All posts tagged "DNS"
-
 269Vulnerability Analysis
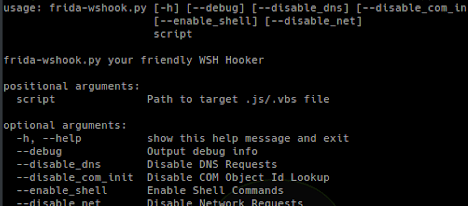
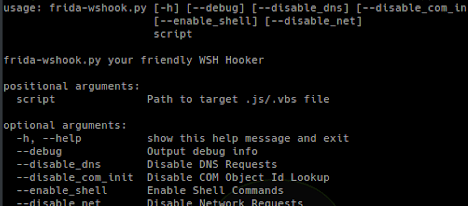
269Vulnerability AnalysisFrida-Wshook – Script Analysis Tool Based On Frida.re
frida-wshook is an analysis and instrumentation tool which uses frida.re to hook common functions often used by malicious script files which are...
-
 276News
276NewsWhat Do We Need to Know About the 2018 Global DNS Threat Report?
Just like the healthcare industry, the financial market players are also a profitable target of cybercriminal elements. The Global DNS Threat Report...
-

 385Data Security
385Data SecurityDon’t ever use a VPN without paying attention to these five things
Ryan Lin was just recently sentenced to 17 years in prison. He was sentenced for committing a range of crimes including cyberstalking,...
-

 366News
366NewsNew GhostDNS, DNS Changer Botnet Hijacked Over 1,00,000 Routers
Chinese researchers have discovered cyber widely spread the GhostDNS malicious campaign that has captured more than 100,000 home routers and changed their...
-

 393Data Security
393Data SecurityMost Threatening DNS Security Risks And How To Avoid Them
The DNS or Domain Name System is one of the most necessary components for the internet functionality. Most often, the internet businesses...
-
 288Data Security
288Data SecurityMeet GhostDNS: The dangerous malware behind IoT botnet targeting banks
Security researchers at NetLab, a sub-division of the Chinese cybersecurity firm Qihoo 360, have discovered a new, wide-scale, and very active malware...
-

 363Data Security
363Data SecurityHackers can intercept and manipulate DNS queries, researchers warn
DNS Queries Intercepted Due to Bogus DNS Traffic Protection Standards. Would you believe that a majority of the DNS queries that are...
-

