All posts tagged "DOS"
-

 432Vulnerabilities
432Vulnerabilities18 Vulnerabilities that Affected Cisco Software’s Let Hackers Perform DOS, RCE to Gain Unauthorized System Access
Cisco released new security updates for multiple software products such as Cisco ASA, FMC, and FTD Software that affects 18 vulnerabilities in...
-
 447Mobile Security
447Mobile Security9 Android Zero-day Vulnerabilities Affects Billions of Android Devices – Hackers Perform DOS, RCE, Make, Deny & Spoof Calls
Exclusive research found 9 critical system-level Android VoIP Zero-day vulnerabilities that allow attackers to perform malicious operations, including denying voice calls, caller...
-

 352Geek
352GeekVulnerability in Zoom video conference app lets Mac’s camera hijacking
The vulnerability in the Zoom video conference app lets attackers hijack Mac’s camera by merely using malicious websites. The Zoom video conference...
-

 359Data Security
359Data SecurityThe Future of Wi-Fi Security: Assessing Vulnerabilities in WPA3
A new study by researchers Matty Vanhoef and Eyal Ronen revealed five vulnerabilities – collectively named ‘Dragonblood’ – in the WPA3 Wi-Fi...
-
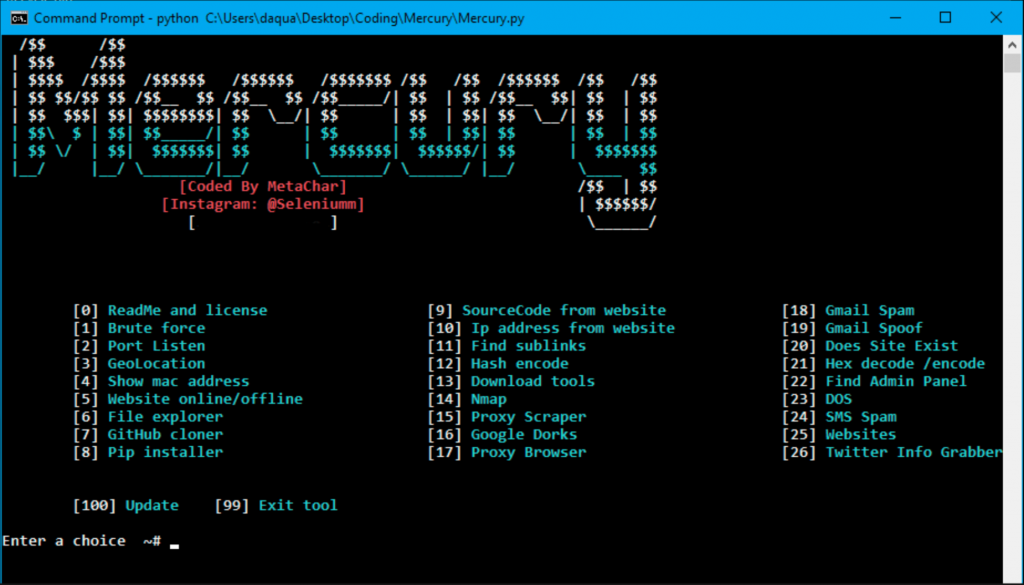
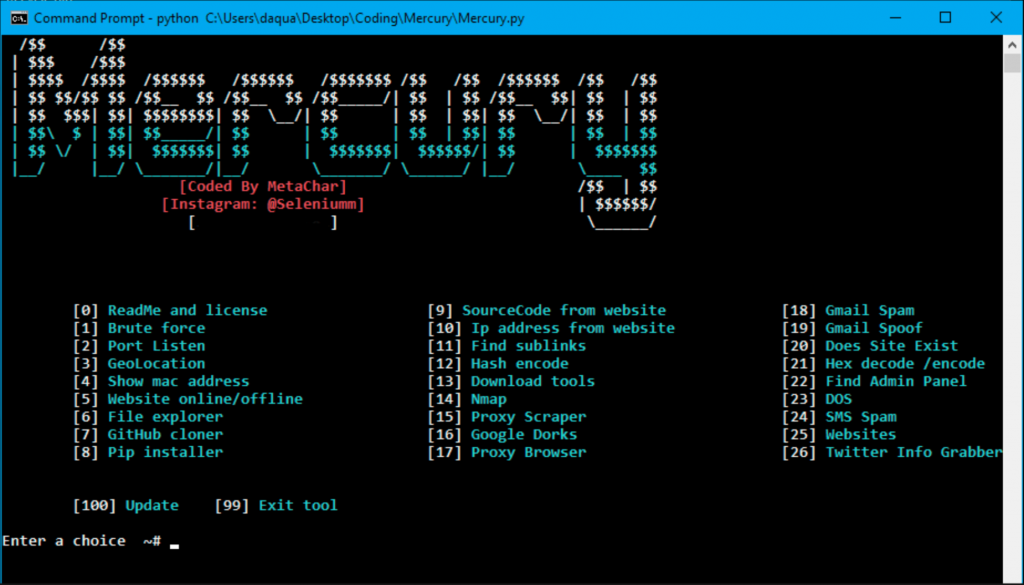 332Tutorials
332TutorialsHack any website with All in One Tool
Internet is the hub of web applications. Many past developers has made numerous web applications to use internet more effectively. Internet has...
-

