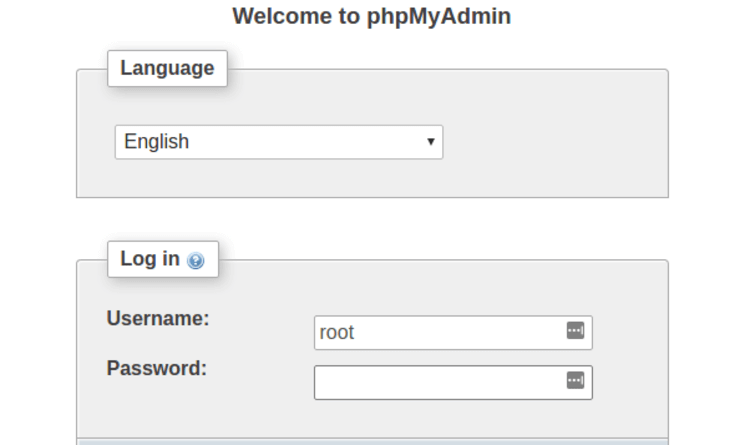
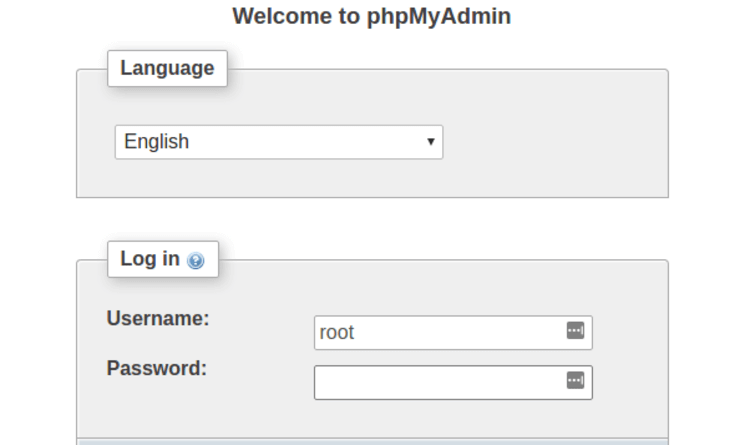
194ArticlesA Bug in phpMyAdmin lets Hackers Delete Database Tables and Records
Amongst the most common and in demand applications for MySQL database management is the phpMyAdmin, which became vulnerable, when a critical flaw...
-

 241System Administration
241System AdministrationPowerUpSQL – A PowerShell Toolkit for Attacking SQL Server
The PowerUpSQL module includes functions that support SQL Server discovery, auditing for common weak configurations, and privilege escalation on scale. It is...
-
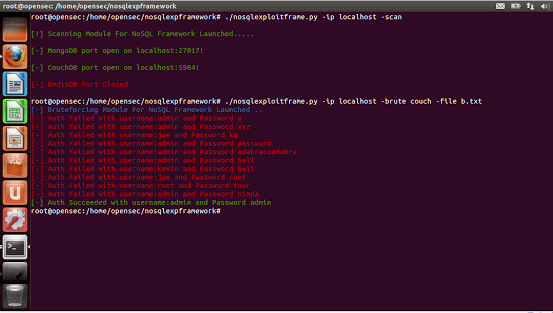
 215Exploitation Tools
215Exploitation ToolsNoSQL Exploitation Framework 2.0 – A Framework For NoSQL Scanning and Exploitation
A FrameWork For NoSQL Scanning and Exploitation Framework Authored By Francis Alexander. Added Features: First Ever Tool With Added Support For Mongo,Couch,Redis,H-Base,Cassandra...
-