 409Data Security
409Data SecurityDNS rebinding attack puts half a billion IoT devices at risk
Armis, an Internet of Things (IoT) security vendor and cyber-security firm, reports that about half a billion smart devices being used around...
-
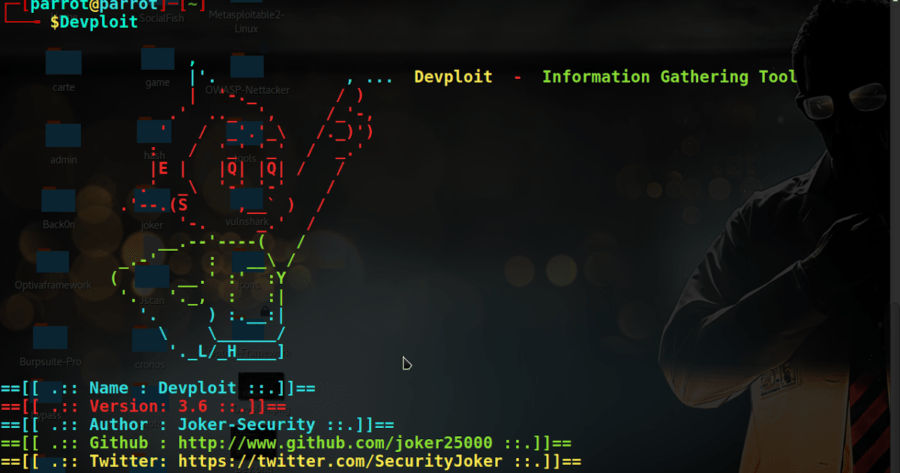
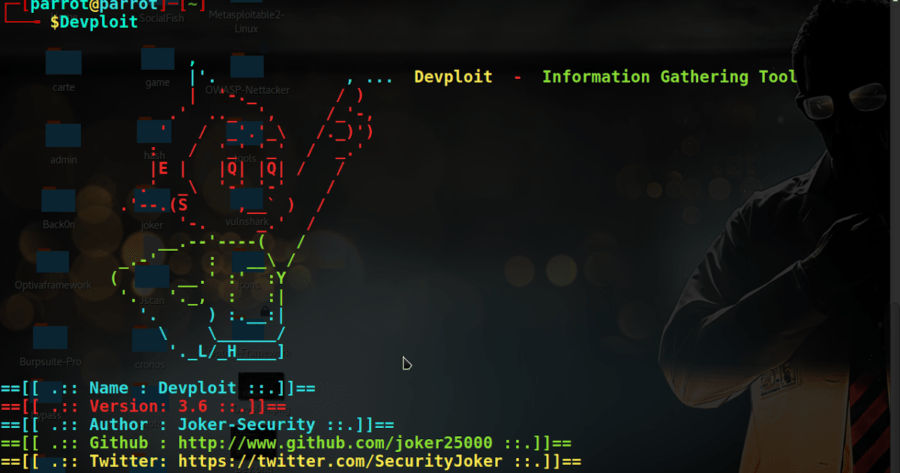 218Information Gathering
218Information GatheringDevploit v3.6 – Information Gathering Tool
Devploit is a simple python script to Information Gathering. Download: git clone https://github.com/joker25000/Devploit How to use: cd Devploit chmod +x install ./install...
-
 315Network Tools
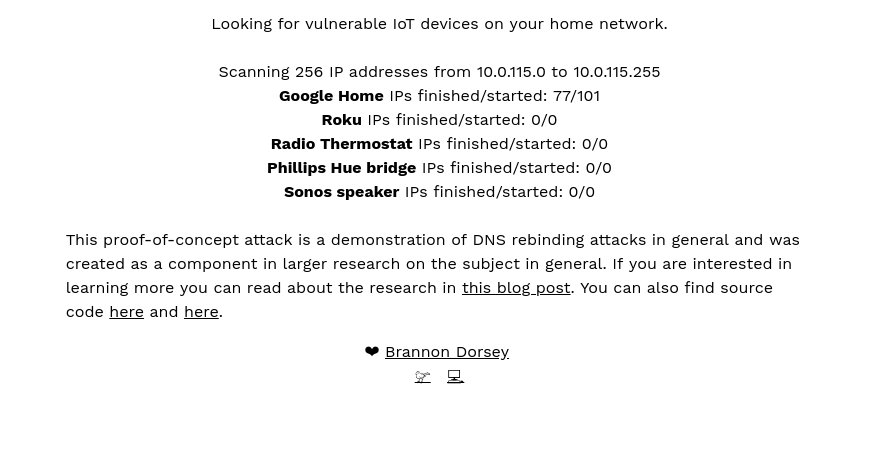
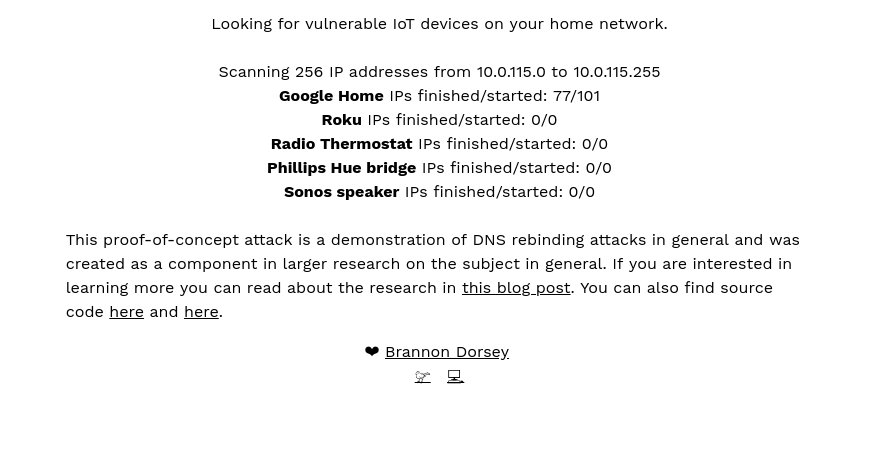
315Network ToolsDNS Rebind Toolkit – A Front-End JavaScript Toolkit For Creating DNS Rebinding Attacks
DNS Rebind Toolkit is a frontend JavaScript framework for developing DNS Rebinding exploits against vulnerable hosts and services on a...
-