 330Cyber Crime
330Cyber CrimeMan who conducted DDoS attacks on Sony, Xbox & EA pleads guilty
Austin Thompson, a 23-year-old man from Utah has pleaded guilty to conducting DDoS attacks on gaming giants between 2013 to 2014. Among...
-
 345Man-In-The-Middle
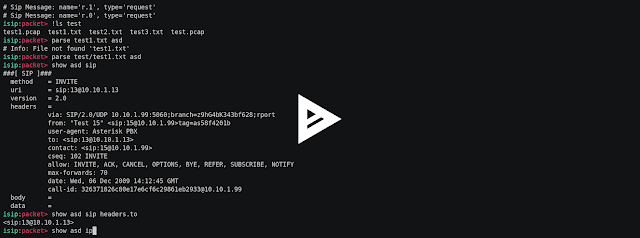
345Man-In-The-MiddleIsip – Interactive Sip Toolkit For Packet Manipulations, Sniffing, Man In The Middle Attacks, Fuzzing, Simulating Of Dos Attacks
Interactive sip toolkit for packet manipulations, sniffing, man in the middle attacks, fuzzing, simulating of dos attacks. Video Setup git clone https://github.com/halitalptekin/isip.git...
-

 186News
186NewsA DoS Flaw That Could Help Take Down WordPress Websites
Quite recently, a simple but serious application-level DoS (Denial of Service) flaw has been discovered in the WordPress CMS platform; this DoS...
-
 313Data Security
313Data SecurityHackers can conduct DoS attacks Using Flaw in Brother Printers
For unsuspecting users, the fact that printers can be used to conduct cyber attacks is difficult to believe but then when a coffee maker can...
-

 198Hacked
198HackedDoS And DDoS Attacks — The Origin Of A Species
Short Bytes: Over the last few months, we’ve seen some of the largest DDoS attacks to date and, by far, the most disruptive. You...
-
 225Geek
225GeekFind This Secret Command In MS-DOS Code To Win $100,000 And “Embarrass” Microsoft
Short Bytes: The creator of landmark PC operating system CP/M, late Gary Kildall, accused Microsoft of copying his operating system to make MS-DOS. It’s...
-

 161Hacked
161HackedBeware! More Than 135 Million Modems Are Vulnerable To DoS Attack
Short Bytes: A newly discovered flaw in the Arris modems has risked more than 135 million modems to DoS attacks. The flaw...
-

 272Hacked
272HackedDDoS Attacks Are Now Stronger Than Ever, 12 Mega Attacks in Recent Times
Image: Dailydot Short Bytes: The infamous DDoS attacks have increased at a staggering pace in the recent past. According to a latest...
-

 245Hacked
245HackedYour BitTorrent Client Can Be Exploited for DoS Attacks, Research Warns
Short Bytes: According to a new research, your BitTorrent client and BitTorrent Sync can be targeted and successfully exploited for DoS (Denial...
-

 310Denial of service
310Denial of serviceHow to perform a simple DOS attack
Performing a DOS attack may seem confusing at first , but when you have the right tools and knowledge , it’s quite...
-

 258News
258News#OpNSA: Australian Federal Police and Reserve Bank websites taken down amid spying row with Indonesia
Thursday: An Indonesian hacker going with the handle of ./BCT_48 has claimed responsibility for taking down the official website of Australian Federal Police and Reserve Bank amid an...