 303News
303NewsHackers steal 19M California voter records after holding database for ransom
In late 2015, a security researcher found voter registration records of 191 million US voters on the Internet. Months later, hackers were...
-
 256Cyber Crime
256Cyber CrimeData Breach Index Website “Leakbase” Shut Down
On December 2nd, Leakbase.pw, a data breach index website announced it has closed down the service effective immediately. In a tweet, the...
-
 223Vulnerability Analysis
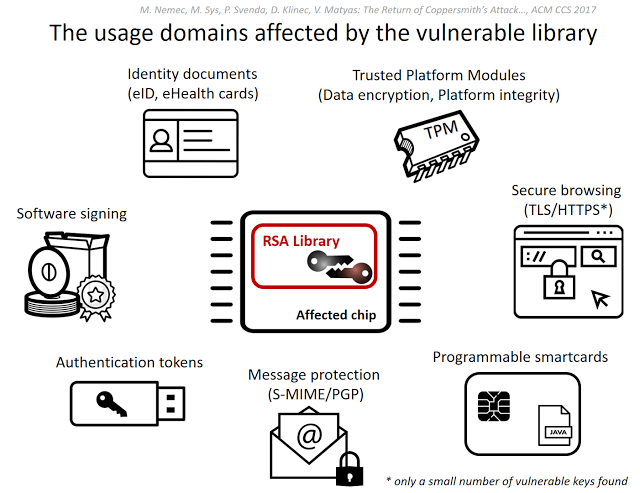
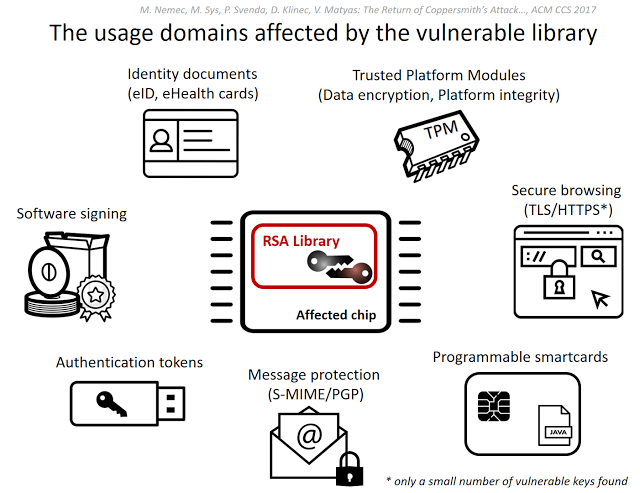
223Vulnerability AnalysisROC – Infineon RSA Vulnerability
This tool is related to ACM CCS 2017 conference paper #124 Return of the Coppersmith’s Attack: Practical Factorization of Widely Used RSA...
-

 305Data Security
305Data SecurityFive tips for keeping your database secure
When we give privacy or security advice, we usually talk about strong passwords, backing up your data, using security applications, keeping systems...
-
 218Vulnerability Analysis
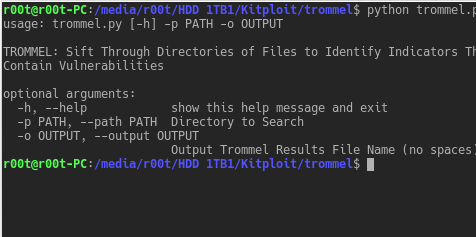
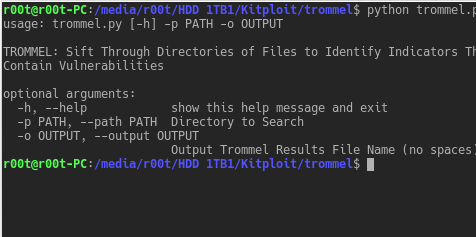
218Vulnerability AnalysisTROMMEL – Sift Through Directories of Files to Identify Indicators That May Contain Vulnerabilities
TROMMEL sifts through directories of files to identify indicators that may contain vulnerabilities. TROMMEL identifies the following indicators related to: Secure Shell...
-

 274News
274NewsOver Half a Million Vehicle Records from SVR Tracking Leaked Online
Over Half a Million Vehicle Records from SVR Tracking Leaked Online – Thanks to Amazon Web Services Bucket. SVR Tracking, a renowned...
-

 339News
339NewsMassive Viacom Data Exposed Through Amazon Web Services
Database on Amazon Web Services Containing Sensitive Data of Viacom Is Publicly Available. Amazon Web Services S3 is in the news for...
-

 277News
277NewsAlaska Voter Database Exposed Online
IT security researchers at Kromtech Security Center discovered an unprotected database exposed online due to misconfiguration of CouchDB containing nearly 600,000 records belonging to Alaskan...