 361Data Security
361Data SecurityMultilingual malware hits Android devices for phishing & cryptomining
Roaming Mantis malware also targets iOS devices for phishing attacks. ‘Roaming Mantis uses DNS hijacking to infect Android smartphones’ was the title...
-

 394News
394NewsPopular Chrome VPN extensions are leaking your DNS data
Last month, HackRead reported how tons of popular VPN (Virtual Private Network) software were leaking real IP addresses of users through WebRTC leak along...
-
 245Information Gathering
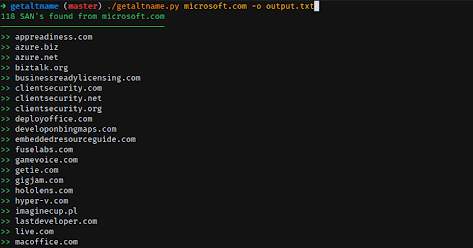
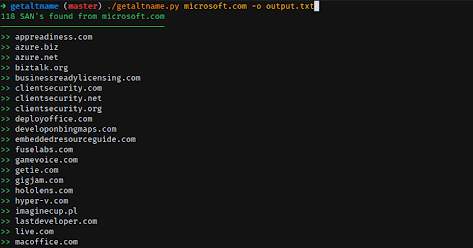
245Information GatheringGetAltName – Get Subject Alt Name From SSL Certificates
GetAltName it’s a little script that can extract Subject Alt Names for SSL Certificates directly from HTTPS web sites which can provide...
-
 381Information Gathering
381Information GatheringScanless – Online Port Scan Scraper – Kali Linux 2018.1
Scanless is a command-line utility for using websites that can perform port scans on your behalf. Useful for early stages of a...
-

 382News
382NewsAPT15 Hackers Hit UK Govt Contractor to Steal Military Technology Secrets
The APT15 hacking group has always been associated with Chinese intelligence and it has been part of quite a few, infamous hacking...
-

 344News
344NewsNew macOS malware hijacks DNS settings and takes screenshots
The general perception about Apple devices is that they are protected from malware and other hacking attacks. But since hackers are getting...
-

 293News
293NewsBlackWallet hacked: Hackers replace DNS server, steal $400k in Stellar
As the price of Bitcoin and other cryptocurrencies is surging, the cybercriminal community is exploring the opportunity to steal user funds as...
-

 349Data Security
349Data SecurityNew BitTorrent Flaw Puts Linux & Windows devices at risk of hacking
Tavis Ormandy, an IT security researcher at Google’s Project Zero has identified a critical flaw in Transmission BitTorrent app that if exploited lets...
-
 274Network Tools
274Network Toolsmitm6 – Compromising IPv4 Networks via IPv6
mitm6 is a pentesting tool that exploits the default configuration of Windows to take over the default DNS server. It does this...
-

 245Network Tools
245Network ToolsDNSCAP – DNS Traffic Capture
dnscap is a network capture utility designed specifically for DNS traffic. It produces binary data in pcap(3) and other format. This utility is similar to tcpdump(1),...
-

 331Post Exploitation
331Post ExploitationDNSExfiltrator – Data Exfiltration over DNS Request Covert Channel
DNSExfiltrator allows for transfering (exfiltrate) a file over a DNS request covert channel. This is basically a data leak testing tool allowing...






