All posts tagged "Digital Forensics"
-

 570Vulnerabilities
570VulnerabilitiesNew Internet Explorer zero-day vulnerability would allow local file theft
Internet Explorer is not exactly the most popular search engine, and this new security incident definitively won’t help. According to cyber forensics...
-

 391Incidents
391IncidentsMicrosoft was hacked – Outlook and employees’ accounts have been hacked
Microsoft has revealed that a group of unknown hackers has perpetrated a data breach in some of the company’s systems; according to...
-

 297Incidents
297IncidentsRansomware attack cripples the South Carolina, U.S. systems
A ransomware attack forced the shutdown of all the computer operations of the city of Greenville, South Carolina, According to the cyber...
-
 467Vulnerabilities
467VulnerabilitiesPulse Secure, Cisco, F5 Networks and Palo Alto Networks business VPN services present security vulnerabilities, says Homeland Security
According to cyber forensics course specialists from the International Institute of Cyber Security (IICS) the services of virtual private networks (VPN) provided...
-
 213Vulnerabilities
213VulnerabilitiesJuniper switch vulnerability exposes login credentials
According to cyber forensics course specialists from the International Institute of Cyber Security (IICS), Juniper Networks has launched an unexpected update after...
-
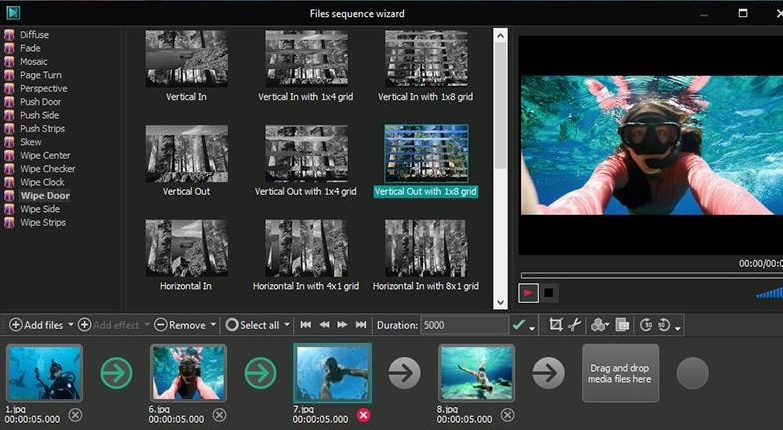
 345Malware
345MalwareThe webpage of VSDC, popular video editing software is hacked, users get infected with Trojan
The official website of VSDC, one of the most used free video edition and conversion services (with almost 1.5 million visitors per...
-

 314Data Security
314Data SecurityTelegram TON Blockchain Network, a Tor’s alternative, will be launched soon
Telegram instant messaging service will launch a private beta test of your blockchain, Telegram Open Network (TON), reported cyber forensics course experts...
-
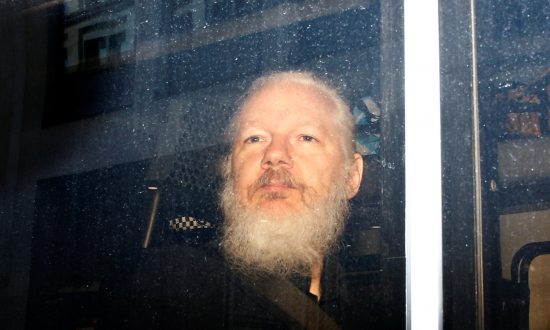
 436Incidents
436IncidentsWhat will happen with WikiLeaks? Julian Assange is arrested by British authorities
Cyber forensics course specialists reported that a few days ago Julian Assange was expelled from the Embassy of Ecuador in London this...
-

 267Pentest Linux Distributions
267Pentest Linux DistributionsCAINE 10.0 – GNU/Linux Live Distribution For Digital Forensics Project, Windows Side Forensics And Incident Response
CAINE (Computer Aided INvestigative Environment) is an Italian GNU/Linux live distribution created as a Digital Forensics project. Currently, the project manager is Nanni Bassetti...
-

 300Data Security
300Data SecuritySteam error allowed people to download any game for free
The person who reported the bug was rewarded with $20k USD A cybersecurity researcher discovered and reported a bug on Steam that allowed people...
-
 250Vulnerabilities
250VulnerabilitiesA jQuery plugin has been exploitable for 8 years
Different ways of exploiting the flaw have been widely spread too Out of the thousands of plugins for the jQuery framework, one of the...
-

 248Data Security
248Data SecurityHow to become an expert in digital forensics
A review of the interesting work of the experts in digital forensics What exactly does a professional in digital forensics do? In general, experts in digital forensics are computer detectives that...
-

 145Vulnerabilities
145VulnerabilitiesExperts recommend avoiding single step logins
It’s more secure to use unique passwords for each service and password managers for each app we use Single logins are a...
-
Forensics Tools
srum-dump – A Forensics Tool to Convert the Data in the Windows srum
srum-dump This program will create an excel spreadsheet containing forensics artifacts contained the SRUM (System Resource Utilization Manager) database. The program can...
-

 99Data Security
99Data SecurityHack Like a Pro: Digital Forensics for the Aspiring Hacker
In this tutorial, we will explore where and what the forensic investigator can find information about the activities of the suspect in...






