All posts tagged "DNS server"
-
 3.9KDDOS
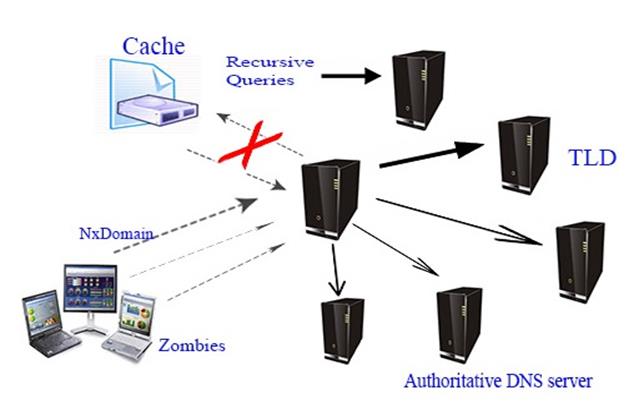
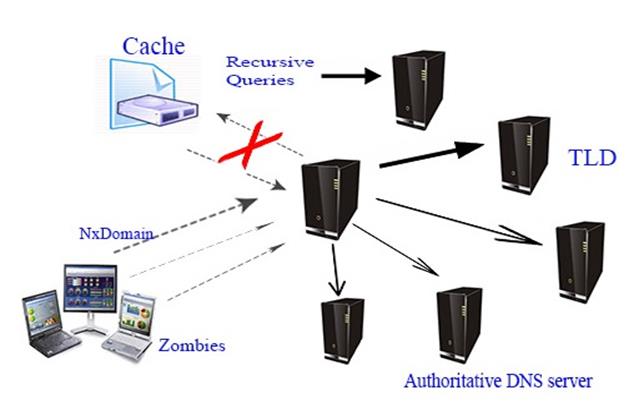
3.9KDDOSHow Companies Fight DDoS Attacks?
The threat of DDoS (Denial-of-Service) attacks that send massive processing demands from multiple Internet-connected devices (be it a PC, a smartphone, a...
-

 314News
314NewsHacker Group Has Been Hacking DNS Traffic on D-Link Routers
Earlier, we had service provider playing tricks with your DNS traffic. Then, it was difficult for us to fathom unless you are...
-
 281Data Security
281Data SecurityDifferent ways of Subdomain enumeration
An information security professional wrote a list of the most popular methods, the expert tried to make a list of some tools and online...
-
 274Network Tools
274Network Toolsmitm6 – Compromising IPv4 Networks via IPv6
mitm6 is a pentesting tool that exploits the default configuration of Windows to take over the default DNS server. It does this...
-

 205Vulnerabilities
205VulnerabilitiesA Bug Has No Name: Multiple Heap Buffer Overflows In the Windows DNS Client
CVE-2017-11779 fixed by Microsoft in October of 2017, covers multiple memory corruption vulnerabilities in the Windows DNS client. The issues affect computers running Windows...
-
 190Vulnerabilities
190VulnerabilitiesA critical flaw allows hacking Linux machines with just a malicious DNS Response
A remote attacker can trigger the buffer overflow vulnerability to execute malicious code on affected Linux systems with just a malicious DNS response....
-
 240Vulnerabilities
240VulnerabilitiesDNS attacks: How they try to direct you to fake pages
DNS servers are essential to the normal functioning of the internet as we know and love it, but they tend to go unnoticed by...
-

 290Hacked
290HackedNorth Korea’s Internet Is Exposed And It Has Only 28 Websites
Short Bytes: A GitHub user has uploaded the list of domains that exist on North Korea internet. His TLDR project fetched DNS...
-

 363How To
363How ToWhat is DNS (Domain Name System) and How it Works ?
What is the definition of DNS? DNS, which stands for Domain Name System, is used as the medium to translate domain names...






